WPA-PSK Spiegato: Cos'è, Come Funziona e i Suoi Rischi per la Sicurezza
Questo autorevole riferimento tecnico analizza i meccanismi di WPA-PSK — il suo handshake a 4 vie, l'architettura crittografica e le vulnerabilità di sicurezza intrinseche — e spiega precisamente perché le reti aziendali devono passare a robuste architetture 802.1X o a captive portal gestiti. Fornisce una guida pratica all'implementazione per i responsabili IT che gestiscono ambienti complessi in settori come l'ospitalità, il commercio al dettaglio, gli eventi e le organizzazioni del settore pubblico.
Ascolta questa guida
Visualizza trascrizione del podcast
- Riepilogo Esecutivo
- Approfondimento Tecnico: Come Funziona WPA-PSK
- Le Basi Crittografiche
- L'Handshake a 4 Vie
- Dove il Modello di Sicurezza si Infrange
- Guida all'Implementazione: Transizione alla Sicurezza Aziendale
- Fase 1: Verifica della Tua Attuale Infrastruttura di Rete
- Fase 2: Separare il traffico degli ospiti da quello aziendale
- Fase 3: Implementare il WiFi gestito per gli ospiti
- Fase 4: Contenere i dispositivi PSK legacy
- Fase 5: Integrare con l'architettura di rete moderna
- Best Practice e Mitigazione del Rischio
- ROI e Impatto sul Business

Riepilogo Esecutivo
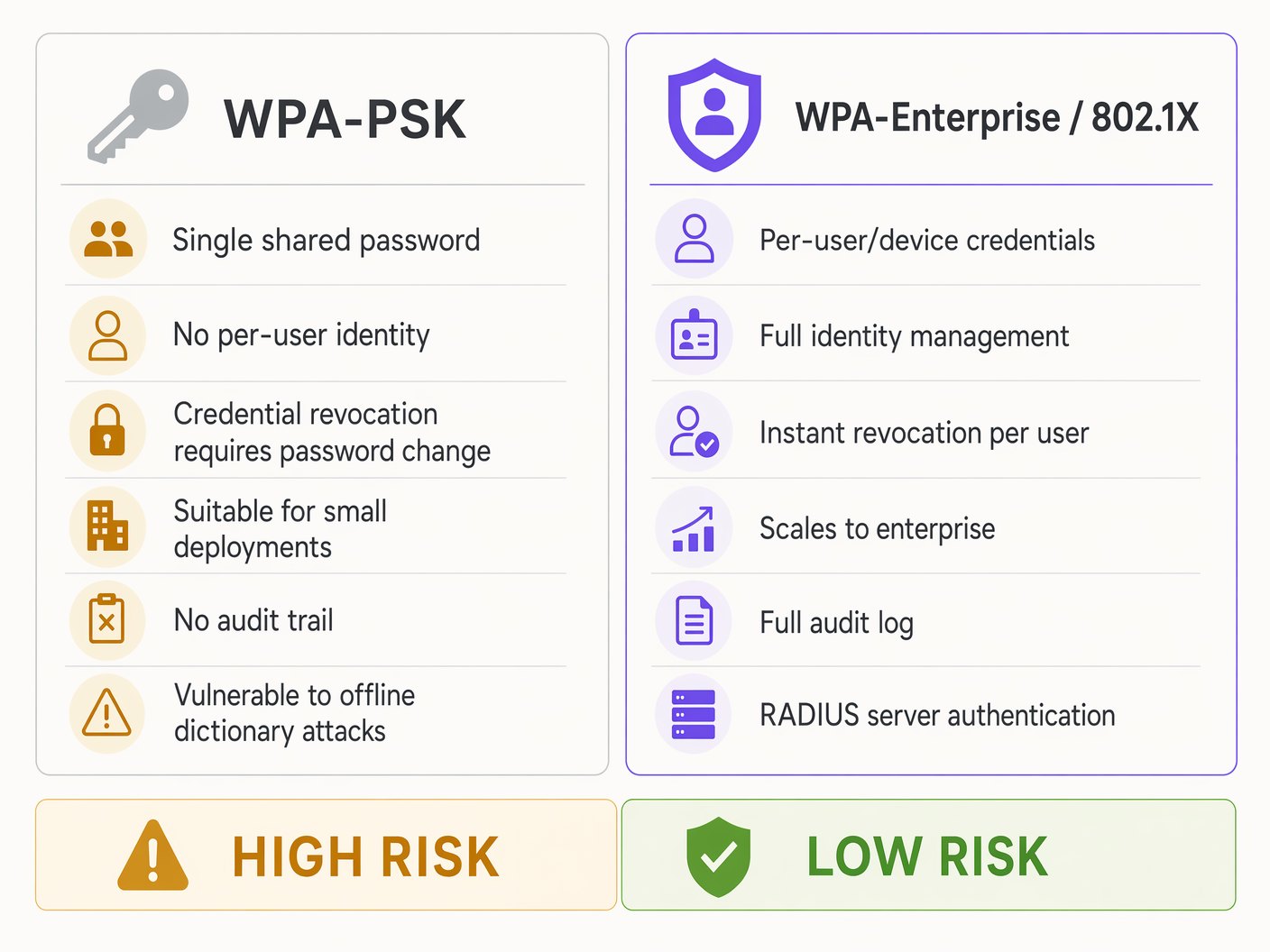
Per i responsabili IT e gli architetti di rete che operano su larga scala — sia in catene di vendita al dettaglio, strutture ricettive o grandi strutture del settore pubblico — la sicurezza WiFi non può basarsi su meccanismi di livello consumer. WPA-PSK (WiFi Protected Access Pre-Shared Key) rimane lo standard predefinito per le reti domestiche e le piccole imprese, ma le sue limitazioni architetturali introducono rischi inaccettabili negli ambienti aziendali.
Sebbene WPA-PSK sia semplice da implementare, l'affidamento a una singola passphrase condivisa crea gravi colli di bottiglia operativi: la revoca delle credenziali è impossibile senza interruzioni a livello di rete, l'identità dell'utente rimane opaca e la crittografia fondamentale è vulnerabile agli attacchi a dizionario offline. Questa guida analizza i meccanismi tecnici di WPA-PSK, spiega esattamente dove il suo modello di sicurezza si rivela inadeguato per le applicazioni aziendali e delinea il passaggio imperativo verso WPA-Enterprise (802.1X) e robuste soluzioni Guest WiFi .
Comprendendo queste limitazioni, i CTO e i direttori delle operazioni delle strutture possono mitigare i rischi, garantire la conformità a standard come PCI DSS e GDPR e sfruttare piattaforme come Purple per trasformare una passività di sicurezza in una risorsa gestita e basata su analisi.
Approfondimento Tecnico: Come Funziona WPA-PSK
WPA-PSK è stato progettato per fornire una crittografia robusta senza il sovraccarico di un server di autenticazione. Si basa su una Pre-Shared Key (PSK) — una password che va da 8 a 63 caratteri — nota sia al dispositivo client (supplicante) che all'Access Point (autenticatore).
Le Basi Crittografiche
La PSK non viene utilizzata direttamente per crittografare il traffico dati. Serve invece come materiale di base per generare una Pairwise Master Key (PMK). La PMK viene calcolata utilizzando l'algoritmo PBKDF2 (Password-Based Key Derivation Function 2), che esegue l'hashing della passphrase insieme all'SSID della rete per 4.096 volte. Questo processo computazionalmente intensivo è stato progettato per rallentare gli attacchi a forza bruta. Tuttavia, le moderne piattaforme GPU possono eseguire miliardi di operazioni di hash al secondo, rendendo questa protezione inadeguata contro un attaccante determinato con un handshake catturato.
L'Handshake a 4 Vie
Una volta stabilita la PMK, il client e l'AP devono dimostrare di conoscere entrambi la PMK senza mai trasmetterla via etere. Ciò si ottiene tramite l'Handshake a 4 Vie, che deriva la Pairwise Transient Key (PTK) utilizzata per la crittografia effettiva della sessione.
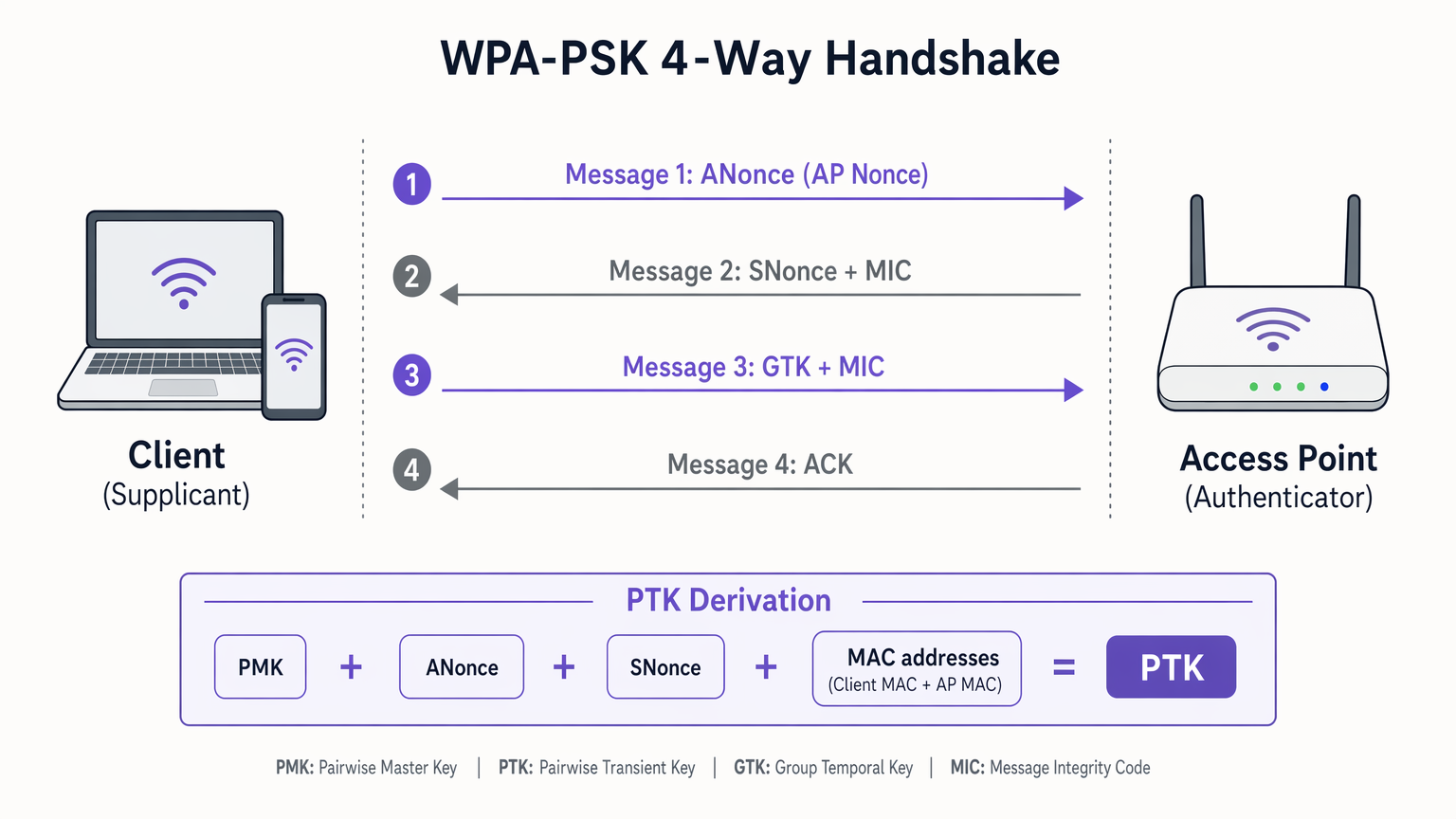
L'handshake procede come segue. Nel Messaggio 1, l'AP invia un nonce crittografico (ANonce) al client. Il client ora ha tutti gli input necessari — PMK, ANonce, il proprio SNonce e entrambi gli indirizzi MAC — per calcolare la PTK. Nel Messaggio 2, il client invia il proprio nonce (SNonce) all'AP, insieme a un Message Integrity Code (MIC) per dimostrare di aver generato con successo la PTK. Nel Messaggio 3, l'AP verifica il MIC, genera la PTK e invia la Group Temporal Key (GTK) — utilizzata per il traffico broadcast e multicast — crittografata sotto la PTK. Nel Messaggio 4, il client conferma la ricezione e inizia la trasmissione dei dati crittografati.
Dove il Modello di Sicurezza si Infrange
Il difetto fondamentale di WPA-PSK in un contesto aziendale non è l'algoritmo di crittografia — AES-CCMP è altamente sicuro — ma l'architettura di gestione delle chiavi.
In primo luogo, gli attacchi a dizionario offline rappresentano il principale rischio crittografico. Se un attaccante cattura l'handshake a 4 vie (che viene trasmesso in chiaro), può eseguire attacchi a forza bruta offline contro il MIC catturato. Poiché molte strutture utilizzano password deboli o prevedibili, questo è un esercizio banale per le moderne piattaforme GPU in grado di miliardi di operazioni di hash al secondo.
In secondo luogo, la mancanza di identità utente è un fallimento operativo critico. WPA-PSK autentica il dispositivo, non l'utente. Un indirizzo IP e un indirizzo MAC non forniscono alcuna identità verificabile, limitando gravemente WiFi Analytics e rendendo la risposta agli incidenti quasi impossibile. I moderni sistemi operativi mobili (iOS 14+, Android 10+) randomizzano anche gli indirizzi MAC per impostazione predefinita, rendendo inaffidabile anche il tracciamento a livello di dispositivo.
In terzo luogo, il problema della revoca crea un onere operativo continuo. Quando un dipendente se ne va o un dispositivo viene compromesso, l'unico modo per revocare l'accesso è cambiare la PSK sull'AP e aggiornare manualmente ogni singolo dispositivo client legittimo. In un ambiente Retail con centinaia di sedi e migliaia di dispositivi, questo è operativamente irrealizzabile — e in pratica, le password vengono raramente cambiate.
Guida all'Implementazione: Transizione alla Sicurezza Aziendale
Per gli ambienti aziendali, la migrazione da WPA-PSK a WPA-Enterprise (802.1X) è un imperativo di sicurezza critico. Il seguente framework si applica a implementazioni in Hospitality , Healthcare , Retail e Transport .
Fase 1: Verifica della Tua Attuale Infrastruttura di Rete
Inizia con un inventario completo. Identifica ogni SSID, ogni metodo di autenticazione e ogni tipo di dispositivo che si connette alla tua rete. Categorizza i dispositivi in tre gruppi: asset aziendali gestiti, dispositivi ospiti o visitatori e dispositivi legacy o IoT. Questa segmentazione guida ogni successiva ddecisione.
Fase 2: Separare il traffico degli ospiti da quello aziendale
Non utilizzare mai un PSK per le risorse aziendali. I dispositivi aziendali devono autenticarsi tramite 802.1X utilizzando server RADIUS e metodi EAP. EAP-TLS (basato su certificati) è lo standard di riferimento per i dispositivi headless come i terminali POS, mentre PEAP-MSCHAPv2 è appropriato per i dispositivi rivolti agli utenti collegati agli account di Active Directory. Per un confronto dettagliato di questi protocolli, fare riferimento a EAP-TLS vs. PEAP: ¿Qué protocolo de autenticación es el adecuado para su red? .
Fase 3: Implementare il WiFi gestito per gli ospiti
Per le reti pubbliche, fornire un PSK statico è un fallimento sia in termini di sicurezza che di marketing. Implementare un SSID aperto che reindirizza a un captive portal. Piattaforme come Purple si integrano perfettamente con l'hardware esistente per fornire un accesso sicuro basato sull'identità. Gli utenti si autenticano tramite social login, email o SMS, generando una sessione unica con un registro di controllo completo, soddisfacendo i requisiti dell'Articolo 32 del GDPR per misure di sicurezza tecniche appropriate.
Fase 4: Contenere i dispositivi PSK legacy
Per i dispositivi IoT o l'hardware legacy che non supportano 802.1X, la strategia è il contenimento. Collocare tutti i dispositivi PSK su una VLAN dedicata e fortemente limitata, senza accesso alla sottorete aziendale. Abilitare l'isolamento del client per prevenire movimenti laterali tra i dispositivi. Utilizzare una passphrase complessa, generata casualmente, di 20 o più caratteri e stabilire un programma di rotazione.
Fase 5: Integrare con l'architettura di rete moderna
Le moderne implementazioni di rete devono supportare politiche di sicurezza dinamiche in tutte le sedi distribuite. L'integrazione di una robusta sicurezza WiFi con SD-WAN garantisce un'applicazione coerente delle politiche dall'edge al core. Scopri di più su The Core SD WAN Benefits for Modern Businesses .
Best Practice e Mitigazione del Rischio
La seguente tabella riassume i principali controlli di mitigazione del rischio per ciascun segmento di rete.
| Segmento di Rete | Metodo di Autenticazione | Controlli Chiave | Rilevanza per la Conformità |
|---|---|---|---|
| Personale Aziendale | WPA-Enterprise / 802.1X | RADIUS, EAP-TLS o PEAP, revoca per utente | PCI DSS Req. 8.2, ISO 27001 |
| Ospiti / Visitatori | Open SSID + Captive Portal | Acquisizione identità, limitazione della larghezza di banda, registrazione sessioni | GDPR Art. 32, PCI DSS Req. 1.3 |
| IoT / Legacy | WPA-PSK (contenuto) | VLAN isolata, isolamento client, passphrase complessa, rotazione | PCI DSS Req. 1.3, segmentazione della rete |
Oltre all'architettura, i controlli operativi sono altrettanto importanti. Configurare il proprio Wireless Intrusion Detection System (WIDS) per avvisare in caso di frame di deautenticazione eccessivi, un forte indicatore di un attacco attivo di cattura dell'handshake. Se il tuo hardware supporta WPA3, abilita la Simultaneous Authentication of Equals (SAE) su tutte le reti PSK rimanenti, poiché SAE fornisce forward secrecy e resistenza agli attacchi a dizionario offline anche in modalità PSK.
ROI e Impatto sul Business
Abbandonare WPA-PSK non è solo un aggiornamento di sicurezza; è un fattore abilitante strategico per il business con risultati misurabili.
Riduzione dell'Overhead Operativo: I ticket dell'helpdesk relativi agli aggiornamenti delle password WiFi diminuiscono significativamente quando l'identità è gestita centralmente. In una catena di negozi con 500 sedi, l'eliminazione della rotazione manuale dei PSK su migliaia di dispositivi può far risparmiare centinaia di ore IT all'anno.
Conformità e Mitigazione del Rischio: 802.1X e i captive portal gestiti forniscono i registri di controllo per utente richiesti da PCI DSS e GDPR. Il costo di una multa per non conformità PCI DSS o di una notifica di violazione dei dati GDPR supera di gran lunga l'investimento in un'infrastruttura di autenticazione adeguata.
Monetizzazione dei Dati: Il passaggio da un PSK statico a un captive portal gestito da Purple trasforma il WiFi da centro di costo a generatore di entrate. Le sedi che utilizzano la piattaforma di Purple acquisiscono dati di prima parte opt-in, consentendo campagne di marketing mirate, integrazione di programmi fedeltà e analisi approfondite della sede, inclusi tempi di permanenza, modelli di affluenza e tassi di visite ripetute.
Definizioni chiave
Pre-Shared Key (PSK)
A static passphrase of 8 to 63 characters shared between the access point and all client devices, used as the seed material for generating encryption keys.
The primary vulnerability in small business and consumer networks. When one person knows the PSK, the entire network is potentially compromised, and revocation requires a network-wide password change.
Pairwise Master Key (PMK)
A 256-bit key derived from the PSK and the network SSID using the PBKDF2 hashing algorithm, run 4,096 times.
The PMK is the top-level key in the WPA architecture. Because it incorporates the SSID, changing the network name requires recalculating the PMK on all devices.
4-Way Handshake
The cryptographic exchange where the AP and client swap nonces to independently calculate the session encryption key without transmitting the master key over the air.
The critical phase where offline dictionary attacks occur. If an attacker captures this handshake, they can attempt to crack the PSK entirely offline, with no network interaction required.
Pairwise Transient Key (PTK)
The temporary per-session encryption key generated during the 4-way handshake, used to encrypt unicast data traffic between a specific client and the AP.
Ensures that even though all users share the same PSK, they cannot easily decrypt each other's unicast traffic — though this protection is undermined if the PSK is cracked.
Message Integrity Code (MIC)
A cryptographic checksum transmitted during the handshake to prove that the sender possesses the correct PMK and has successfully calculated the PTK.
The MIC is the target of offline dictionary attacks. Attackers capture the MIC and use brute-force tools to generate matching MICs, thereby discovering the original PSK.
WPA-Enterprise / 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism requiring each user or device to authenticate individually against a RADIUS server using an EAP method.
The necessary upgrade path for enterprises moving away from WPA-PSK. Provides per-user identity, instant revocation, and a full audit trail.
Captive Portal
A web page that a user of a public-access network is required to interact with before network access is granted, typically used to capture identity, enforce terms of service, and apply access policies.
The modern alternative to providing a static PSK to guests. Enables identity capture, GDPR-compliant consent collection, bandwidth management, and marketing analytics integration.
Deauthentication Attack
A denial-of-service attack where forged 802.11 management frames are sent to force a client to disconnect from the AP, causing it to reconnect and perform a new 4-way handshake.
Used by attackers to actively generate handshake traffic for capture. Detection requires a Wireless Intrusion Detection System (WIDS) monitoring for abnormal deauthentication frame volumes.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised authentication, authorisation, and accounting (AAA) management for users connecting to a network service.
The core infrastructure component required for WPA-Enterprise deployments. Can be cloud-hosted or on-premises, and integrates with identity providers such as Active Directory, Azure AD, or Okta.
Esempi pratici
A national retail chain with 500 locations currently uses a single WPA-PSK for all point-of-sale (POS) terminals and handheld inventory scanners. They have experienced high staff turnover and are preparing for a PCI DSS compliance audit. How should the network architecture be redesigned?
- Deploy a cloud-managed RADIUS server integrated with the corporate Identity Provider (IdP), such as Azure AD or Okta.
- Configure the APs to broadcast a dedicated corporate SSID using WPA-Enterprise (802.1X).
- Provision POS terminals with EAP-TLS (certificate-based authentication) to eliminate passwords entirely — certificates are provisioned via an MDM platform.
- Provision inventory scanners using PEAP-MSCHAPv2 tied to individual employee accounts in Active Directory.
- Retire the old WPA-PSK SSID for all corporate devices.
- If legacy scanners cannot support 802.1X, isolate them on a dedicated VLAN with MAC filtering and a highly complex, unique PSK per store — and document this as a compensating control in the PCI DSS audit.
- Deploy a separate guest SSID with a captive portal for customer-facing WiFi, ensuring complete network segmentation from the corporate environment.
A large conference centre provides WiFi to attendees by printing a WPA-PSK on the back of event badges. The IT team is dealing with bandwidth exhaustion, cannot identify malicious users, and is missing out on attendee engagement data. What is the recommended deployment?
- Remove the WPA-PSK requirement and transition to an Open SSID for all attendees.
- Implement a captive portal solution (such as Purple) for guest access, requiring authentication via email, social login, or SMS validation.
- Apply per-user bandwidth throttling policies through the portal to prevent any single user from exhausting available throughput.
- Configure content filtering to block known malicious domains and peer-to-peer traffic.
- Integrate the portal with the event's CRM or marketing automation platform to capture attendee demographics and consent.
- Enable Purple's analytics dashboard to monitor real-time footfall, dwell time by zone, and return visitor rates.
- Maintain the existing WPA-Enterprise SSID for event staff and AV equipment, ensuring complete separation from the attendee network.
Domande di esercitazione
Q1. A stadium IT director proposes using a WPA-PSK network for the press box, changing the password before every match to maintain security. What is the primary operational risk of this approach, and what alternative architecture would you recommend?
Suggerimento: Consider the workflow required when a journalist arrives late, needs to connect a secondary device mid-match, or when a credential is shared beyond the intended recipients.
Visualizza risposta modello
The primary operational risk is the support bottleneck and lack of identity it creates. Every journalist must manually enter the new password, leading to support calls and delays during a time-critical event. More critically, there is no audit trail to identify which specific individual is consuming excessive bandwidth or attempting malicious activity. The recommended architecture is a dedicated SSID for accredited press using a captive portal with pre-issued credentials tied to individual media accreditation IDs, or a WPA-Enterprise SSID using PEAP tied to a temporary RADIUS account provisioned for each accredited journalist. This provides individual accountability, instant revocation, and bandwidth management per user.
Q2. During a penetration test, a tester captures the 4-way handshake of your WPA-PSK network and cracks the password offline within four hours using a GPU rig. How does migrating to WPA-Enterprise (802.1X) using PEAP prevent this specific attack vector?
Suggerimento: Consider how the authentication tunnel is established in PEAP before any user credentials are exchanged, and what an attacker would capture from the wireless frames.
Visualizza risposta modello
WPA-Enterprise using PEAP (Protected Extensible Authentication Protocol) establishes an encrypted TLS tunnel between the client and the RADIUS server before any user credentials are exchanged. The user authentication happens inside this secure tunnel. Therefore, even if an attacker captures all wireless frames during the association process, they cannot perform an offline dictionary attack against the credentials — the credentials are protected by the server's TLS certificate. The attacker would need to compromise the RADIUS server's private key to decrypt the tunnel, which is a fundamentally different and far more difficult attack surface.
Q3. A hotel chain wants to improve its guest WiFi analytics to understand dwell times and repeat visit rates, but currently uses a static WPA-PSK for all guest rooms. Why does the PSK model prevent effective analytics, and what specific data does a captive portal solution unlock?
Suggerimento: Consider what data is visible to the network when a device connects using a shared key versus an individualised portal login, and how modern mobile OS privacy features affect MAC-based tracking.
Visualizza risposta modello
WPA-PSK only authenticates the device's MAC address, which is randomised by default on iOS 14+ and Android 10+ for privacy. Because all guests share the same key, the network has no way to link a specific device to a specific guest identity. Even if MAC randomisation were not a factor, a MAC address provides no demographic or identity data. Moving to a captive portal unlocks explicit first-party data: name, email address, loyalty programme ID, marketing consent, and demographic information provided at login. This ties every session to a known user profile, enabling accurate dwell time measurement, repeat visit identification, segmented marketing campaigns, and integration with the hotel's CRM and loyalty platform.
Continua a leggere questa serie
Il Futuro della Sicurezza Wi-Fi: NAC basato su AI e Rilevamento delle Minacce
Questa guida autorevole esplora l'evoluzione della sicurezza Wi-Fi aziendale, dal WPA2 tradizionale al Network Access Control (NAC) basato su AI e al rilevamento delle minacce. Progettata per i leader IT, fornisce strategie di implementazione attuabili per la messa in sicurezza di ambienti ad alta densità come negozi al dettaglio, strutture ricettive e stadi, utilizzando le reti basate sull'identità di Purple.
Gestire la sicurezza dei dispositivi IoT con NAC e MPSK
Questa guida tecnica illustra come le aziende possano proteggere i dispositivi IoT headless utilizzando l'architettura Multiple Pre-Shared Key (MPSK) e il Network Access Control (NAC). Fornisce passaggi di implementazione pratici per ottenere la micro-segmentazione, contenere i raggi di esplosione della sicurezza e mantenere la conformità senza sacrificare la scalabilità.
RadSec: Come RADIUS su TLS migliora la sicurezza dell'autenticazione WiFi
Questo riferimento tecnico autorevole spiega come RadSec (RFC 6614) protegge l'autenticazione WiFi aziendale incapsulando il traffico RADIUS tradizionale nella crittografia TLS. Progettato per manager IT e architetti di rete, copre architettura, strategie di implementazione e passaggi pratici per mitigare i rischi del traffico RADIUS UDP non crittografato attraverso reti aziendali e guest.