Is Café and Coffee Shop WiFi Safe?
This authoritative technical guide examines the real security risks of café and coffee shop WiFi for both consumers and venue operators, covering threat vectors including Evil Twin attacks, packet sniffing, and client-to-client exploits. It provides IT managers and network architects with a practical, standards-referenced deployment framework — from VLAN segmentation and WPA3 migration to captive portal implementation and GDPR-compliant analytics. Purple's Guest WiFi and analytics platform is positioned as a concrete solution across hospitality, retail, and public-sector environments.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: The Threat Landscape
- Implementation Guide: Secure Architecture for Venues
- Step 1: Network Segmentation via VLANs
- Step 2: Enable Client Isolation
- Step 3: Deploy a Captive Portal
- Step 4: Implement Content Filtering and Bandwidth Management
- Step 5: Migrate to WPA3
- Best Practices and Industry Standards
- Troubleshooting and Risk Mitigation
- ROI and Business Impact

Executive Summary
For IT managers and network architects overseeing connectivity in retail and hospitality environments, the question "is café WiFi safe?" is no longer a consumer concern — it is a critical business liability. Unsecured public networks expose guests to Man-in-the-Middle (MitM) attacks, rogue hotspots, and packet sniffing, while simultaneously putting the venue's own operational network at risk if improperly segmented.
This guide provides a comprehensive technical breakdown of the risks inherent in coffee shop WiFi deployments. More importantly, it outlines the enterprise-grade architectures required to mitigate these threats. By implementing robust VLAN segmentation, WPA3 encryption, and sophisticated captive portal authentication — such as those provided by Guest WiFi platforms — venues can transform a high-risk amenity into a secure, value-generating asset that complies with PCI DSS and GDPR standards. Whether you operate a single boutique café or a chain of 500 retail locations, the principles in this guide apply at every scale.
Technical Deep-Dive: The Threat Landscape
The fundamental vulnerability of traditional café WiFi lies in its open nature. When a network uses Open System Authentication (no password) or a Pre-Shared Key (PSK) written on a chalkboard, the encryption keys are either easily accessible or entirely absent. This exposes the network to several well-documented attack vectors that any competent threat actor can exploit with commodity hardware.
Evil Twin Attacks and Rogue Access Points represent the most dangerous threat in the café environment. Attackers deploy a malicious Access Point (AP) broadcasting the same SSID as the legitimate café network — for example, "CafeGuest_WiFi". Modern operating systems are configured to auto-connect to previously seen SSIDs, and devices will connect to the strongest signal. Once a user connects to the attacker's AP, all traffic is routed through their hardware, enabling full MitM interception.
Packet Sniffing and Eavesdropping remain viable on unencrypted or weakly encrypted networks. Tools like Wireshark are freely available and require no specialist knowledge to operate. On networks using WEP or even WPA2-Personal with a known PSK, attackers can decrypt captured traffic. While the widespread adoption of HTTPS has reduced the exposure of payload content, session cookies, authentication tokens, and DNS queries remain visible.
Man-in-the-Middle (MitM) Attacks extend beyond simple eavesdropping. By controlling the network gateway, an attacker can perform SSL stripping — downgrading HTTPS connections to HTTP — to intercept credentials and sensitive data in plain text. They can also inject malicious content into unencrypted responses, redirect users to phishing pages, or manipulate DNS responses.
Client-to-Client Attacks are enabled when Layer 2 isolation is absent. If client isolation is not enabled on the wireless controller, devices connected to the same AP share the same broadcast domain. A compromised device can scan for open ports on other guests' machines, exploit local vulnerabilities, or attempt to spread malware laterally across the network.

Implementation Guide: Secure Architecture for Venues
To protect both the consumer and the business, IT teams must deploy a layered security architecture. A flat network where point-of-sale (POS) systems, staff devices, and guest laptops share the same subnet is not merely a security risk — it is a PCI DSS compliance failure with significant financial consequences.
Step 1: Network Segmentation via VLANs
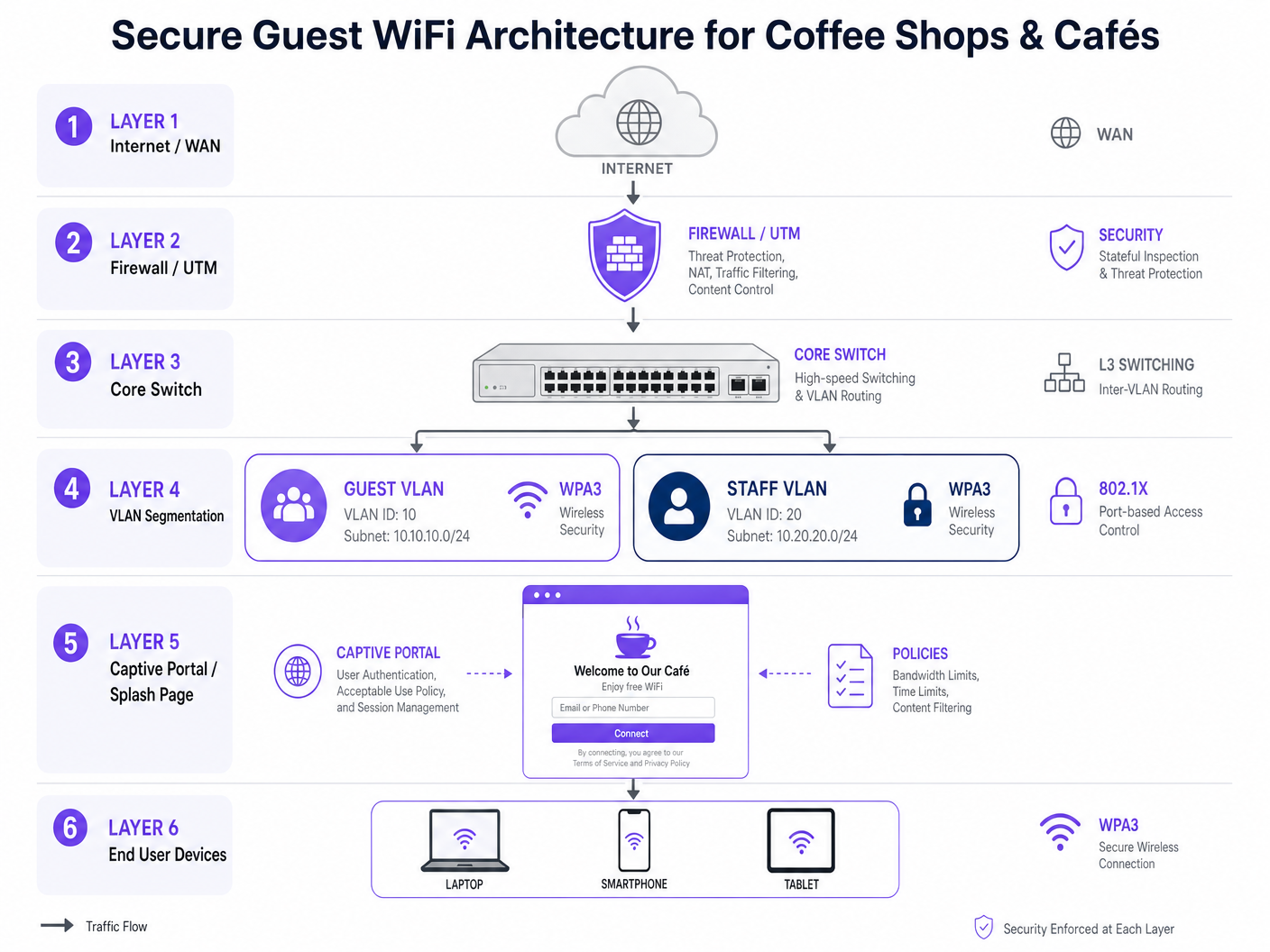
The foundational step is strict Layer 2 segmentation. Guest traffic must be logically separated from corporate and operational traffic at the switch and controller level.
| VLAN | Purpose | Access Policy |
|---|---|---|
| VLAN 10 | Guest WiFi | Internet-only. Deny all routing to internal subnets. |
| VLAN 20 | Staff / Corporate | Secured via 802.1X (RADIUS) authentication. Full internal access. |
| VLAN 30 | IoT / Operations (POS, CCTV) | Strict ACLs. Outbound to payment gateway only. |
| VLAN 99 | Network Management | Restricted to network admin devices only. |
Firewall rules must explicitly deny inter-VLAN routing from VLAN 10 to VLANs 20 and 30. This is the single most important configuration to prevent a guest-side compromise from pivoting into the payment or operational environment.
Step 2: Enable Client Isolation
Enable Client Isolation (also known as AP Isolation or Layer 2 Isolation) on the Guest SSID at the wireless controller level. This prevents devices connected to the same AP from communicating directly with each other, neutralising peer-to-peer attacks and lateral movement across the guest subnet.
Step 3: Deploy a Captive Portal
Replace open networks with a sophisticated captive portal. This serves multiple purposes simultaneously. From a legal standpoint, it enforces acceptance of Terms and Conditions and an Acceptable Use Policy (AUP), protecting the venue from liability for illicit activity on their connection. From a security standpoint, it moves away from anonymous access by authenticating users via email, SMS, or social login. From a commercial standpoint, it integrates with platforms like Purple's WiFi Analytics to gather GDPR-compliant demographic and behavioural data — dwell time, return rate, visit frequency — that feeds directly into marketing automation.
Step 4: Implement Content Filtering and Bandwidth Management
Deploy DNS-based content filtering to block malicious domains, phishing sites, and inappropriate content. This protects the venue's reputation and prevents the network from being used for illegal activities. Apply per-user rate limiting (e.g., 5 Mbps down / 2 Mbps up) and session timeouts (e.g., 2 hours) to prevent network abuse and ensure fair access for all patrons.
Step 5: Migrate to WPA3
The industry is moving away from WPA2-Personal toward WPA3-SAE (Simultaneous Authentication of Equals) and, for enterprise deployments, WPA3-Enterprise. WPA3 provides forward secrecy, meaning that even if a session key is compromised, past sessions cannot be decrypted. For venues planning longer-term roadmaps, Passpoint (Hotspot 2.0) and OpenRoaming provide cellular-like secure authentication without a captive portal.
Best Practices and Industry Standards
The following standards and frameworks should govern any enterprise café or retail WiFi deployment.
| Standard | Relevance | Key Requirement |
|---|---|---|
| PCI DSS v4.0 | Payment card data protection | Complete network isolation between guest and cardholder data environments. |
| GDPR / UK GDPR | Personal data collected via captive portal | Explicit consent, data minimisation, right to erasure. |
| IEEE 802.1X | Port-based network access control | RADIUS authentication for staff and management VLANs. |
| WPA3 (IEEE 802.11ax) | Over-the-air encryption | Mandatory for new deployments; plan migration for legacy hardware. |
| NIST SP 800-153 | Guidelines for WLAN security | Comprehensive wireless security policy framework. |
For sector-specific guidance, Purple has published dedicated deployment resources for Retail , Hospitality , Healthcare , and Transport environments. Related technical reading includes our guide on WiFi in Hospitals: A Guide to Secure Clinical Networks and the Is Airport WiFi Safe? A Traveller's Security Guide , which covers analogous threat models in high-density public environments.
Troubleshooting and Risk Mitigation
Even with a robust architecture in place, operational failures can introduce risk. The following are the most common failure modes encountered in real-world deployments.
The Hidden Rogue AP. Staff or third-party vendors sometimes plug unauthorised consumer-grade routers into wall ports to extend coverage. These rogue APs bypass the corporate firewall and captive portal entirely, creating a significant security gap. Mitigation requires enabling Rogue AP detection on the wireless controller and implementing Port Security (802.1X or MAC limiting) on all physical switch ports to prevent unauthorised devices from gaining network access.
DNS Hijacking on the Captive Portal. If the captive portal is not secured with a valid SSL certificate (HTTPS), attackers can spoof the portal page to harvest guest credentials. Ensure all captive portal redirections use HTTPS with valid, auto-renewing certificates. Enterprise platforms like Purple handle this by default.
Firmware Vulnerabilities. The KRACK (Key Reinstallation Attack) vulnerability demonstrated that even WPA2 has exploitable weaknesses at the protocol level. Maintain a strict quarterly patching schedule for all APs, switches, and firewalls, and automate firmware updates where the controller supports it.
Misconfigured ACLs. A common error is creating the correct VLANs but failing to configure the firewall ACLs to deny inter-VLAN routing. Always validate segmentation post-deployment using a penetration test or at minimum a manual scan from a guest device attempting to reach internal subnets.
ROI and Business Impact
Investing in secure café WiFi is not merely a cost centre — it is a strategic enabler with measurable returns across three dimensions.
Risk Mitigation Value. A single PCI DSS breach resulting from a compromised guest network bridging to a POS system can result in fines of up to £100,000 per month under UK GDPR, plus card scheme penalties and the cost of forensic investigation. The infrastructure investment is trivially justified against this exposure.
Marketing ROI. By gating access behind a secure, compliant captive portal, venues build a first-party data asset at scale. Every authenticated connection adds a verified profile — email, demographics, visit history — to a CRM. This data feeds directly into marketing automation, driving repeat visits and measurable loyalty uplift. Purple's Guest WiFi platform is purpose-built for this use case, with integrations to major marketing automation and CRM platforms.
Operational Intelligence. Integrating WiFi Analytics provides physical space metrics that rival e-commerce analytics in their granularity. Footfall by hour, dwell time by zone, return visitor rate, and peak capacity data allow operations directors to make data-driven decisions on staffing, layout, and promotional timing. For venues exploring more advanced location services, our Indoor Positioning System: UWB, BLE, and WiFi Guide covers the next tier of spatial analytics.
The business case is clear: secure WiFi infrastructure, deployed correctly with a managed platform, pays for itself through risk avoidance, marketing efficiency, and operational optimisation.
Key Terms & Definitions
Evil Twin Attack
A rogue wireless access point that masquerades as a legitimate Wi-Fi network by broadcasting the same SSID, used to intercept traffic, steal credentials, or perform Man-in-the-Middle attacks.
Common in high-density public environments like cafés and airports. Mitigated by deploying Rogue AP detection on enterprise wireless controllers and educating users to verify the network via a captive portal URL.
Client Isolation (Layer 2 Isolation)
A wireless network security feature configured at the AP or controller level that prevents devices connected to the same access point from communicating directly with each other at the data link layer.
Essential for all public WiFi deployments. Prevents peer-to-peer attacks, port scanning, and malware propagation among guests. Must be explicitly enabled — it is not active by default on most platforms.
VLAN (Virtual Local Area Network)
A logical grouping of network devices that behave as if they are on a single isolated LAN, enforced at the switch level via IEEE 802.1Q tagging, regardless of physical location.
The primary mechanism for separating guest WiFi traffic from corporate, POS, and management traffic. Critical for PCI DSS compliance and for containing the blast radius of a security incident.
Captive Portal
A web-based authentication gateway that intercepts HTTP/HTTPS traffic from unauthenticated users and redirects them to a login or registration page before granting network access.
Serves as the legal, security, and commercial interface between the venue and the guest. Used to enforce Acceptable Use Policies, collect GDPR-compliant first-party data, and integrate with marketing platforms.
Packet Sniffing
The capture and inspection of data packets traversing a network, typically using tools such as Wireshark or tcpdump.
On unencrypted or weakly encrypted networks, attackers can extract session cookies, authentication tokens, and plain-text credentials from captured traffic. Mitigated by enforcing WPA3 encryption and HTTPS-only policies.
WPA3 (Wi-Fi Protected Access 3)
The current Wi-Fi security certification standard, introducing Simultaneous Authentication of Equals (SAE) to replace the vulnerable PSK handshake, providing forward secrecy and resistance to offline dictionary attacks.
The mandatory target for all new wireless deployments. Venues still running WPA2-Personal with a shared PSK should treat migration to WPA3 as a priority infrastructure project.
OpenRoaming / Passpoint (Hotspot 2.0)
A Wi-Fi Alliance standard (IEEE 802.11u) that enables devices to automatically discover and securely authenticate to trusted Wi-Fi networks using a pre-provisioned credential or identity provider profile, without manual intervention.
Represents the next generation of public WiFi security, providing cellular-like roaming and enterprise-grade encryption over public airwaves. Relevant for venues planning 3–5 year network roadmaps.
Rogue AP
An unauthorised wireless access point connected to a corporate network without the explicit authorisation of the network administrator.
Most commonly installed by well-meaning staff attempting to fix coverage dead zones. Bypasses corporate security policies, captive portals, and VLANs. Detected via wireless intrusion detection systems (WIDS) built into enterprise controllers.
SSL Stripping
A Man-in-the-Middle attack technique that downgrades an HTTPS connection to HTTP by intercepting the initial redirect, allowing the attacker to read and modify traffic in plain text.
Viable on networks where the attacker controls the gateway. Mitigated by HSTS (HTTP Strict Transport Security) headers on websites and by ensuring the captive portal itself uses HTTPS.
Case Studies
A national coffee shop chain with 500 locations is upgrading its network. They currently use an open SSID with a shared password written on the counter. They have recently introduced mobile ordering with a POS integration, and their compliance team has flagged a PCI DSS gap. They also want to start collecting customer data for a new loyalty programme. How should they architect the network to address all three requirements simultaneously?
Phase 1 — Network Segmentation: Deploy enterprise-grade APs capable of multi-SSID broadcasting and VLAN tagging across all 500 locations via a centralised cloud controller. Create three VLANs: Guest (VLAN 10, internet-only), POS/Mobile Order (VLAN 20, isolated to payment gateway egress only), and Management (VLAN 99, admin-only). Configure the firewall at each site with explicit deny rules blocking all inter-VLAN routing from VLAN 10 to VLAN 20. Phase 2 — Guest Security: Enable Client Isolation on the Guest SSID. Retire the shared PSK and implement a captive portal (Purple) requiring email or loyalty app authentication, paired with an Acceptable Use Policy. Phase 3 — Compliance and Analytics: Configure the captive portal to collect GDPR-compliant consent at the point of authentication. Integrate the Purple platform with the chain's CRM and marketing automation tools to begin building the first-party data asset for the loyalty programme.
A boutique hotel café is experiencing poor guest WiFi performance. Guests are complaining they cannot stream video or join video calls. The IT manager discovers that a small number of users are consuming the entire 200 Mbps WAN link with large downloads. Simultaneously, the hotel's security team has flagged that guest devices appear to be scanning other devices on the same subnet. How should the IT manager resolve both issues?
Performance Fix: Implement Per-User Bandwidth Limiting at the wireless controller level, capping each authenticated device at 10 Mbps down / 5 Mbps up. Implement Application Layer (Layer 7) Traffic Shaping to deprioritise P2P file sharing and large software update traffic during peak hours (07:00–22:00). Enforce a Session Timeout of 4 hours on the captive portal to clear inactive sessions and free up DHCP leases. Security Fix: Enable Client Isolation (AP Isolation) on the Guest SSID immediately. This is the root cause of the subnet scanning issue — without it, guest devices share a broadcast domain and can communicate directly. Validate the fix by running a post-change scan from a guest device to confirm it cannot reach other guest devices on the subnet.
Scenario Analysis
Q1. You are auditing a newly acquired coffee shop's network. You find that the guest WiFi and the back-office PC used for inventory management and payroll processing are on the same 192.168.1.0/24 subnet with no firewall between them. What is the immediate technical recommendation, and what compliance framework does this violation fall under?
💡 Hint:Consider the implications for lateral movement, data exfiltration, and the specific compliance standard that governs the separation of cardholder data environments.
Show Recommended Approach
Immediate action: Implement VLAN segmentation. Create a dedicated VLAN for guest traffic (VLAN 10) and a separate VLAN for corporate back-office devices (VLAN 20). Configure the firewall with explicit ACL rules blocking all inter-VLAN routing from VLAN 10 to VLAN 20. Enable client isolation on the guest SSID. Compliance context: If the back-office PC is in scope for payment card processing, this is a PCI DSS violation — specifically Requirement 1.3, which mandates that systems in the cardholder data environment are isolated from untrusted networks. Even if the PC is not directly processing payments, the flat network creates an unacceptable risk of lateral movement from a compromised guest device.
Q2. A venue operations director wants to remove the captive portal from their café network because 'it adds friction' and they want an open network with no authentication. How do you advise them from both a security and a commercial perspective?
💡 Hint:Address the legal liability, the GDPR implications, and the lost commercial value of the first-party data asset.
Show Recommended Approach
Advise strongly against this. From a legal standpoint, removing the captive portal means no Acceptable Use Policy is enforced, leaving the venue potentially liable for illegal activity conducted over their connection. From a GDPR standpoint, if the venue is collecting any data about users (even connection logs), they need a lawful basis — the captive portal consent mechanism provides this. From a commercial standpoint, the captive portal is the mechanism that converts anonymous footfall into a verified, marketable first-party data asset. Removing it eliminates the ability to build a loyalty database, run targeted marketing campaigns, or measure the return on the WiFi investment. The 'friction' argument is addressed by optimising the portal UX — single-click social login or SMS authentication takes under 10 seconds — not by removing the portal entirely.
Q3. During a penetration test of a café's network, the tester successfully captured another user's HTTP session cookie while connected to the Guest SSID. They also successfully reached a device on the 10.20.0.0/24 subnet (the staff network) from the guest network. Identify the two specific misconfigurations responsible for each finding.
💡 Hint:One finding relates to wireless controller configuration; the other relates to firewall ACL configuration.
Show Recommended Approach
Finding 1 (session cookie capture): Client Isolation is disabled on the Guest SSID. When enabled, this setting prevents wireless clients connected to the same AP from communicating directly at Layer 2, which would prevent the tester from capturing traffic from another guest device. Finding 2 (cross-VLAN access): The firewall ACLs are misconfigured. Either the inter-VLAN routing deny rule between the Guest VLAN and the Staff VLAN is absent, incorrectly ordered, or the VLANs are not correctly tagged at the switch level. The fix is to add an explicit deny rule on the firewall blocking all traffic from the Guest VLAN (e.g., 10.10.0.0/24) to the Staff VLAN (10.20.0.0/24), and to validate this with a post-change penetration test.



