Como Construir uma Rede WiFi de Campus: Um Guia de TI para Universidades
Este guia técnico fornece um plano abrangente para projetar e implementar redes WiFi de campus de alta densidade, cobrindo tudo, desde levantamentos de site ativos e posicionamento de pontos de acesso até arquitetura de controlador, roaming contínuo e onboarding seguro de convidados. É destinado a gestores de TI, arquitetos de rede e CTOs em universidades e grandes espaços que necessitam de orientação prática para planear e executar uma implementação sem fios neste trimestre. O guia também mapeia a plataforma Guest WiFi e de análise da Purple para pontos de integração reais dentro do ciclo de vida da implementação.
Listen to this guide
View podcast transcript
- Resumo Executivo
- Análise Técnica Aprofundada: Arquitetura e Normas
- A Arquitetura de Três Camadas
- Normas e Frequências Sem Fios
- Segurança e Autenticação
- Guia de Implementação: Do Levantamento à Implementação
- Fase 1: O Levantamento Ativo do Local
- Fase 2: Planeamento de Capacidade
- Fase 3: Posicionamento de AP e Planeamento de Canais
- Fase 4: Configurar Roaming Contínuo
- Fase 5: Segmentação de VLAN e Aplicação de Políticas
- Melhores Práticas para Ambientes de Campus
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio
- Ouça o Briefing

Resumo Executivo
Para equipas de TI universitárias e operadores de espaços, uma rede WiFi de campus já não é uma comodidade — é uma infraestrutura crítica. Os ambientes modernos de ensino superior exigem redes sem fios de alta densidade e alto débito, capazes de suportar múltiplos dispositivos por utilizador, aplicações que consomem muita largura de banda e mobilidade contínua em vastas áreas físicas. Este guia descreve a arquitetura técnica, as estratégias de implementação e as melhores práticas operacionais necessárias para construir uma rede sem fios de campus resiliente. Focamo-nos na implementação prática — desde o planeamento de RF e seleção de pontos de acesso (AP) até à arquitetura do controlador e onboarding seguro — garantindo que a sua implementação oferece ROI, conformidade e uma experiência de utilizador sem atritos. Quer esteja a implementar num único edifício ou num complexo multi-site, os princípios aqui aplicam-se igualmente a ambientes de Hotelaria , Retalho , Saúde e Transportes .
Análise Técnica Aprofundada: Arquitetura e Normas
Construir uma rede sem fios de campus requer uma abordagem estruturada à topologia e adesão às normas sem fios modernas. As decisões tomadas na fase de arquitetura determinam a escalabilidade, segurança e desempenho de tudo o que se segue.
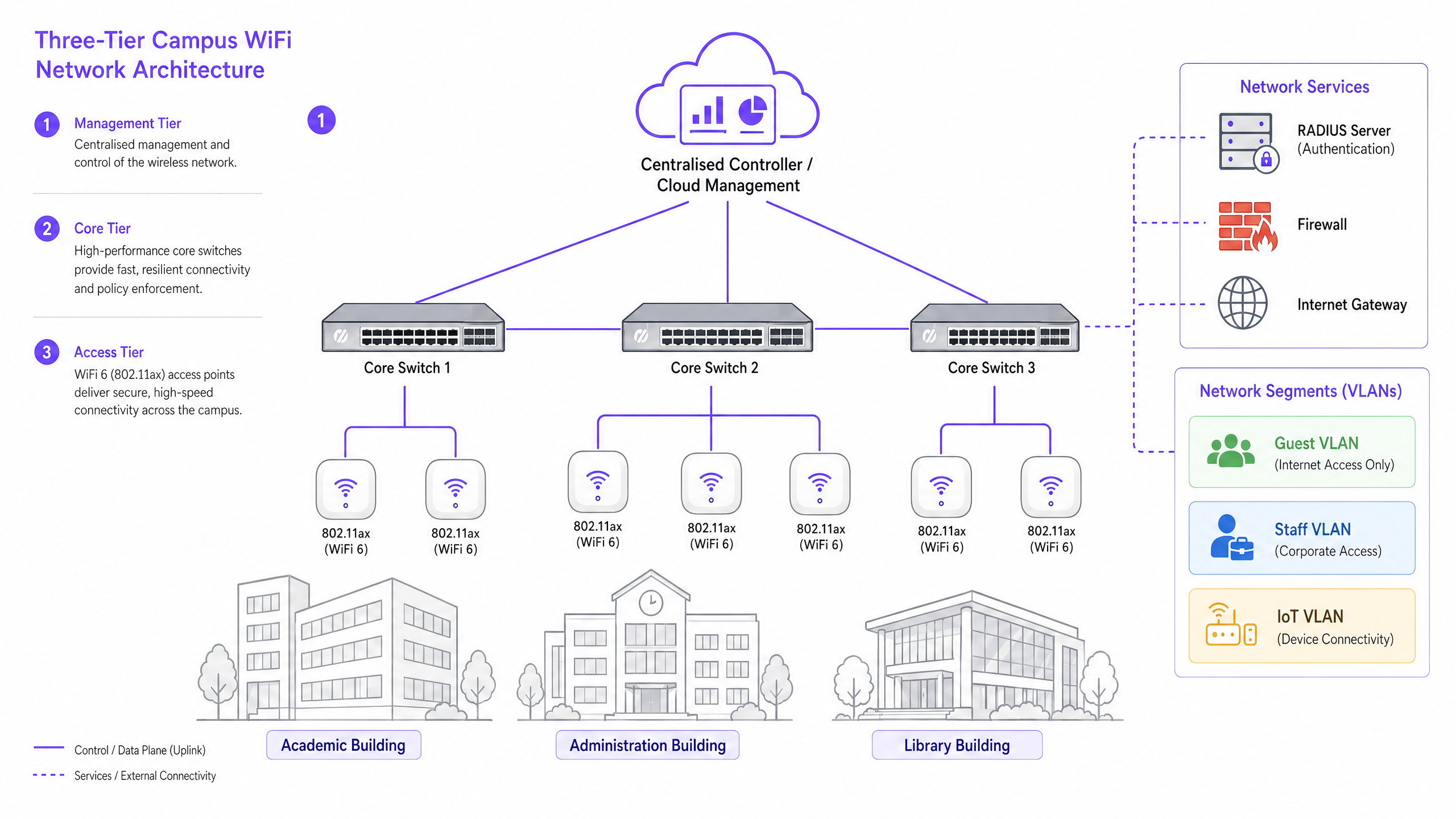
A Arquitetura de Três Camadas
As redes de campus empresariais empregam uma arquitetura hierárquica de três camadas para garantir escalabilidade, resiliência e desempenho. As três camadas são as seguintes:
Camada de Gestão/Core: O sistema nervoso central da rede. Isto inclui switches de routing core de alta capacidade e o controlador WLAN central — seja on-premise ou gerido na cloud. O controlador gere a gestão de RF, transferências de roaming, aplicação de políticas globais e gestão de firmware em todos os pontos de acesso. Os controladores geridos na cloud tornaram-se a escolha dominante para novas implementações, simplificando a gestão multi-site e reduzindo os custos de hardware on-premise.
Camada de Distribuição: Agrega o tráfego da camada de acesso, aplicando políticas de routing e garantindo redundância antes de passar os dados para o core. Em campi mais pequenos, esta camada é frequentemente colapsada no core.
Camada de Acesso: A extremidade da rede, composta por switches de borda Power over Ethernet Plus (PoE+) e os próprios Access Points (APs) sem fios. Para novas implementações, o PoE+ é o padrão mínimo, uma vez que os pontos de acesso WiFi 6 consomem significativamente mais energia do que os seus antecessores.
Normas e Frequências Sem Fios
As implementações modernas devem padronizar em 802.11ax (WiFi 6) ou WiFi 6E. O WiFi 6 introduz funcionalidades críticas de alta densidade, incluindo Orthogonal Frequency-Division Multiple Access (OFDMA), que permite que um único AP sirva múltiplos clientes simultaneamente em subcanais, e Target Wake Time (TWT), que reduz o consumo de bateria em dispositivos IoT. O WiFi 6E estende estas capacidades para a banda de 6GHz, oferecendo um espectro contíguo massivo livre de interferências de dispositivos legados — uma vantagem significativa em ambientes de alta densidade como anfiteatros e salas de conferências.
| Norma | Bandas de Frequência | Débito Máximo | Característica Chave | Melhor Caso de Uso |
|---|---|---|---|---|
| 802.11n (WiFi 4) | 2.4GHz / 5GHz | 600 Mbps | MIMO | Apenas suporte legado |
| 802.11ac (WiFi 5) | 5GHz | 3.5 Gbps | MU-MIMO | Implementações existentes |
| 802.11ax (WiFi 6) | 2.4GHz / 5GHz | 9.6 Gbps | OFDMA, TWT | Novas implementações de campus |
| 802.11ax (WiFi 6E) | 2.4 / 5 / 6GHz | 9.6 Gbps | Espectro de 6GHz | Alta densidade, à prova de futuro |
Segurança e Autenticação
A segurança deve ser multi-camadas. Para funcionários e estudantes inscritos, a autenticação 802.1X/EAP ligada ao provedor de identidade da universidade (Active Directory, LDAP, ou um serviço de identidade na cloud) é obrigatória. Isto fornece acesso encriptado baseado em credenciais que cumpre os requisitos de normas como ISO 27001 e Cyber Essentials. Para utilizadores transitórios — académicos visitantes, delegados de conferências e membros do público — é necessário um captive portal seguro. A integração de uma solução robusta de Guest WiFi garante onboarding compatível com GDPR, páginas de splash personalizáveis e a capacidade de recolher insights acionáveis através de WiFi Analytics . Todo o tráfego sem fios deve ser encriptado usando WPA3, o padrão atual, que oferece proteções mais fortes contra ataques de força bruta do que o seu predecessor WPA2. Para uma revisão abrangente da postura de segurança dos pontos de acesso, consulte o nosso Segurança de Pontos de Acesso: O Seu Guia Empresarial para 2026 .
Guia de Implementação: Do Levantamento à Implementação
Implementar uma rede de campus é um processo faseado que requer um planeamento meticuloso antes de um único cabo ser passado ou um AP ser montado.
Fase 1: O Levantamento Ativo do Local
Um levantamento preditivo usando plantas é insuficiente para ambientes de campus complexos. Deve realizar levantamentos de RF ativos e no local. Os materiais de construção em universidades mais antigas — alvenaria espessa, ripas metálicas, betão armado — atenuam os sinais de forma imprevisível. O levantamento identifica "buracos negros" de RF e ajuda a determinar o posicionamento ideal dos APs para garantir cobertura e capacidade. O resultado deve ser um mapa de calor validado mostrando a intensidade do sinal, a utilização do canal e os níveis de interferência em cada piso.
Fase 2: Planeamento de Capacidade
Historicamente, as redes eram projetadas para cobertura — garantindo que um sinal chegava a todos os cantos. Hoje, o design é para capacidade. Num anfiteatro com 300 lugares, assuma três dispositivos por estudante: portátil, smartphone e tablet. Isto requer a implementação de APs de alta densidade com antenas direcionais para setorizar a sala, em vez de depender de um único AP omnidirecional que rapidamente ficará sobrecarregado. A regra geral para implementações de alta densidade é um AP por 25-30 utilizadores simultâneos num ambiente de aula.
Fase 3: Posicionamento de AP e Planeamento de Canais
Um planeamento cuidadoso dos canais é essencial para minimizar a Interferência Co-Canal (CCI). Utilize canais não sobrepostos (1, 6, 11 em 2.4GHz; alocação dinâmica em 5GHz e 6GHz). Certifique-se de que os APs são colocados estrategicamente — evite montá-los acima de tetos falsos ou atrás de condutas de AVAC, o que degrada o desempenho. Para ambientes com tetos altos, utilize APs com antenas direcionais viradas para baixo.
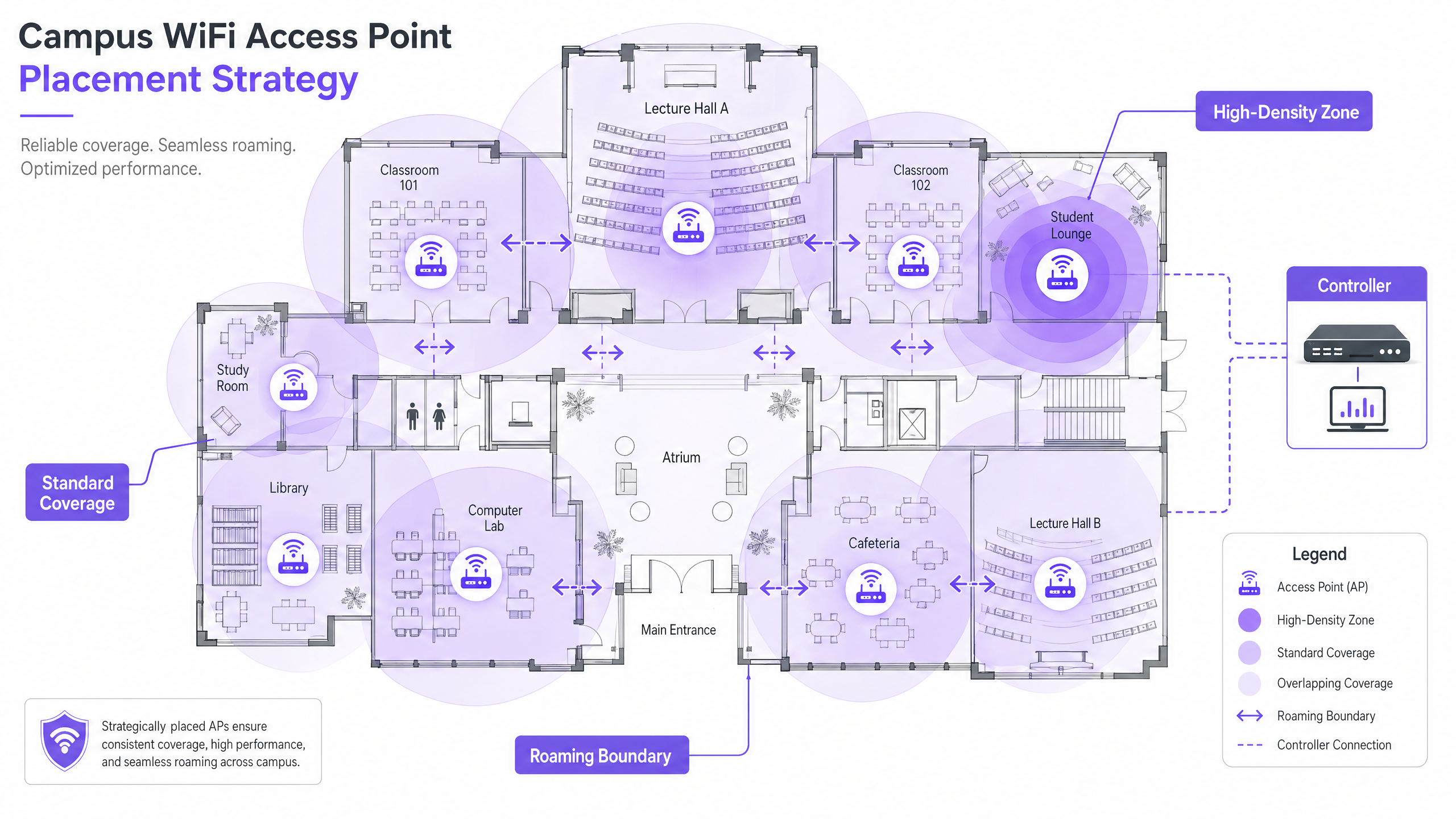
Fase 4: Configurar Roaming Contínuo
À medida que os utilizadores se deslocam entre edifícios, a sua ligação deve ser transferida de forma contínua entre os APs. Implemente a trifeta de roaming rápido: 802.11k (relatórios de vizinhos), 802.11v (gestão de transição BSS) e 802.11r (transição BSS rápida). Juntos, estes padrões permitem que os dispositivos cliente tomem decisões de roaming inteligentes e completem as transferências de autenticação em milissegundos em vez de segundos — crucial para VoIP e aplicações em tempo real.
Ajustar a potência de transmissão é igualmente importante. Se a potência de Tx for demasiado alta, os dispositivos cliente irão "agarrar-se" a um AP distante ('clientes pegajosos') em vez de fazerem roaming para um mais próximo. Reduza a potência de Tx para criar células de cobertura sobrepostas, mas com o tamanho adequado, e desative as taxas de dados legadas (1, 2, 5.5 Mbps) para forçar os dispositivos a abandonar ligações fracas e a fazer roaming.
Fase 5: Segmentação de VLAN e Aplicação de Políticas
Crie VLANs dedicadas para cada classe de utilizador: Pessoal, Estudantes, Convidados e dispositivos IoT. Os dispositivos IoT — sistemas de gestão de edifícios, câmaras de segurança, sinalização digital — nunca devem partilhar um segmento de rede com dispositivos de utilizador. Aplique regras de firewall rigorosas entre VLANs, permitindo apenas a comunicação mínima necessária. Para segurança ao nível de DNS e proteção contra domínios maliciosos, consulte o nosso guia sobre como Proteger a Sua Rede com DNS e Segurança Robustos .
Melhores Práticas para Ambientes de Campus
As seguintes recomendações neutras em relação ao fornecedor representam a prática padrão da indústria para grandes implementações de redes sem fios.
Band Steering: Force os dispositivos cliente capazes para as bandas menos congestionadas de 5GHz ou 6GHz, reservando a banda de 2.4GHz para dispositivos legados e sensores IoT de longo alcance. A maioria dos controladores modernos suporta band steering automático.
Limiares Mínimos de RSSI: Configure o controlador para recusar ligações de clientes cuja força de sinal caia abaixo de um limiar definido (tipicamente -75 dBm). Isto evita que clientes com sinal fraco degradem a experiência para todos os outros utilizadores no AP.
Prevenção de Intrusões Sem Fios (WIPS): Ative o WIPS no controlador para detetar e suprimir APs não autorizados — routers pessoais ligados por estudantes ou funcionários que causam interferência e introduzem vulnerabilidades de segurança.
Cobertura Exterior: Estenda a rede a pátios e áreas de estar exteriores utilizando APs robustos e à prova de intempéries com antenas direcionais. Os APs exteriores devem suportar temperaturas extremas, humidade e resistência ao vandalismo.
Gestão de Concessões DHCP: Em áreas de alta rotatividade (cafetarias, bibliotecas), reduza os tempos de concessão DHCP para redes de convidados para uma a duas horas para evitar o esgotamento de endereços IP.
O foco da Purple no ensino superior está a crescer rapidamente — leia sobre a entrada do nosso VP de Educação Tim Peers na equipa e o que isso significa para a estratégia de rede do campus.
Resolução de Problemas e Mitigação de Riscos
Mesmo redes bem projetadas encontram problemas operacionais. Os seguintes são os modos de falha mais comuns e as suas mitigações.
| Modo de Falha | Sintomas | Causa Raiz | Mitigação |
|---|---|---|---|
| Clientes Pegajosos | Desempenho fraco apesar de sinal forte | Potência de Tx demasiado alta; taxas legadas ativadas | Reduzir potência de Tx; desativar taxas abaixo de 11 Mbps |
| Esgotamento de DHCP | Utilizadores incapazes de ligar | Tempos de concessão demasiado longos; sub-rede demasiado pequena | Reduzir tempos de concessão; expandir sub-redes |
| Interferência Co-Canal | Débito lento em todo o piso | Mau planeamento de canais | Implementar atribuição dinâmica de canais |
| APs Não Autorizados | Interferência; alertas de segurança | Routers pessoais não autorizados | Ativar WIPS; realizar auditorias RF regulares |
| Falhas de Autenticação | Utilizadores incapazes de iniciar sessão | Sobrecarga ou má configuração do servidor RADIUS | Implementar RADIUS redundante; monitorizar registos de autenticação |
ROI e Impacto no Negócio
Para a liderança universitária e diretores de operações de espaços, o ROI de uma rede de alto desempenho estende-se muito além da conectividade básica. Uma rede sem fios robusta no campus suporta diretamente ferramentas pedagógicas modernas, iniciativas de campus digital e programas de eficiência operacional.
Aproveitar o WiFi Analytics fornece inteligência acionável sobre o fluxo de pessoas, tempos de permanência e utilização do espaço. Estes dados podem informar decisões imobiliárias — identificando edifícios subutilizados ou espaços de pico de procura — e otimizar o uso de AVAC com base em dados reais de ocupação, proporcionando poupanças de energia mensuráveis. Estas são as mesmas estratégias de análise implementadas por operadores em ambientes de Retalho e Hotelaria , agora cada vez mais aplicadas a ambientes de campus.
Para organizações que implementam guest WiFi como parte de uma estratégia mais ampla de envolvimento digital, uma plataforma de Guest WiFi bem configurada também pode suportar automação de marketing, envolvimento de ex-alunos e programas de experiência do visitante. Para locais de campus mais pequenos ou satélites, o nosso guia sobre Como Configurar um Hotspot WiFi para o Seu Negócio fornece um ponto de partida prático.
Ouça o Briefing
Key Definitions
802.11ax (WiFi 6)
The current IEEE standard for wireless networking, designed specifically to improve efficiency and performance in high-density environments through OFDMA, MU-MIMO, and TWT.
Essential for modern campus deployments to support a high volume of concurrent devices without performance degradation.
Co-Channel Interference (CCI)
Interference that occurs when multiple access points in the same area operate on the same channel, causing devices to wait for clear airtime before transmitting.
Poor channel planning leads to high CCI, which severely degrades network throughput even when signal strength is strong.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices, isolating their traffic from other devices on the same physical network infrastructure.
Crucial for security and performance; separating guest, staff, student, and IoT traffic prevents lateral movement and reduces congestion.
802.1X
An IEEE standard for port-based Network Access Control, providing a credential-based authentication mechanism for devices connecting to a LAN or WLAN via a RADIUS server.
The mandatory standard for secure, enterprise-grade authentication for staff and enrolled students on campus networks.
Captive Portal
A web page that a user of a public-access network must interact with before network access is granted, typically used for terms of service acceptance, authentication, and data capture.
Used for guest onboarding on campus networks; must be GDPR-compliant and integrated with an analytics platform for operational value.
OFDMA (Orthogonal Frequency-Division Multiple Access)
A multi-user version of OFDM that allows a single access point to simultaneously serve multiple clients on different sub-channels within the same transmission.
A key WiFi 6 feature that dramatically improves efficiency in high-density environments like lecture halls.
Sticky Client
A wireless device that remains connected to a distant AP with a weak signal, even when a closer AP with a stronger signal is available, due to the client's reluctance to initiate a roam.
Causes poor performance for the affected user and unnecessary load on the distant AP; mitigated by proper RF tuning and disabling legacy data rates.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, typically expressed in dBm (decibels relative to one milliwatt), where values closer to zero indicate a stronger signal.
Used during site surveys to determine coverage boundaries and during controller configuration to set minimum connection thresholds.
PoE+ (Power over Ethernet Plus)
An IEEE 802.3at standard that delivers up to 30 watts of power over standard Ethernet cabling, sufficient to power WiFi 6 access points without a separate power supply.
The minimum PoE standard required for new campus deployments using WiFi 6 APs.
Worked Examples
A Russell Group university is upgrading a Grade II listed, 19th-century library to support 500 concurrent student connections. The building features thick stone walls, high ceilings, and ornate internal partitions. How should the IT team approach the wireless deployment?
Step 1: Commission an active, on-site RF survey — predictive modelling will be highly inaccurate due to the stone walls and irregular floor plan. Use professional wifi survey software to generate validated heat maps. Step 2: Deploy high-density WiFi 6 APs with directional patch antennas focused downward into reading areas, avoiding signal bounce off high ceilings. Target one AP per 25 concurrent users. Step 3: Implement a dedicated VLAN for student access via 802.1X linked to the university's Active Directory, and a separate guest VLAN with a captive portal for visiting researchers and public users. Step 4: Tune AP transmit power to create appropriately sized coverage cells, preventing sticky clients as students move between reading rooms. Step 5: Disable legacy data rates (1, 2, 5.5 Mbps) to enforce roaming. Step 6: Deploy a cloud-managed controller for centralised visibility and RF optimisation.
A Premier League football stadium needs to provide WiFi coverage for 40,000 concurrent connections on match days, with a secondary requirement for event-day analytics on fan movement and dwell times.
Step 1: Deploy under-seat APs with highly directional antennas to create micro-cells for specific seating sections — this is the only viable approach at this density. Step 2: Disable 2.4GHz radios on the majority of APs to eliminate Co-Channel Interference in the dense RF environment; force all traffic to 5GHz and 6GHz. Step 3: Enable 802.11k/v/r to facilitate rapid roaming as fans move through concourses during half-time. Step 4: Implement a captive portal via Purple's Guest WiFi platform for secure, high-throughput onboarding, capturing opt-in analytics data on fan movement and dwell times. Step 5: Segment the network with separate VLANs for fans, operations staff, broadcast equipment, and point-of-sale systems. Step 6: Ensure PCI DSS compliance on the payment network segment.
Practice Questions
Q1. You are deploying APs in a new university dormitory block. The building has long central corridors with student rooms on either side, separated by solid concrete walls. Should you place APs in the central corridors or inside the individual dorm rooms?
Hint: Consider the attenuation caused by concrete walls and fire doors, and the capacity required per room.
View model answer
Deploy APs inside the dorm rooms, using wall-plate APs that mount flush to the wall and connect via the in-room Ethernet port. Corridor deployments result in poor signal penetration into rooms due to concrete walls and heavy fire doors, and fail to provide the per-room capacity needed for multiple devices per student. Wall-plate APs provide a dedicated, high-quality connection for each room and are the industry-standard approach for student accommodation.
Q2. Users in the university cafeteria are reporting slow WiFi speeds during the lunch period, despite their devices showing full signal strength bars. What are the two most likely causes, and how would you investigate each?
Hint: Signal strength does not equal capacity. Consider both the RF environment and the number of concurrent users.
View model answer
The two most likely causes are: (1) AP capacity overload — the APs are overwhelmed by the sheer number of concurrent devices during the lunch rush. Investigate by checking the controller dashboard for client counts per AP and throughput utilisation. If APs are serving 80+ clients, additional APs or a high-density AP upgrade is required. (2) Co-Channel Interference — multiple APs in the cafeteria are operating on the same channel, causing devices to wait for clear airtime. Investigate using a spectrum analyser or the controller's RF health dashboard. Resolve by enabling dynamic channel assignment and ensuring non-overlapping channel allocation.
Q3. Your university is hosting a major international conference with 800 delegates, all of whom will need WiFi access for three days. The conference is held in a building that normally serves 200 staff. How do you approach the temporary network uplift?
Hint: Consider both the temporary capacity increase and the security separation between conference delegates and permanent staff.
View model answer
Deploy temporary high-density APs in the main conference hall and breakout rooms, connected to the existing switching infrastructure via temporary PoE+ switches if port capacity is insufficient. Create a dedicated conference VLAN, completely isolated from the staff network, with its own DHCP scope and internet breakout. Deploy a branded captive portal via a guest WiFi platform for delegate onboarding, capturing opt-in data for post-event analytics. Reduce DHCP lease times to two hours to manage IP address churn across the three-day event. After the conference, remove temporary APs and decommission the conference VLAN.