O WiFi de Cafés e Cafetarias é Seguro?
Este guia técnico autorizado examina os riscos de segurança reais do WiFi de cafés e cafetarias tanto para consumidores como para operadores de espaços, cobrindo vetores de ameaça incluindo ataques Evil Twin, packet sniffing e exploits cliente-a-cliente. Fornece a gestores de TI e arquitetos de rede um framework de implementação prático e referenciado por padrões — desde a segmentação VLAN e migração WPA3 até à implementação de Captive Portal e análises compatíveis com GDPR. A plataforma Guest WiFi e de análises da Purple é posicionada como uma solução concreta em ambientes de hotelaria, retalho e setor público.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: O Cenário de Ameaças
- Guia de Implementação: Arquitetura Segura para Espaços
- Passo 1: Segmentação de Rede via VLANs
- Passo 2: Ativar o Isolamento de Cliente
- Passo 3: Implementar um Captive Portal
- Passo 4: Implementar Filtragem de Conteúdo e Gestão de Largura de Banda
- Passo 5: Migrar para WPA3
- Melhores Práticas e Normas da Indústria
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio

Resumo Executivo
Para gestores de TI e arquitetos de rede que supervisionam a conectividade em ambientes de retalho e hotelaria, a questão "o WiFi de cafés é seguro?" já não é uma preocupação do consumidor — é uma responsabilidade empresarial crítica. Redes públicas não seguras expõem os convidados a ataques Man-in-the-Middle (MitM), hotspots fraudulentos e packet sniffing, ao mesmo tempo que colocam em risco a própria rede operacional do espaço se esta não for devidamente segmentada.
Este guia fornece uma análise técnica abrangente dos riscos inerentes às implementações de WiFi em cafetarias. Mais importante, descreve as arquiteturas de nível empresarial necessárias para mitigar estas ameaças. Ao implementar uma segmentação VLAN robusta, encriptação WPA3 e autenticação sofisticada de Captive Portal — como as fornecidas por plataformas Guest WiFi — os espaços podem transformar uma comodidade de alto risco num ativo seguro e gerador de valor que cumpre os padrões PCI DSS e GDPR. Quer opere um único café boutique ou uma cadeia de 500 lojas de retalho, os princípios deste guia aplicam-se a todas as escalas.
Análise Técnica Aprofundada: O Cenário de Ameaças
A vulnerabilidade fundamental do WiFi tradicional de cafés reside na sua natureza aberta. Quando uma rede utiliza Autenticação de Sistema Aberto (sem palavra-passe) ou uma Chave Pré-Partilhada (PSK) escrita num quadro, as chaves de encriptação são facilmente acessíveis ou totalmente ausentes. Isto expõe a rede a vários vetores de ataque bem documentados que qualquer ator de ameaça competente pode explorar com hardware comum.
Ataques Evil Twin e Pontos de Acesso Maliciosos representam a ameaça mais perigosa no ambiente de café. Os atacantes implementam um Ponto de Acesso (AP) malicioso que transmite o mesmo SSID que a rede legítima do café — por exemplo, "CafeGuest_WiFi". Os sistemas operativos modernos estão configurados para se ligarem automaticamente a SSIDs vistos anteriormente, e os dispositivos ligar-se-ão ao sinal mais forte. Uma vez que um utilizador se liga ao AP do atacante, todo o tráfego é encaminhado através do seu hardware, permitindo a interceção MitM completa.
Packet Sniffing e Escuta permanecem viáveis em redes não encriptadas ou fracamente encriptadas. Ferramentas como o Wireshark estão livremente disponíveis e não requerem conhecimento especializado para operar. Em redes que utilizam WEP ou mesmo WPA2-Personal com uma PSK conhecida, os atacantes podem desencriptar o tráfego capturado. Embora a adoção generalizada de HTTPS tenha reduzido a exposição do conteúdo da carga útil, os cookies de sessão, tokens de autenticação e consultas DNS permanecem visíveis.
Ataques Man-in-the-Middle (MitM) vão além da simples escuta. Ao controlar o gateway da rede, um atacante pode realizar SSL stripping — desgraduando as ligações HTTPS para HTTP — para intercetar credenciais e dados sensíveis em texto simples. Podem também injetar conteúdo malicioso em respostas não encriptadas, redirecionar utilizadores para páginas de phishing ou manipular respostas DNS.
Ataques Cliente-a-Cliente são ativados quando a isolamento da Camada 2 está ausente. Se o isolamento de cliente não estiver ativado no controlador wireless, os dispositivos ligados ao mesmo AP partilham o mesmo domínio de difusão. Um dispositivo comprometido pode procurar portas abertas nas máquinas de outros convidados, explorar vulnerabilidades locais ou tentar espalhar malware lateralmente pela rede.

Guia de Implementação: Arquitetura Segura para Espaços
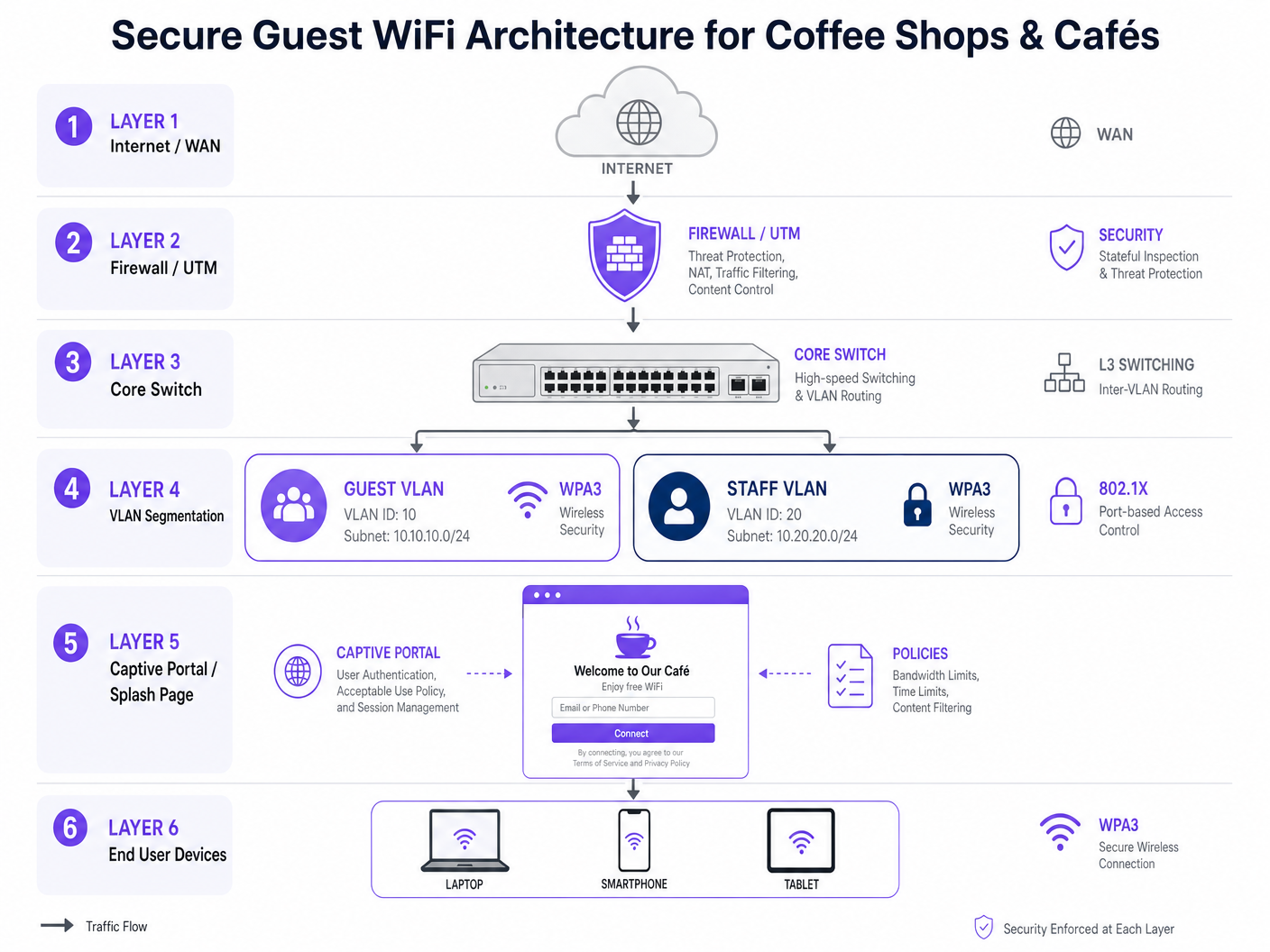
Para proteger tanto o consumidor como o negócio, as equipas de TI devem implementar uma arquitetura de segurança em camadas. Uma rede plana onde os sistemas de ponto de venda (POS), dispositivos de funcionários e portáteis de convidados partilham a mesma sub-rede não é meramente um risco de segurança — é uma falha de conformidade PCI DSS com consequências financeiras significativas.
Passo 1: Segmentação de Rede via VLANs
O passo fundamental é a segmentação rigorosa da Camada 2. O tráfego de convidados deve ser logicamente separado do tráfego corporativo e operacional ao nível do switch e do controlador.
| VLAN | Propósito | Política de Acesso |
|---|---|---|
| VLAN 10 | Guest WiFi | Apenas Internet. Negar todo o encaminhamento para sub-redes internas. |
| VLAN 20 | Funcionários / Corporativo | Protegido via autenticação 802.1X (RADIUS). Acesso interno total. |
| VLAN 30 | IoT / Operações (POS, CCTV) | ACLs rigorosas. Apenas saída para gateway de pagamento. |
| VLAN 99 | Gestão de Rede | Restrito apenas a dispositivos de administração de rede. |
As regras da firewall devem negar explicitamente o encaminhamento inter-VLAN da VLAN 10 para as VLANs 20 e 30. Esta é a configuração mais importante para evitar que um comprometimento do lado do convidado se propague para o ambiente de pagamento ou operacional.
Passo 2: Ativar o Isolamento de Cliente
Ativar o Isolamento de Cliente (também conhecido como Isolamento de AP ou Isolamento da Camada 2) no Guest SSID ao nível do controlador wireless. Isto impede que os dispositivos ligados ao mesmo AP comuniquem diretamente entre si, neutralizando ataques peer-to-peer e movimento lateral através da sub-rede de convidados.
Passo 3: Implementar um Captive Portal
Substitua redes abertas por um Captive Portal sofisticado. Isto serve múltiplos propósitos simultaneamente. Do ponto de vista legal, impõe a aceitação dos Termos e Condições e de uma Política de Utilização Aceitável (AUP), protegendo o espaço de responsabilidade por atividade ilícita na sua ligação. Do ponto de vista da segurança, afasta-se do acesso anónimo ao autenticar utilizadores via e-mail, SMS ou login social. Do ponto de vista comercial, integra-se com plataformas como o WiFi Analytics da Purple para recolher dados demográficos e comportamentais compatíveis com GDPR — tempo de permanência, taxa de retorno, frequência de visitaência — que alimenta diretamente a automação de marketing.
Passo 4: Implementar Filtragem de Conteúdo e Gestão de Largura de Banda
Implemente filtragem de conteúdo baseada em DNS para bloquear domínios maliciosos, sites de phishing e conteúdo inadequado. Isto protege a reputação do local e impede que a rede seja utilizada para atividades ilegais. Aplique limitação de taxa por utilizador (por exemplo, 5 Mbps de download / 2 Mbps de upload) e tempos limite de sessão (por exemplo, 2 horas) para evitar o abuso da rede e garantir acesso justo para todos os clientes.
Passo 5: Migrar para WPA3
A indústria está a afastar-se do WPA2-Personal em direção ao WPA3-SAE (Simultaneous Authentication of Equals) e, para implementações empresariais, ao WPA3-Enterprise. O WPA3 oferece sigilo de encaminhamento, o que significa que, mesmo que uma chave de sessão seja comprometida, sessões anteriores não podem ser desencriptadas. Para locais que planeiam roteiros a longo prazo, o Passpoint (Hotspot 2.0) e o OpenRoaming fornecem autenticação segura semelhante à celular, sem um captive portal.
Melhores Práticas e Normas da Indústria
As seguintes normas e frameworks devem reger qualquer implementação de WiFi em cafés empresariais ou retalho.
| Norma | Relevância | Requisito Chave |
|---|---|---|
| PCI DSS v4.0 | Proteção de dados de cartões de pagamento | Isolamento completo da rede entre ambientes de dados de convidados e titulares de cartões. |
| GDPR / UK GDPR | Dados pessoais recolhidos via captive portal | Consentimento explícito, minimização de dados, direito ao apagamento. |
| IEEE 802.1X | Controlo de acesso à rede baseado em porta | Autenticação RADIUS para VLANs de pessoal e gestão. |
| WPA3 (IEEE 802.11ax) | Encriptação over-the-air | Obrigatório para novas implementações; planear a migração para hardware legado. |
| NIST SP 800-153 | Orientações para segurança WLAN | Framework abrangente de política de segurança sem fios. |
Para orientação específica do setor, a Purple publicou recursos de implementação dedicados para ambientes de Retalho , Hotelaria , Saúde e Transportes . A leitura técnica relacionada inclui o nosso guia sobre WiFi em Hospitais: Um Guia para Redes Clínicas Seguras e o O WiFi do Aeroporto é Seguro? Um Guia de Segurança para Viajantes , que aborda modelos de ameaça análogos em ambientes públicos de alta densidade.
Resolução de Problemas e Mitigação de Riscos
Mesmo com uma arquitetura robusta implementada, falhas operacionais podem introduzir riscos. Os seguintes são os modos de falha mais comuns encontrados em implementações reais.
O AP Malicioso Oculto. O pessoal ou fornecedores terceiros, por vezes, ligam routers de consumo não autorizados a portas de parede para estender a cobertura. Estes APs maliciosos contornam completamente a firewall corporativa e o captive portal, criando uma lacuna de segurança significativa. A mitigação requer a ativação da deteção de APs Maliciosos no controlador sem fios e a implementação de Segurança de Porta (802.1X ou limitação de MAC) em todas as portas físicas do switch para impedir que dispositivos não autorizados obtenham acesso à rede.
Sequestro de DNS no Captive Portal. Se o captive portal não estiver seguro com um certificado SSL (HTTPS) válido, os atacantes podem falsificar a página do portal para recolher credenciais de convidados. Garanta que todos os redirecionamentos do captive portal utilizam HTTPS com certificados válidos e de renovação automática. Plataformas empresariais como a Purple tratam disto por predefinição.
Vulnerabilidades de Firmware. A vulnerabilidade KRACK (Key Reinstallation Attack) demonstrou que mesmo o WPA2 possui fraquezas exploráveis ao nível do protocolo. Mantenha um rigoroso cronograma trimestral de aplicação de patches para todos os APs, switches e firewalls, e automatize as atualizações de firmware onde o controlador o suporte.
ACLs Mal Configuradas. Um erro comum é criar as VLANs corretas, mas falhar na configuração das ACLs da firewall para negar o encaminhamento inter-VLAN. Valide sempre a segmentação pós-implementação utilizando um teste de penetração ou, no mínimo, uma análise manual a partir de um dispositivo convidado a tentar aceder a sub-redes internas.
ROI e Impacto no Negócio
Investir em WiFi seguro para cafés não é meramente um centro de custos — é um facilitador estratégico com retornos mensuráveis em três dimensões.
Valor da Mitigação de Riscos. Uma única violação do PCI DSS resultante de uma rede de convidados comprometida que se liga a um sistema POS pode resultar em multas de até £100.000 por mês ao abrigo do UK GDPR, mais penalidades do esquema de cartões e o custo da investigação forense. O investimento em infraestrutura é trivialmente justificado face a esta exposição.
ROI de Marketing. Ao restringir o acesso através de um captive portal seguro e compatível, os locais constroem um ativo de dados primários em escala. Cada conexão autenticada adiciona um perfil verificado — e-mail, dados demográficos, histórico de visitas — a um CRM. Estes dados alimentam diretamente a automação de marketing, impulsionando visitas repetidas e um aumento mensurável da lealdade. A plataforma Guest WiFi da Purple é construída especificamente para este caso de uso, com integrações a grandes plataformas de automação de marketing e CRM.
Inteligência Operacional. A integração de WiFi Analytics fornece métricas de espaço físico que rivalizam com a análise de e-commerce na sua granularidade. Dados de afluência por hora, tempo de permanência por zona, taxa de visitantes recorrentes e capacidade máxima permitem que os diretores de operações tomem decisões baseadas em dados sobre pessoal, layout e timing promocional. Para locais que exploram serviços de localização mais avançados, o nosso Sistema de Posicionamento Interior: Guia UWB, BLE e WiFi abrange o próximo nível de análise espacial.
O caso de negócio é claro: uma infraestrutura WiFi segura, implementada corretamente com uma plataforma gerida, paga-se a si mesma através da prevenção de riscos, eficiência de marketing e otimização operacional.
Termos-Chave e Definições
Evil Twin Attack
A rogue wireless access point that masquerades as a legitimate Wi-Fi network by broadcasting the same SSID, used to intercept traffic, steal credentials, or perform Man-in-the-Middle attacks.
Common in high-density public environments like cafés and airports. Mitigated by deploying Rogue AP detection on enterprise wireless controllers and educating users to verify the network via a captive portal URL.
Client Isolation (Layer 2 Isolation)
A wireless network security feature configured at the AP or controller level that prevents devices connected to the same access point from communicating directly with each other at the data link layer.
Essential for all public WiFi deployments. Prevents peer-to-peer attacks, port scanning, and malware propagation among guests. Must be explicitly enabled — it is not active by default on most platforms.
VLAN (Virtual Local Area Network)
A logical grouping of network devices that behave as if they are on a single isolated LAN, enforced at the switch level via IEEE 802.1Q tagging, regardless of physical location.
The primary mechanism for separating guest WiFi traffic from corporate, POS, and management traffic. Critical for PCI DSS compliance and for containing the blast radius of a security incident.
Captive Portal
A web-based authentication gateway that intercepts HTTP/HTTPS traffic from unauthenticated users and redirects them to a login or registration page before granting network access.
Serves as the legal, security, and commercial interface between the venue and the guest. Used to enforce Acceptable Use Policies, collect GDPR-compliant first-party data, and integrate with marketing platforms.
Packet Sniffing
The capture and inspection of data packets traversing a network, typically using tools such as Wireshark or tcpdump.
On unencrypted or weakly encrypted networks, attackers can extract session cookies, authentication tokens, and plain-text credentials from captured traffic. Mitigated by enforcing WPA3 encryption and HTTPS-only policies.
WPA3 (Wi-Fi Protected Access 3)
The current Wi-Fi security certification standard, introducing Simultaneous Authentication of Equals (SAE) to replace the vulnerable PSK handshake, providing forward secrecy and resistance to offline dictionary attacks.
The mandatory target for all new wireless deployments. Venues still running WPA2-Personal with a shared PSK should treat migration to WPA3 as a priority infrastructure project.
OpenRoaming / Passpoint (Hotspot 2.0)
A Wi-Fi Alliance standard (IEEE 802.11u) that enables devices to automatically discover and securely authenticate to trusted Wi-Fi networks using a pre-provisioned credential or identity provider profile, without manual intervention.
Represents the next generation of public WiFi security, providing cellular-like roaming and enterprise-grade encryption over public airwaves. Relevant for venues planning 3–5 year network roadmaps.
Rogue AP
An unauthorised wireless access point connected to a corporate network without the explicit authorisation of the network administrator.
Most commonly installed by well-meaning staff attempting to fix coverage dead zones. Bypasses corporate security policies, captive portals, and VLANs. Detected via wireless intrusion detection systems (WIDS) built into enterprise controllers.
SSL Stripping
A Man-in-the-Middle attack technique that downgrades an HTTPS connection to HTTP by intercepting the initial redirect, allowing the attacker to read and modify traffic in plain text.
Viable on networks where the attacker controls the gateway. Mitigated by HSTS (HTTP Strict Transport Security) headers on websites and by ensuring the captive portal itself uses HTTPS.
Estudos de Caso
A national coffee shop chain with 500 locations is upgrading its network. They currently use an open SSID with a shared password written on the counter. They have recently introduced mobile ordering with a POS integration, and their compliance team has flagged a PCI DSS gap. They also want to start collecting customer data for a new loyalty programme. How should they architect the network to address all three requirements simultaneously?
Phase 1 — Network Segmentation: Deploy enterprise-grade APs capable of multi-SSID broadcasting and VLAN tagging across all 500 locations via a centralised cloud controller. Create three VLANs: Guest (VLAN 10, internet-only), POS/Mobile Order (VLAN 20, isolated to payment gateway egress only), and Management (VLAN 99, admin-only). Configure the firewall at each site with explicit deny rules blocking all inter-VLAN routing from VLAN 10 to VLAN 20. Phase 2 — Guest Security: Enable Client Isolation on the Guest SSID. Retire the shared PSK and implement a captive portal (Purple) requiring email or loyalty app authentication, paired with an Acceptable Use Policy. Phase 3 — Compliance and Analytics: Configure the captive portal to collect GDPR-compliant consent at the point of authentication. Integrate the Purple platform with the chain's CRM and marketing automation tools to begin building the first-party data asset for the loyalty programme.
A boutique hotel café is experiencing poor guest WiFi performance. Guests are complaining they cannot stream video or join video calls. The IT manager discovers that a small number of users are consuming the entire 200 Mbps WAN link with large downloads. Simultaneously, the hotel's security team has flagged that guest devices appear to be scanning other devices on the same subnet. How should the IT manager resolve both issues?
Performance Fix: Implement Per-User Bandwidth Limiting at the wireless controller level, capping each authenticated device at 10 Mbps down / 5 Mbps up. Implement Application Layer (Layer 7) Traffic Shaping to deprioritise P2P file sharing and large software update traffic during peak hours (07:00–22:00). Enforce a Session Timeout of 4 hours on the captive portal to clear inactive sessions and free up DHCP leases. Security Fix: Enable Client Isolation (AP Isolation) on the Guest SSID immediately. This is the root cause of the subnet scanning issue — without it, guest devices share a broadcast domain and can communicate directly. Validate the fix by running a post-change scan from a guest device to confirm it cannot reach other guest devices on the subnet.
Análise de Cenários
Q1. You are auditing a newly acquired coffee shop's network. You find that the guest WiFi and the back-office PC used for inventory management and payroll processing are on the same 192.168.1.0/24 subnet with no firewall between them. What is the immediate technical recommendation, and what compliance framework does this violation fall under?
💡 Dica:Consider the implications for lateral movement, data exfiltration, and the specific compliance standard that governs the separation of cardholder data environments.
Mostrar Abordagem Recomendada
Immediate action: Implement VLAN segmentation. Create a dedicated VLAN for guest traffic (VLAN 10) and a separate VLAN for corporate back-office devices (VLAN 20). Configure the firewall with explicit ACL rules blocking all inter-VLAN routing from VLAN 10 to VLAN 20. Enable client isolation on the guest SSID. Compliance context: If the back-office PC is in scope for payment card processing, this is a PCI DSS violation — specifically Requirement 1.3, which mandates that systems in the cardholder data environment are isolated from untrusted networks. Even if the PC is not directly processing payments, the flat network creates an unacceptable risk of lateral movement from a compromised guest device.
Q2. A venue operations director wants to remove the captive portal from their café network because 'it adds friction' and they want an open network with no authentication. How do you advise them from both a security and a commercial perspective?
💡 Dica:Address the legal liability, the GDPR implications, and the lost commercial value of the first-party data asset.
Mostrar Abordagem Recomendada
Advise strongly against this. From a legal standpoint, removing the captive portal means no Acceptable Use Policy is enforced, leaving the venue potentially liable for illegal activity conducted over their connection. From a GDPR standpoint, if the venue is collecting any data about users (even connection logs), they need a lawful basis — the captive portal consent mechanism provides this. From a commercial standpoint, the captive portal is the mechanism that converts anonymous footfall into a verified, marketable first-party data asset. Removing it eliminates the ability to build a loyalty database, run targeted marketing campaigns, or measure the return on the WiFi investment. The 'friction' argument is addressed by optimising the portal UX — single-click social login or SMS authentication takes under 10 seconds — not by removing the portal entirely.
Q3. During a penetration test of a café's network, the tester successfully captured another user's HTTP session cookie while connected to the Guest SSID. They also successfully reached a device on the 10.20.0.0/24 subnet (the staff network) from the guest network. Identify the two specific misconfigurations responsible for each finding.
💡 Dica:One finding relates to wireless controller configuration; the other relates to firewall ACL configuration.
Mostrar Abordagem Recomendada
Finding 1 (session cookie capture): Client Isolation is disabled on the Guest SSID. When enabled, this setting prevents wireless clients connected to the same AP from communicating directly at Layer 2, which would prevent the tester from capturing traffic from another guest device. Finding 2 (cross-VLAN access): The firewall ACLs are misconfigured. Either the inter-VLAN routing deny rule between the Guest VLAN and the Staff VLAN is absent, incorrectly ordered, or the VLANs are not correctly tagged at the switch level. The fix is to add an explicit deny rule on the firewall blocking all traffic from the Guest VLAN (e.g., 10.10.0.0/24) to the Staff VLAN (10.20.0.0/24), and to validate this with a post-change penetration test.



