¿Es seguro el WiFi de cafeterías y cafés?
Esta guía técnica autorizada examina los riesgos de seguridad reales del WiFi de cafeterías y cafés tanto para consumidores como para operadores de locales, cubriendo vectores de amenaza que incluyen ataques Evil Twin, rastreo de paquetes y exploits de cliente a cliente. Proporciona a los gerentes de TI y arquitectos de red un marco de implementación práctico y referenciado por estándares, desde la segmentación de VLAN y la migración a WPA3 hasta la implementación de un Captive Portal y análisis compatibles con GDPR. La plataforma de Guest WiFi y análisis de Purple se posiciona como una solución concreta en entornos de hostelería, comercio minorista y sector público.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: El Panorama de Amenazas
- Guía de Implementación: Arquitectura Segura para Locales
- Paso 1: Segmentación de Red mediante VLANs
- Paso 2: Habilitar la Aislación de Cliente
- Paso 3: Implementar un Captive Portal
- Paso 4: Implementar filtrado de contenido y gestión de ancho de banda
- Paso 5: Migrar a WPA3
- Mejores Prácticas y Estándares de la Industria
- Solución de Problemas y Mitigación de Riesgos
- ROI e Impacto Empresarial

Resumen Ejecutivo
Para los gerentes de TI y arquitectos de red que supervisan la conectividad en entornos minoristas y de hostelería, la pregunta "¿es seguro el WiFi de cafeterías?" ya no es una preocupación del consumidor, sino una responsabilidad empresarial crítica. Las redes públicas no seguras exponen a los invitados a ataques Man-in-the-Middle (MitM), puntos de acceso no autorizados y rastreo de paquetes, al mismo tiempo que ponen en riesgo la propia red operativa del local si no está segmentada correctamente.
Esta guía proporciona un desglose técnico exhaustivo de los riesgos inherentes a las implementaciones de WiFi en cafeterías. Más importante aún, describe las arquitecturas de nivel empresarial necesarias para mitigar estas amenazas. Al implementar una sólida segmentación de VLAN, cifrado WPA3 y una autenticación sofisticada mediante Captive Portal, como las que ofrecen las plataformas de Guest WiFi , los locales pueden transformar un servicio de alto riesgo en un activo seguro y generador de valor que cumple con los estándares PCI DSS y GDPR. Ya sea que opere una sola cafetería boutique o una cadena de 500 ubicaciones minoristas, los principios de esta guía se aplican a todas las escalas.
Análisis Técnico Detallado: El Panorama de Amenazas
La vulnerabilidad fundamental del WiFi tradicional de cafeterías radica en su naturaleza abierta. Cuando una red utiliza Autenticación de Sistema Abierto (sin contraseña) o una Clave Precompartida (PSK) escrita en una pizarra, las claves de cifrado son fácilmente accesibles o están completamente ausentes. Esto expone la red a varios vectores de ataque bien documentados que cualquier actor de amenazas competente puede explotar con hardware comercial.
Los ataques Evil Twin y los Puntos de Acceso Maliciosos representan la amenaza más peligrosa en el entorno de una cafetería. Los atacantes despliegan un Punto de Acceso (AP) malicioso que transmite el mismo SSID que la red legítima de la cafetería, por ejemplo, "CafeGuest_WiFi". Los sistemas operativos modernos están configurados para conectarse automáticamente a los SSID vistos anteriormente, y los dispositivos se conectarán a la señal más fuerte. Una vez que un usuario se conecta al AP del atacante, todo el tráfico se enruta a través de su hardware, lo que permite la intercepción completa de MitM.
El rastreo de paquetes y la escucha siguen siendo viables en redes no cifradas o débilmente cifradas. Herramientas como Wireshark están disponibles gratuitamente y no requieren conocimientos especializados para operar. En redes que utilizan WEP o incluso WPA2-Personal con una PSK conocida, los atacantes pueden descifrar el tráfico capturado. Si bien la adopción generalizada de HTTPS ha reducido la exposición del contenido de la carga útil, las cookies de sesión, los tokens de autenticación y las consultas DNS siguen siendo visibles.
Los ataques Man-in-the-Middle (MitM) van más allá de la simple escucha. Al controlar la puerta de enlace de la red, un atacante puede realizar SSL stripping —degradando las conexiones HTTPS a HTTP— para interceptar credenciales y datos sensibles en texto plano. También pueden inyectar contenido malicioso en respuestas no cifradas, redirigir a los usuarios a páginas de phishing o manipular las respuestas DNS.
Los ataques de cliente a cliente se habilitan cuando la aislación de Capa 2 está ausente. Si la aislación de cliente no está habilitada en el controlador inalámbrico, los dispositivos conectados al mismo AP comparten el mismo dominio de difusión. Un dispositivo comprometido puede escanear puertos abiertos en las máquinas de otros invitados, explotar vulnerabilidades locales o intentar propagar malware lateralmente a través de la red.

Guía de Implementación: Arquitectura Segura para Locales
Para proteger tanto al consumidor como al negocio, los equipos de TI deben implementar una arquitectura de seguridad por capas. Una red plana donde los sistemas de punto de venta (POS), los dispositivos del personal y las laptops de los invitados comparten la misma subred no es meramente un riesgo de seguridad, es un fallo de cumplimiento de PCI DSS con importantes consecuencias financieras.
Paso 1: Segmentación de Red mediante VLANs
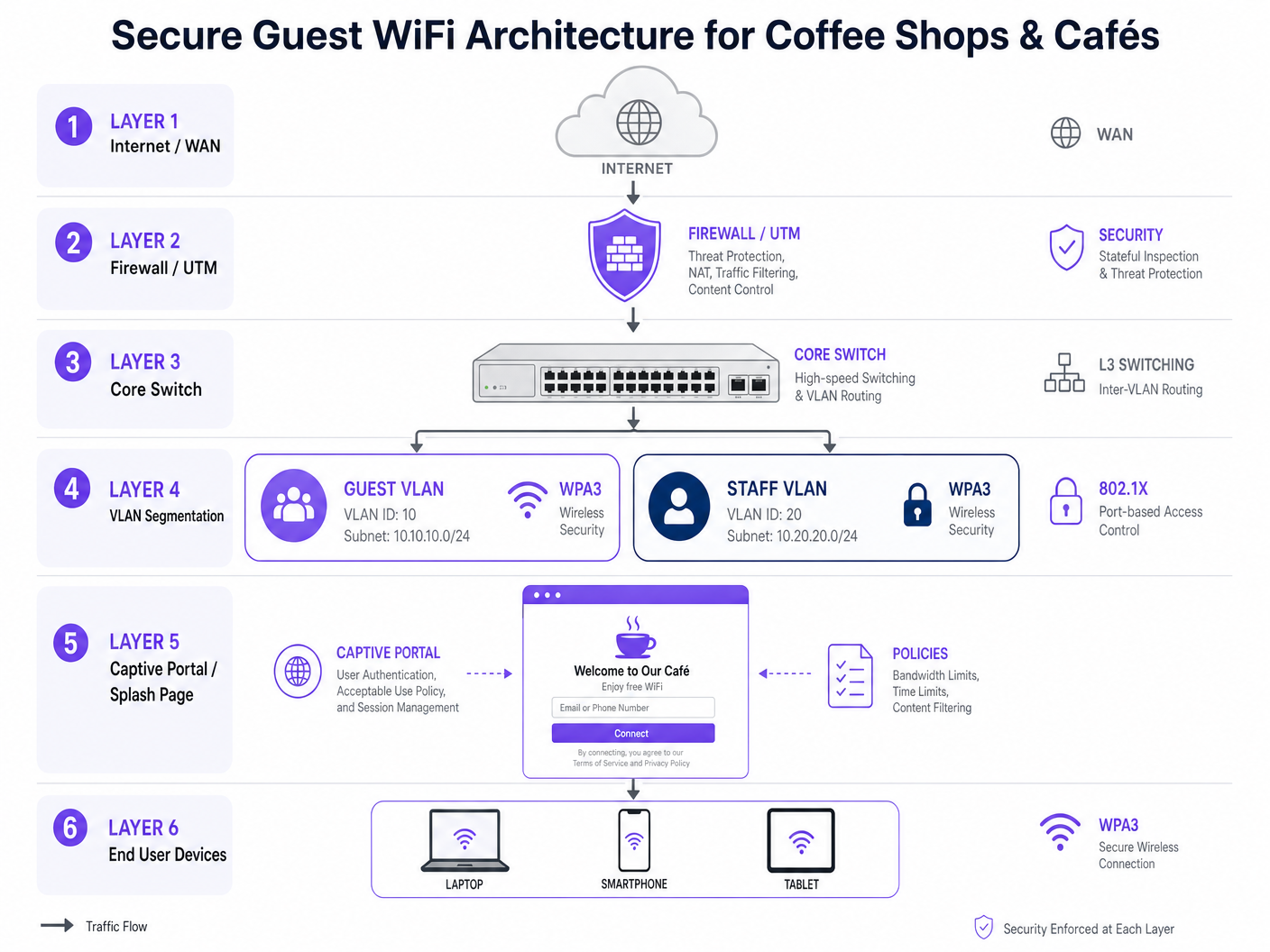
El paso fundamental es una segmentación estricta de Capa 2. El tráfico de invitados debe separarse lógicamente del tráfico corporativo y operativo a nivel de switch y controlador.
| VLAN | Propósito | Política de Acceso |
|---|---|---|
| VLAN 10 | Guest WiFi | Solo Internet. Denegar todo el enrutamiento a subredes internas. |
| VLAN 20 | Personal / Corporativo | Asegurado mediante autenticación 802.1X (RADIUS). Acceso interno completo. |
| VLAN 30 | IoT / Operaciones (POS, CCTV) | ACLs estrictas. Salida solo a la pasarela de pago. |
| VLAN 99 | Gestión de Red | Restringido solo a dispositivos de administración de red. |
Las reglas del firewall deben denegar explícitamente el enrutamiento entre VLAN desde la VLAN 10 a las VLAN 20 y 30. Esta es la configuración más importante para evitar que un compromiso del lado del invitado se extienda al entorno de pago u operativo.
Paso 2: Habilitar la Aislación de Cliente
Habilite la Aislación de Cliente (también conocida como Aislación de AP o Aislación de Capa 2) en el SSID de Invitados a nivel del controlador inalámbrico. Esto evita que los dispositivos conectados al mismo AP se comuniquen directamente entre sí, neutralizando los ataques peer-to-peer y el movimiento lateral a través de la subred de invitados.
Paso 3: Implementar un Captive Portal
Reemplace las redes abiertas con un Captive Portal sofisticado. Esto cumple múltiples propósitos simultáneamente. Desde un punto de vista legal, impone la aceptación de los Términos y Condiciones y una Política de Uso Aceptable (AUP), protegiendo al local de responsabilidad por actividades ilícitas en su conexión. Desde un punto de vista de seguridad, se aleja del acceso anónimo al autenticar a los usuarios a través de correo electrónico, SMS o inicio de sesión social. Desde un punto de vista comercial, se integra con plataformas como WiFi Analytics de Purple para recopilar datos demográficos y de comportamiento compatibles con GDPR — tiempo de permanencia, tasa de retorno, frecuencia de visitaencia, que se integra directamente con la automatización de marketing.
Paso 4: Implementar filtrado de contenido y gestión de ancho de banda
Implemente el filtrado de contenido basado en DNS para bloquear dominios maliciosos, sitios de phishing y contenido inapropiado. Esto protege la reputación del lugar y evita que la red se utilice para actividades ilegales. Aplique límites de velocidad por usuario (por ejemplo, 5 Mbps de bajada / 2 Mbps de subida) y tiempos de espera de sesión (por ejemplo, 2 horas) para evitar el abuso de la red y garantizar un acceso justo para todos los clientes.
Paso 5: Migrar a WPA3
La industria está migrando de WPA2-Personal a WPA3-SAE (Simultaneous Authentication of Equals) y, para implementaciones empresariales, a WPA3-Enterprise. WPA3 proporciona secreto hacia adelante, lo que significa que incluso si una clave de sesión se ve comprometida, las sesiones pasadas no pueden ser descifradas. Para los lugares que planifican hojas de ruta a largo plazo, Passpoint (Hotspot 2.0) y OpenRoaming proporcionan autenticación segura similar a la celular sin un Captive Portal.
Mejores Prácticas y Estándares de la Industria
Los siguientes estándares y marcos deben regir cualquier implementación de WiFi empresarial en cafeterías o tiendas minoristas.
| Estándar | Relevancia | Requisito Clave |
|---|---|---|
| PCI DSS v4.0 | Protección de datos de tarjetas de pago | Aislamiento completo de la red entre los entornos de datos de invitados y titulares de tarjetas. |
| GDPR / UK GDPR | Datos personales recopilados a través del Captive Portal | Consentimiento explícito, minimización de datos, derecho al borrado. |
| IEEE 802.1X | Control de acceso a la red basado en puertos | Autenticación RADIUS para VLANs de personal y gestión. |
| WPA3 (IEEE 802.11ax) | Cifrado inalámbrico | Obligatorio para nuevas implementaciones; planificar la migración para hardware heredado. |
| NIST SP 800-153 | Directrices para la seguridad de WLAN | Marco integral de políticas de seguridad inalámbrica. |
Para orientación específica del sector, Purple ha publicado recursos de implementación dedicados para entornos de Retail , Hospitality , Healthcare y Transport . La lectura técnica relacionada incluye nuestra guía sobre WiFi en Hospitales: Una Guía para Redes Clínicas Seguras y la ¿Es seguro el WiFi del aeropuerto? Una guía de seguridad para viajeros , que cubre modelos de amenazas análogos en entornos públicos de alta densidad.
Solución de Problemas y Mitigación de Riesgos
Incluso con una arquitectura robusta implementada, las fallas operativas pueden introducir riesgos. Los siguientes son los modos de falla más comunes encontrados en implementaciones reales.
El AP Malicioso Oculto. El personal o los proveedores externos a veces conectan routers de consumo no autorizados a los puertos de pared para extender la cobertura. Estos APs maliciosos eluden completamente el firewall corporativo y el Captive Portal, creando una brecha de seguridad significativa. La mitigación requiere habilitar la detección de APs maliciosos en el controlador inalámbrico e implementar la Seguridad de Puertos (802.1X o limitación de MAC) en todos los puertos físicos del switch para evitar que dispositivos no autorizados obtengan acceso a la red.
Secuestro de DNS en el Captive Portal. Si el Captive Portal no está asegurado con un certificado SSL válido (HTTPS), los atacantes pueden falsificar la página del portal para recopilar credenciales de invitados. Asegúrese de que todas las redirecciones del Captive Portal utilicen HTTPS con certificados válidos y de renovación automática. Las plataformas empresariales como Purple manejan esto por defecto.
Vulnerabilidades de Firmware. La vulnerabilidad KRACK (Key Reinstallation Attack) demostró que incluso WPA2 tiene debilidades explotables a nivel de protocolo. Mantenga un estricto programa trimestral de parches para todos los APs, switches y firewalls, y automatice las actualizaciones de firmware donde el controlador lo admita.
ACLs Mal Configuradas. Un error común es crear las VLANs correctas pero no configurar las ACLs del firewall para denegar el enrutamiento entre VLANs. Siempre valide la segmentación después de la implementación utilizando una prueba de penetración o, como mínimo, un escaneo manual desde un dispositivo invitado que intente acceder a subredes internas.
ROI e Impacto Empresarial
Invertir en WiFi seguro para cafeterías no es simplemente un centro de costos, es un facilitador estratégico con retornos medibles en tres dimensiones.
Valor de Mitigación de Riesgos. Una sola brecha de PCI DSS resultante de una red de invitados comprometida que se conecta a un sistema POS puede resultar en multas de hasta £100,000 por mes bajo UK GDPR, además de sanciones del esquema de tarjetas y el costo de la investigación forense. La inversión en infraestructura se justifica trivialmente frente a esta exposición.
ROI de Marketing. Al restringir el acceso detrás de un Captive Portal seguro y compatible, los lugares construyen un activo de datos de primera parte a escala. Cada conexión autenticada añade un perfil verificado — correo electrónico, datos demográficos, historial de visitas — a un CRM. Estos datos se integran directamente con la automatización de marketing, impulsando visitas repetidas y un aumento medible de la lealtad. La plataforma Guest WiFi de Purple está diseñada específicamente para este caso de uso, con integraciones a las principales plataformas de automatización de marketing y CRM.
Inteligencia Operacional. La integración de WiFi Analytics proporciona métricas de espacio físico que rivalizan con las analíticas de comercio electrónico en su granularidad. Los datos de afluencia por hora, tiempo de permanencia por zona, tasa de visitantes recurrentes y capacidad máxima permiten a los directores de operaciones tomar decisiones basadas en datos sobre la dotación de personal, el diseño y la programación de promociones. Para los lugares que exploran servicios de ubicación más avanzados, nuestra Guía de Sistema de Posicionamiento Interior: UWB, BLE y WiFi cubre el siguiente nivel de analíticas espaciales.
El caso de negocio es claro: una infraestructura WiFi segura, implementada correctamente con una plataforma gestionada, se amortiza a sí misma a través de la evitación de riesgos, la eficiencia de marketing y la optimización operativa.
Términos clave y definiciones
Evil Twin Attack
A rogue wireless access point that masquerades as a legitimate Wi-Fi network by broadcasting the same SSID, used to intercept traffic, steal credentials, or perform Man-in-the-Middle attacks.
Common in high-density public environments like cafés and airports. Mitigated by deploying Rogue AP detection on enterprise wireless controllers and educating users to verify the network via a captive portal URL.
Client Isolation (Layer 2 Isolation)
A wireless network security feature configured at the AP or controller level that prevents devices connected to the same access point from communicating directly with each other at the data link layer.
Essential for all public WiFi deployments. Prevents peer-to-peer attacks, port scanning, and malware propagation among guests. Must be explicitly enabled — it is not active by default on most platforms.
VLAN (Virtual Local Area Network)
A logical grouping of network devices that behave as if they are on a single isolated LAN, enforced at the switch level via IEEE 802.1Q tagging, regardless of physical location.
The primary mechanism for separating guest WiFi traffic from corporate, POS, and management traffic. Critical for PCI DSS compliance and for containing the blast radius of a security incident.
Captive Portal
A web-based authentication gateway that intercepts HTTP/HTTPS traffic from unauthenticated users and redirects them to a login or registration page before granting network access.
Serves as the legal, security, and commercial interface between the venue and the guest. Used to enforce Acceptable Use Policies, collect GDPR-compliant first-party data, and integrate with marketing platforms.
Packet Sniffing
The capture and inspection of data packets traversing a network, typically using tools such as Wireshark or tcpdump.
On unencrypted or weakly encrypted networks, attackers can extract session cookies, authentication tokens, and plain-text credentials from captured traffic. Mitigated by enforcing WPA3 encryption and HTTPS-only policies.
WPA3 (Wi-Fi Protected Access 3)
The current Wi-Fi security certification standard, introducing Simultaneous Authentication of Equals (SAE) to replace the vulnerable PSK handshake, providing forward secrecy and resistance to offline dictionary attacks.
The mandatory target for all new wireless deployments. Venues still running WPA2-Personal with a shared PSK should treat migration to WPA3 as a priority infrastructure project.
OpenRoaming / Passpoint (Hotspot 2.0)
A Wi-Fi Alliance standard (IEEE 802.11u) that enables devices to automatically discover and securely authenticate to trusted Wi-Fi networks using a pre-provisioned credential or identity provider profile, without manual intervention.
Represents the next generation of public WiFi security, providing cellular-like roaming and enterprise-grade encryption over public airwaves. Relevant for venues planning 3–5 year network roadmaps.
Rogue AP
An unauthorised wireless access point connected to a corporate network without the explicit authorisation of the network administrator.
Most commonly installed by well-meaning staff attempting to fix coverage dead zones. Bypasses corporate security policies, captive portals, and VLANs. Detected via wireless intrusion detection systems (WIDS) built into enterprise controllers.
SSL Stripping
A Man-in-the-Middle attack technique that downgrades an HTTPS connection to HTTP by intercepting the initial redirect, allowing the attacker to read and modify traffic in plain text.
Viable on networks where the attacker controls the gateway. Mitigated by HSTS (HTTP Strict Transport Security) headers on websites and by ensuring the captive portal itself uses HTTPS.
Casos de éxito
A national coffee shop chain with 500 locations is upgrading its network. They currently use an open SSID with a shared password written on the counter. They have recently introduced mobile ordering with a POS integration, and their compliance team has flagged a PCI DSS gap. They also want to start collecting customer data for a new loyalty programme. How should they architect the network to address all three requirements simultaneously?
Phase 1 — Network Segmentation: Deploy enterprise-grade APs capable of multi-SSID broadcasting and VLAN tagging across all 500 locations via a centralised cloud controller. Create three VLANs: Guest (VLAN 10, internet-only), POS/Mobile Order (VLAN 20, isolated to payment gateway egress only), and Management (VLAN 99, admin-only). Configure the firewall at each site with explicit deny rules blocking all inter-VLAN routing from VLAN 10 to VLAN 20. Phase 2 — Guest Security: Enable Client Isolation on the Guest SSID. Retire the shared PSK and implement a captive portal (Purple) requiring email or loyalty app authentication, paired with an Acceptable Use Policy. Phase 3 — Compliance and Analytics: Configure the captive portal to collect GDPR-compliant consent at the point of authentication. Integrate the Purple platform with the chain's CRM and marketing automation tools to begin building the first-party data asset for the loyalty programme.
A boutique hotel café is experiencing poor guest WiFi performance. Guests are complaining they cannot stream video or join video calls. The IT manager discovers that a small number of users are consuming the entire 200 Mbps WAN link with large downloads. Simultaneously, the hotel's security team has flagged that guest devices appear to be scanning other devices on the same subnet. How should the IT manager resolve both issues?
Performance Fix: Implement Per-User Bandwidth Limiting at the wireless controller level, capping each authenticated device at 10 Mbps down / 5 Mbps up. Implement Application Layer (Layer 7) Traffic Shaping to deprioritise P2P file sharing and large software update traffic during peak hours (07:00–22:00). Enforce a Session Timeout of 4 hours on the captive portal to clear inactive sessions and free up DHCP leases. Security Fix: Enable Client Isolation (AP Isolation) on the Guest SSID immediately. This is the root cause of the subnet scanning issue — without it, guest devices share a broadcast domain and can communicate directly. Validate the fix by running a post-change scan from a guest device to confirm it cannot reach other guest devices on the subnet.
Análisis de escenarios
Q1. You are auditing a newly acquired coffee shop's network. You find that the guest WiFi and the back-office PC used for inventory management and payroll processing are on the same 192.168.1.0/24 subnet with no firewall between them. What is the immediate technical recommendation, and what compliance framework does this violation fall under?
💡 Sugerencia:Consider the implications for lateral movement, data exfiltration, and the specific compliance standard that governs the separation of cardholder data environments.
Mostrar enfoque recomendado
Immediate action: Implement VLAN segmentation. Create a dedicated VLAN for guest traffic (VLAN 10) and a separate VLAN for corporate back-office devices (VLAN 20). Configure the firewall with explicit ACL rules blocking all inter-VLAN routing from VLAN 10 to VLAN 20. Enable client isolation on the guest SSID. Compliance context: If the back-office PC is in scope for payment card processing, this is a PCI DSS violation — specifically Requirement 1.3, which mandates that systems in the cardholder data environment are isolated from untrusted networks. Even if the PC is not directly processing payments, the flat network creates an unacceptable risk of lateral movement from a compromised guest device.
Q2. A venue operations director wants to remove the captive portal from their café network because 'it adds friction' and they want an open network with no authentication. How do you advise them from both a security and a commercial perspective?
💡 Sugerencia:Address the legal liability, the GDPR implications, and the lost commercial value of the first-party data asset.
Mostrar enfoque recomendado
Advise strongly against this. From a legal standpoint, removing the captive portal means no Acceptable Use Policy is enforced, leaving the venue potentially liable for illegal activity conducted over their connection. From a GDPR standpoint, if the venue is collecting any data about users (even connection logs), they need a lawful basis — the captive portal consent mechanism provides this. From a commercial standpoint, the captive portal is the mechanism that converts anonymous footfall into a verified, marketable first-party data asset. Removing it eliminates the ability to build a loyalty database, run targeted marketing campaigns, or measure the return on the WiFi investment. The 'friction' argument is addressed by optimising the portal UX — single-click social login or SMS authentication takes under 10 seconds — not by removing the portal entirely.
Q3. During a penetration test of a café's network, the tester successfully captured another user's HTTP session cookie while connected to the Guest SSID. They also successfully reached a device on the 10.20.0.0/24 subnet (the staff network) from the guest network. Identify the two specific misconfigurations responsible for each finding.
💡 Sugerencia:One finding relates to wireless controller configuration; the other relates to firewall ACL configuration.
Mostrar enfoque recomendado
Finding 1 (session cookie capture): Client Isolation is disabled on the Guest SSID. When enabled, this setting prevents wireless clients connected to the same AP from communicating directly at Layer 2, which would prevent the tester from capturing traffic from another guest device. Finding 2 (cross-VLAN access): The firewall ACLs are misconfigured. Either the inter-VLAN routing deny rule between the Guest VLAN and the Staff VLAN is absent, incorrectly ordered, or the VLANs are not correctly tagged at the switch level. The fix is to add an explicit deny rule on the firewall blocking all traffic from the Guest VLAN (e.g., 10.10.0.0/24) to the Staff VLAN (10.20.0.0/24), and to validate this with a post-change penetration test.



