¿Es seguro el WiFi de los hospitales? Lo que los pacientes y visitantes deben saber
Esta guía técnica de referencia exhaustiva examina la arquitectura de seguridad de las redes WiFi para invitados en hospitales. Proporciona a los gerentes de TI y operadores de recintos estrategias de implementación prácticas, centrándose en la segmentación de la red, los estándares de cifrado y los marcos de cumplimiento para garantizar que los datos de los pacientes permanezcan protegidos sin comprometer las operaciones clínicas.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura de Red y Segmentación
- Aislamiento Clínico vs. Invitados
- Estándares de Cifrado
- Guía de Implementación: Asegurando la Experiencia del Paciente
- El Rol del Captive Portal
- Aislamiento de Clientes y Mitigación de APs Maliciosos
- Mejores Prácticas para Equipos de TI en el Sector Salud
- Resolución de Problemas y Mitigación de Riesgos
- ROI e Impacto Comercial
- Referencias
Resumen Ejecutivo
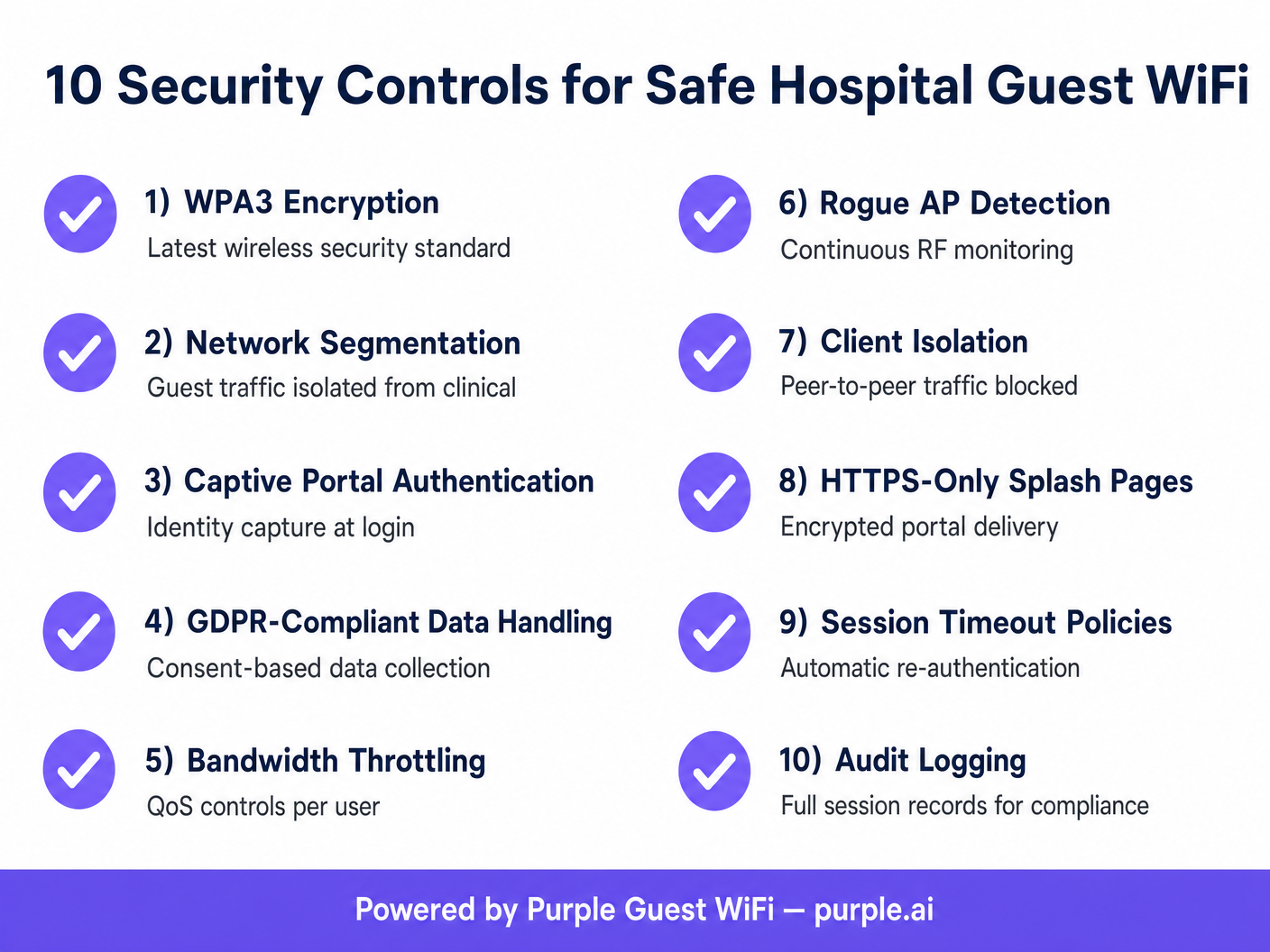
Para los gerentes de TI y CTOs en el sector de la salud, la pregunta "¿es seguro el WiFi de los hospitales?" no es meramente una cuestión de conveniencia para el paciente; es un imperativo crítico de cumplimiento y mitigación de riesgos. Proporcionar WiFi gratuito en hospitales para pacientes y visitantes es ahora una expectativa estándar, pero introduce superficies de ataque significativas si no se diseña correctamente. Esta guía detalla los controles técnicos necesarios para asegurar los entornos WiFi de los pacientes, garantizando que el acceso de invitados permanezca estrictamente aislado de las redes clínicas. Exploraremos la implementación de IEEE 802.1X, WPA3 y Captive Portals seguros, demostrando cómo las plataformas empresariales como Guest WiFi de Purple mitigan el riesgo al tiempo que ofrecen una experiencia de usuario fluida. Al implementar estos estándares, los proveedores de atención médica pueden responder con confianza que sí cuando se les pregunte si es seguro usar el WiFi del hospital.

Análisis Técnico Detallado: Arquitectura de Red y Segmentación
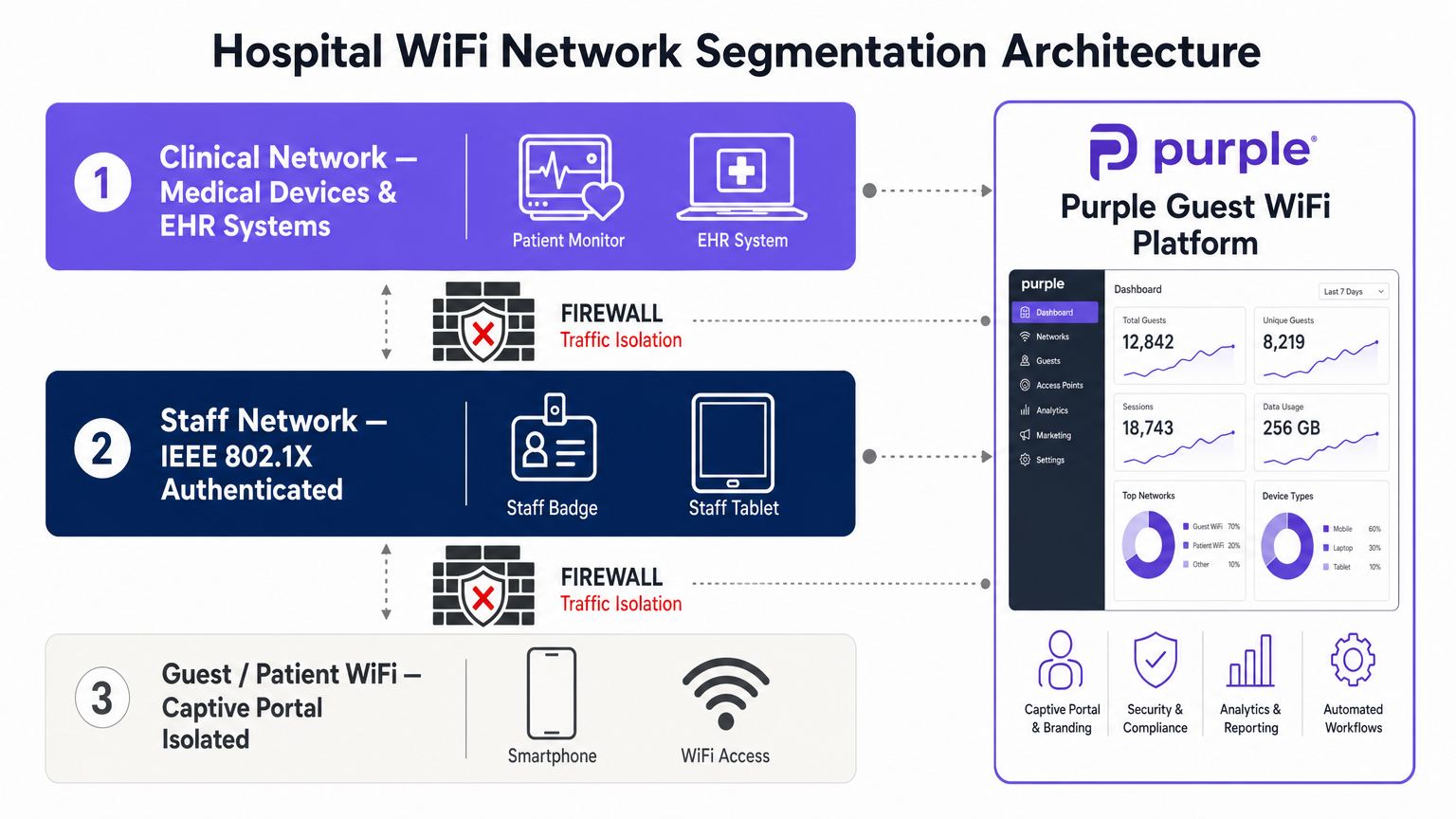
La base de un WiFi hospitalario seguro es una segmentación de red rigurosa. Una arquitectura de red plana es una vulnerabilidad catastrófica en un entorno de atención médica.
Aislamiento Clínico vs. Invitados
El tráfico de invitados debe separarse lógicamente de los sistemas clínicos (EHR, dispositivos médicos conectados, comunicaciones del personal) utilizando Redes de Área Local Virtuales (VLANs) distintas. La red WiFi para pacientes debe configurarse para enrutar el tráfico directamente a la puerta de enlace de internet, omitiendo por completo las tablas de enrutamiento internas. Los firewalls deben aplicar Listas de Control de Acceso (ACLs) estrictas que denieguen cualquier tráfico de entrada desde la VLAN de invitados a las VLANs clínicas.
Estándares de Cifrado
Históricamente, las redes de invitados abiertas no proporcionaban cifrado por aire. La adopción de WPA3 (Wi-Fi Protected Access 3) y Opportunistic Wireless Encryption (OWE) ha transformado este panorama. WPA3 proporciona cifrado de datos individualizado incluso en redes que no requieren una clave precompartida, reduciendo significativamente el riesgo de escucha pasiva. Además, la integración de Passpoint (Hotspot 2.0) permite un roaming fluido y cifrado. Purple actúa como un proveedor de identidad gratuito para servicios como OpenRoaming bajo la licencia Connect, lo que permite una autenticación segura basada en perfiles que elimina la fricción de las contraseñas tradicionales mientras mantiene una seguridad de nivel empresarial.
Guía de Implementación: Asegurando la Experiencia del Paciente
La implementación de WiFi seguro en hospitales requiere un enfoque sistemático para la gestión de identidades y la mitigación de amenazas.
El Rol del Captive Portal
El Captive Portal es el punto de aplicación principal para las políticas de la red de invitados. No es solo un ejercicio de marca; es un mecanismo de cumplimiento. Al implementar un Captive Portal a través de una plataforma de WiFi Analytics , los equipos de TI deben asegurarse de que aplique la entrega solo por HTTPS para evitar la interceptación de credenciales. El portal también debe capturar el consentimiento del usuario de acuerdo con GDPR o las regulaciones de privacidad locales antes de otorgar acceso.
Aislamiento de Clientes y Mitigación de APs Maliciosos
Para proteger a los usuarios de ataques laterales, el Aislamiento de Clientes (también conocido como Aislamiento de AP) debe estar habilitado en el SSID de invitados. Esto evita que los dispositivos conectados al mismo punto de acceso se comuniquen directamente entre sí, neutralizando las amenazas peer-to-peer. Además, se requiere una monitorización continua de RF para detectar y contener puntos de acceso maliciosos. Si un actor malicioso intenta un ataque de "gemelo malvado" suplantando el SSID del hospital, el sistema de prevención de intrusiones inalámbricas (WIPS) debe desautenticar automáticamente a los clientes que intenten conectarse al AP malicioso.
Mejores Prácticas para Equipos de TI en el Sector Salud
- Implementar Filtrado DNS: Bloquee el acceso a dominios maliciosos conocidos, sitios de phishing y contenido inapropiado a nivel de DNS. Esto protege la red del malware y limita la responsabilidad.
- Aplicar Calidad de Servicio (QoS): Aplique la limitación de ancho de banda por usuario para evitar la saturación de la red. Un solo usuario transmitiendo video de alta definición no debe degradar el rendimiento de toda la red WiFi de pacientes.
- Gestión de Sesiones: Configure políticas agresivas de tiempo de espera de sesión. Requerir a los usuarios que se vuelvan a autenticar diariamente para borrar sesiones inactivas y mantener un registro de auditoría preciso de los dispositivos activos.
- Auditorías Regulares: Realice pruebas de penetración inalámbricas trimestrales y revise las reglas del firewall para asegurar que el aislamiento de VLAN permanezca intacto.
Para obtener más información sobre implementaciones seguras en entornos complejos, revise nuestra guía completa WiFi en Hospitales: Una Guía para Redes Clínicas Seguras .
Resolución de Problemas y Mitigación de Riesgos
Los modos de falla comunes en las redes de invitados de hospitales a menudo provienen de VLANs mal configuradas o de una seguridad de portal inadecuada.
- Modo de Falla: Agotamiento de DHCP: Las redes de invitados a menudo experimentan una alta rotación. Si los tiempos de arrendamiento de DHCP son demasiado largos, el pool de IP se agotará, impidiendo nuevas conexiones. Mitigación: Establezca los tiempos de arrendamiento de DHCP para la subred de invitados en 1-2 horas.
- Modo de Falla: Elusión del Captive Portal: Los usuarios avanzados pueden intentar eludir el Captive Portal utilizando túneles DNS. Mitigación: Bloquee todas las solicitudes DNS salientes de la VLAN de invitados, excepto aquellas dirigidas a los servidores DNS aprobados y filtrados.
Desafíos similares se observan a menudo en otros entornos de alto tráfico; para una vista comparativa, consulte nuestra guía sobre ¿Es seguro el WiFi de cafeterías y cafés? .
ROI e Impacto Comercial
El retorno de la inversión para una implementación segura de WiFi hospitalarioEl rendimiento se mide en la mitigación de riesgos y la eficiencia operativa. Una brecha de seguridad originada en una red de invitados no segura puede resultar en millones de dólares en multas, daño a la reputación y operaciones clínicas interrumpidas. Al implementar una arquitectura robusta y segmentada, los hospitales reducen los tickets de soporte técnico relacionados con problemas de conectividad y mejoran los puntajes de satisfacción del paciente. Los datos capturados a través de Captive Portals seguros y conformes también proporcionan análisis valiosos sobre el flujo de visitantes y los tiempos de permanencia, lo que ayuda en la planificación operativa y la asignación de recursos.
Referencias
[1] IEEE Standards Association. "IEEE 802.1X-2020 - Estándar IEEE para Redes de Área Local y Metropolitana—Control de Acceso a la Red Basado en Puertos." https://standards.ieee.org/ieee/802.1X/7342/ [2] Wi-Fi Alliance. "Seguridad: WPA3." https://www.wi-fi.org/discover-wi-fi/security
Términos clave y definiciones
Network Segmentation
The practice of splitting a computer network into subnetworks to improve performance and security.
Critical in hospitals to ensure patient WiFi traffic cannot access clinical EHR systems or medical devices.
Client Isolation
A wireless network security feature that prevents devices connected to the same access point from communicating with each other.
Used on guest networks to prevent lateral attacks and peer-to-peer malware spread.
WPA3
The latest generation of Wi-Fi security, providing robust authentication and individualized data encryption.
Replaces WPA2 to offer better protection against brute-force dictionary attacks on wireless networks.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Used by IT teams to enforce terms of service, capture identity data, and ensure regulatory compliance.
Rogue Access Point
A wireless access point that has been installed on a secure network without explicit authorization from a local network administrator.
A major threat vector; IT teams use WIPS to detect and contain these devices to prevent data interception.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
The fundamental technology used to isolate guest traffic from the clinical network.
OpenRoaming
A roaming federation service that enables an automatic and secure Wi-Fi experience.
Allows patients to connect securely without passwords, using profile-based authentication.
DNS Filtering
The process of using the Domain Name System to block malicious websites and filter out harmful or inappropriate content.
Implemented on guest networks to protect users from malware and the hospital from liability.
Casos de éxito
A 400-bed regional hospital needs to deploy patient WiFi across all wards and waiting areas. The IT director is concerned about patients inadvertently downloading malware that could spread to other devices on the guest network. How should the network be configured to mitigate this risk?
- Deploy a dedicated Guest SSID mapped to an isolated VLAN. 2. Enable Client Isolation (AP Isolation) on the wireless LAN controller for the Guest SSID to block peer-to-peer communication. 3. Implement DNS-level content filtering to block known malware and phishing domains. 4. Configure the firewall to only allow HTTP (80) and HTTPS (443) traffic outbound from the guest VLAN, blocking all other ports.
During a routine audit, the network team discovers that visitors in the cafeteria are experiencing extremely slow WiFi speeds. Investigation reveals a small number of users are streaming 4K video, saturating the access points. What is the technical solution?
Implement Quality of Service (QoS) and bandwidth throttling on the Guest SSID. Configure a per-user bandwidth limit (e.g., 5 Mbps down / 2 Mbps up) within the wireless controller or via the Purple Guest WiFi platform's policy engine.
Análisis de escenarios
Q1. A hospital IT director is planning a network upgrade and wants to implement OpenRoaming for patient WiFi to improve security and user experience. What is the primary benefit of this approach compared to a traditional open network with a captive portal?
💡 Sugerencia:Consider how the over-the-air connection is secured before the user even reaches the portal.
Mostrar enfoque recomendado
OpenRoaming provides automatic, profile-based authentication and encrypts the over-the-air connection (typically via Passpoint/802.1X), whereas a traditional open network transmits data in plaintext until the user authenticates at the portal (and even then, only HTTPS traffic is secure). This eliminates the risk of passive eavesdropping on the wireless link.
Q2. During a penetration test, the security team successfully accesses the hospital's IP-based security cameras from the patient WiFi network. What architectural failure does this indicate, and how should it be resolved?
💡 Sugerencia:Think about how different types of traffic should be separated logically.
Mostrar enfoque recomendado
This indicates a failure in network segmentation. The patient WiFi and the security cameras are likely on the same VLAN, or the firewall ACLs between their respective VLANs are misconfigured. The resolution is to place the guest WiFi on a dedicated VLAN and implement strict firewall rules that deny all traffic from the guest VLAN to any internal IP ranges, routing guest traffic exclusively to the internet.
Q3. A venue operations director notices that the captive portal is generating warnings in modern web browsers stating the connection is 'Not Secure'. Why is this happening, and what is the technical remediation?
💡 Sugerencia:Consider the protocol used to serve the captive portal page.
Mostrar enfoque recomendado
The captive portal is likely being served over unencrypted HTTP rather than HTTPS. Modern browsers flag HTTP login pages as insecure. The remediation is to install a valid SSL/TLS certificate on the wireless controller or the external captive portal server (like Purple's platform) and force all portal traffic over HTTPS (port 443).



