Troubleshooting Windows 11 802.1X Authentication Issues
This technical reference guide provides a definitive diagnostic and remediation path for Windows 11 802.1X authentication failures. It details how OS upgrades disrupt certificate trust chains and Credential Guard enforcement, offering actionable GPO configurations and architectural best practices for enterprise IT teams.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- The Certificate Trust Breakdown
- Log Analysis and Error Codes
- Implementation Guide
- Step 1: Verify Root CA Deployment
- Step 2: Reconfigure the Wireless Network (IEEE 802.11) Policy
- Step 3: Address Credential Guard Conflicts
- Best Practices
- Troubleshooting & Risk Mitigation
- RADIUS Server Overload
- Captive Portal Fallback
- ROI & Business Impact
Executive Summary
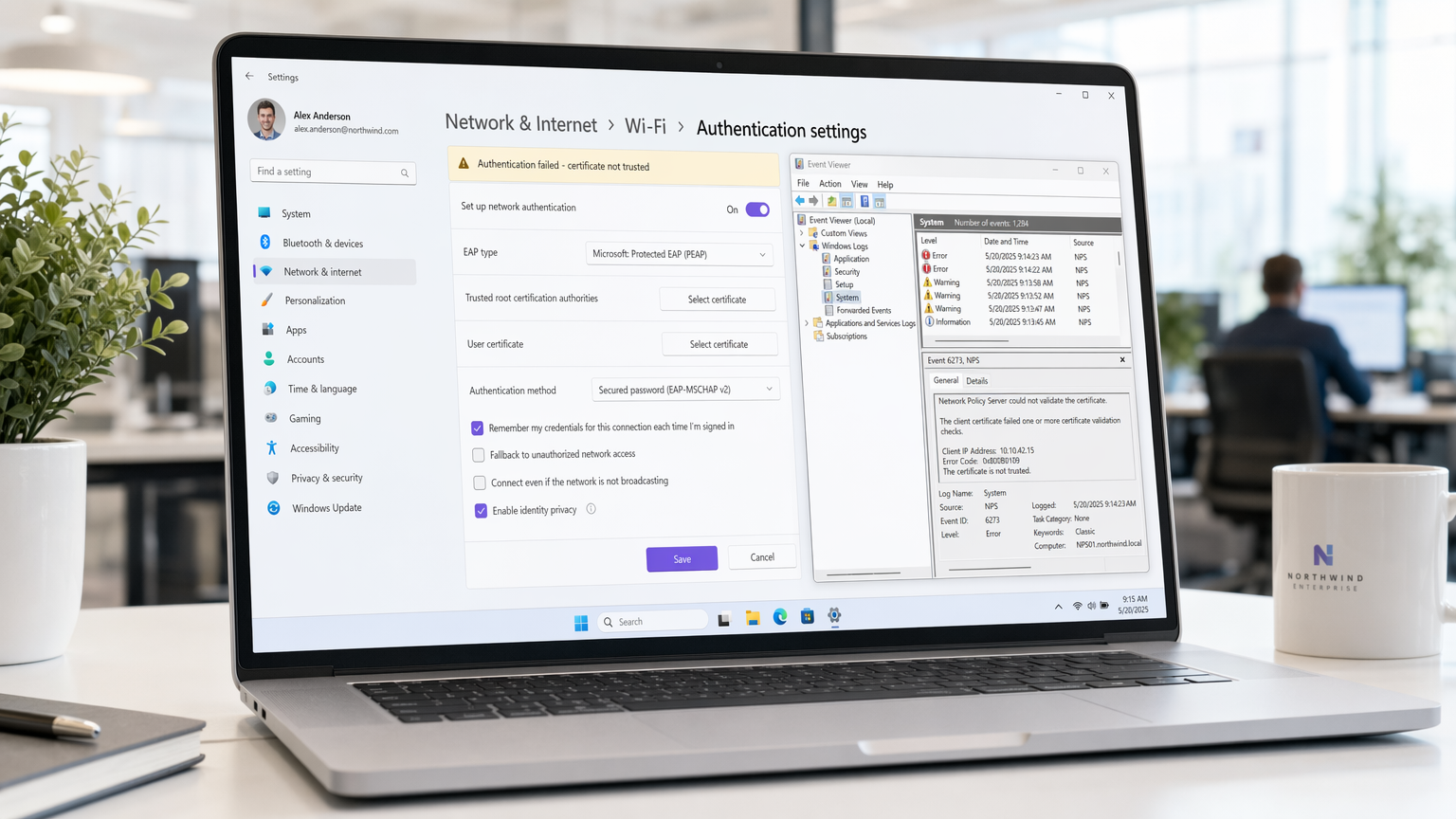
For enterprise IT teams managing large-scale deployments across Hospitality , Retail , and corporate campuses, the rollout of Windows 11 has introduced significant disruptions to 802.1X wireless authentication. The core issue stems from how Windows 11 handles legacy credential storage (via Credential Guard) and the migration of trusted root certificates within wireless profiles. When a device upgrades, the pre-existing PEAP-MSCHAPv2 or EAP-TLS configurations often fail to validate the Network Policy Server (NPS) certificate, resulting in an immediate, silent drop of the TLS tunnel.
This guide provides a vendor-neutral, architectural approach to diagnosing these failures. We detail the exact Event Viewer logs to monitor, the specific Group Policy Object (GPO) modifications required to restore trust, and the long-term strategic shift toward EAP-TLS required to maintain compliance with PCI DSS and GDPR. For venue operations directors and network architects, resolving this is not merely a helpdesk issue—it is a critical requirement for maintaining secure throughput and operational continuity.
Technical Deep-Dive
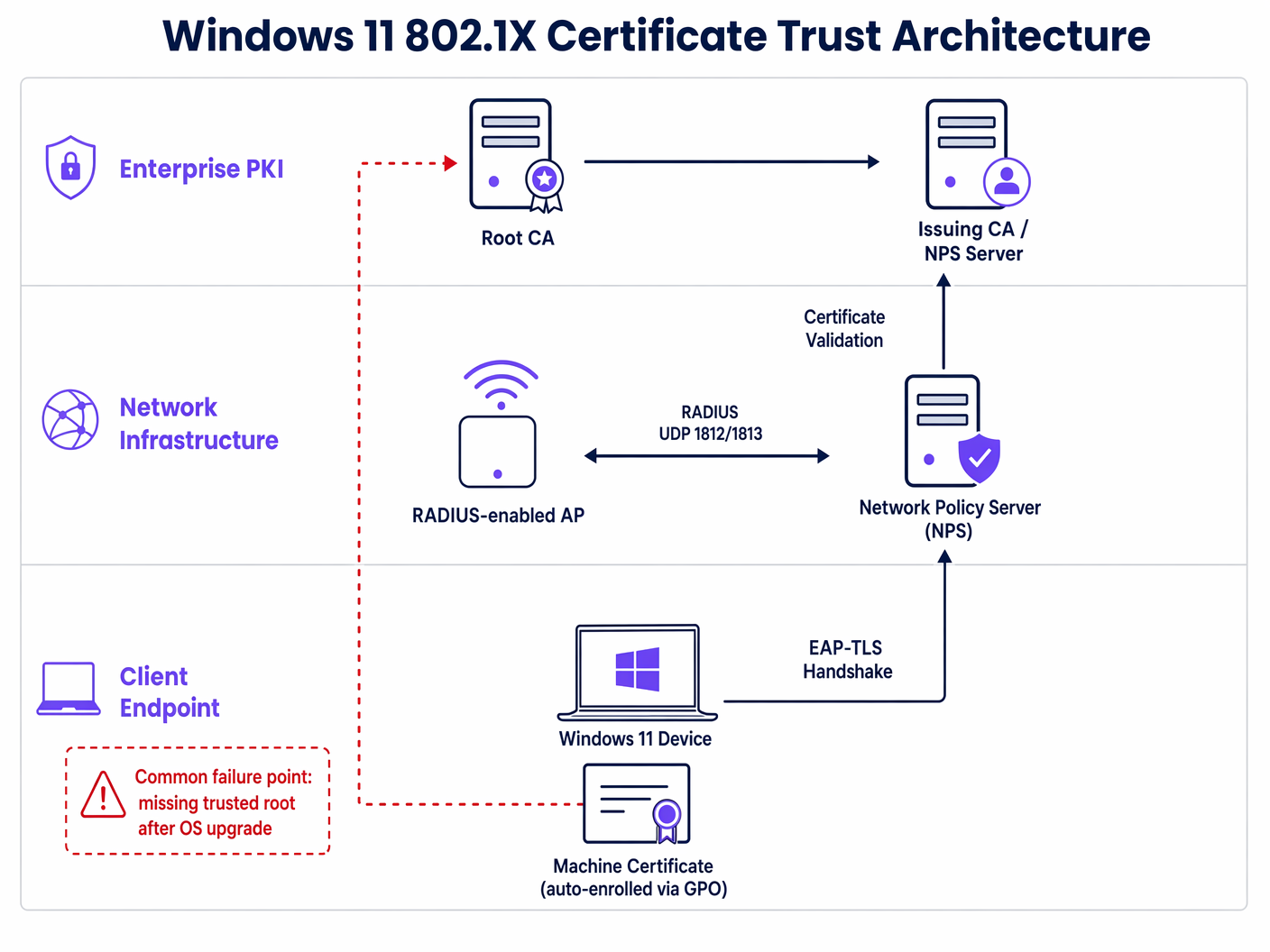
The 802.1X authentication framework relies on a complex chain of trust between the supplicant (the Windows 11 endpoint), the authenticator (the wireless access point), and the authentication server (typically a RADIUS/NPS server). The failure mechanism in Windows 11 primarily involves the supplicant's inability to validate the authenticator's identity.
The Certificate Trust Breakdown
In a standard PEAP (Protected Extensible Authentication Protocol) deployment, the server presents a certificate to the client to establish an encrypted TLS tunnel. The client must verify that this certificate was issued by a Trusted Root Certification Authority (CA).
During a Windows 11 upgrade, two critical changes often occur:
- Profile Migration Failures: The specific setting within the wireless profile that explicitly trusts the RADIUS server's Root CA is frequently stripped or corrupted.
- Credential Guard Enforcement: Windows 11 enables Windows Defender Credential Guard by default on compatible hardware. This virtualisation-based security isolates NTLM password hashes and Kerberos Ticket Granting Tickets. While excellent for mitigating Pass-the-Hash attacks, it can interfere with how legacy MS-CHAPv2 credentials are passed to the 802.1X supplicant, causing silent authentication failures even when the certificate is trusted.
Log Analysis and Error Codes
Diagnosing the issue requires examining the WLAN-AutoConfig operational logs within the Windows Event Viewer. The most common indicators of a certificate trust failure are:
- Error 11: The network stopped responding.
- Error 15: The certificate chain was issued by an authority that is not trusted.
These errors confirm that the TLS handshake is failing before the actual user or machine credentials can be verified.
Implementation Guide
Resolving the Windows 11 802.1X issue requires a coordinated update to your endpoint management baseline. The following steps outline the required remediation via Active Directory Group Policy.
Step 1: Verify Root CA Deployment
Ensure that the Root CA certificate that issued your NPS server's certificate is deployed to the Trusted Root Certification Authorities store on all client machines. This is typically handled via Computer Configuration > Policies > Windows Settings > Security Settings > Public Key Policies.
Step 2: Reconfigure the Wireless Network (IEEE 802.11) Policy
The critical fix lies in explicitly defining the trust relationship within the wireless profile.
- Open the relevant GPO and navigate to
Computer Configuration > Policies > Windows Settings > Security Settings > Wireless Network (IEEE 802.11) Policies. - Edit the properties of your corporate SSID profile.
- Navigate to the Security tab and select Properties for your chosen network authentication method (e.g., Microsoft: Protected EAP (PEAP)).
- In the PEAP properties window, tick the box for Verify the server's identity by validating the certificate.
- Crucially, in the Trusted Root Certification Authorities list, you MUST explicitly tick the box next to the CA that issued your NPS certificate.
- Ensure Enable Fast Reconnect is ticked to optimise roaming performance.
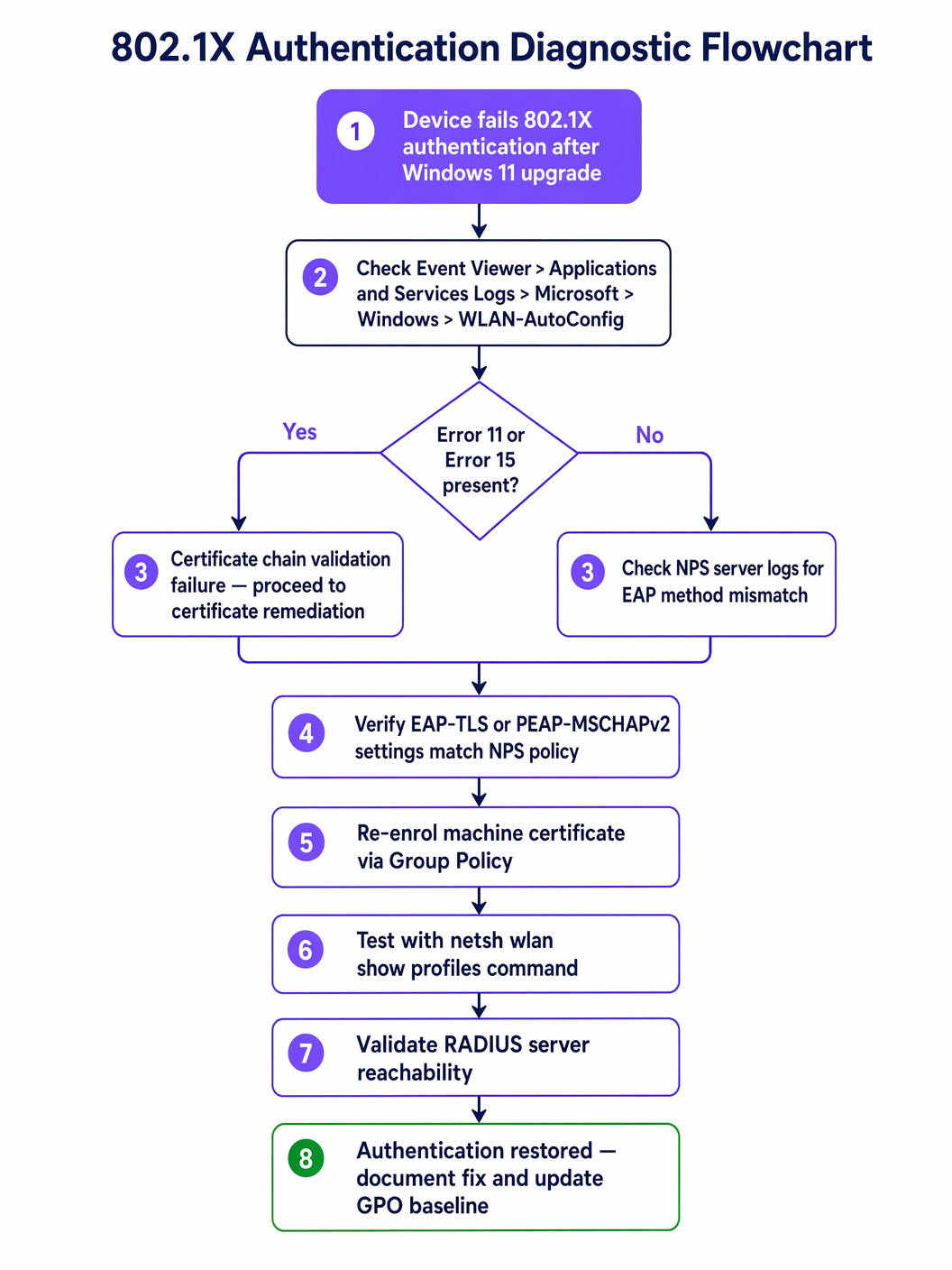
Step 3: Address Credential Guard Conflicts
If the certificate trust is verified but PEAP-MSCHAPv2 authentication still fails, Credential Guard is likely interfering. The long-term architectural solution is to migrate away from password-based authentication entirely. Transitioning to EAP-TLS (certificate-based authentication for both machine and user) bypasses the MS-CHAPv2 credential storage issue entirely. For detailed guidance on modernising your security posture, review our guide on Implementing WPA3-Enterprise for Enhanced Wireless Security .
Best Practices
When managing enterprise wireless infrastructure, particularly in high-density environments like Healthcare or large-scale Transport hubs, adhering to vendor-neutral standards is essential for risk mitigation.
- Never Disable Certificate Validation: The most common—and dangerous—workaround IT teams employ is unchecking the "Verify the server's identity" box. This exposes the network to Evil Twin attacks and credential harvesting, directly violating PCI DSS compliance. Always fix the underlying trust chain.
- Implement Machine Authentication: Relying solely on user credentials means devices cannot connect to the network before a user logs in, breaking GPO updates and remote management. Implement machine authentication (using EAP-TLS) to ensure devices are always connected and manageable.
- Standardise on EAP-TLS: Password-based 802.1X (PEAP) is increasingly fragile against OS-level security changes. EAP-TLS provides stronger security, seamless user experience (no password prompts), and immunity to Credential Guard conflicts.
Troubleshooting & Risk Mitigation
Beyond the primary certificate trust issue, network architects must be prepared for secondary failure modes during a Windows 11 rollout.
RADIUS Server Overload
When a large batch of machines is upgraded and subsequently fails authentication, they will continuously retry the connection. This can lead to a RADIUS storm, overwhelming the NPS servers and causing a denial-of-service condition for the entire wireless network.
Mitigation: Implement aggressive RADIUS timeout and retry limits on the wireless LAN controllers (WLCs). Stagger OS upgrade rollouts to monitor NPS server CPU and memory utilisation.
Captive Portal Fallback
For devices that absolutely cannot be remediated via GPO (e.g., unmanaged BYOD or contractor devices), provide a secure fallback mechanism. Utilising a robust Guest WiFi solution with a captive portal allows these users to gain internet access while remaining isolated from the internal corporate network. This ensures productivity is not halted while the IT team investigates the 802.1X failure.
ROI & Business Impact
Resolving 802.1X authentication issues is not just a technical necessity; it has direct business implications.
- Helpdesk Cost Reduction: A proactive GPO fix prevents hundreds of tier-1 support tickets, significantly reducing IT operational expenditure.
- Operational Continuity: In sectors like Retail , where mobile point-of-sale (mPOS) devices rely on secure Wi-Fi, authentication failures directly impact revenue generation.
- Compliance Posture: Maintaining strict certificate validation ensures ongoing compliance with regulatory frameworks, avoiding potential fines and reputational damage associated with data breaches.
By addressing the root cause of Windows 11 authentication failures and migrating towards robust EAP-TLS architectures, IT leaders can ensure their wireless infrastructure remains a secure, high-performance asset.
Key Terms & Definitions
802.1X
An IEEE standard for port-based network access control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational security protocol for enterprise wireless networks, ensuring only authorized devices and users can access corporate resources.
PEAP (Protected Extensible Authentication Protocol)
An authentication protocol that encapsulates the EAP within an encrypted and authenticated TLS tunnel.
The most common legacy 802.1X deployment, relying on a server-side certificate and client-side passwords (MS-CHAPv2). It is highly susceptible to Windows 11 upgrade issues.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An EAP method that relies on client and server certificates to establish a secure connection.
The recommended architectural standard for modern enterprise wireless, providing the highest level of security and immunity to password-related OS conflicts.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The server component (often Microsoft NPS) that processes the 802.1X authentication requests from the wireless access points.
Supplicant
The client device (e.g., a Windows 11 laptop) attempting to access the network.
The endpoint that must be correctly configured via GPO to trust the RADIUS server's certificate.
Authenticator
The network device (e.g., a wireless access point or switch) that facilitates the authentication process between the supplicant and the RADIUS server.
The infrastructure component that enforces the 802.1X policy, blocking access until authentication is successful.
Credential Guard
A Windows security feature that uses virtualization-based security to isolate secrets so that only privileged system software can access them.
A common cause of PEAP-MSCHAPv2 failures in Windows 11, as it alters how legacy passwords are handled during the authentication process.
Group Policy Object (GPO)
A collection of settings that define what a system will look like and how it will behave for a defined group of users or computers in Active Directory.
The primary mechanism for deploying the required certificate trust and wireless profile configurations to resolve Windows 11 802.1X issues at scale.
Case Studies
A large retail chain with 500 locations is rolling out Windows 11 to all store manager laptops. After the first 50 upgrades, managers report they cannot connect to the 'Corp-Secure' SSID. The helpdesk confirms the devices are receiving the correct GPO, but the connection drops silently. How should the network architect resolve this?
The architect must first verify the specific error in the WLAN-AutoConfig logs on a failing device. If Error 11 or 15 is present, the issue is certificate trust. The architect must edit the 'Wireless Network (IEEE 802.11) Policies' GPO. Within the PEAP properties for the 'Corp-Secure' profile, they must explicitly check the box next to the specific Root CA that issued the RADIUS server's certificate. Once the GPO is updated and pushed via gpupdate /force, the laptops will successfully validate the server and connect.
A hospital IT team has updated their GPO to explicitly trust the RADIUS server's Root CA, but Windows 11 devices using PEAP-MSCHAPv2 are still failing to authenticate. The NPS logs show 'Authentication failed due to a user credentials mismatch.' What is the likely cause and the recommended long-term solution?
The likely cause is Windows Defender Credential Guard, which is enabled by default in Windows 11 and can interfere with legacy MS-CHAPv2 credential handling. The immediate fix is to disable Credential Guard via GPO for those specific devices, but this weakens the endpoint security posture. The recommended long-term architectural solution is to migrate the wireless network to EAP-TLS using machine and user certificates. This eliminates the reliance on passwords and bypasses the Credential Guard conflict entirely.
Scenario Analysis
Q1. A CTO asks you to resolve a widespread 802.1X failure immediately by unchecking 'Verify the server's identity' in the GPO to get the sales team back online. How do you respond?
💡 Hint:Consider the compliance and security implications of disabling certificate validation.
Show Recommended Approach
I would advise against this approach. Disabling certificate validation exposes the network to Evil Twin attacks and credential harvesting, which directly violates PCI DSS and GDPR compliance. The correct approach is to identify the missing Root CA and explicitly trust it within the GPO. If immediate access is required, we can route affected users through a secure Guest WiFi captive portal as a temporary fallback while the GPO propagates.
Q2. You are designing the wireless architecture for a new corporate campus and must choose between PEAP-MSCHAPv2 and EAP-TLS. Given the recent Windows 11 upgrade issues, which do you recommend and why?
💡 Hint:Evaluate the impact of OS-level security features like Credential Guard on legacy authentication methods.
Show Recommended Approach
I strongly recommend EAP-TLS. While PEAP-MSCHAPv2 is easier to deploy initially (relying on AD passwords), it is highly susceptible to OS-level changes like Credential Guard and profile migration failures. EAP-TLS uses machine and user certificates, eliminating password-related vulnerabilities, providing a seamless user experience, and ensuring long-term architectural stability against future OS updates.
Q3. After deploying the correct GPO to explicitly trust the Root CA, several machines still fail to connect. You notice these machines have not been on the network for several weeks. What is the likely issue and how do you resolve it?
💡 Hint:Consider how Group Policy updates are delivered to endpoints.
Show Recommended Approach
The likely issue is that these machines have not received the updated GPO because they cannot connect to the network to pull the policy. This is a classic 'chicken-and-egg' problem. To resolve it, the machines must be temporarily connected via a wired Ethernet connection or a secure VPN to authenticate to the domain and run gpupdate /force to receive the new wireless profile configuration.



