Automating Certificate Revocation with OCSP and CRL in a NAC Environment
This technical reference guide provides IT managers and network architects with a comprehensive breakdown of automating certificate revocation in a Network Access Control (NAC) environment. It explores the architectural tradeoffs between OCSP and CRL, offers vendor-neutral implementation guidance, and outlines the business impact of real-time policy enforcement.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- Certificate Revocation List (CRL) Architecture
- Online Certificate Status Protocol (OCSP) Architecture
- Integration with Guest and Analytics Platforms
- Implementation Guide
- Step 1: Define the Revocation Trigger
- Step 2: Configure the Revocation Infrastructure
- Step 3: Establish the Fallback Policy
- Step 4: Define the Failure Behaviour
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For enterprise IT directors and network architects managing high-density environments—such as Hospitality venues, Retail estates, and public-sector deployments—certificate lifecycle management is a critical security frontier. While IEEE 802.1X provides robust authentication for corporate and BYOD devices, the mechanism by which trust is revoked is often overlooked until a breach occurs.
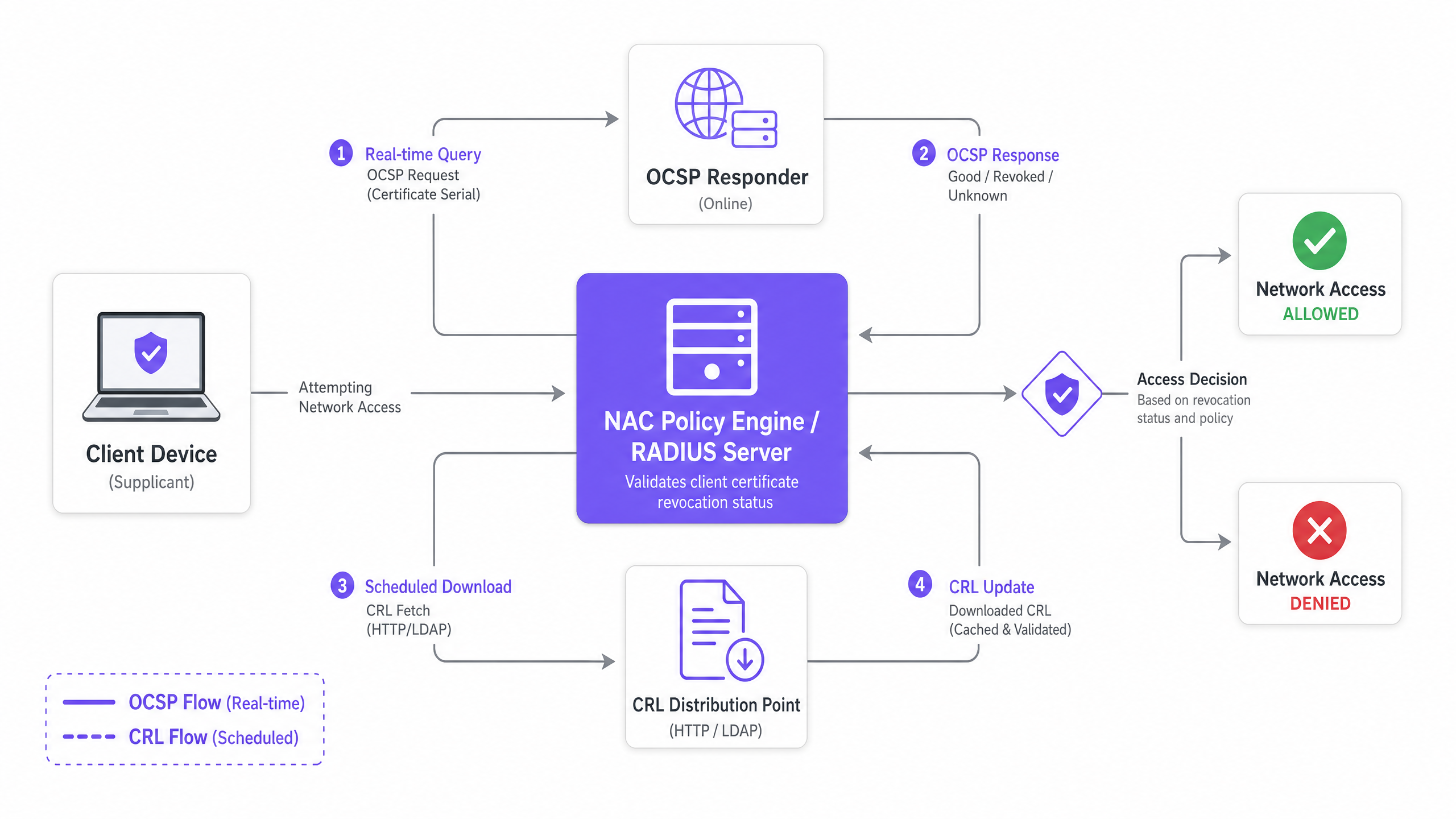
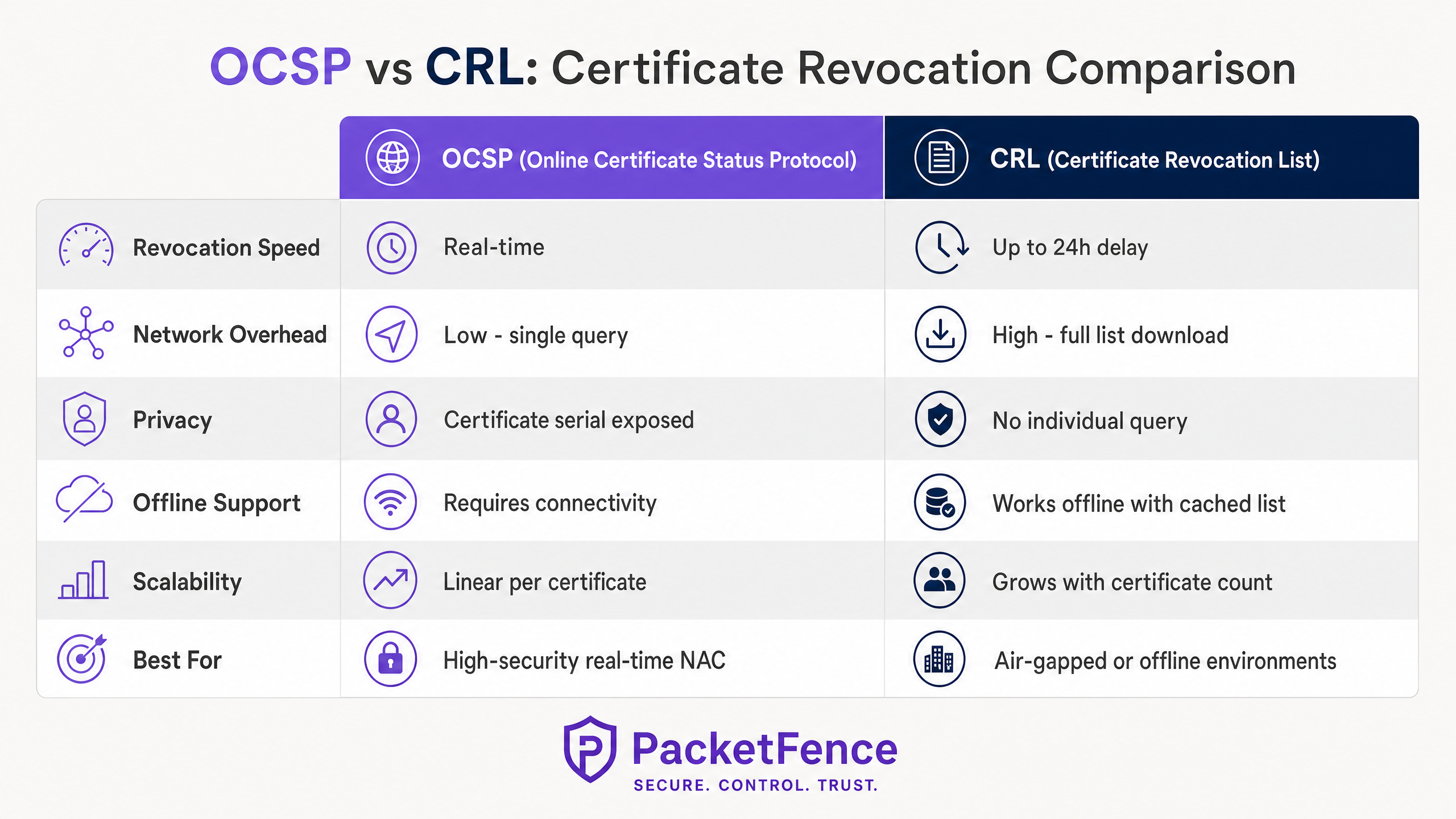
Automating certificate revocation with Online Certificate Status Protocol (OCSP) and Certificate Revocation Lists (CRL) within a Network Access Control (NAC) environment bridges the gap between endpoint decommissioning and network policy enforcement. This guide explores the architectural mechanics of automated revocation, comparing the real-time capabilities of OCSP against the offline resilience of CRL.
By integrating your Mobile Device Management (MDM) platform, Certificate Authority (CA), and NAC policy engine, organisations can achieve zero-trust network access where compromised or decommissioned devices are instantly denied entry. This technical reference provides actionable deployment guidance, risk mitigation strategies, and explores how this staff-facing security posture complements public-facing infrastructure like Purple's Guest WiFi and WiFi Analytics platforms.
Technical Deep-Dive
In any enterprise network leveraging IEEE 802.1X with EAP-TLS, devices authenticate using digital certificates rather than shared credentials. This approach is fundamental to modern security architectures, providing device-bound identity that integrates seamlessly with MDM platforms via protocols like SCEP (for further reading, see The Role of SCEP and NAC in Modern MDM Infrastructure ). However, certificates have a defined lifecycle. When a device is lost, a user is terminated, or a private key is compromised, the network infrastructure must be explicitly instructed to stop trusting that certificate.
This revocation instruction is delivered via two primary mechanisms: CRL and OCSP.
Certificate Revocation List (CRL) Architecture
A CRL is a digitally signed file published by the Certificate Authority containing the serial numbers of all revoked certificates that have not yet expired. The NAC policy engine (acting as the RADIUS server) periodically downloads this list from a CRL Distribution Point (CDP) via HTTP or LDAP.
During the EAP-TLS handshake, the RADIUS server checks the incoming client certificate's serial number against its locally cached CRL. If the serial number is present, authentication is rejected.
Architectural Characteristics:
- Offline Resilience: Because the RADIUS server caches the CRL, revocation checking continues even if the CA or CDP becomes unreachable.
- Latency: The primary drawback is the latency between revocation and enforcement. If a certificate is revoked at 09:00 and the CRL refresh interval is 24 hours, the compromised device retains network access until the next download.
- Throughput Overhead: In environments with tens of thousands of certificates, CRL files can grow to several megabytes, creating bandwidth strain during refresh cycles.
Online Certificate Status Protocol (OCSP) Architecture
OCSP addresses the latency limitations of CRL by enabling real-time revocation checking. Instead of downloading a full list, the RADIUS server sends a targeted query containing the certificate serial number to an OCSP Responder. The responder returns a signed status: Good, Revoked, or Unknown.
Architectural Characteristics:
- Real-Time Enforcement: Revocation decisions propagate instantly. Once the CA updates the OCSP Responder, the next authentication attempt by the compromised device will fail.
- Availability Dependency: The NAC policy engine relies on the OCSP Responder being highly available. If the responder is unreachable, the network administrator must define a failure policy: "fail open" (allow access, compromising security) or "fail closed" (deny access, compromising availability).
- OCSP Stapling: To mitigate load and privacy concerns, OCSP Stapling allows the client device to fetch the signed OCSP response and attach it to the TLS handshake, though supplicant support varies.
Integration with Guest and Analytics Platforms
While OCSP and CRL handle the rigorous security requirements of staff and corporate devices, public-facing networks require different architectures. For public venues, integrating a robust staff NAC with a dedicated public platform like Purple ensures comprehensive coverage. Purple's platform handles captive portal authentication, terms-of-service acceptance, and data capture for the public segment, while the underlying network infrastructure (often the same physical access points and switches) enforces 802.1X and OCSP for corporate SSIDs. Understanding the radio environment is crucial for both segments; refer to Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 for spectrum planning.
Implementation Guide
Deploying automated certificate revocation requires coordination across the PKI, MDM, and NAC domains. Follow these vendor-neutral implementation steps to establish a resilient revocation pipeline.
Step 1: Define the Revocation Trigger
Automation begins at the endpoint management layer. Configure your MDM platform (e.g., Microsoft Intune, Jamf Pro) to trigger a revocation API call to your Certificate Authority when specific conditions are met:
- Device unenrolled from MDM
- Device marked as non-compliant
- User account disabled in the directory service
Step 2: Configure the Revocation Infrastructure
For CRL Deployments:
- Configure the CA to publish the CRL to a highly available CDP (e.g., an load-balanced internal web server).
- Set the CRL publication interval based on your risk tolerance (e.g., every 4 hours).
- Configure the RADIUS server to fetch the CRL at an interval slightly shorter than the publication interval to ensure the cache is always fresh.
For OCSP Deployments:
- Deploy at least two OCSP Responders behind a load balancer to ensure high availability.
- Configure the CA to push revocation updates to the OCSP Responders immediately.
- Configure the RADIUS server to query the load-balanced OCSP virtual IP during EAP-TLS authentication.
Step 3: Establish the Fallback Policy
Do not rely on a single mechanism. Configure your RADIUS server to use OCSP as the primary revocation check, with a fallback to a locally cached CRL if the OCSP Responder is unreachable. This provides real-time enforcement under normal conditions and offline resilience during infrastructure outages.
Step 4: Define the Failure Behaviour
If both OCSP and the cached CRL are unavailable, the RADIUS server must decide how to handle the authentication request.
- High-Security Environments (e.g., Healthcare ): Configure "fail closed". Deny access to prevent potentially compromised devices from connecting.
- Standard Environments (e.g., Transport hubs): Configure "fail open" with alerting. Allow access to maintain operational continuity, but generate a high-priority alert for the SOC.
Best Practices
- Implement Delta CRLs: If relying on CRLs in a large environment, implement Delta CRLs. These files contain only the revocation changes since the last full Base CRL was published, significantly reducing download size and bandwidth consumption.
- Monitor OCSP Latency: OCSP queries occur inline during the EAP-TLS handshake. If the OCSP Responder takes 500ms to reply, authentication is delayed by 500ms. Monitor responder latency and scale horizontally if response times degrade.
- Short-Lived Certificates: Consider reducing certificate validity periods (e.g., from 1 year to 7 days) via automated SCEP/EST renewal. Short-lived certificates naturally expire quickly, reducing the reliance on robust revocation infrastructure.
- Align with Broader Network Strategy: Ensure your NAC deployment aligns with your wide-area network architecture. For insights into modern WAN design, see SD WAN vs MPLS: The 2026 Enterprise Network Guide .
Troubleshooting & Risk Mitigation
The most common failure mode in automated revocation is a broken CA-to-NAC pipeline resulting in a "fail closed" event that locks out legitimate users.
Risk: OCSP Responder Outage Mitigation: Deploy responders in an active-active cluster across multiple fault domains. Implement comprehensive health checks on the load balancer that verify the responder's ability to query the CA database, not just TCP port 80 availability.
Risk: Stale CRL Cache Mitigation: RADIUS servers may fail to download the latest CRL due to network partitions or CDP outages. Implement monitoring that alerts if the locally cached CRL is older than the defined publication interval.
Risk: Incomplete MDM Revocation Mitigation: If the MDM fails to trigger the revocation call to the CA, the certificate remains valid. Implement a reconciliation script that periodically compares the MDM's list of active devices against the CA's list of valid certificates, automatically revoking any discrepancies.
ROI & Business Impact
Automating certificate revocation transforms security from a reactive, manual process into a proactive, automated defence mechanism.
- Risk Reduction: By eliminating the window of exposure between device compromise and network isolation, organisations significantly reduce the risk of lateral movement and data exfiltration. This is crucial for maintaining compliance with frameworks like PCI DSS and GDPR.
- Operational Efficiency: Automating the revocation pipeline eliminates the need for helpdesk staff to manually update RADIUS configurations or CA databases when an employee departs, saving hundreds of hours annually in large enterprises.
- Unified Access Strategy: A robust NAC environment for corporate devices allows IT teams to confidently deploy parallel services, such as Purple's analytics-driven guest WiFi or location-based services (see BLE Low Energy Explained for Enterprise ), knowing the core infrastructure is secure.
Listen to our technical briefing on this topic below:
Key Definitions
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
The most secure standard for 802.1X network authentication, requiring both the client and the server to present digital certificates to prove their identity.
IT teams deploy EAP-TLS to eliminate the risks associated with password-based authentication, ensuring only managed, certificate-bearing devices can connect to the corporate network.
OCSP (Online Certificate Status Protocol)
An internet protocol used for obtaining the revocation status of an X.509 digital certificate in real-time.
Crucial for environments requiring immediate enforcement of access policies, such as when an employee is terminated and their device must be instantly disconnected.
CRL (Certificate Revocation List)
A periodically published, digitally signed list of certificate serial numbers that have been revoked by the issuing Certificate Authority.
Used as a primary revocation mechanism in offline or air-gapped networks, or as a highly resilient fallback mechanism for OCSP.
OCSP Stapling
A mechanism where the client device fetches its own OCSP response and 'staples' it to the TLS handshake, presenting it to the RADIUS server.
Reduces the load on the RADIUS server and OCSP Responder, and improves privacy by preventing the CA from seeing exactly when and where a device is authenticating.
Delta CRL
A smaller revocation list containing only the certificates revoked since the last full Base CRL was published.
Essential for large deployments to prevent network congestion, as full CRLs can become massive and consume significant bandwidth during refresh cycles.
CDP (CRL Distribution Point)
The location, typically an HTTP or LDAP URL, where the Certificate Authority publishes the CRL for clients and RADIUS servers to download.
IT teams must ensure the CDP is highly available and reachable from all NAC policy engines; if the CDP goes down, the RADIUS servers cannot update their caches.
Fail Open / Fail Closed
The policy decision dictating what happens when the revocation infrastructure (OCSP or CDP) is unreachable. Fail Open allows access; Fail Closed denies access.
A critical business decision balancing security posture against operational uptime. Requires sign-off from both IT operations and the CISO.
SCEP (Simple Certificate Enrollment Protocol)
A protocol used by MDM platforms to automate the issuance of digital certificates to managed devices without user intervention.
The starting point of the automated lifecycle. SCEP issues the certificate, and the MDM later triggers the CA to revoke it when the device is retired.
Worked Examples
A 500-bed hospital network is migrating from credential-based 802.1X to certificate-based EAP-TLS for all medical IoT devices and staff laptops. The CISO mandates that if a device is reported stolen, its network access must be terminated within 5 minutes. The network team is concerned about the RADIUS server load if it has to constantly query external services. How should the revocation architecture be designed?
The hospital must deploy OCSP to meet the 5-minute revocation SLA, as CRL refresh intervals cannot reliably meet this target without causing severe network overhead. To address the network team's load concerns, the architecture should implement OCSP Responders locally within the hospital's data centre, positioned close to the RADIUS servers to minimise latency. The RADIUS servers should be configured to query the local OCSP VIP. To ensure resilience, the RADIUS servers must be configured with a fallback to a locally cached CRL, updated hourly. The failure policy must be set to 'fail closed' due to the healthcare environment's strict compliance requirements.
A global retail chain with 1,200 stores uses SCEP to provision certificates to point-of-sale (POS) tablets. The stores have limited WAN bandwidth. The IT director wants to implement certificate revocation but is concerned that downloading large CRL files across 1,200 branch RADIUS servers will saturate the WAN links. What is the optimal deployment strategy?
The retail chain should implement a hybrid approach utilising Delta CRLs and OCSP Stapling. First, the CA should be configured to publish a Base CRL weekly and a Delta CRL (containing only recent revocations) every 4 hours. The branch RADIUS servers will only download the small Delta CRLs during the day, minimising WAN impact. Alternatively, if the POS tablets' EAP supplicants support it, OCSP Stapling should be enabled. This shifts the burden of fetching the OCSP response from the branch RADIUS server to the tablet itself, which can fetch the response directly from the central CA over standard HTTPS, bypassing the RADIUS server's processing overhead entirely.
Practice Questions
Q1. Your organisation is deploying 802.1X across 50 remote branch offices. The WAN links to the central data centre are highly congested and frequently drop packets. You need to implement certificate revocation for the branch corporate laptops. Which architecture should you choose?
Hint: Consider the impact of packet loss on real-time protocols versus the resilience of cached data.
View model answer
You should implement a CRL-based architecture, specifically using Base and Delta CRLs. Because the WAN links are congested and unreliable, real-time OCSP queries will frequently time out, causing authentication delays or failures. By configuring the branch RADIUS servers to download and cache Delta CRLs during off-peak hours, the local RADIUS server can perform revocation checks instantly against its cache, even if the WAN link drops entirely during the authentication attempt.
Q2. A security audit reveals that when your primary OCSP Responder goes offline for maintenance, all corporate users are completely locked out of the WiFi network. The business demands that maintenance should not impact user connectivity, but the CISO refuses to change the policy to 'Fail Open'. How do you resolve this?
Hint: If you cannot change the failure policy, you must change the availability of the service.
View model answer
You must implement high availability for the OCSP service. Deploy at least one additional OCSP Responder and place both behind a load balancer. Configure the RADIUS server to query the load balancer's Virtual IP (VIP). During maintenance, you can drain connections from the primary responder, take it offline, and the load balancer will seamlessly route all OCSP queries to the secondary responder, satisfying both the business uptime requirement and the CISO's 'Fail Closed' mandate.
Q3. You have configured your MDM to automatically revoke certificates when a device is marked as 'lost'. You test the system by marking a test iPad as lost. The MDM confirms the revocation, but 10 minutes later, the iPad successfully connects to the corporate WiFi. The RADIUS server is configured to use a CRL published every 24 hours. What is the root cause and how do you fix it?
Hint: Trace the timeline of the revocation data from the CA to the RADIUS server's enforcement engine.
View model answer
The root cause is latency in the CRL publication and refresh cycle. While the MDM successfully told the CA to revoke the certificate, the CA will not publish that updated status to the CRL Distribution Point until the next 24-hour cycle, and the RADIUS server will not download it until its own cache expires. To fix this, you must either migrate to OCSP for real-time checking, or drastically reduce the CRL publication and download intervals (e.g., to 1 hour) to meet your required enforcement timeline.