How to Set Up a RADIUS Server for WiFi Authentication
This authoritative guide provides IT leaders and network architects with a comprehensive blueprint for deploying a RADIUS server for enterprise WiFi authentication. It covers the architectural trade-offs between on-premise and cloud-hosted deployments, EAP method selection, Active Directory integration, and dynamic VLAN assignment. Venue operators and IT teams will find actionable implementation steps, real-world case studies, and risk mitigation strategies to move from an insecure PSK environment to a robust 802.1X infrastructure this quarter.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Executive Summary
- Technical Deep-Dive
- The 802.1X Architecture
- Choosing an EAP Method
- Implementation Guide
- Step 1: Architectural Decision — On-Premise vs. Cloud RADIUS
- Step 2: Install and Configure the RADIUS Server
- Step 3: Configure Access Points
- Step 4: Directory Integration
- Step 5: Client Configuration and Certificate Validation
- Step 6: Implement Dynamic VLAN Assignment
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For enterprise environments — whether a sprawling university campus, a high-density stadium, or a distributed retail chain — relying on a Pre-Shared Key (PSK) for WiFi access is a significant security liability. A single compromised credential exposes the entire network, and revoking access requires changing the password for every device on the estate. Implementing 802.1X authentication via a RADIUS (Remote Authentication Dial-In User Service) server eliminates this problem entirely: each user authenticates individually, access can be revoked instantly, and network segmentation is enforced dynamically.
This guide provides a definitive roadmap for IT managers and network architects to deploy RADIUS authentication. We cover the architectural trade-offs between on-premise and cloud-hosted deployments, the configuration of Extensible Authentication Protocol (EAP) methods, and the integration with directory services like Active Directory. We also demonstrate how a robust authentication layer integrates with Guest WiFi solutions to provide seamless access for visitors, while capturing the WiFi Analytics that turn your network into a business intelligence asset.
Technical Deep-Dive
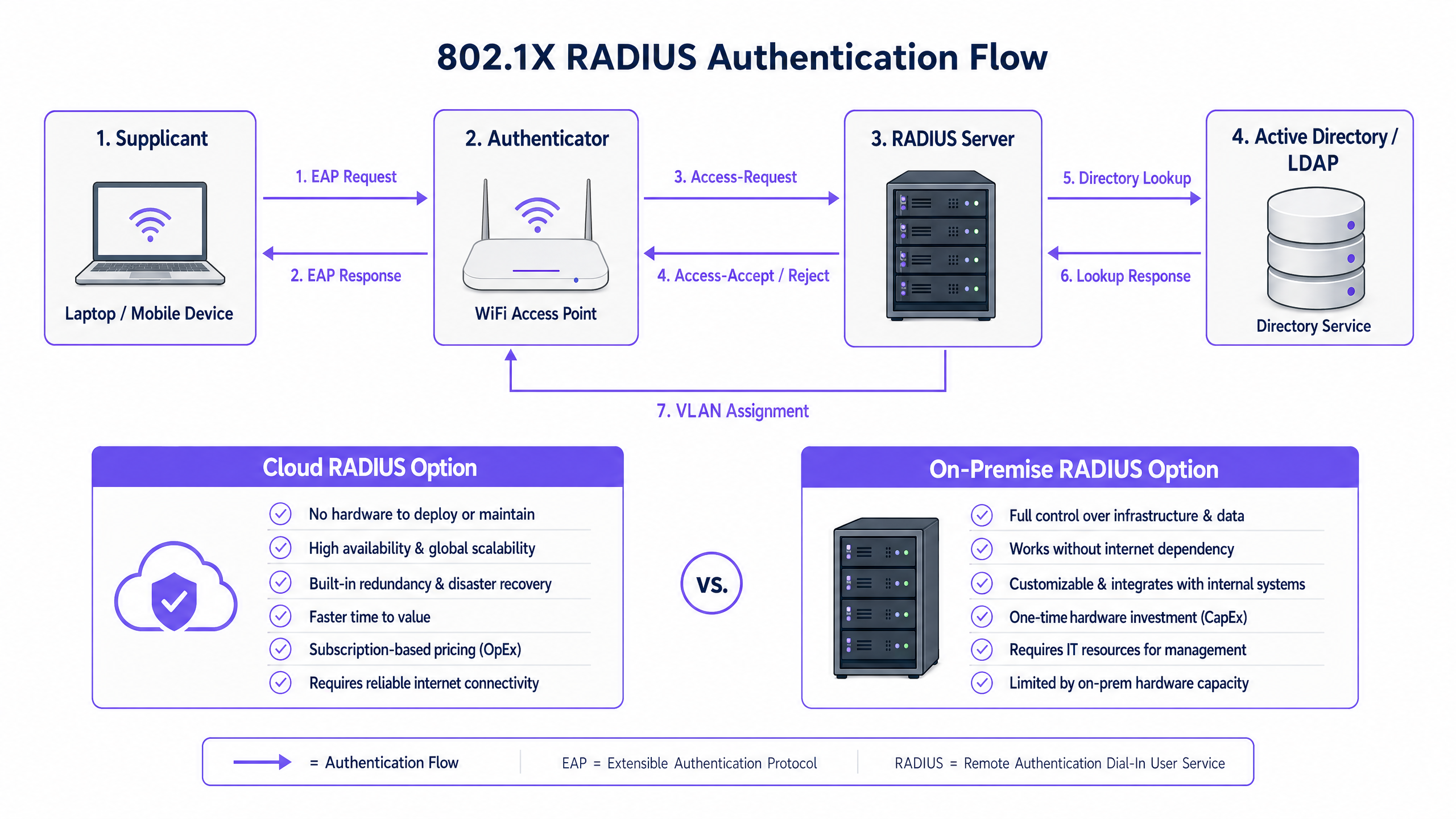
The 802.1X Architecture
The IEEE 802.1X standard defines port-based Network Access Control (PNAC). In a wireless context, it involves three primary roles working in concert:
| Role | Component | Responsibility |
|---|---|---|
| Supplicant | Client device (laptop, smartphone) | Presents credentials to request network access |
| Authenticator | WiFi Access Point or Controller | Enforces access control; relays EAP messages |
| Authentication Server | RADIUS Server | Validates credentials; returns accept/reject and policy attributes |
When a supplicant associates with an access point, the AP blocks all data traffic except EAP (Extensible Authentication Protocol) messages. The AP encapsulates these EAP messages in RADIUS packets and forwards them to the RADIUS server. The server verifies the credentials against a backend database — typically LDAP or Active Directory — and returns an Access-Accept or Access-Reject message. If accepted, the AP unblocks the port and the client's traffic flows freely.
Choosing an EAP Method
The security of your RADIUS deployment depends heavily on the EAP method selected. The two most prevalent in enterprise deployments are:
EAP-TLS (Transport Layer Security) is the gold standard. It requires digital certificates on both the RADIUS server and every client device, eliminating passwords entirely. Even if an attacker captures the full authentication exchange, there are no credentials to extract. The trade-off is administrative overhead: deploying and managing client certificates requires a functioning Public Key Infrastructure (PKI) and an MDM solution (e.g., Microsoft Intune, Jamf) to distribute certificates to endpoints.
PEAP-MSCHAPv2 (Protected EAP) is the most widely deployed method in practice. It uses a server-side certificate to establish an encrypted TLS tunnel, inside which the client authenticates with a username and password. This is significantly easier to deploy than EAP-TLS because only one certificate — the server's — needs to be managed. However, it carries a critical caveat: if client devices are not explicitly configured to validate the RADIUS server's certificate, they are vulnerable to Man-in-the-Middle (MitM) attacks via rogue access points.
> Critical Security Note: Failing to enforce strict certificate validation on client devices effectively nullifies the security benefits of PEAP-MSCHAPv2. An attacker can deploy a rogue AP, present a fraudulent certificate, and capture user credentials in plaintext. This is not a theoretical risk — it is a well-documented attack vector that has been exploited in real-world environments.
Implementation Guide
Step 1: Architectural Decision — On-Premise vs. Cloud RADIUS
The first decision is where to host the RADIUS infrastructure. This is primarily an operational and cost question, not a security one — both models can be deployed securely.
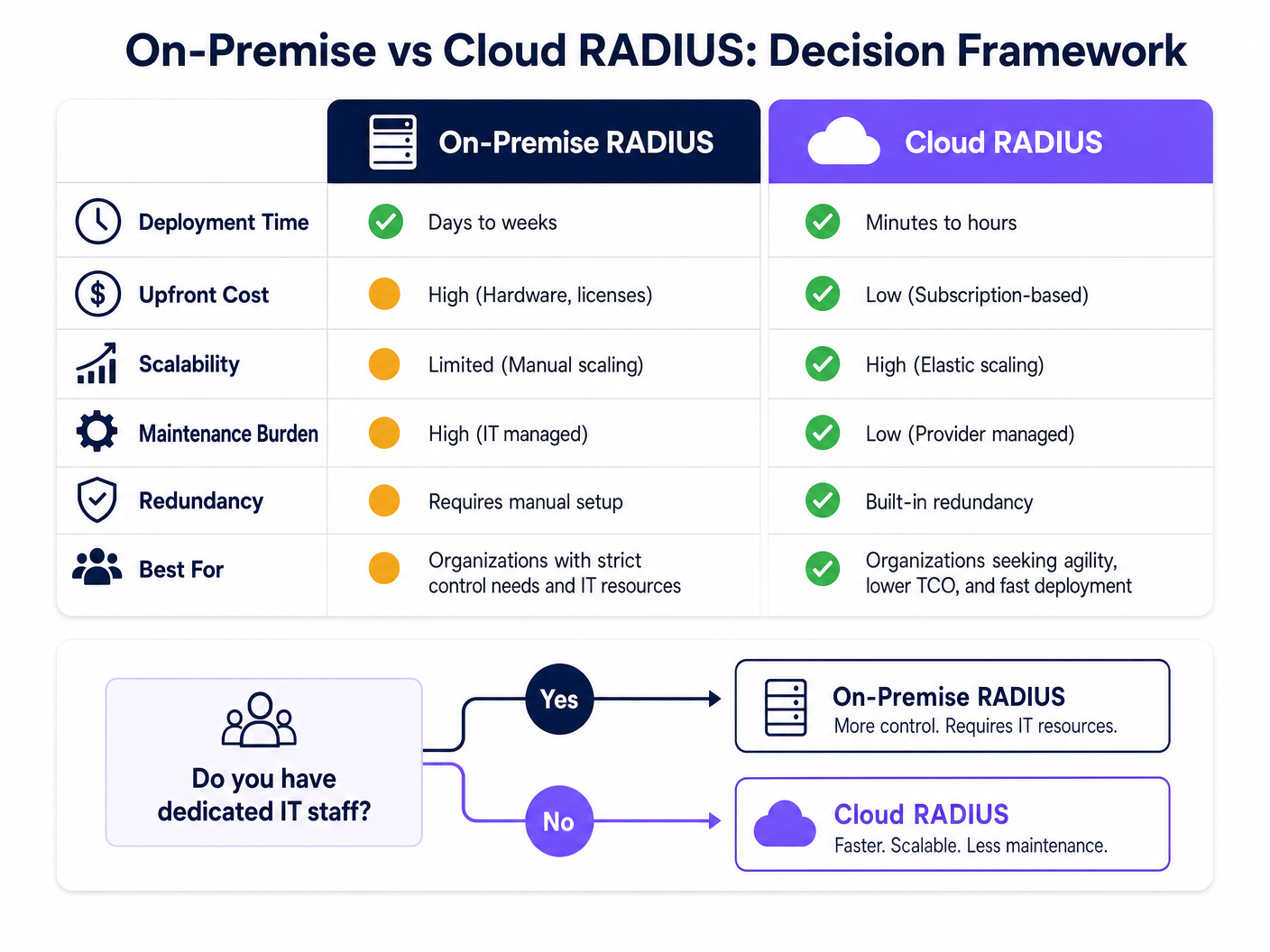
On-Premise RADIUS (e.g., Microsoft NPS, FreeRADIUS, Cisco ISE) is suited for organisations with dedicated IT staff, existing on-premise directory infrastructure, and stringent data sovereignty or compliance requirements. It does not depend on internet connectivity for authentication, which is a meaningful advantage for environments where internet uptime cannot be guaranteed.
Cloud RADIUS is increasingly the preferred model for distributed environments — Retail chains, Hospitality groups, and Transport hubs where deploying servers at every location is operationally impractical. Cloud RADIUS integrates natively with cloud identity providers (Azure AD, Google Workspace, Okta) and provides built-in high availability and global scalability.
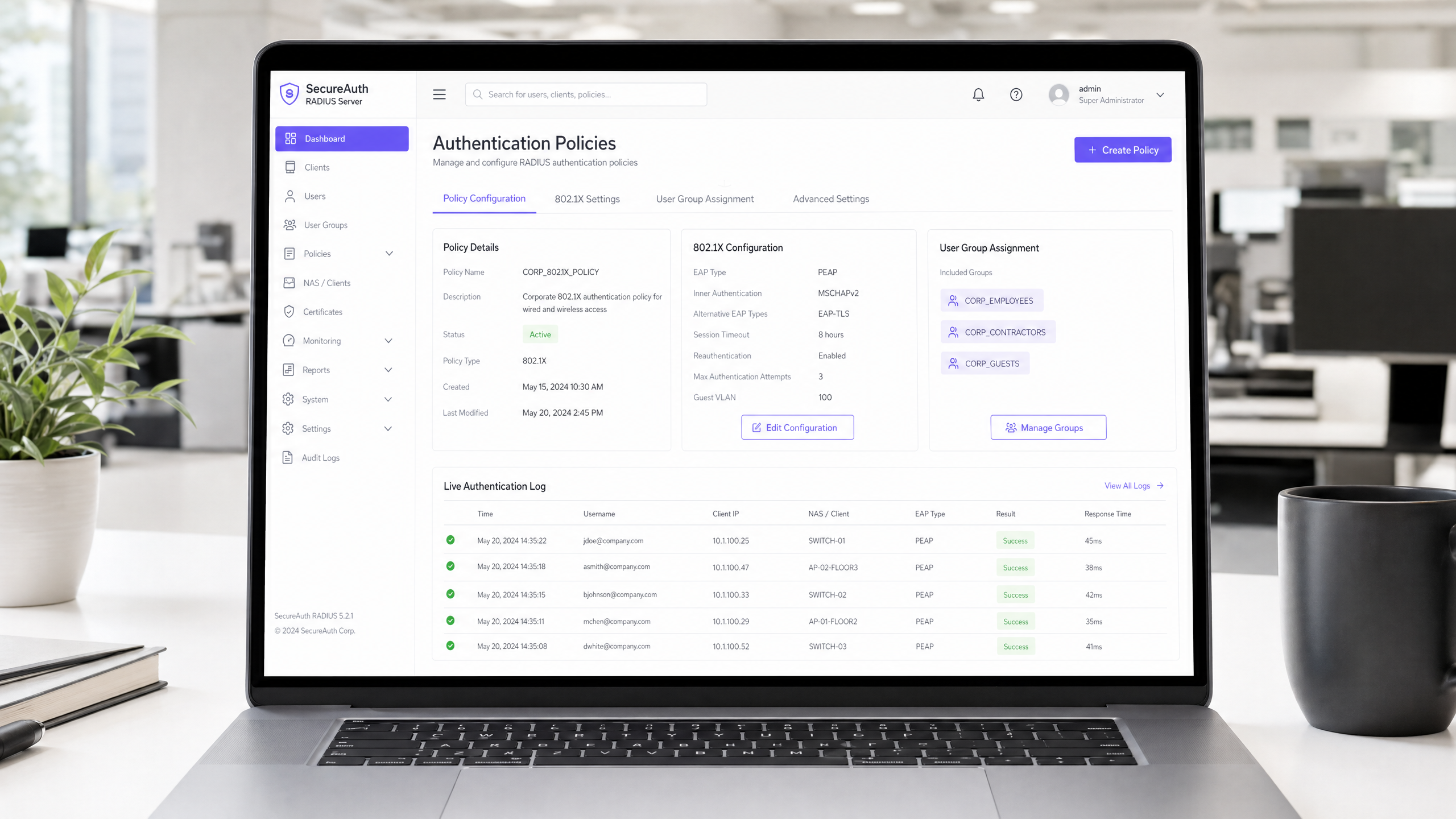
Step 2: Install and Configure the RADIUS Server
For an on-premise deployment using Microsoft NPS (the most common choice in Windows-centric environments):
- Install the Network Policy Server role via Server Manager.
- Register the NPS server in Active Directory to allow it to read user dial-in properties.
- Create a RADIUS Client entry for each access point or wireless controller, specifying the AP's IP address and a strong, unique Shared Secret.
- Configure a Network Policy defining the conditions (e.g., user group membership) and constraints (e.g., EAP method, session timeout) for access.
- Configure the Connection Request Policy to process requests locally.
For FreeRADIUS on Linux:
- Install via package manager:
sudo apt-get install freeradius freeradius-ldap. - Configure
/etc/freeradius/3.0/clients.confto define RADIUS clients (APs) and their shared secrets. - Configure the LDAP module in
/etc/freeradius/3.0/mods-available/ldapto point to your Active Directory or LDAP server. - Enable the LDAP module:
sudo ln -s /etc/freeradius/3.0/mods-available/ldap /etc/freeradius/3.0/mods-enabled/. - Define EAP methods in
/etc/freeradius/3.0/mods-available/eap.
Step 3: Configure Access Points
On your wireless controller or individual access points:
- Define the RADIUS server IP address(es) and authentication port (default: UDP 1812).
- Configure the Shared Secret — use a minimum of 22 characters, mixing alphanumeric and special characters. Use a unique secret per location or AP group.
- Configure the SSID to use WPA2-Enterprise or WPA3-Enterprise security mode with 802.1X key management.
- Configure a secondary RADIUS server for failover.
Step 4: Directory Integration
For on-premise AD integration, the RADIUS server must be joined to the domain or have LDAP read access. Ensure service accounts used for LDAP binding have the minimum required permissions. For cloud RADIUS, configure the API-based synchronisation or SAML/OIDC integration with your IdP.
Define clear user groups in your directory, as these will drive authorisation policies. Recommended group structure:
| Group | VLAN | Access Level |
|---|---|---|
Corp_Staff |
VLAN 10 | Full internal network |
Corp_Contractors |
VLAN 20 | Internet + specific internal resources |
Corp_IoT |
VLAN 30 | Isolated, device-specific ports only |
Corp_Guests |
VLAN 100 | Internet only via captive portal |
Step 5: Client Configuration and Certificate Validation
This is the most operationally critical step. Use Group Policy (GPO) for Windows and MDM profiles for macOS/iOS/Android to push WiFi configurations silently to managed devices. The profile must specify:
- The Root CA that issued the RADIUS server's certificate.
- The expected server name (CN or SAN of the server certificate).
- The EAP method and inner authentication protocol.
For unmanaged BYOD devices, provide clear self-service onboarding instructions, ideally via a Network Access Control (NAC) portal.
Step 6: Implement Dynamic VLAN Assignment
Configure the RADIUS server to return VLAN assignment attributes in the Access-Accept response:
Tunnel-Type=VLAN(13)Tunnel-Medium-Type=IEEE-802(6)Tunnel-Private-Group-Id= ``
The access point reads these attributes and places the authenticated client on the specified VLAN — no manual reconfiguration required as users change roles or locations.
Best Practices
Redundancy is non-negotiable. Deploy a minimum of two RADIUS servers (primary and secondary) and configure all access points to fail over automatically. For on-premise deployments, consider placing the secondary server in a different physical location or availability zone. A RADIUS outage means nobody can authenticate, which is a complete network outage for 802.1X-protected SSIDs.
Monitor certificate expiry proactively. A RADIUS server certificate expiry is one of the most common causes of sudden, widespread authentication failures. Implement monitoring to alert administrators at least 30 days before expiry. This applies to both the server certificate and any intermediate CA certificates in the chain.
Treat the Shared Secret as a critical credential. The shared secret between the AP and the RADIUS server encrypts RADIUS packets. Use unique secrets per location or AP group, store them in a secrets manager, and rotate them periodically. See our guide on Protect Your Network with Strong DNS and Security for broader network security hygiene recommendations.
Align with compliance frameworks. For environments subject to PCI DSS (e.g., retail payment networks), 802.1X authentication directly supports requirements for network access control and audit logging. For GDPR compliance, RADIUS accounting logs (port 1813) provide a detailed audit trail of who accessed the network, from where, and when — valuable for incident response. For Healthcare environments, network segmentation via dynamic VLAN assignment supports HIPAA requirements for protecting electronic protected health information (ePHI).
Troubleshooting & Risk Mitigation
| Failure Mode | Symptom | Resolution |
|---|---|---|
| Certificate expiry | Sudden mass authentication failures | Monitor expiry; renew and redeploy certificate |
| NTP desynchronisation | Intermittent EAP-TLS failures | Ensure RADIUS server and DCs sync to same NTP source |
| LDAP connectivity loss | Authentication fails when AD is unreachable | Deploy redundant DCs; configure RADIUS to cache recent authentications |
| Incorrect Shared Secret | AP logs show RADIUS timeout or Bad authenticator |
Verify secret matches on both AP and RADIUS server |
| Client certificate mismatch | EAP-TLS failures for specific devices | Verify client cert is issued by trusted CA; check cert validity period |
| VLAN not assigned | User authenticated but on wrong network segment | Verify RADIUS attributes are correctly returned; check AP VLAN configuration |
For a deeper dive into the 802.1X configuration process itself, the How to Configure 802.1X WiFi Authentication: A Step-by-Step Guide provides granular, vendor-specific configuration walkthroughs.
ROI & Business Impact
Transitioning from PSK to RADIUS-backed 802.1X requires an initial investment in configuration, and potentially licensing for cloud solutions or hardware for on-premises deployments. The ROI case is straightforward:
Risk mitigation: The average cost of a data breach in the UK is in excess of £3 million (IBM Cost of a Data Breach Report). A compromised PSK can expose the entire network. 802.1X limits the blast radius to a single compromised user account, which can be disabled in seconds via the directory.
Operational efficiency: Dynamic VLAN assignment eliminates manual network reconfiguration as staff change roles. Onboarding a new employee means adding them to the correct AD group — the network access follows automatically.
Compliance posture: For organisations subject to PCI DSS, ISO 27001, or Cyber Essentials Plus, 802.1X is a direct control that auditors expect to see. Deploying it strengthens your compliance posture and reduces audit remediation costs.
Guest experience and analytics: For venue operators, integrating RADIUS for staff authentication with Purple's Guest WiFi platform for visitor access creates a unified, tiered access model. Staff authenticate silently via 802.1X; guests connect via a branded captive portal. Purple's WiFi Analytics platform then provides real-time visibility into visitor dwell times, repeat visit rates, and engagement metrics — data that directly informs marketing spend and venue operations decisions.
For further reading, see the Como Configurar a Autenticação 802.1X WiFi: Um Guia Passo a Passo for Portuguese-language implementation guidance, and What Is a Leased Line? Dedicated Business Internet for guidance on ensuring the underlying connectivity meets enterprise requirements.
GuidesSlugPage.keyDefinitionsTitle
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service. Defined in RFC 2865.
The core server component that validates user credentials against a directory before granting WiFi access. Every enterprise WiFi deployment using 802.1X requires a RADIUS server.
802.1X
An IEEE Standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, blocking all non-EAP traffic until authentication succeeds.
The overarching framework standard that defines how the Supplicant, Authenticator, and Authentication Server communicate. When IT teams refer to 'enterprise WiFi security', they typically mean WPA2/WPA3-Enterprise with 802.1X.
Supplicant
The client device — or more precisely, the 802.1X software stack on that device — that initiates the authentication process by presenting credentials to the network.
On Windows, the built-in supplicant is the Wireless AutoConfig service. On macOS and iOS, it is native to the OS. Ensuring the supplicant is correctly configured (especially for certificate validation) is the most common source of deployment issues.
Authenticator
The network device — typically a WiFi access point or wireless controller — that acts as an intermediary between the Supplicant and the RADIUS server, enforcing access control based on the authentication result.
The AP blocks all data traffic on the port until it receives an Access-Accept from the RADIUS server. It also reads RADIUS attributes (e.g., VLAN assignment) from the Access-Accept response and applies them to the session.
EAP (Extensible Authentication Protocol)
An authentication framework defined in RFC 3748 that provides a standardised transport mechanism for various authentication methods (TLS, PEAP, TTLS, etc.) between the Supplicant and the Authentication Server.
EAP is the 'language' spoken between the client and the RADIUS server. The choice of EAP method (EAP-TLS vs PEAP) determines the security strength and deployment complexity of the authentication system.
PEAP (Protected EAP)
An EAP method that first establishes a TLS tunnel using the server's certificate, then performs a secondary authentication (typically MSCHAPv2 with username/password) inside that encrypted tunnel.
The most common enterprise WiFi authentication method due to its balance of security and deployment simplicity. Requires only a server-side certificate, making it far easier to roll out than EAP-TLS.
Dynamic VLAN Assignment
A RADIUS feature where the server includes VLAN-specific attributes (Tunnel-Type, Tunnel-Medium-Type, Tunnel-Private-Group-Id) in the Access-Accept response, instructing the AP to place the authenticated client on a specific VLAN.
Enables a single SSID to serve multiple user populations with different security requirements. Eliminates the need to broadcast multiple SSIDs for different user groups, reducing RF overhead and simplifying the user experience.
Shared Secret
A pre-configured text string known only to the Authenticator (AP) and the RADIUS server, used to sign and encrypt RADIUS packets, ensuring the integrity and authenticity of the communication.
A critical security configuration element. If the shared secret is weak or compromised, an attacker could forge RADIUS Access-Accept responses, granting unauthorised network access. Use unique secrets per location and store them in a secrets manager.
MAC Authentication Bypass (MAB)
A fallback authentication mechanism where a device's MAC address is used as its identity credential, enabling network access for devices that do not support 802.1X supplicants.
Used for headless devices (printers, IoT sensors, IP cameras). Because MAC addresses are publicly visible and easily spoofed, MAB provides device identification rather than strong authentication. Always pair with restrictive VLAN assignment.
GuidesSlugPage.workedExamplesTitle
A national retail chain with 500 locations needs to implement secure WiFi for store managers' tablets and POS terminals. They currently use a single PSK across all stores, which is frequently shared with unauthorized staff and contractors. They use Azure AD for identity management and have no dedicated IT staff at branch locations.
Deploy a Cloud RADIUS solution integrated directly with Azure AD. This eliminates the need to deploy and manage on-premise RADIUS servers at 500 locations. The IT team uses Microsoft Intune to push a WiFi profile to all store managers' tablets and POS terminals configured for PEAP-MSCHAPv2, strictly enforcing validation of the Cloud RADIUS server's certificate. The Cloud RADIUS policy checks the user's Azure AD group membership before granting access: 'Store_Managers' group receives VLAN 10 (full POS and back-office access), 'Contractors' group receives VLAN 20 (internet-only). When a contractor's engagement ends, removing them from the Azure AD group immediately revokes their WiFi access across all 500 locations simultaneously — no PSK change required.
A 400-room city-centre hotel needs to provide secure WiFi for both staff (front desk, housekeeping, management) and guests. Staff require access to the property management system (PMS) and internal servers. Guests require internet access only. The hotel has a single on-premise Windows Server environment.
Deploy Microsoft NPS on a dedicated Windows Server VM. Configure two SSIDs on the wireless infrastructure: 'Hotel_Staff' (WPA2-Enterprise, 802.1X) and 'Hotel_Guest' (open or WPA2-Personal, redirecting to a captive portal). For the staff SSID, NPS validates credentials against Active Directory and returns dynamic VLAN assignments: 'Management' AD group → VLAN 10 (full access), 'FrontDesk' → VLAN 20 (PMS access), 'Housekeeping' → VLAN 30 (internet + scheduling app only). For guests, integrate the captive portal with Purple's Guest WiFi platform to provide a branded login experience, collect first-party data (email, marketing consent), and gain analytics on dwell time and repeat visits. The two-SSID model keeps staff and guest traffic completely separated at the network layer.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your organisation is migrating 2,000 Windows laptops from a shared PSK to 802.1X with PEAP-MSCHAPv2. Your security team flags that PEAP is vulnerable to credential harvesting via rogue access points. What is the single most important configuration step to mitigate this risk, and how do you deploy it at scale?
GuidesSlugPage.hintPrefixConsider what prevents a client from trusting a fraudulent RADIUS server presenting a self-signed certificate.
GuidesSlugPage.viewModelAnswer
The critical step is enforcing strict server certificate validation on every client device. Using Group Policy Objects (GPO), push a WiFi profile to all 2,000 laptops that specifies: (1) the exact Root CA certificate that issued the RADIUS server's certificate, (2) the expected server name (CN/SAN), and (3) that the client must not prompt the user to trust new certificates. This ensures that even if an attacker deploys a rogue AP with a fraudulent certificate, the client will reject the TLS handshake and refuse to send credentials. Without this configuration, PEAP provides no meaningful protection against rogue AP attacks.
Q2. A hospital IT director needs to provide network access for 300 medical IoT devices (infusion pumps, monitoring equipment) that do not support 802.1X. These devices sit alongside staff workstations on the same wireless infrastructure. How should the RADIUS infrastructure handle these devices, and what network controls must be in place?
GuidesSlugPage.hintPrefixThink about the authentication method available for headless devices and how to compensate for its inherent weakness.
GuidesSlugPage.viewModelAnswer
Configure MAC Authentication Bypass (MAB) on the RADIUS server for these specific devices. Register each device's MAC address in a dedicated Active Directory group or RADIUS database. Because MAC addresses are easily spoofed, the RADIUS server must use Dynamic VLAN Assignment to place all MAB-authenticated devices onto a dedicated, highly restricted VLAN (e.g., VLAN 30 - IoT). This VLAN should be firewalled to allow communication only with specific medical server IP addresses and block all other traffic, including internet access and lateral movement to staff VLANs. Staff workstations authenticate via 802.1X and are placed on a separate VLAN. This architecture satisfies HIPAA network segmentation requirements for ePHI-adjacent devices.
Q3. You are the network architect for a 50-venue restaurant chain. Authentication is working correctly at 49 venues using Cloud RADIUS, but one specific venue reports that all devices fail to authenticate. The Cloud RADIUS management portal shows zero authentication requests arriving from that venue. What is your diagnostic approach?
GuidesSlugPage.hintPrefixIf the RADIUS server is receiving no requests at all, the problem is in the communication path between the Authenticator and the server — not in the authentication logic itself.
GuidesSlugPage.viewModelAnswer
Since the RADIUS server is receiving zero requests from this venue, the fault lies between the access points and the cloud RADIUS server. Diagnostic steps in order: (1) Verify the RADIUS server IP address and port (UDP 1812) configured on the venue's APs or wireless controller — a typo here is the most common cause. (2) Check the local firewall or router rules at that venue to confirm outbound UDP 1812 traffic is permitted to the cloud RADIUS IP range. (3) Verify the Shared Secret configured on the APs matches the secret configured for that venue in the Cloud RADIUS portal — a mismatch causes the RADIUS server to silently discard packets. (4) Check if the venue's internet connection is functioning — cloud RADIUS requires reliable internet connectivity. Running a packet capture on the AP or upstream router will confirm whether RADIUS packets are being sent and whether responses are being received.



