Is Hospital WiFi Safe? What Patients and Visitors Should Know
This comprehensive technical reference guide examines the security architecture of hospital guest WiFi networks. It provides IT managers and venue operators with actionable implementation strategies, focusing on network segmentation, encryption standards, and compliance frameworks to ensure patient data remains protected without compromising clinical operations.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Network Architecture and Segmentation
- Clinical vs. Guest Isolation
- Encryption Standards
- Implementation Guide: Securing the Patient Experience
- The Role of the Captive Portal
- Client Isolation and Rogue AP Mitigation
- Best Practices for Healthcare IT Teams
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- References
Executive Summary
For IT managers and CTOs in the healthcare sector, the question "is hospital wifi safe?" is not merely a matter of patient convenience; it is a critical compliance and risk mitigation imperative. Providing free WiFi in hospitals for patients and visitors is now a standard expectation, but it introduces significant attack surfaces if not architected correctly. This guide details the technical controls required to secure patient WiFi environments, ensuring that guest access remains strictly isolated from clinical networks. We will explore the deployment of IEEE 802.1X, WPA3, and secure captive portals, demonstrating how enterprise platforms like Purple's Guest WiFi mitigate risk while delivering a seamless user experience. By implementing these standards, healthcare providers can confidently answer yes when asked if it is safe to use hospital WiFi.

Technical Deep-Dive: Network Architecture and Segmentation
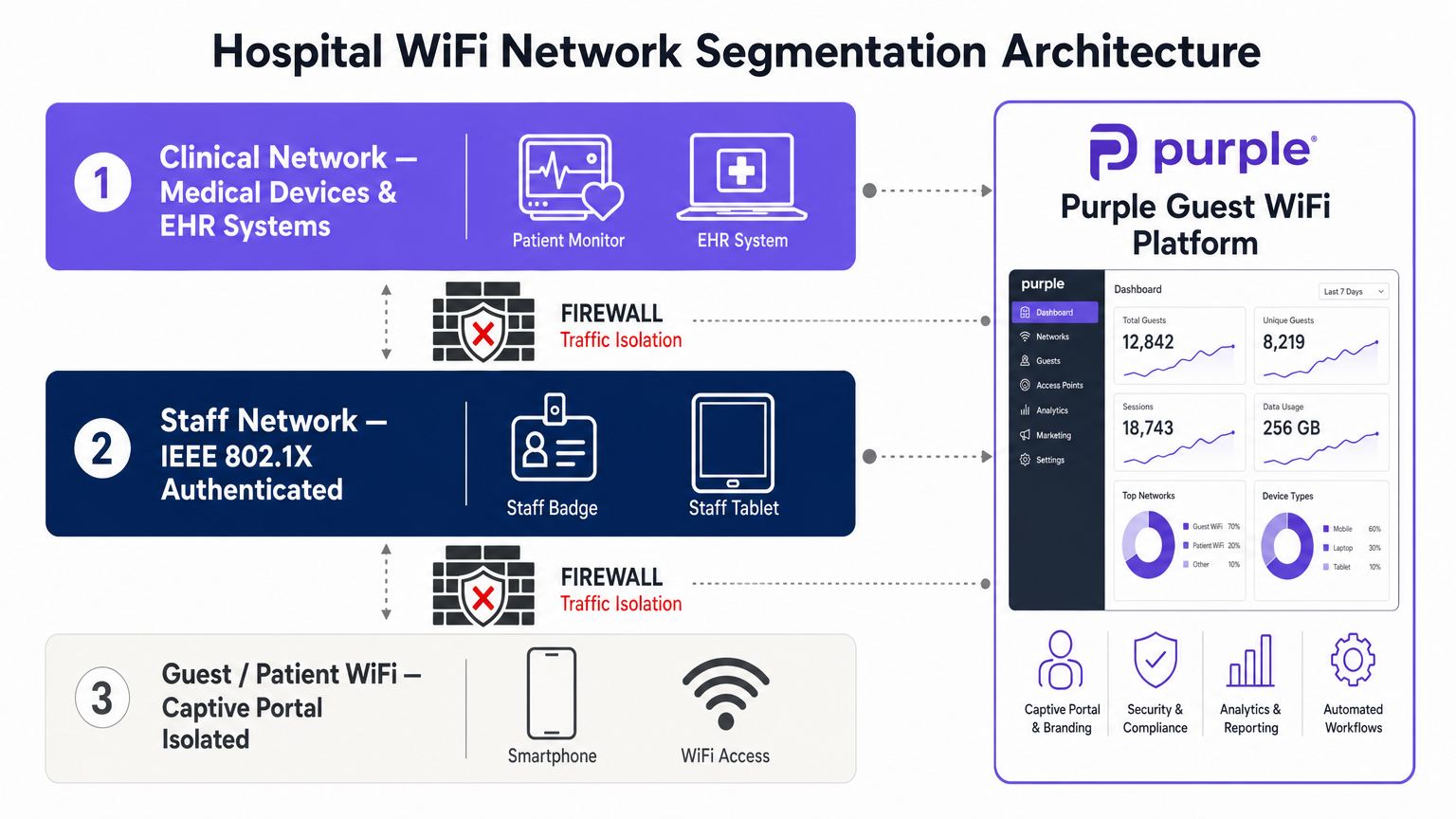
The foundation of secure hospital WiFi is rigorous network segmentation. A flat network architecture is a catastrophic vulnerability in a healthcare setting.
Clinical vs. Guest Isolation
Guest traffic must be logically separated from clinical systems (EHR, connected medical devices, staff communications) using distinct Virtual Local Area Networks (VLANs). The patient WiFi network should be configured to route traffic directly to the internet gateway, bypassing internal routing tables entirely. Firewalls must enforce strict Access Control Lists (ACLs) that deny any ingress traffic from the guest VLAN to the clinical VLANs.
Encryption Standards
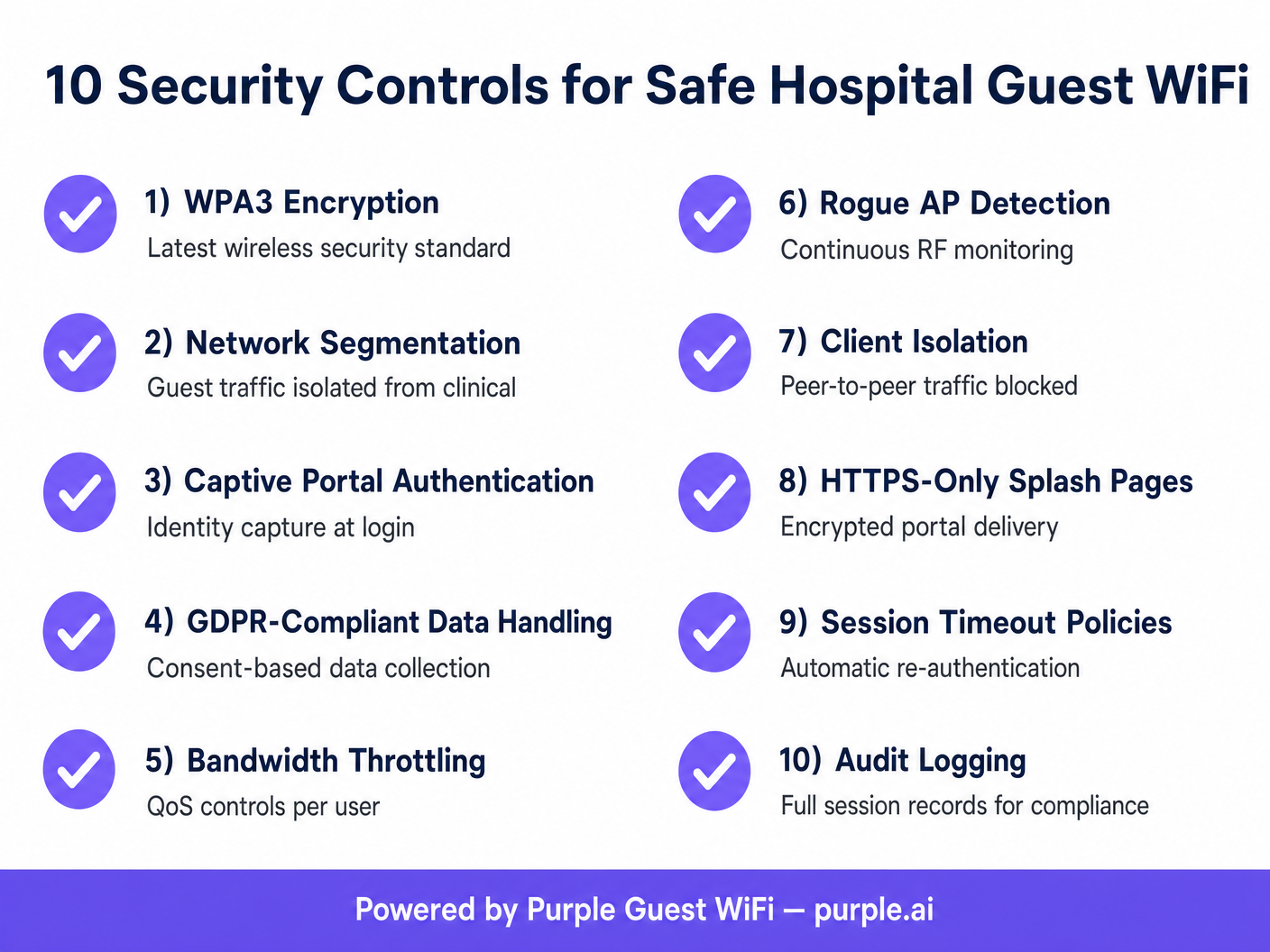
Historically, open guest networks provided no over-the-air encryption. The adoption of WPA3 (Wi-Fi Protected Access 3) and Opportunistic Wireless Encryption (OWE) has transformed this landscape. WPA3 provides individualized data encryption even on networks that do not require a pre-shared key, significantly reducing the risk of passive eavesdropping. Furthermore, the integration of Passpoint (Hotspot 2.0) allows for seamless, encrypted roaming. Purple acts as a free identity provider for services like OpenRoaming under the Connect license, enabling secure, profile-based authentication that eliminates the friction of traditional passwords while maintaining enterprise-grade security.
Implementation Guide: Securing the Patient Experience
Deploying secure WiFi in hospitals requires a systematic approach to identity management and threat mitigation.
The Role of the Captive Portal
The captive portal is the primary enforcement point for guest network policies. It is not just a branding exercise; it is a compliance mechanism. When deploying a captive portal via a WiFi Analytics platform, IT teams must ensure it enforces HTTPS-only delivery to prevent credential interception. The portal must also capture user consent in accordance with GDPR or local privacy regulations before granting access.
Client Isolation and Rogue AP Mitigation
To protect users from lateral attacks, Client Isolation (also known as AP Isolation) must be enabled on the guest SSID. This prevents devices connected to the same access point from communicating directly with each other, neutralizing peer-to-peer threats. Additionally, continuous RF monitoring is required to detect and contain rogue access points. If a malicious actor attempts an "evil twin" attack by spoofing the hospital's SSID, the wireless intrusion prevention system (WIPS) must automatically de-authenticate clients attempting to connect to the rogue AP.
Best Practices for Healthcare IT Teams
- Implement DNS Filtering: Block access to known malicious domains, phishing sites, and inappropriate content at the DNS level. This protects the network from malware and limits liability.
- Enforce Quality of Service (QoS): Apply bandwidth throttling per user to prevent network saturation. A single user streaming high-definition video should not degrade the performance of the entire patient WiFi network.
- Session Management: Configure aggressive session timeout policies. Require users to re-authenticate daily to clear stale sessions and maintain an accurate audit log of active devices.
- Regular Auditing: Conduct quarterly wireless penetration testing and review firewall rules to ensure VLAN isolation remains intact.
For more insights on secure deployments in complex environments, review our comprehensive WiFi in Hospitals: A Guide to Secure Clinical Networks .
Troubleshooting & Risk Mitigation
Common failure modes in hospital guest networks often stem from misconfigured VLANs or inadequate portal security.
- Failure Mode: DHCP Exhaustion: Guest networks often experience high churn. If DHCP lease times are too long, the IP pool will exhaust, preventing new connections. Mitigation: Set DHCP lease times for the guest subnet to 1-2 hours.
- Failure Mode: Captive Portal Bypasses: Advanced users may attempt to bypass the captive portal using DNS tunneling. Mitigation: Block all outbound DNS requests from the guest VLAN except those directed to the approved, filtered DNS servers.
Similar challenges are often seen in other high-footfall environments; for a comparative view, see our guide on Is Café and Coffee Shop WiFi Safe? .
ROI & Business Impact
The return on investment for a secure hospital WiFi deployment is measured in risk mitigation and operational efficiency. A breach originating from an unsecured guest network can result in millions of dollars in fines, reputational damage, and disrupted clinical operations. By implementing a robust, segmented architecture, hospitals reduce helpdesk tickets related to connectivity issues and improve patient satisfaction scores. The data captured through secure, compliant captive portals also provides valuable analytics on visitor flow and dwell times, aiding in operational planning and resource allocation.
References
[1] IEEE Standards Association. "IEEE 802.1X-2020 - IEEE Standard for Local and Metropolitan Area Networks--Port-Based Network Access Control." https://standards.ieee.org/ieee/802.1X/7342/ [2] Wi-Fi Alliance. "Security: WPA3." https://www.wi-fi.org/discover-wi-fi/security
Key Terms & Definitions
Network Segmentation
The practice of splitting a computer network into subnetworks to improve performance and security.
Critical in hospitals to ensure patient WiFi traffic cannot access clinical EHR systems or medical devices.
Client Isolation
A wireless network security feature that prevents devices connected to the same access point from communicating with each other.
Used on guest networks to prevent lateral attacks and peer-to-peer malware spread.
WPA3
The latest generation of Wi-Fi security, providing robust authentication and individualized data encryption.
Replaces WPA2 to offer better protection against brute-force dictionary attacks on wireless networks.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Used by IT teams to enforce terms of service, capture identity data, and ensure regulatory compliance.
Rogue Access Point
A wireless access point that has been installed on a secure network without explicit authorization from a local network administrator.
A major threat vector; IT teams use WIPS to detect and contain these devices to prevent data interception.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
The fundamental technology used to isolate guest traffic from the clinical network.
OpenRoaming
A roaming federation service that enables an automatic and secure Wi-Fi experience.
Allows patients to connect securely without passwords, using profile-based authentication.
DNS Filtering
The process of using the Domain Name System to block malicious websites and filter out harmful or inappropriate content.
Implemented on guest networks to protect users from malware and the hospital from liability.
Case Studies
A 400-bed regional hospital needs to deploy patient WiFi across all wards and waiting areas. The IT director is concerned about patients inadvertently downloading malware that could spread to other devices on the guest network. How should the network be configured to mitigate this risk?
- Deploy a dedicated Guest SSID mapped to an isolated VLAN. 2. Enable Client Isolation (AP Isolation) on the wireless LAN controller for the Guest SSID to block peer-to-peer communication. 3. Implement DNS-level content filtering to block known malware and phishing domains. 4. Configure the firewall to only allow HTTP (80) and HTTPS (443) traffic outbound from the guest VLAN, blocking all other ports.
During a routine audit, the network team discovers that visitors in the cafeteria are experiencing extremely slow WiFi speeds. Investigation reveals a small number of users are streaming 4K video, saturating the access points. What is the technical solution?
Implement Quality of Service (QoS) and bandwidth throttling on the Guest SSID. Configure a per-user bandwidth limit (e.g., 5 Mbps down / 2 Mbps up) within the wireless controller or via the Purple Guest WiFi platform's policy engine.
Scenario Analysis
Q1. A hospital IT director is planning a network upgrade and wants to implement OpenRoaming for patient WiFi to improve security and user experience. What is the primary benefit of this approach compared to a traditional open network with a captive portal?
💡 Hint:Consider how the over-the-air connection is secured before the user even reaches the portal.
Show Recommended Approach
OpenRoaming provides automatic, profile-based authentication and encrypts the over-the-air connection (typically via Passpoint/802.1X), whereas a traditional open network transmits data in plaintext until the user authenticates at the portal (and even then, only HTTPS traffic is secure). This eliminates the risk of passive eavesdropping on the wireless link.
Q2. During a penetration test, the security team successfully accesses the hospital's IP-based security cameras from the patient WiFi network. What architectural failure does this indicate, and how should it be resolved?
💡 Hint:Think about how different types of traffic should be separated logically.
Show Recommended Approach
This indicates a failure in network segmentation. The patient WiFi and the security cameras are likely on the same VLAN, or the firewall ACLs between their respective VLANs are misconfigured. The resolution is to place the guest WiFi on a dedicated VLAN and implement strict firewall rules that deny all traffic from the guest VLAN to any internal IP ranges, routing guest traffic exclusively to the internet.
Q3. A venue operations director notices that the captive portal is generating warnings in modern web browsers stating the connection is 'Not Secure'. Why is this happening, and what is the technical remediation?
💡 Hint:Consider the protocol used to serve the captive portal page.
Show Recommended Approach
The captive portal is likely being served over unencrypted HTTP rather than HTTPS. Modern browsers flag HTTP login pages as insecure. The remediation is to install a valid SSL/TLS certificate on the wireless controller or the external captive portal server (like Purple's platform) and force all portal traffic over HTTPS (port 443).



