Is Airport WiFi Safe? A Traveller's Security Guide
This guide provides an authoritative technical reference for IT managers, network architects, and venue operations directors on the security risks of airport WiFi and how to mitigate them. It covers the full threat landscape — from Evil Twin access points to rogue DHCP servers — and delivers a practical, standards-based deployment framework using IEEE 802.1X, WPA3, and network segmentation. It also maps Purple's Guest WiFi and analytics platform to each risk vector, providing concrete integration points for operators looking to deploy secure, GDPR-compliant, and commercially viable public WiFi.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- The Threat Landscape
- Authentication and Encryption Standards
- Implementation Guide
- Phase 1: Network Segmentation
- Phase 2: Client Isolation
- Phase 3: Captive Portal Deployment
- Phase 4: Rogue AP Detection and Containment
- Phase 5: DNS Filtering and Traffic Inspection
- Phase 6: Monitoring and Analytics
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For enterprise IT leaders and venue operations directors, the question of whether airport WiFi is safe is not merely theoretical — it is a live operational risk. With a significant proportion of travellers connecting to public networks without verifying the SSID, the threat surface at major transport hubs is vast and largely unmitigated. This guide provides a technical teardown of airport WiFi vulnerabilities — from Evil Twin access points and rogue DHCP servers to unencrypted captive portals — and outlines the robust architectural requirements necessary to secure these high-density environments. By implementing standards such as IEEE 802.1X, WPA3, and proper VLAN segmentation, alongside Purple's Guest WiFi and WiFi Analytics solutions, venue operators can mitigate risk, ensure compliance with PCI DSS and GDPR, and deliver a secure, high-performance connectivity experience that also drives commercial value. This document is a practical deployment and risk mitigation framework for CTOs and network architects operating in the Transport , Hospitality , and Retail sectors.
Technical Deep-Dive
The architecture of a secure public WiFi network in a high-density environment like an airport requires multiple, overlapping layers of defence. The primary vulnerability of open public WiFi is the absence of per-client over-the-air encryption. In a standard open network, all traffic is broadcast in plaintext at the radio layer, meaning any device within range can capture and decode packets transmitted by other devices. This is the foundational risk from which most airport WiFi threats derive.
The Threat Landscape

The six primary threat vectors in an airport WiFi environment are as follows.
Evil Twin Access Points represent the most prevalent and dangerous threat. An attacker deploys a rogue access point broadcasting a legitimate-sounding SSID — for example, "AirportFreeWiFi" or a close variant of the official network name. Client devices configured to auto-connect to known networks, or users who simply select the most prominent SSID, connect without verification. The attacker is now positioned as a Man-in-the-Middle (MitM), capable of intercepting credentials, injecting malicious content into HTTP responses, or redirecting users to phishing pages.
Man-in-the-Middle Attacks extend beyond the Evil Twin scenario. On an open, unencrypted network, an attacker on the same subnet can use ARP poisoning to intercept traffic between a client and the legitimate gateway, even without deploying a rogue AP.
Packet Sniffing is the most passive and therefore most difficult to detect threat. Using freely available tools, an attacker can capture all unencrypted traffic on the network. Any application-layer data not protected by TLS — including legacy HTTP traffic, some DNS queries, and certain application protocols — is exposed.
Rogue DHCP Servers allow an attacker to assign malicious network configurations to connecting clients, including a rogue DNS server that resolves legitimate domain names to attacker-controlled IP addresses.
Session Hijacking exploits the theft of valid session cookies or authentication tokens. Even where the initial login is protected by HTTPS, if the session cookie is subsequently transmitted over HTTP (a common misconfiguration), an attacker can steal it and impersonate the authenticated user.
Unencrypted Captive Portals represent a systemic vulnerability in many legacy deployments. If the captive portal is served over HTTP rather than HTTPS, any credentials, personal data, or consent signals submitted by the user are transmitted in plaintext — a direct GDPR violation and a trivial attack vector.
Authentication and Encryption Standards
Modern deployments must transition away from open SSIDs towards WPA3-Enterprise or Passpoint (Hotspot 2.0). WPA3 introduces Simultaneous Authentication of Equals (SAE), replacing the Pre-Shared Key (PSK) handshake of WPA2 and providing protection against offline dictionary attacks. Critically, WPA3 also provides Opportunistic Wireless Encryption (OWE) for open networks, which encrypts traffic between each client and the AP without requiring a password — directly addressing the packet sniffing risk on open networks.
Passpoint (IEEE 802.11u) takes this further by leveraging 802.1X and the Extensible Authentication Protocol (EAP) to provide enterprise-grade authentication. The client device presents a credential (certificate or SIM) to the network, and the network presents a certificate to the client. This mutual authentication cryptographically eliminates the Evil Twin threat. Purple operates as a free identity provider for OpenRoaming under the Connect licence, enabling venues to deploy profile-based, seamless authentication at scale without building their own RADIUS infrastructure.
Implementation Guide
The following framework provides a vendor-neutral deployment sequence for a secure airport guest WiFi environment.

Phase 1: Network Segmentation
Network segmentation is the single most impactful control in a high-density public environment. The objective is to ensure that a compromise on the guest network cannot propagate to operational or corporate systems.
| VLAN | Purpose | Subnet Example | Inter-VLAN Routing |
|---|---|---|---|
| VLAN 10 | Corporate Operations | 10.10.0.0/24 | Deny all from VLAN 20, 30 |
| VLAN 20 | IoT Devices (HVAC, CCTV) | 10.20.0.0/24 | Deny all from VLAN 10, 30 |
| VLAN 30 | Guest WiFi | 10.30.0.0/23 | Internet only, deny RFC1918 |
Firewall rules must explicitly deny all inter-VLAN routing between the guest VLAN and all internal VLANs. The guest VLAN should have access to the internet only, with all RFC 1918 address space blocked at the gateway.
Phase 2: Client Isolation
Enable AP-level client isolation (Layer 2 isolation) on all guest SSIDs. This prevents devices on the same AP from communicating directly with each other, eliminating peer-to-peer attack vectors including ARP poisoning and direct exploitation of vulnerable guest devices.
Phase 3: Captive Portal Deployment
Deploy a GDPR-compliant, HTTPS-enforced captive portal. Purple's platform provides a fully managed captive portal that handles encrypted data capture, explicit consent management, and GDPR-compliant data storage. The splash page serves as both a security control and a commercial asset, enabling targeted retail media and personalised marketing.
Phase 4: Rogue AP Detection and Containment
Configure the Wireless LAN Controller (WLC) to operate in hybrid mode, with a subset of access points dedicated to monitor mode for continuous RF scanning. Configure automatic containment for detected rogue APs. Implement 802.11w Management Frame Protection (MFP) to prevent attackers from spoofing deauthentication frames against legitimate APs.
Phase 5: DNS Filtering and Traffic Inspection
Deploy DNS-level filtering to block known malicious domains and prevent malware command-and-control (C2) communication. Integrate with a Next-Generation Firewall (NGFW) for application-layer visibility, enabling detection of anomalous traffic patterns and protocol violations.
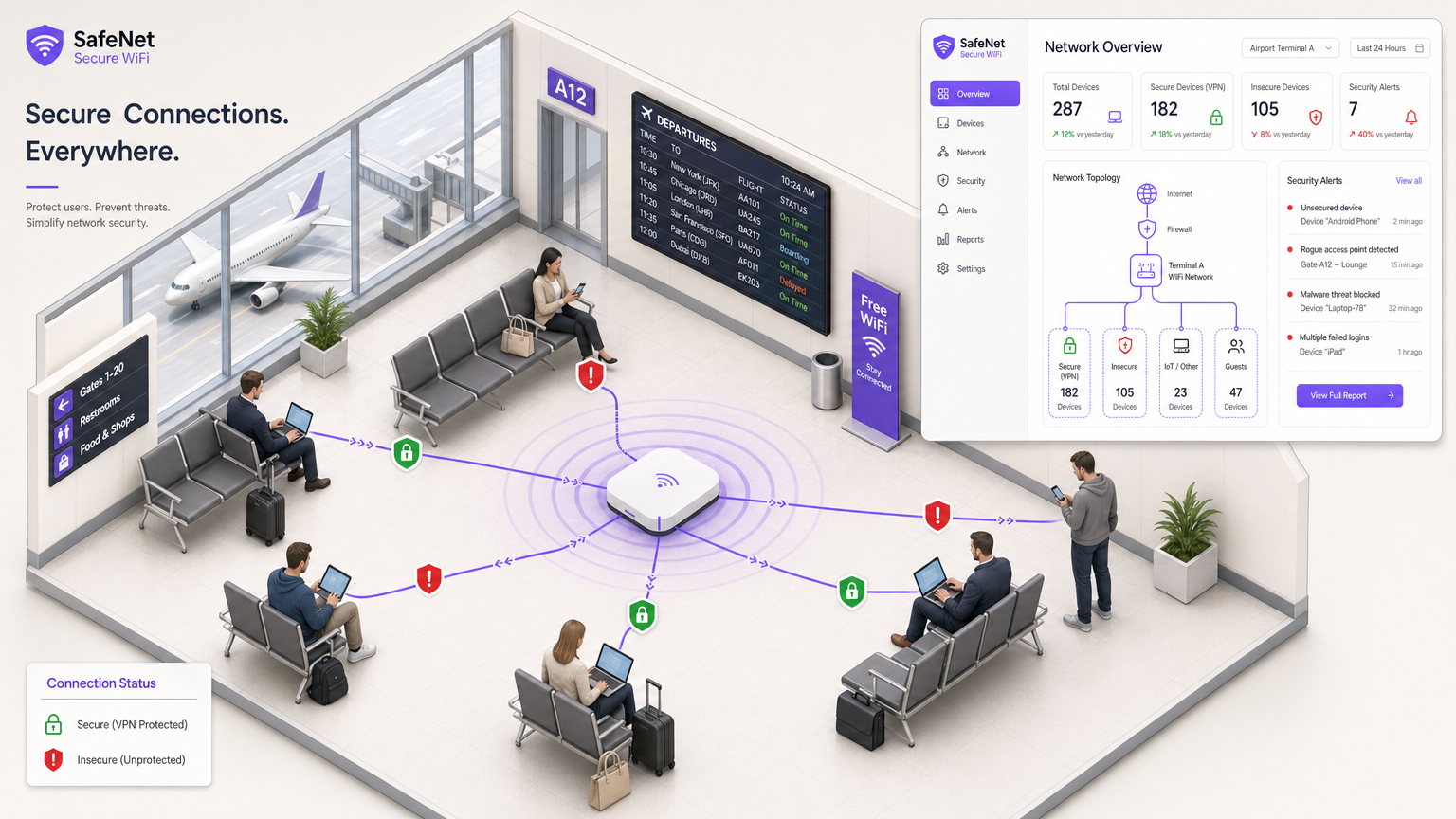
Phase 6: Monitoring and Analytics
Deploy a centralised monitoring platform that provides real-time visibility into connected device counts, threat alerts, bandwidth utilisation, and configuration drift. Purple's WiFi Analytics platform provides this operational visibility alongside commercial analytics, including dwell time, repeat visitor rates, and footfall heatmaps — delivering dual value for IT and marketing teams.
Best Practices
The following recommendations align with IEEE, PCI DSS, and GDPR requirements and represent the current industry consensus for secure public WiFi deployments.
Enforce WPA3 on all new deployments. WPA3-SAE provides forward secrecy, meaning that even if a session key is compromised, past sessions cannot be decrypted. This is a fundamental improvement over WPA2-PSK.
Implement OWE for legacy open SSIDs. Where Passpoint adoption is not yet feasible, OWE provides opportunistic encryption for open networks with no user friction, directly mitigating packet sniffing.
Conduct quarterly wireless penetration tests. Regular testing against the OWASP Wireless Security Testing Guide and PCI DSS Requirement 11.3 ensures that configuration drift and new vulnerabilities are identified before they are exploited.
Maintain a SSID inventory. Document all authorised SSIDs and their associated VLANs, security profiles, and access policies. Any SSID not on the inventory should trigger an immediate security alert.
Apply rate limiting per client. Prevent individual devices from consuming disproportionate bandwidth, which can degrade service quality for all users and mask denial-of-service attacks.
For further reading on secure network deployment in adjacent environments, the guides on WiFi in Hospitals: A Guide to Secure Clinical Networks and Your Guide to a Wireless Access Point Ruckus provide relevant architectural context. The Is Hotel WiFi Safe? What Every Traveller Needs to Know guide covers the same threat landscape in a hospitality context.
Troubleshooting & Risk Mitigation
Failure Mode: High Latency During Peak Hours. This is typically caused by broadcast storms on large, unsegmented subnets or by excessive management frame overhead in high-density environments. Mitigation: Reduce subnet sizes (use /23 or /24 rather than /16), enable broadcast and multicast suppression at the AP and switch level, and implement BSS Colouring (802.11ax) to reduce co-channel interference.
Failure Mode: Captive Portal Bypass via MAC Spoofing. Advanced users can spoof MAC addresses to impersonate previously authenticated devices, bypassing time limits or access controls. Mitigation: Implement robust session management tied to multiple device identifiers, not solely MAC address. Integrate with an NGFW for application-layer session tracking.
Failure Mode: Rogue AP Containment Causing Legal Issues. In some jurisdictions, actively transmitting deauthentication frames to contain rogue APs may have legal implications. Mitigation: Consult legal counsel before enabling active containment. As an alternative, implement Passpoint to make rogue APs ineffective rather than actively containing them.
Failure Mode: GDPR Non-Compliance at the Captive Portal. If the captive portal collects personal data (email, name, social login) without explicit, informed consent, this constitutes a GDPR violation. Mitigation: Deploy Purple's platform, which is designed from the ground up for GDPR compliance, including granular consent management and data subject access request (DSAR) handling.
ROI & Business Impact
Secure infrastructure is not a cost centre — it is a commercial enabler. The business case for investing in enterprise-grade airport WiFi security operates on two dimensions: risk avoidance and revenue generation.
On the risk avoidance side, a single data breach involving guest WiFi can result in ICO fines of up to 4% of global annual turnover under GDPR, reputational damage, and operational disruption. The cost of deploying proper segmentation, WPA3, and a compliant captive portal is a fraction of the potential liability.
On the revenue generation side, Purple's platform transforms the captive portal from a compliance tick box into a commercial asset. By capturing first-party data through a GDPR-compliant consent flow, venue operators can build detailed passenger profiles, enabling targeted retail media, personalised offers, and loyalty programme integration. This model is directly analogous to the retail media monetisation strategies deployed by major retailers — and the same principles apply in Retail , Hospitality , and Healthcare environments.
The WiFi Analytics platform provides measurable outcomes including dwell time analysis, repeat visitor rates, and footfall heatmaps, enabling venue operators to optimise retail layouts, staffing levels, and marketing spend based on real-world behavioural data.
For operators considering in-transit connectivity beyond the terminal, the guide on In-Car Wi-Fi Solutions extends these principles to vehicle-based deployments.
Key Terms & Definitions
Evil Twin
A malicious wireless access point that broadcasts the same SSID as a legitimate network in order to intercept client connections and execute Man-in-the-Middle attacks.
The most prevalent threat in airport environments. Mitigated by Passpoint/802.1X, which provides cryptographic network authentication.
Client Isolation
An access point configuration that prevents devices connected to the same AP or SSID from communicating directly with each other at Layer 2.
Essential for all guest networks. Eliminates ARP poisoning, peer-to-peer exploitation, and lateral movement between guest devices.
Passpoint (Hotspot 2.0 / IEEE 802.11u)
A Wi-Fi Alliance standard that enables seamless, secure roaming between WiFi networks using 802.1X authentication and mutual certificate-based verification.
The modern replacement for open captive portals. Provides cellular-like roaming and eliminates the Evil Twin attack vector.
WPA3-SAE (Simultaneous Authentication of Equals)
The authentication mechanism in WPA3 that replaces the WPA2 Pre-Shared Key handshake, providing forward secrecy and resistance to offline dictionary attacks.
Mandatory for all new enterprise deployments. Ensures that past sessions cannot be decrypted even if a session key is later compromised.
OWE (Opportunistic Wireless Encryption)
A WPA3 feature that provides per-client encryption on open networks without requiring a password or authentication, using a Diffie-Hellman key exchange.
A transitional control for venues that cannot yet deploy Passpoint. Directly mitigates packet sniffing on open SSIDs.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices connecting to a LAN or WLAN.
The underlying authentication mechanism for enterprise-grade WiFi and Passpoint. Requires a RADIUS server or a managed identity provider such as Purple.
VLAN (Virtual Local Area Network)
A logical network partition that segments traffic on the same physical infrastructure, enforcing isolation between different classes of devices and users.
The foundational control for network segmentation. Separates guest, corporate, and IoT traffic to contain the blast radius of any compromise.
Captive Portal
A web page that intercepts a connecting device's HTTP traffic and requires the user to authenticate or accept terms before granting network access.
The primary mechanism for GDPR-compliant data capture on guest networks. Must be served over HTTPS to avoid transmitting user data in plaintext.
Rogue AP
An unauthorised wireless access point connected to or operating within a network environment, whether deployed maliciously or inadvertently.
Detected via WLC-based RF scanning and monitor-mode APs. Mitigated long-term by transitioning to Passpoint, which renders rogue APs ineffective.
Management Frame Protection (802.11w)
An IEEE standard that provides cryptographic protection for 802.11 management frames, preventing attackers from spoofing deauthentication or disassociation frames.
Prevents deauthentication attacks that force clients to disconnect from legitimate APs and reconnect to rogue ones.
Case Studies
A major international airport is experiencing intermittent connectivity issues and suspects rogue access points are spoofing their official 'Airport_Free_WiFi' SSID in Terminal B. The security team has received reports from passengers of being redirected to unfamiliar login pages. How should the network architect respond, and what long-term architectural change should be prioritised?
Immediate response: 1) Activate Rogue AP containment on the WLC, which will transmit deauthentication frames to clients connected to the rogue APs. 2) Deploy a temporary monitor-mode AP in Terminal B to improve RF visibility and accelerate rogue AP identification. 3) Issue a passenger advisory via the airport app and departure boards specifying the exact official SSID and warning against connecting to variants. Long-term architecture: 1) Implement 802.11w Management Frame Protection (MFP) to prevent attackers from spoofing deauthentication frames against legitimate APs. 2) Transition the network to support Passpoint (Hotspot 2.0) with 802.1X authentication, providing cryptographic proof of network identity to client devices. 3) Integrate Purple's identity provider capability for OpenRoaming to enable seamless, secure profile-based authentication without a captive portal.
A retail chain operating concession stands across three terminals of a major airport wants to offer free WiFi to customers. Their existing POS systems are connected to the same network infrastructure. The IT manager needs to ensure PCI DSS compliance while also enabling a GDPR-compliant data capture mechanism for marketing purposes. What is the recommended architecture?
- Implement strict VLAN segmentation: POS systems on a dedicated, isolated VLAN (e.g., VLAN 10) with no routing to any other VLAN. Guest WiFi on a separate VLAN (e.g., VLAN 30) with internet-only access. 2) Enable client isolation on the guest SSID to prevent peer-to-peer attacks. 3) Deploy Purple's Guest WiFi platform to manage the captive portal, ensuring HTTPS enforcement, explicit GDPR consent capture, and first-party data collection. 4) Apply firewall rules at the gateway explicitly denying all traffic from VLAN 30 to VLAN 10. 5) Conduct a PCI DSS scoping exercise to confirm that the guest VLAN is out of scope for PCI DSS, reducing compliance overhead. 6) Configure the Purple analytics platform to capture dwell time and repeat visit data, enabling targeted marketing to loyalty programme members.
Scenario Analysis
Q1. A venue operator at a major airport wants to monetise their free guest WiFi through targeted advertising but is concerned about GDPR compliance and the security of the data capture mechanism. The current captive portal is served over HTTP and collects email addresses. What are the immediate risks, and what is the recommended remediation?
💡 Hint:Consider both the data transmission security and the legal basis for data processing under GDPR Article 6.
Show Recommended Approach
Immediate risks: 1) The HTTP captive portal transmits user credentials and personal data in plaintext, exposing them to packet sniffing — a direct GDPR Article 32 violation (failure to implement appropriate technical security measures). 2) Without explicit, informed consent, the collection of email addresses for marketing purposes lacks a valid legal basis under GDPR Article 6. Remediation: 1) Immediately migrate the captive portal to HTTPS with a valid TLS certificate. 2) Deploy Purple's Guest WiFi platform to manage the captive portal, which provides GDPR-compliant consent flows, encrypted data capture, and first-party data management. 3) Implement granular consent options allowing users to opt in to marketing communications separately from network access. 4) Ensure data retention policies are documented and enforced.
Q2. During a security audit of an airport's wireless infrastructure, it is discovered that the guest WiFi, the baggage handling IoT network, and the airline operations workstations are all on the same /16 subnet with no VLAN segmentation. What is the severity of this finding, and what is the remediation priority order?
💡 Hint:Consider the potential impact of a compromised guest device on critical operational infrastructure.
Show Recommended Approach
Severity: Critical. A compromised guest device on the same subnet as baggage handling IoT systems and airline operations workstations can execute ARP poisoning, scan for and exploit vulnerable IoT devices, and potentially disrupt critical airport operations. This is also a likely PCI DSS violation if any payment processing occurs on the operations network. Remediation priority: 1) Immediately implement VLAN segmentation to isolate the three traffic classes. 2) Apply strict firewall rules denying all inter-VLAN routing between the guest VLAN and the operational VLANs. 3) Enable client isolation on the guest SSID. 4) Conduct a threat assessment to determine whether any lateral movement has already occurred. 5) Reduce subnet sizes to /23 or /24 to limit broadcast domain scope.
Q3. An IT manager at an airport has been tasked with eliminating Evil Twin attacks in the departures lounge. The current network uses WPA2-Personal with a shared passphrase displayed on signage. What is the most effective long-term technical control, and what interim measures can be deployed immediately?
💡 Hint:Consider the difference between SSID-based and cryptographic network identity verification.
Show Recommended Approach
Long-term control: Transition to Passpoint (Hotspot 2.0) with 802.1X authentication. Passpoint provides mutual certificate-based authentication, meaning the client device cryptographically verifies the network's identity before connecting. An Evil Twin AP cannot present a valid certificate, so client devices will not connect to it — regardless of the SSID. Purple's OpenRoaming identity provider capability can accelerate this deployment. Interim measures: 1) Activate Rogue AP detection and containment on the WLC. 2) Implement 802.11w Management Frame Protection to prevent deauthentication spoofing. 3) Issue clear passenger communications specifying the exact official SSID and warning against connecting to variants. 4) Transition from WPA2-Personal to WPA3-SAE to improve over-the-air encryption quality while Passpoint is being deployed.



