How to Implement Post-Admission NAC for Continuous Trust Monitoring
This guide provides an authoritative technical blueprint for implementing Post-Admission Network Access Control (NAC) with Continuous Trust Monitoring across enterprise venues including hospitality, retail, healthcare, and public-sector environments. It details the architectural shift from static pre-admission checks to dynamic, session-aware enforcement using RADIUS CoA, behavioural baselining, and telemetry integration. IT architects and network operations teams will find actionable deployment guidance, real-world case studies, compliance alignment notes, and measurable ROI frameworks.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Shift from Pre-Admission to Post-Admission
- Core Components of a Continuous Trust Monitoring Architecture
- Standards and Protocol References
- Implementation Guide
- Phase 1: Visibility and Baselining (Weeks 1–4)
- Phase 2: Policy Development and Testing (Weeks 5–6)
- Phase 3: Graduated Enforcement Rollout (Weeks 7–10)
- Phase 4: Full Production and Continuous Optimisation
- Best Practices
- Troubleshooting & Risk Mitigation
- CoA Failures
- False Positives and Operational Disruption
- Scale and Throughput
- Vendor Lock-In
- ROI & Business Impact

Executive Summary
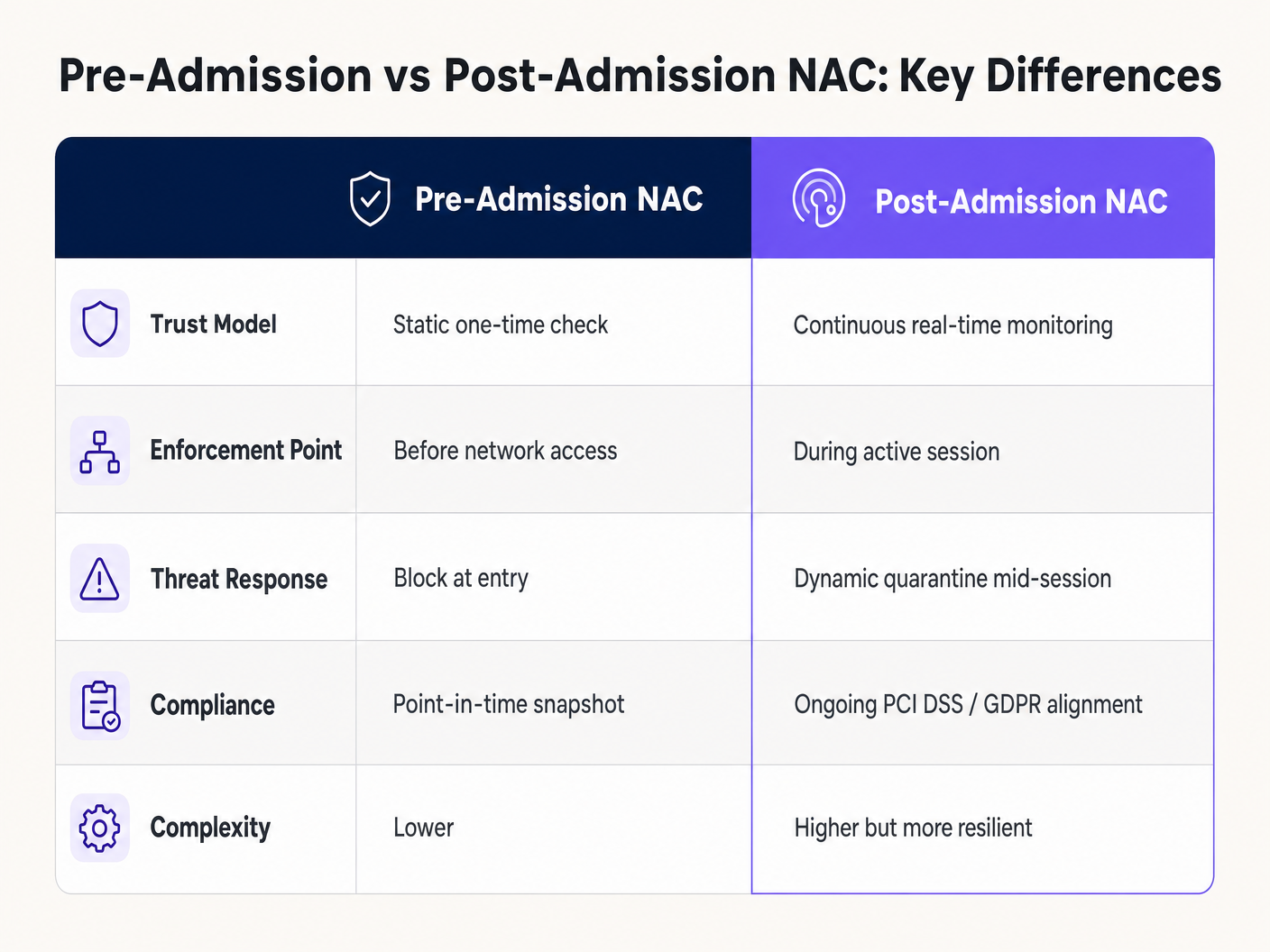
For enterprise networks in high-density environments — hospitality, retail, stadiums, and public-sector venues — traditional pre-admission Network Access Control is no longer sufficient. Static, point-in-time authentication checks cannot account for devices that become compromised or exhibit malicious behaviour after they have been granted network access. A device may authenticate cleanly against an 802.1X policy engine and then, minutes later, begin scanning internal subnets or exfiltrating data.
Post-Admission NAC shifts the security paradigm from "authenticate and trust" to Continuous Trust Monitoring. By continuously evaluating device posture, traffic patterns, and session context against established behavioural baselines, IT and network operations teams can dynamically enforce policies mid-session using RADIUS Change of Authorization (CoA). This guide provides a practical, vendor-neutral blueprint for implementing Post-Admission NAC. It covers architectural considerations, integration with Guest WiFi and WiFi Analytics platforms, and actionable deployment strategies that mitigate risk without disrupting the user experience.
Technical Deep-Dive
The Shift from Pre-Admission to Post-Admission
Traditional NAC relies on IEEE 802.1X, MAC Authentication Bypass (MAB), or captive portals to verify identity and posture before granting access. Once admitted, the device typically enjoys unimpeded access to its assigned VLAN or micro-segment for the duration of the session. This model has a fundamental flaw: it treats admission as a binary, one-time event. The threat landscape does not operate on that basis.
Post-Admission NAC introduces a dynamic policy engine that monitors the active session continuously. If a device begins scanning internal subnets, generating unusual traffic volumes, or attempting to communicate with known command-and-control (C2) servers, the NAC solution dynamically alters the device's network privileges. This is achieved through Change of Authorization (CoA) requests via RADIUS (RFC 5176), API integrations with wireless LAN controllers (WLCs), or direct integration with SD-WAN fabrics — a topic explored in depth in the SD WAN vs MPLS: The 2026 Enterprise Network Guide .
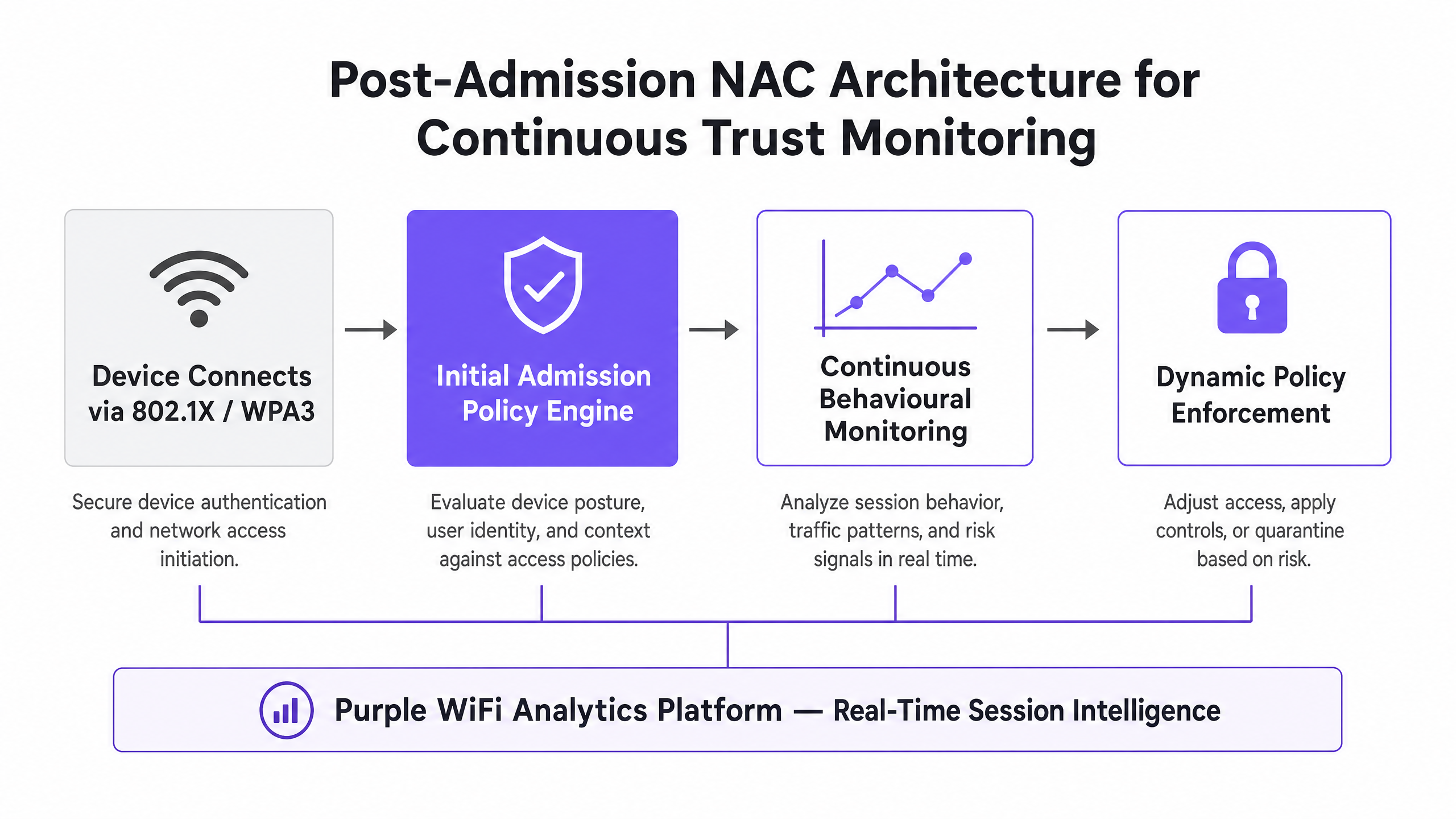
Core Components of a Continuous Trust Monitoring Architecture
A production-grade Post-Admission NAC deployment requires four integrated components working in concert.
Telemetry Ingestion is the foundation. The system must ingest real-time data from WLCs, switches, firewalls, and endpoint detection and response (EDR) agents. This includes NetFlow/IPFIX data, RADIUS accounting records, DNS request logs, and application visibility metrics from deep packet inspection (DPI) engines. Without comprehensive telemetry, the policy engine is operating blind.
Behavioural Analytics Engine processes the telemetry stream and compares it against established baselines. Machine learning models are increasingly used to automate baseline construction and anomaly scoring, reducing the manual configuration burden. For a detailed look at how AI is transforming this space, refer to The Future of Wi-Fi Security: AI-Driven NAC and Threat Detection and its Spanish-language counterpart El Futuro de la Seguridad Wi-Fi: NAC Impulsado por IA y Detección de Amenazas .
Dynamic Policy Enforcement is the operational output. The ability to issue RADIUS CoA to bounce a port, change a VLAN assignment, or apply a restrictive Access Control List (ACL) in real-time is what differentiates Post-Admission NAC from a passive monitoring system. Without reliable CoA, you have an alerting system, not an enforcement system.
Integration Layer connects the NAC engine to the broader security ecosystem: SIEM platforms for event correlation, threat intelligence feeds for known-bad IP enrichment, and identity providers for user-context enrichment. In guest-facing environments, the WiFi Analytics platform provides session-level context that significantly enriches policy decisions.
Standards and Protocol References
| Standard | Relevance to Post-Admission NAC |
|---|---|
| IEEE 802.1X | Foundation for port-based authentication; provides the identity binding that NAC policies reference |
| RFC 5176 (RADIUS CoA) | The protocol mechanism for mid-session policy enforcement |
| WPA3-Enterprise | Provides stronger cryptographic protection for the 802.1X authentication exchange |
| PCI DSS v4.0 | Requires continuous monitoring of network access and automated response capabilities |
| GDPR Article 32 | Mandates appropriate technical measures to ensure ongoing confidentiality and integrity |
| NIST SP 800-207 | Zero Trust Architecture framework that Post-Admission NAC directly implements |
Implementation Guide
Deploying Post-Admission NAC requires a phased approach to avoid widespread network disruption. Attempting to enable active enforcement immediately is the single most common cause of failed deployments.
Phase 1: Visibility and Baselining (Weeks 1–4)
Deploy the NAC solution in monitor-only mode. No enforcement actions should be configured at this stage.
Begin by ensuring all Network Access Devices are sending RADIUS accounting data and flow telemetry to the NAC policy engine. Configure NetFlow or IPFIX export on all managed switches and WLCs. Verify that the NAC engine is receiving and parsing records correctly before proceeding.
Allow the system to observe traffic patterns across different device profiles. This is particularly critical in Healthcare environments where medical IoT devices have highly predictable traffic patterns, and in Retail environments where point-of-sale terminals have well-defined communication requirements. The baselining period should cover at least one full business cycle — typically four weeks — to capture weekend versus weekday variation.
Phase 2: Policy Development and Testing (Weeks 5–6)
With baselines established, develop risk-based policies. Define explicit quarantine triggers based on business risk rather than purely technical indicators.
For a retail environment, a critical trigger might be: any traffic from the Guest VLAN attempting to route to the POS VLAN subnet. For a hospitality environment, it might be: any device generating more than 500 SMB connection attempts per minute. For a healthcare environment: any device authenticated via MAB communicating with an external IP address outside its approved destination list.
Test each policy in a lab environment by simulating the trigger condition. Verify that the NAC engine correctly identifies the anomaly, generates the CoA request, and that the NAD applies the new policy within an acceptable time window (typically under 500 milliseconds for critical triggers).
Phase 3: Graduated Enforcement Rollout (Weeks 7–10)
Enable active enforcement on a low-risk network segment first. A staff-only IoT VLAN is typically a good starting point, as false positives have limited operational impact compared to a guest or clinical network.
Begin with a graduated enforcement response. Rather than immediately disconnecting a device, apply a restrictive ACL that permits basic internet access (HTTP/HTTPS to approved destinations) but blocks all internal routing. This reduces the impact of false positives while still containing the threat. Monitor the quarantine queue daily and adjust thresholds as needed.
Expand enforcement to additional segments incrementally, validating each before proceeding. Ensure that RADIUS CoA is functioning reliably — UDP port 3799 must be open between the NAC engine and all NADs, and shared secrets must be consistent. In Transport hub deployments, where network segments may span multiple physical locations, validate CoA response times across WAN links.
Phase 4: Full Production and Continuous Optimisation
Once all segments are under active enforcement, establish an ongoing optimisation cadence. Review quarantine events weekly, identify recurring false positives, and refine baselines accordingly. Integrate the NAC event stream with your SIEM for cross-correlation with endpoint and perimeter security events.
For Hospitality deployments, consider seasonal baseline adjustments — a hotel network in peak summer season will have materially different traffic patterns from the same network in January. Static baselines will generate elevated false positives during peak periods if not updated.
Best Practices
Standardise on 802.1X Where Possible. While MAB is necessary for headless IoT devices, 802.1X provides stronger cryptographic identity binding. Ensure WPA3-Enterprise is utilised where supported. Understanding the underlying RF environment is essential — review Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 to ensure your spectrum design supports the management overhead of continuous monitoring.
Leverage Micro-Segmentation as a Companion Control. Combine Post-Admission NAC with network micro-segmentation. If a device is compromised and the CoA response is delayed for any reason, micro-segmentation limits the blast radius to the device's own segment. The two controls are complementary, not redundant.
Align Enforcement Policies with Compliance Mandates. Ensure your continuous monitoring and automated response procedures are documented for auditors. PCI DSS v4.0 Requirement 10 mandates logging and monitoring of all access to network resources. GDPR Article 32 requires ongoing confidentiality and integrity measures. Post-Admission NAC directly satisfies both, but only if the audit trail is preserved and the automated response procedures are formally documented.
Consider BLE for Physical Context Enrichment. In environments where physical presence matters — such as a conference centre or retail floor — integrating BLE beacon data can enrich the NAC policy engine's context. A device authenticated on the network but physically located in a restricted area is a higher-risk signal than the same device in a public zone. See BLE Low Energy Explained for Enterprise for implementation guidance.
Troubleshooting & Risk Mitigation
CoA Failures
The most common issue in Post-Admission NAC deployments is the failure of the NAD to process a RADIUS CoA request. Symptoms include: the NAC engine logs a successful CoA transmission, but the client device remains on the network with unchanged access. Diagnose by capturing traffic on UDP port 3799 at the NAD. Common causes include firewall rules blocking the CoA port, mismatched RADIUS shared secrets, or the NAD not having CoA explicitly enabled in its configuration. Always validate CoA in a controlled test before production rollout.
False Positives and Operational Disruption
Overly aggressive behavioural baselines lead to legitimate devices being quarantined. This is particularly problematic in hospitality environments where guest devices exhibit unppredictable behaviour — streaming video, VPN usage, and cloud backup operations can all trigger anomaly thresholds if baselines are too narrow. Always use a graduated enforcement approach and maintain a whitelist process for known-good devices that regularly trigger alerts.
Scale and Throughput
Continuous monitoring generates significant telemetry. In a stadium or large conference centre with 10,000 concurrent sessions, the NAC policy engine and logging infrastructure must be scaled to handle the ingest rate without dropping records. Dropped telemetry creates blind spots. Size your infrastructure based on peak concurrent session counts, not average, and implement telemetry buffering at the collector layer to handle burst conditions.
Vendor Lock-In
Some NAC vendors implement proprietary CoA extensions that only function with their own hardware ecosystem. Ensure your NAC policy engine supports standard RFC 5176 CoA and that your NADs are on the vendor's tested compatibility matrix before committing to a deployment architecture.
ROI & Business Impact
Implementing Post-Admission NAC delivers measurable business value that extends well beyond security compliance.
Reduced Mean Time to Respond (MTTR): Automated quarantine reduces MTTR from hours — or days in environments without dedicated SOC teams — to milliseconds. For a retail chain with 500 locations, this means a compromised device at a branch is contained before it can reach the POS network, regardless of whether a network engineer is on-site.
Operational Efficiency: Network operations teams spend significantly less time manually hunting down compromised devices. Automated quarantine and detailed audit logs reduce the investigation burden and accelerate post-incident reporting.
Brand and Revenue Protection: In public-facing environments, preventing a guest device from becoming a launchpad for a wider breach protects the venue's reputation. A data breach in a hotel or retail environment carries both regulatory penalties under GDPR and significant reputational damage that directly impacts revenue.
Compliance Cost Reduction: Automated, continuous monitoring with a preserved audit trail reduces the cost and effort of compliance audits. Demonstrating to a PCI QSA that your network has automated, real-time response capabilities is materially easier than presenting manual process documentation.
Key Definitions
Post-Admission NAC
The continuous monitoring and dynamic enforcement of security policies on a device after it has been granted initial network access, as opposed to pre-admission checks which occur only at the point of connection.
Crucial for identifying devices that become compromised mid-session or exhibit malicious behaviour that was not apparent during the initial authentication phase. Directly relevant to any environment with guest or unmanaged device access.
Continuous Trust Monitoring
A security model in which trust is never permanently assumed; a device's posture, behaviour, and context are continuously evaluated against established baselines throughout the duration of its network session.
The operational philosophy underpinning Post-Admission NAC, and a direct implementation of NIST SP 800-207 Zero Trust Architecture principles.
Change of Authorization (CoA)
A RADIUS extension defined in RFC 5176 that allows a policy server to dynamically modify the session authorisation attributes of an active network client, including changing VLAN assignment, applying ACLs, or terminating the session entirely.
The technical enforcement mechanism that distinguishes Post-Admission NAC from passive monitoring. If CoA is not functioning, the system cannot enforce dynamic policies mid-session.
Behavioural Baselining
The process of establishing a statistically normal pattern of network activity for a specific device type, user role, or network segment over a defined observation period.
The foundation of anomaly detection in Post-Admission NAC. Baselines that are too narrow generate false positives; baselines that are too broad miss genuine threats. Typically requires a minimum of four weeks of observation across a full business cycle.
MAC Authentication Bypass (MAB)
A network access method that grants access based solely on a device's MAC address, typically used for headless IoT devices that cannot support 802.1X EAP authentication.
Inherently vulnerable to MAC spoofing attacks. Post-Admission NAC with device profiling is essential to secure any environment that relies on MAB, particularly healthcare and industrial IoT deployments.
Network Access Device (NAD)
The physical hardware component — typically a managed switch, wireless LAN controller, or VPN gateway — that enforces access policies at the edge of the network and receives CoA instructions from the NAC policy engine.
The NAD is the enforcement point. Its compatibility with RFC 5176 CoA and the reliability of its CoA processing are critical factors in any Post-Admission NAC architecture.
Telemetry
The automated, real-time collection and transmission of network operational data — including NetFlow/IPFIX records, RADIUS accounting data, syslog events, and SNMP traps — from network devices to a centralised analytics engine.
Provides the raw data stream required for the NAC behavioural analytics engine to operate. Gaps in telemetry coverage create blind spots where compromised devices can operate undetected.
Micro-Segmentation
The network architecture practice of dividing a network into small, isolated segments with granular access controls between them, limiting the lateral movement of an attacker or compromised device.
A complementary control to Post-Admission NAC. If a CoA enforcement action is delayed, micro-segmentation limits the blast radius of a compromised device to its own segment, preventing it from reaching critical assets on adjacent segments.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect to and use a network service.
The foundational protocol for both initial admission (Access-Request/Accept) and post-admission enforcement (CoA). Most enterprise NAC deployments are built on a RADIUS infrastructure.
Worked Examples
A large retail chain deploying Guest WiFi across 500 locations needs to ensure that compromised guest devices cannot scan or reach the Point of Sale (POS) network. The IT team has limited on-site resource and needs an automated, centrally managed solution. How should they implement Post-Admission NAC?
- Deploy a cloud-hosted NAC policy engine with a distributed telemetry collector at each branch, avoiding the need for on-site NAC hardware.
- Configure all branch WLCs and switches to send RADIUS accounting records and NetFlow data to the central NAC engine via encrypted tunnels.
- Define a four-week baselining period covering both weekday and weekend traffic patterns for the Guest VLAN.
- Create a critical violation policy: if any traffic from the Guest VLAN subnet attempts to route to the POS VLAN subnet (defined by IP range), the NAC engine immediately issues a RADIUS CoA to the local WLC.
- The CoA instructs the WLC to apply a 'Quarantine' ACL to the specific client MAC address, dropping all traffic except DHCP and DNS, effectively isolating the device mid-session.
- Configure an automated alert to the central NOC and log the event to the SIEM for post-incident analysis.
- Validate CoA functionality at 10 pilot sites before rolling out to all 500 locations.
A hospital network has thousands of headless medical IoT devices using MAC Authentication Bypass (MAB) for initial access. The security team is concerned about MAC spoofing attacks and the inability to detect compromised devices mid-session. How can Post-Admission NAC mitigate these risks?
- Deploy a NAC solution with device profiling capabilities that can ingest DHCP fingerprints, HTTP user agents, and traffic flow characteristics.
- During the baselining phase, build a profile for each device type: an infusion pump communicates with a specific internal server on port 443 at regular intervals; a patient monitoring system communicates with a nursing station on a specific internal subnet.
- Configure violation policies based on profile deviation: if a device authenticated via MAB as an infusion pump begins communicating with any external IP address, or initiates more than 10 connections per minute to non-approved internal destinations, trigger a quarantine.
- Issue a RADIUS CoA to the switch to move the port to a quarantine VLAN, isolating the device from the clinical network while preserving connectivity for investigation.
- Alert the clinical engineering team and the SOC simultaneously, providing the device MAC address, switch port, and the specific traffic anomaly that triggered the response.
Practice Questions
Q1. Your network operations team reports that the new Post-Admission NAC deployment is generating a high volume of false positives, quarantining legitimate guest devices in a busy hotel lobby. The guest services team is escalating complaints. What is the most appropriate immediate action, and what longer-term remediation should you plan?
Hint: Consider the phases of deployment and the specific traffic characteristics of a hospitality guest network.
View model answer
Immediately revert the enforcement policy from Active Quarantine to Monitor Only, or apply a less restrictive graduated enforcement ACL that limits internal routing without disconnecting the device. Review the behavioural baselines specifically for the Guest VLAN — hospitality environments have inherently unpredictable guest traffic including VPN usage, streaming services, and cloud backup. Extend the baselining period and widen the anomaly thresholds before re-enabling active enforcement. Longer-term, implement seasonal baseline adjustments and consider a tiered enforcement model where guest devices receive a less aggressive response than corporate or IoT devices.
Q2. During a pilot deployment, the NAC policy engine successfully detects anomalous behaviour and logs the event with a high-confidence anomaly score, but the client device remains on the network with unchanged access. The NOC receives the alert but no quarantine action has been applied. What is the most likely technical failure, and how do you diagnose it?
Hint: Think about the specific protocol and port used for mid-session enforcement.
View model answer
The most likely failure is that RADIUS Change of Authorization (CoA) is not functioning correctly between the NAC engine and the Network Access Device. Diagnose by capturing traffic on UDP port 3799 at the NAD to confirm whether the CoA packet is arriving. If it is arriving but being rejected, check the RADIUS shared secret configuration on both the NAC engine and the NAD. If it is not arriving, check firewall rules between the NAC engine and the NAD. Also verify that CoA is explicitly enabled in the NAD's RADIUS client configuration — many devices require a separate configuration statement to accept CoA requests.
Q3. A large conference centre is planning a Post-Admission NAC deployment ahead of a major trade show with an expected 8,000 concurrent WiFi users. The IT director is concerned about the telemetry infrastructure being overwhelmed during peak load. How should the architecture be designed to handle this scale?
Hint: Consider the difference between raw telemetry volume and processed event volume, and where in the architecture aggregation should occur.
View model answer
Implement a distributed telemetry architecture with local collectors at each access layer tier. Raw NetFlow and RADIUS accounting data should be aggregated and pre-processed at the local collector before being forwarded to the central NAC policy engine. This reduces WAN bandwidth consumption and processing load on the central engine. Size the central policy engine based on processed event rate, not raw telemetry volume. Implement telemetry buffering at the collector layer to handle burst conditions during peak load. Additionally, consider applying sampling to NetFlow data (e.g., 1-in-10 packet sampling) for general traffic monitoring, reserving full-rate telemetry for high-risk device segments. Validate the architecture under simulated peak load before the event.
Q4. A retail CTO asks whether implementing Post-Admission NAC will satisfy PCI DSS v4.0 Requirement 10 and reduce the scope of their annual QSA audit. How do you advise them?
Hint: Consider what PCI DSS Requirement 10 specifically mandates and what documentation a QSA will require.
View model answer
Post-Admission NAC directly supports PCI DSS v4.0 Requirement 10 compliance by providing automated, continuous logging and monitoring of all access to network resources and cardholder data environments. The automated quarantine capability demonstrates a real-time response mechanism, which satisfies the spirit of Requirement 10.7 (responding to failures of critical security controls). However, to reduce audit scope, the CTO must ensure that: the NAC event log is tamper-evident and retained for at least 12 months; automated response procedures are formally documented; and the QSA can review evidence of the system operating in production. Scope reduction is more likely to be achieved through network segmentation (isolating the CDE) than through NAC alone, but NAC significantly strengthens the evidence package presented to the QSA.