Blocking Malware and Phishing at the Network Edge
This technical reference guide outlines the architecture, deployment, and business impact of implementing network-level threat protection to secure unmanaged guest and IoT devices at the network edge. It provides actionable guidance for IT leaders to block malware and phishing proactively.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Architecture of Network Edge Protection
- Key Components
- Implementation Guide
- Step 1: Network Segmentation
- Step 2: Gateway Configuration
- Step 3: Policy Definition
- Best Practices
- Troubleshooting & Risk Mitigation
- Handling Encrypted DNS
- Over-Blocking Legitimate Traffic
- ROI & Business Impact

Executive Summary
For CTOs and network architects managing high-footfall venues, securing unmanaged devices is a critical operational challenge. You cannot deploy endpoint agents on guest smartphones, nor can you rely on users to avoid malicious links. This guide details how implementing network-level threat protection stops malware and phishing at the network edge before it reaches guest devices. By enforcing security policies at the gateway via DNS filtering and threat intelligence integration, venues can secure BYOD, IoT, and guest traffic proactively. This approach reduces incident response overhead, ensures compliance with standards like GDPR and PCI DSS, and maintains a secure environment for Guest WiFi users across Hospitality , Retail , and Transport sectors.
Technical Deep-Dive
The Architecture of Network Edge Protection
Network edge malware protection shifts the security enforcement point from the endpoint to the gateway. When a device connects to a venue network and attempts to resolve a domain, the DNS query is intercepted by the edge gateway. Instead of standard resolution, the query is evaluated against continuously updated threat intelligence feeds.
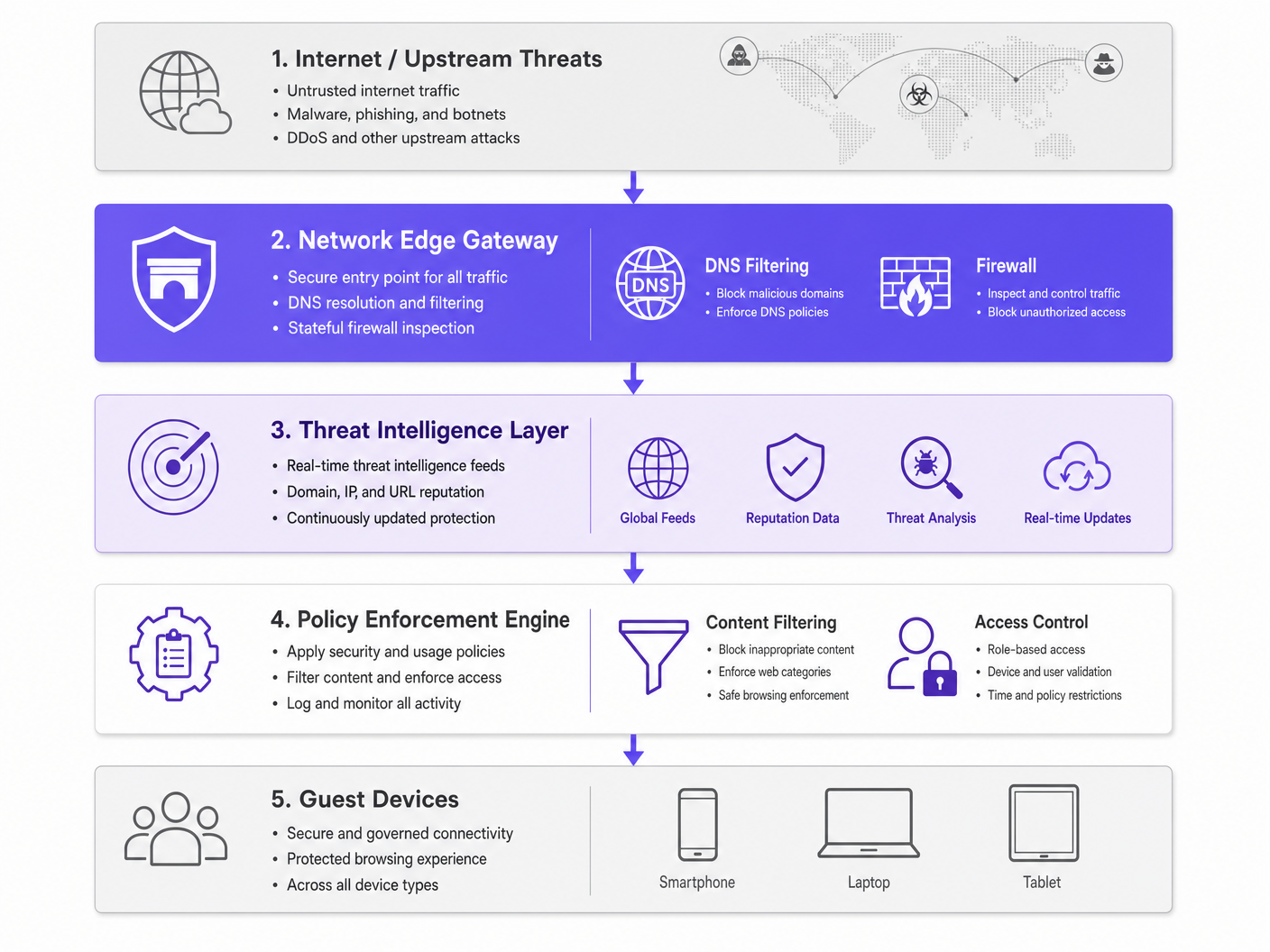
If the domain is associated with malware distribution, phishing campaigns, or botnet command-and-control (C2) infrastructure, the DNS request is sinkholed. The connection is dropped before the malicious payload can be downloaded. This proactive block prevents lateral movement and protects the venue's IP reputation.
Key Components
- DNS Filtering Engine: Inspects all outbound DNS requests. It is critical to configure this engine to block known public DoH (DNS over HTTPS) resolvers to prevent users from bypassing the venue's secure DNS.
- Threat Intelligence Integration: Subscribes to global feeds that categorise domains in real-time based on reputation, newly registered domain status, and known malicious activity.
- Policy Enforcement: Applies granular rules based on user roles (e.g., staff vs. guest) and content categories, ensuring IWF Compliance for Public WiFi Networks in the UK .
Implementation Guide
Deploying network edge protection requires a phased approach to minimise disruption while maximising security coverage.
Step 1: Network Segmentation
Ensure your network is properly segmented using VLANs. Guest traffic, corporate staff, IoT devices, and POS systems must reside on isolated segments. This limits the blast radius if a device is compromised prior to joining the network.
Step 2: Gateway Configuration
Configure your edge routers or firewalls to forward all DNS traffic to the secure DNS filtering service. Implement firewall rules to block outbound traffic on port 53 (DNS) and port 853 (DoT) to any destination other than the approved secure resolvers. For more on modern network optimization, see Office Wi Fi: Optimize Your Modern Office Wi-Fi Network .
Step 3: Policy Definition
Establish baseline policies. Block known malicious categories globally. For content filtering, apply specific policies based on the venue type—for example, stricter filtering in Healthcare environments compared to general retail.
Best Practices
- Granular Policy Application: Avoid blanket blocks that generate helpdesk tickets. Use role-based access control (RBAC) integrated with your identity provider (e.g., Purple's Connect license).
- Comprehensive Logging: Maintain a full audit trail of DNS queries and blocked threats. This is essential for incident response and compliance reporting. See Explain what is audit trail for IT Security in 2026 for detailed requirements.
- Continuous Monitoring: Leverage WiFi Analytics to monitor network performance and security events in real-time.
Troubleshooting & Risk Mitigation
Handling Encrypted DNS
Modern operating systems increasingly use DoH and DoT, which encrypt DNS queries and can bypass traditional edge filtering. To mitigate this, maintain an updated blocklist of known public DoH resolvers (e.g., 8.8.8.8, 1.1.1.1) to force devices to fall back to the venue's provided secure DNS via standard port 53.
Over-Blocking Legitimate Traffic
Aggressive threat intelligence feeds may occasionally flag legitimate domains, especially newly registered ones used for marketing campaigns. Establish a rapid allowlisting process and empower the IT operations team to resolve false positives quickly.
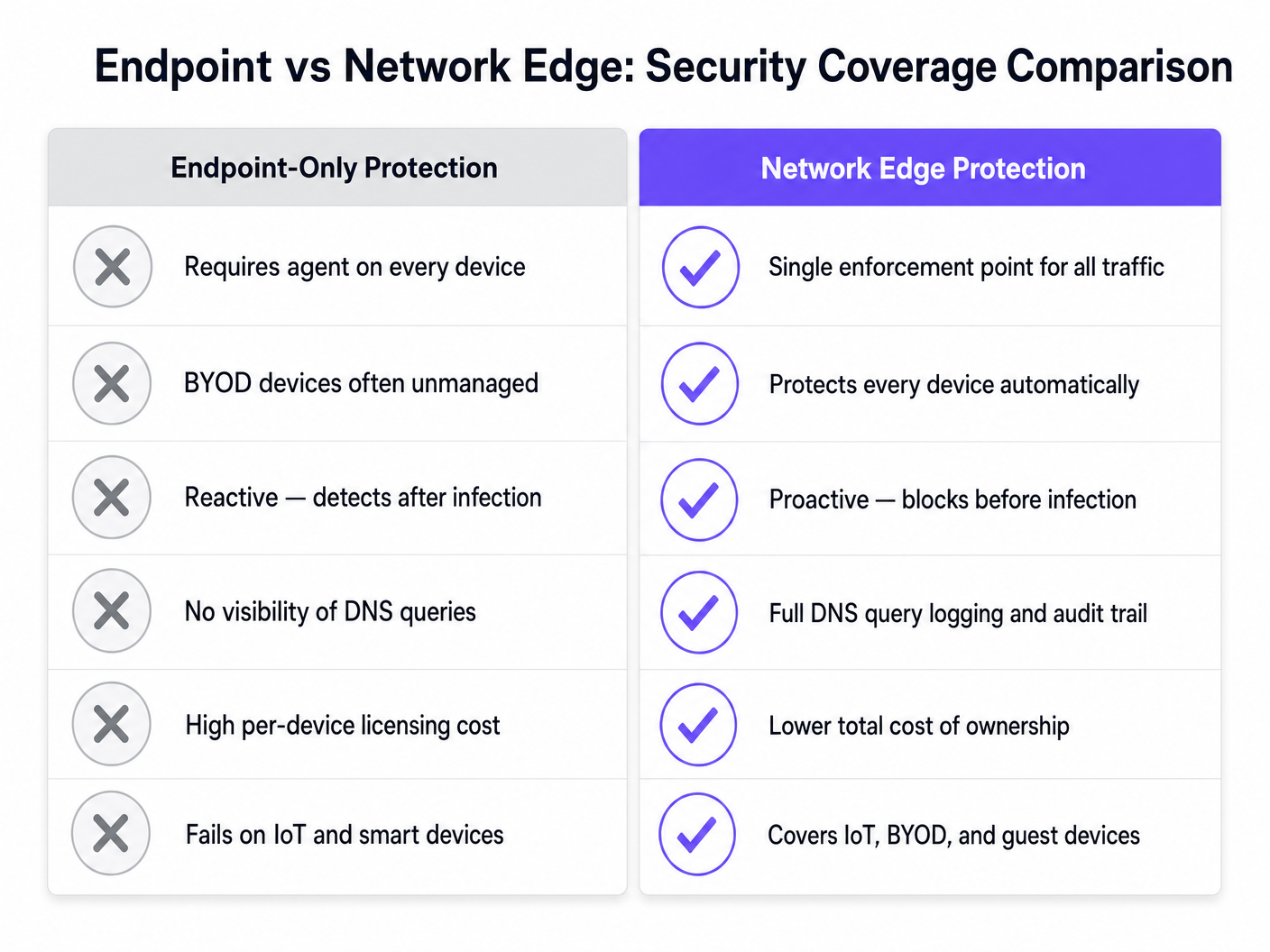
ROI & Business Impact
The business case for network edge malware protection is built on risk mitigation and operational efficiency. By blocking threats at the gateway, venues eliminate the per-device licensing costs associated with endpoint security for BYOD and guest devices. Furthermore, it drastically reduces the IT helpdesk hours spent investigating compromised devices or dealing with blacklisted IP addresses. The resulting secure, reliable connectivity enhances the guest experience and protects the venue's brand reputation.
Key Definitions
Network Edge
The boundary where a local network connects to the internet, typically managed by a router, firewall, or gateway.
This is the optimal location to deploy security controls for unmanaged devices, as all traffic must pass through it.
DNS Filtering
The process of blocking access to certain websites or IP addresses by intercepting DNS queries and evaluating them against a policy or threat feed.
Used to proactively stop devices from connecting to malicious domains before any data is transferred.
Sinkholing
Redirecting malicious traffic to a safe, controlled IP address instead of its intended destination.
When a guest device tries to reach a malware server, the edge gateway sinkholes the request, preventing infection.
Threat Intelligence Feed
A continuously updated stream of data regarding potential or current cyber threats, including known malicious domains and IP addresses.
Edge gateways use these feeds to make real-time decisions on whether to allow or block traffic.
DoH (DNS over HTTPS)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data.
While good for privacy, DoH can bypass corporate edge filtering unless known DoH resolvers are explicitly blocked.
VLAN Segmentation
Dividing a single physical network into multiple logical networks to isolate traffic.
Essential for separating untrusted guest traffic from sensitive corporate or POS systems.
BYOD (Bring Your Own Device)
The practice of allowing employees or guests to use their personal devices on the organisation's network.
BYOD devices are typically unmanaged, making endpoint security impossible and necessitating network edge protection.
Audit Trail
A chronological record of system activities, including DNS queries and blocked connections.
Required for compliance with frameworks like PCI DSS and GDPR to prove security controls are active.
Worked Examples
A 500-room hotel needs to secure guest WiFi while ensuring IoT devices (smart TVs, room controls) are protected from external command-and-control servers.
Deploy a network edge gateway with DNS filtering. Segment the network into Guest, IoT, and Corporate VLANs. Configure the gateway to intercept all DNS queries from the IoT and Guest VLANs, forwarding them to the secure DNS service. Apply a strict policy for the IoT VLAN that only allows resolution of known, required domains (allowlisting), while applying a standard threat-blocking policy for the Guest VLAN.
A large retail chain experiences frequent IP blacklisting due to guest devices sending spam while connected to the in-store WiFi.
Implement network edge malware protection with active threat intelligence feeds. Configure the firewall to block outbound SMTP (port 25) for all guest traffic. Enable DNS filtering to sinkhole requests to known botnet and spam-distribution domains.
Practice Questions
Q1. A stadium network administrator notices that while DNS filtering is enabled, some guest devices are still reaching known malicious domains. What is the most likely cause and how should it be addressed?
Hint: Consider modern protocols that might bypass standard port 53 filtering.
View model answer
The devices are likely using encrypted DNS protocols like DNS over HTTPS (DoH) or DNS over TLS (DoT), which bypass standard port 53 filtering. The administrator should update firewall rules to block known public DoH/DoT resolvers and block outbound traffic on port 853, forcing devices to fall back to the venue's secure DNS.
Q2. When deploying network edge protection in a hospital environment, how should the policies differ between the guest WiFi and the medical IoT device VLAN?
Hint: Think about the concept of least privilege and predictable behavior.
View model answer
The guest WiFi should use a standard threat-blocking policy (blocking malware, phishing, and inappropriate content per IWF guidelines) but generally allow internet access. The medical IoT VLAN should use a strict 'default deny' policy with an allowlist, permitting communication only with specific, required vendor servers. IoT devices have predictable traffic patterns, making allowlisting highly effective.
Q3. A retail client wants to implement edge filtering but is concerned about blocking legitimate marketing campaign domains that are newly registered. What process should be implemented?
Hint: Focus on operational workflows and balancing security with business needs.
View model answer
Implement a rapid allowlisting workflow. While 'Newly Registered Domains' is a common threat category, the IT team should have a process to quickly verify and allowlist domains provided by the marketing team before campaigns launch, ensuring security does not impede business operations.