How to Build a Campus WiFi Network: A University IT Guide
This technical guide provides a comprehensive blueprint for designing and deploying high-density campus WiFi networks, covering everything from active site surveys and access point placement to controller architecture, seamless roaming, and secure guest onboarding. It is written for IT managers, network architects, and CTOs at universities and large venues who need actionable guidance to plan and execute a wireless deployment this quarter. The guide also maps Purple's Guest WiFi and analytics platform to real integration points within the deployment lifecycle.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- The Three-Tier Architecture
- Wireless Standards and Frequencies
- Security and Authentication
- Implementation Guide: From Survey to Deployment
- Phase 1: The Active Site Survey
- Phase 2: Capacity Planning
- Phase 3: AP Placement and Channel Planning
- Phase 4: Configuring Seamless Roaming
- Phase 5: VLAN Segmentation and Policy Enforcement
- Best Practices for Campus Environments
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- Listen to the Briefing

Executive Summary
For university IT teams and venue operators, a campus WiFi network is no longer an amenity — it is critical infrastructure. Modern higher education environments demand high-density, high-throughput wireless networks capable of supporting multiple devices per user, bandwidth-heavy applications, and seamless mobility across vast physical footprints. This guide outlines the technical architecture, deployment strategies, and operational best practices required to build a resilient campus wireless network. We focus on practical implementation — from RF planning and access point (AP) selection to controller architecture and secure onboarding — ensuring your deployment delivers ROI, compliance, and a frictionless user experience. Whether you are deploying across a single building or a multi-site estate, the principles here apply equally to Hospitality , Retail , Healthcare , and Transport environments.
Technical Deep-Dive: Architecture and Standards
Building a campus wireless network requires a structured approach to topology and adherence to modern wireless standards. The decisions made at the architecture stage determine the scalability, security, and performance of everything that follows.
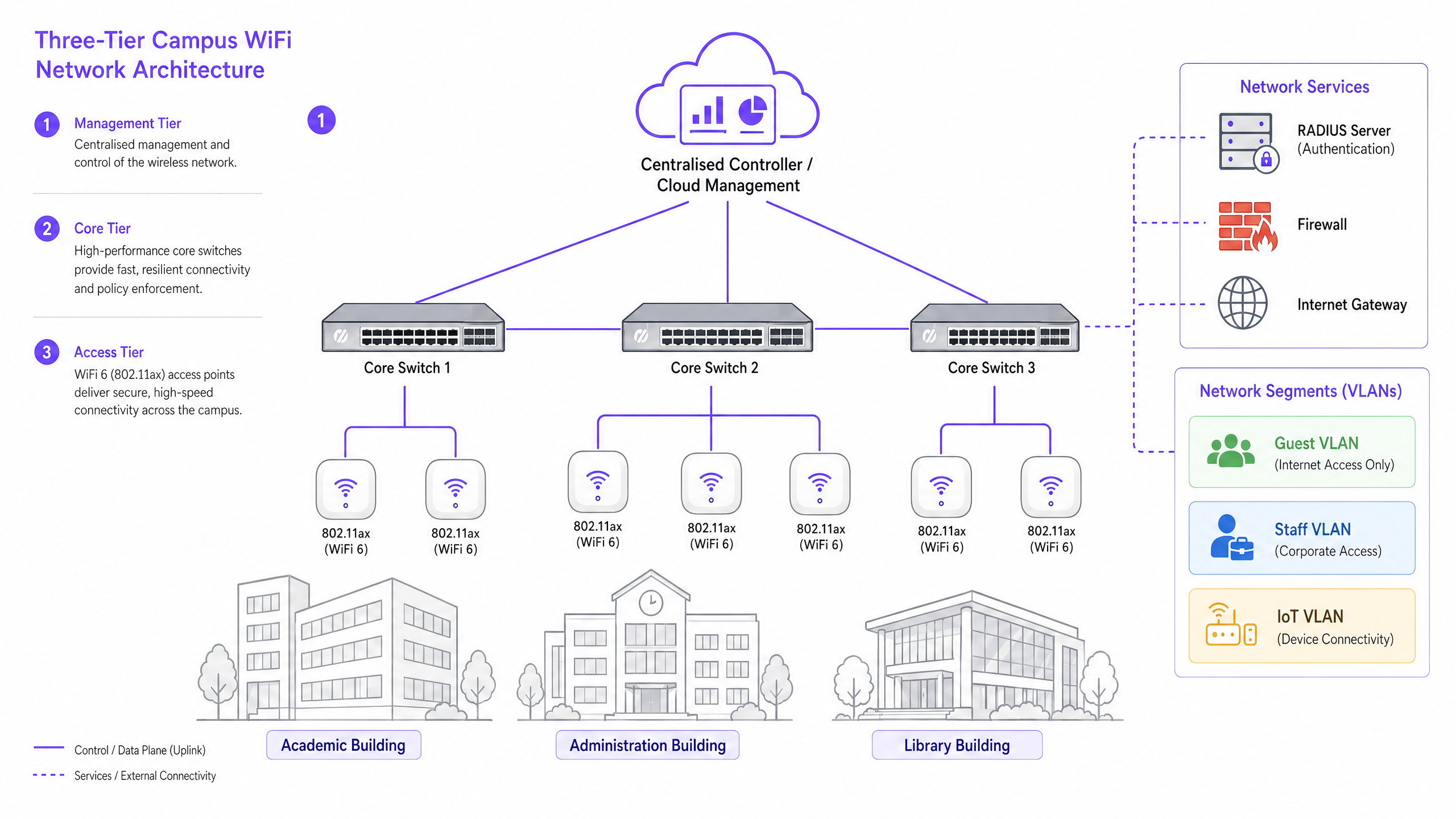
The Three-Tier Architecture
Enterprise campus networks employ a hierarchical three-tier architecture to ensure scalability, resilience, and performance. The three tiers are as follows:
Management/Core Tier: The central nervous system of the network. This includes high-capacity core routing switches and the central WLAN controller — whether on-premise or cloud-managed. The controller handles RF management, roaming handoffs, global policy enforcement, and firmware management across all access points. Cloud-managed controllers have become the dominant choice for new deployments, simplifying multi-site management and reducing on-premise hardware costs.
Distribution Tier: Aggregates traffic from the access tier, applying routing policies and ensuring redundancy before passing data to the core. In smaller campuses, this tier is often collapsed into the core.
Access Tier: The edge of the network, comprising Power over Ethernet Plus (PoE+) edge switches and the wireless Access Points (APs) themselves. For new deployments, PoE+ is the minimum standard, as WiFi 6 access points draw significantly more power than their predecessors.
Wireless Standards and Frequencies
Modern deployments should standardise on 802.11ax (WiFi 6) or WiFi 6E. WiFi 6 introduces critical high-density features including Orthogonal Frequency-Division Multiple Access (OFDMA), which allows a single AP to serve multiple clients simultaneously on sub-channels, and Target Wake Time (TWT), which reduces battery drain on IoT devices. WiFi 6E extends these capabilities into the 6GHz band, offering massive contiguous spectrum free from legacy device interference — a significant advantage in high-density environments like lecture theatres and conference halls.
| Standard | Frequency Bands | Max Throughput | Key Feature | Best Use Case |
|---|---|---|---|---|
| 802.11n (WiFi 4) | 2.4GHz / 5GHz | 600 Mbps | MIMO | Legacy support only |
| 802.11ac (WiFi 5) | 5GHz | 3.5 Gbps | MU-MIMO | Existing deployments |
| 802.11ax (WiFi 6) | 2.4GHz / 5GHz | 9.6 Gbps | OFDMA, TWT | New campus deployments |
| 802.11ax (WiFi 6E) | 2.4 / 5 / 6GHz | 9.6 Gbps | 6GHz spectrum | High-density, future-proof |
Security and Authentication
Security must be multi-layered. For staff and enrolled students, 802.1X/EAP authentication linked to the university's identity provider (Active Directory, LDAP, or a cloud identity service) is mandatory. This provides encrypted, credential-based access that meets the requirements of standards like ISO 27001 and Cyber Essentials. For transient users — visiting academics, conference delegates, and members of the public — a secure captive portal is required. Integrating a robust Guest WiFi solution ensures GDPR-compliant onboarding, customisable splash pages, and the ability to gather actionable insights via WiFi Analytics . All wireless traffic should be encrypted using WPA3, the current standard, which provides stronger protections against brute-force attacks than its predecessor WPA2. For a comprehensive review of access point security posture, see our Access Point Security: Your 2026 Enterprise Guide .
Implementation Guide: From Survey to Deployment
Deploying a campus network is a phased process requiring meticulous planning before a single cable is run or AP is mounted.
Phase 1: The Active Site Survey
A predictive survey using floor plans is insufficient for complex campus environments. You must conduct active, on-site RF surveys. Building materials in older universities — thick masonry, metal lath, reinforced concrete — attenuate signals unpredictably. Surveying identifies RF black holes and helps determine optimal AP placement to ensure both coverage and capacity. The output should be a validated heat map showing signal strength, channel utilisation, and interference levels across every floor.
Phase 2: Capacity Planning
Historically, networks were designed for coverage — ensuring a signal reached every corner. Today, design for capacity. In a 300-seat lecture theatre, assume three devices per student: laptop, smartphone, and tablet. This requires deploying high-density APs with directional antennas to sectorise the room, rather than relying on a single omnidirectional AP that will quickly become overwhelmed. The rule of thumb for high-density deployments is one AP per 25-30 concurrent users in a lecture environment.
Phase 3: AP Placement and Channel Planning
Careful channel planning is essential to minimise Co-Channel Interference (CCI). Use non-overlapping channels (1, 6, 11 on 2.4GHz; dynamic allocation on 5GHz and 6GHz). Ensure APs are placed strategically — avoid mounting them above drop ceilings or behind HVAC ducts, which degrade performance. For high-ceiling environments, use APs with downward-facing directional antennas.
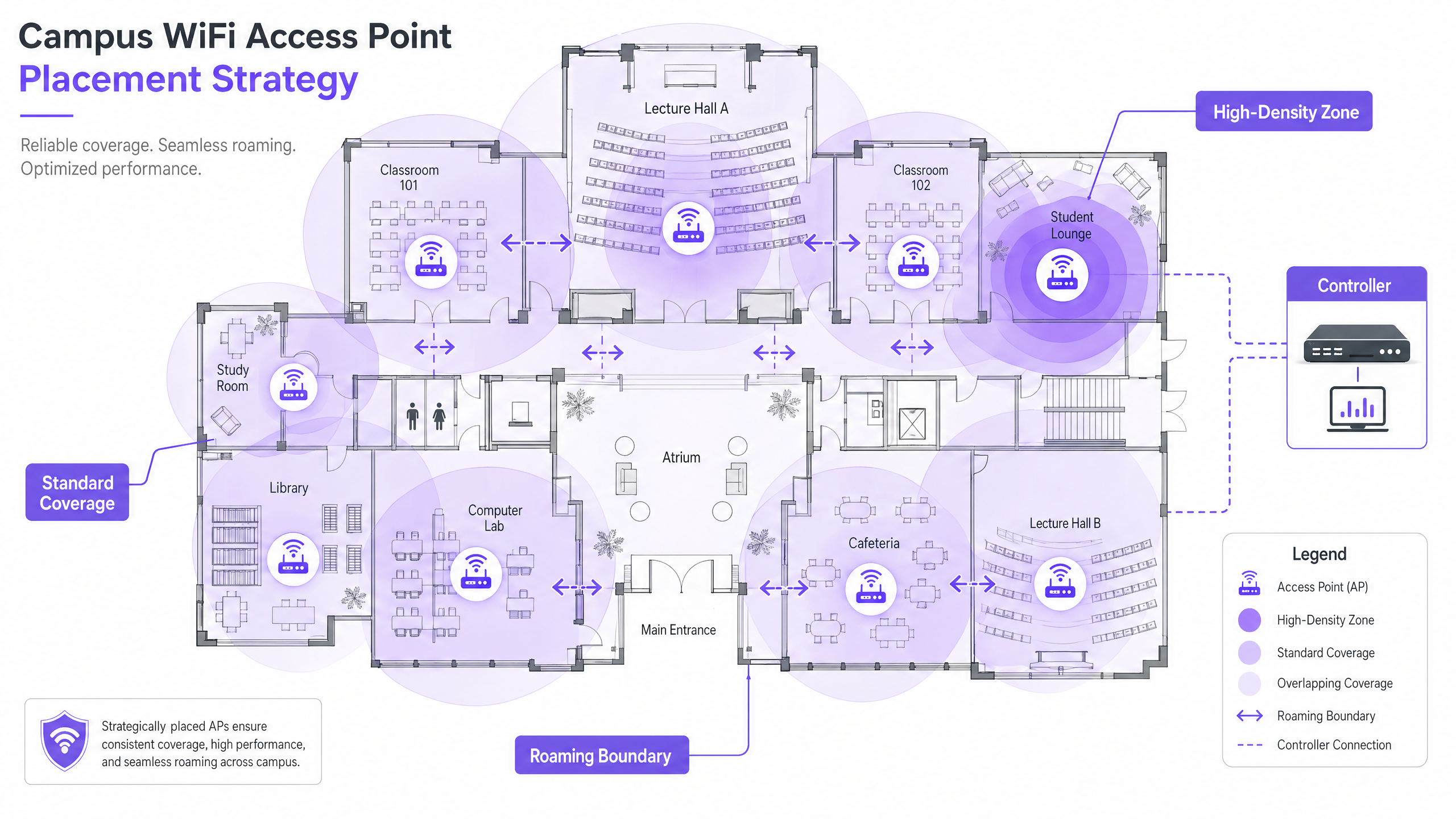
Phase 4: Configuring Seamless Roaming
As users move between buildings, their connection must seamlessly hand off between APs. Implement the fast roaming trifecta: 802.11k (neighbour reports), 802.11v (BSS transition management), and 802.11r (fast BSS transition). Together, these standards allow client devices to make intelligent roaming decisions and complete authentication handoffs in milliseconds rather than seconds — critical for VoIP and real-time applications.
Tuning transmit power is equally important. If Tx power is too high, client devices will cling to a distant AP ('sticky clients') rather than roaming to a closer one. Reduce Tx power to create overlapping but appropriately sized coverage cells, and disable legacy data rates (1, 2, 5.5 Mbps) to force devices to drop weak connections and roam.
Phase 5: VLAN Segmentation and Policy Enforcement
Create dedicated VLANs for each user class: Staff, Students, Guests, and IoT devices. IoT devices — building management systems, security cameras, digital signage — should never share a network segment with user devices. Apply strict firewall rules between VLANs, allowing only the minimum necessary communication. For DNS-level security and protection against malicious domains, see our guide on how to Protect Your Network with Strong DNS and Security .
Best Practices for Campus Environments
The following vendor-neutral recommendations represent industry-standard practice for large wireless network deployments.
Band Steering: Force capable client devices onto the less congested 5GHz or 6GHz bands, reserving the 2.4GHz band for legacy devices and long-range IoT sensors. Most modern controllers support automatic band steering.
Minimum RSSI Thresholds: Configure the controller to refuse connections from clients whose signal strength falls below a defined threshold (typically -75 dBm). This prevents weak-signal clients from degrading the experience for all other users on the AP.
Wireless Intrusion Prevention (WIPS): Enable WIPS on the controller to detect and suppress rogue APs — personal routers plugged in by students or staff that cause interference and introduce security vulnerabilities.
Outdoor Coverage: Extend the network to quads and outdoor seating areas using ruggedised, weather-proof APs with directional antennas. Outdoor APs must handle temperature extremes, moisture, and vandalism resistance.
DHCP Lease Management: In high-turnover areas (cafeterias, libraries), reduce DHCP lease times for guest networks to one to two hours to prevent IP address exhaustion.
Purple's higher education focus is growing rapidly — read about our VP Education Tim Peers joining the team and what it means for campus network strategy.
Troubleshooting & Risk Mitigation
Even well-designed networks encounter operational issues. The following are the most common failure modes and their mitigations.
| Failure Mode | Symptoms | Root Cause | Mitigation |
|---|---|---|---|
| Sticky Clients | Poor performance despite strong signal | Tx power too high; legacy rates enabled | Reduce Tx power; disable rates below 11 Mbps |
| DHCP Exhaustion | Users unable to connect | Lease times too long; subnet too small | Reduce lease times; expand subnets |
| Co-Channel Interference | Slow throughput across the floor | Poor channel planning | Implement dynamic channel assignment |
| Rogue APs | Interference; security alerts | Unauthorised personal routers | Enable WIPS; conduct regular RF audits |
| Authentication Failures | Users unable to log in | RADIUS server overload or misconfiguration | Deploy redundant RADIUS; monitor auth logs |
ROI & Business Impact
For university leadership and venue operations directors, the ROI of a high-performance network extends well beyond basic connectivity. A robust campus wireless network directly supports modern pedagogical tools, digital campus initiatives, and operational efficiency programmes.
Leveraging WiFi Analytics provides actionable intelligence on footfall, dwell times, and space utilisation. This data can inform real estate decisions — identifying underutilised buildings or peak-demand spaces — and optimise HVAC usage based on real occupancy data, delivering measurable energy savings. These are the same analytics strategies deployed by operators in Retail and Hospitality environments, now increasingly applied to campus settings.
For organisations deploying guest WiFi as part of a broader digital engagement strategy, a well-configured Guest WiFi platform can also support marketing automation, alumni engagement, and visitor experience programmes. For smaller or satellite campus locations, our guide on How to Set Up a WiFi Hotspot for Your Business provides a practical starting point.
Listen to the Briefing
Key Definitions
802.11ax (WiFi 6)
The current IEEE standard for wireless networking, designed specifically to improve efficiency and performance in high-density environments through OFDMA, MU-MIMO, and TWT.
Essential for modern campus deployments to support a high volume of concurrent devices without performance degradation.
Co-Channel Interference (CCI)
Interference that occurs when multiple access points in the same area operate on the same channel, causing devices to wait for clear airtime before transmitting.
Poor channel planning leads to high CCI, which severely degrades network throughput even when signal strength is strong.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices, isolating their traffic from other devices on the same physical network infrastructure.
Crucial for security and performance; separating guest, staff, student, and IoT traffic prevents lateral movement and reduces congestion.
802.1X
An IEEE standard for port-based Network Access Control, providing a credential-based authentication mechanism for devices connecting to a LAN or WLAN via a RADIUS server.
The mandatory standard for secure, enterprise-grade authentication for staff and enrolled students on campus networks.
Captive Portal
A web page that a user of a public-access network must interact with before network access is granted, typically used for terms of service acceptance, authentication, and data capture.
Used for guest onboarding on campus networks; must be GDPR-compliant and integrated with an analytics platform for operational value.
OFDMA (Orthogonal Frequency-Division Multiple Access)
A multi-user version of OFDM that allows a single access point to simultaneously serve multiple clients on different sub-channels within the same transmission.
A key WiFi 6 feature that dramatically improves efficiency in high-density environments like lecture halls.
Sticky Client
A wireless device that remains connected to a distant AP with a weak signal, even when a closer AP with a stronger signal is available, due to the client's reluctance to initiate a roam.
Causes poor performance for the affected user and unnecessary load on the distant AP; mitigated by proper RF tuning and disabling legacy data rates.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, typically expressed in dBm (decibels relative to one milliwatt), where values closer to zero indicate a stronger signal.
Used during site surveys to determine coverage boundaries and during controller configuration to set minimum connection thresholds.
PoE+ (Power over Ethernet Plus)
An IEEE 802.3at standard that delivers up to 30 watts of power over standard Ethernet cabling, sufficient to power WiFi 6 access points without a separate power supply.
The minimum PoE standard required for new campus deployments using WiFi 6 APs.
Worked Examples
A Russell Group university is upgrading a Grade II listed, 19th-century library to support 500 concurrent student connections. The building features thick stone walls, high ceilings, and ornate internal partitions. How should the IT team approach the wireless deployment?
Step 1: Commission an active, on-site RF survey — predictive modelling will be highly inaccurate due to the stone walls and irregular floor plan. Use professional wifi survey software to generate validated heat maps. Step 2: Deploy high-density WiFi 6 APs with directional patch antennas focused downward into reading areas, avoiding signal bounce off high ceilings. Target one AP per 25 concurrent users. Step 3: Implement a dedicated VLAN for student access via 802.1X linked to the university's Active Directory, and a separate guest VLAN with a captive portal for visiting researchers and public users. Step 4: Tune AP transmit power to create appropriately sized coverage cells, preventing sticky clients as students move between reading rooms. Step 5: Disable legacy data rates (1, 2, 5.5 Mbps) to enforce roaming. Step 6: Deploy a cloud-managed controller for centralised visibility and RF optimisation.
A Premier League football stadium needs to provide WiFi coverage for 40,000 concurrent connections on match days, with a secondary requirement for event-day analytics on fan movement and dwell times.
Step 1: Deploy under-seat APs with highly directional antennas to create micro-cells for specific seating sections — this is the only viable approach at this density. Step 2: Disable 2.4GHz radios on the majority of APs to eliminate Co-Channel Interference in the dense RF environment; force all traffic to 5GHz and 6GHz. Step 3: Enable 802.11k/v/r to facilitate rapid roaming as fans move through concourses during half-time. Step 4: Implement a captive portal via Purple's Guest WiFi platform for secure, high-throughput onboarding, capturing opt-in analytics data on fan movement and dwell times. Step 5: Segment the network with separate VLANs for fans, operations staff, broadcast equipment, and point-of-sale systems. Step 6: Ensure PCI DSS compliance on the payment network segment.
Practice Questions
Q1. You are deploying APs in a new university dormitory block. The building has long central corridors with student rooms on either side, separated by solid concrete walls. Should you place APs in the central corridors or inside the individual dorm rooms?
Hint: Consider the attenuation caused by concrete walls and fire doors, and the capacity required per room.
View model answer
Deploy APs inside the dorm rooms, using wall-plate APs that mount flush to the wall and connect via the in-room Ethernet port. Corridor deployments result in poor signal penetration into rooms due to concrete walls and heavy fire doors, and fail to provide the per-room capacity needed for multiple devices per student. Wall-plate APs provide a dedicated, high-quality connection for each room and are the industry-standard approach for student accommodation.
Q2. Users in the university cafeteria are reporting slow WiFi speeds during the lunch period, despite their devices showing full signal strength bars. What are the two most likely causes, and how would you investigate each?
Hint: Signal strength does not equal capacity. Consider both the RF environment and the number of concurrent users.
View model answer
The two most likely causes are: (1) AP capacity overload — the APs are overwhelmed by the sheer number of concurrent devices during the lunch rush. Investigate by checking the controller dashboard for client counts per AP and throughput utilisation. If APs are serving 80+ clients, additional APs or a high-density AP upgrade is required. (2) Co-Channel Interference — multiple APs in the cafeteria are operating on the same channel, causing devices to wait for clear airtime. Investigate using a spectrum analyser or the controller's RF health dashboard. Resolve by enabling dynamic channel assignment and ensuring non-overlapping channel allocation.
Q3. Your university is hosting a major international conference with 800 delegates, all of whom will need WiFi access for three days. The conference is held in a building that normally serves 200 staff. How do you approach the temporary network uplift?
Hint: Consider both the temporary capacity increase and the security separation between conference delegates and permanent staff.
View model answer
Deploy temporary high-density APs in the main conference hall and breakout rooms, connected to the existing switching infrastructure via temporary PoE+ switches if port capacity is insufficient. Create a dedicated conference VLAN, completely isolated from the staff network, with its own DHCP scope and internet breakout. Deploy a branded captive portal via a guest WiFi platform for delegate onboarding, capturing opt-in data for post-event analytics. Reduce DHCP lease times to two hours to manage IP address churn across the three-day event. After the conference, remove temporary APs and decommission the conference VLAN.