O WiFi do Hospital é Seguro? O Que Pacientes e Visitantes Devem Saber
Este guia de referência técnica abrangente examina a arquitetura de segurança das redes WiFi de convidados em hospitais. Fornece a gestores de TI e operadores de espaços estratégias de implementação acionáveis, focando na segmentação de rede, padrões de encriptação e estruturas de conformidade para garantir que os dados dos pacientes permaneçam protegidos sem comprometer as operações clínicas.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: Arquitetura de Rede e Segmentação
- Isolamento Clínico vs. Convidados
- Padrões de Encriptação
- Guia de Implementação: Proteger a Experiência do Paciente
- O Papel do Captive Portal
- Isolamento de Clientes e Mitigação de APs Maliciosos
- Melhores Práticas para Equipas de TI na Saúde
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio
- Referências
Resumo Executivo
Para gestores de TI e CTOs no setor da saúde, a questão "o WiFi do hospital é seguro?" não é meramente uma questão de conveniência para o paciente; é um imperativo crítico de conformidade e mitigação de riscos. Fornecer WiFi gratuito em hospitais para pacientes e visitantes é agora uma expectativa padrão, mas introduz superfícies de ataque significativas se não for arquitetado corretamente. Este guia detalha os controlos técnicos necessários para proteger os ambientes de WiFi para pacientes, garantindo que o acesso de convidados permaneça estritamente isolado das redes clínicas. Exploraremos a implementação de IEEE 802.1X, WPA3 e Captive Portals seguros, demonstrando como plataformas empresariais como o Guest WiFi da Purple mitigam o risco ao mesmo tempo que proporcionam uma experiência de utilizador fluida. Ao implementar estes padrões, os prestadores de cuidados de saúde podem responder com confiança que sim quando questionados se é seguro usar o WiFi do hospital.

Análise Técnica Aprofundada: Arquitetura de Rede e Segmentação
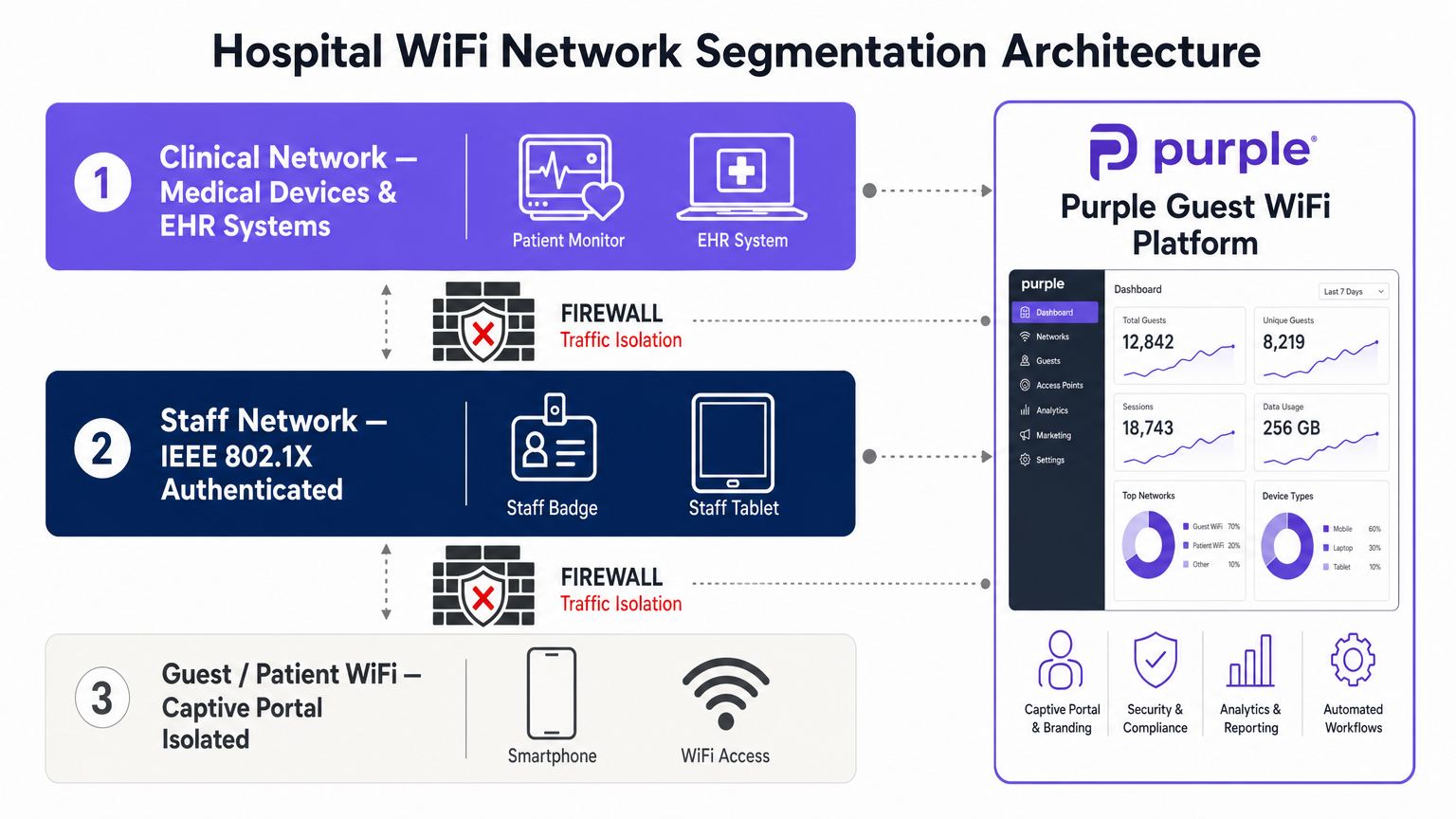
A base do WiFi seguro em hospitais é uma segmentação de rede rigorosa. Uma arquitetura de rede plana é uma vulnerabilidade catastrófica num ambiente de saúde.
Isolamento Clínico vs. Convidados
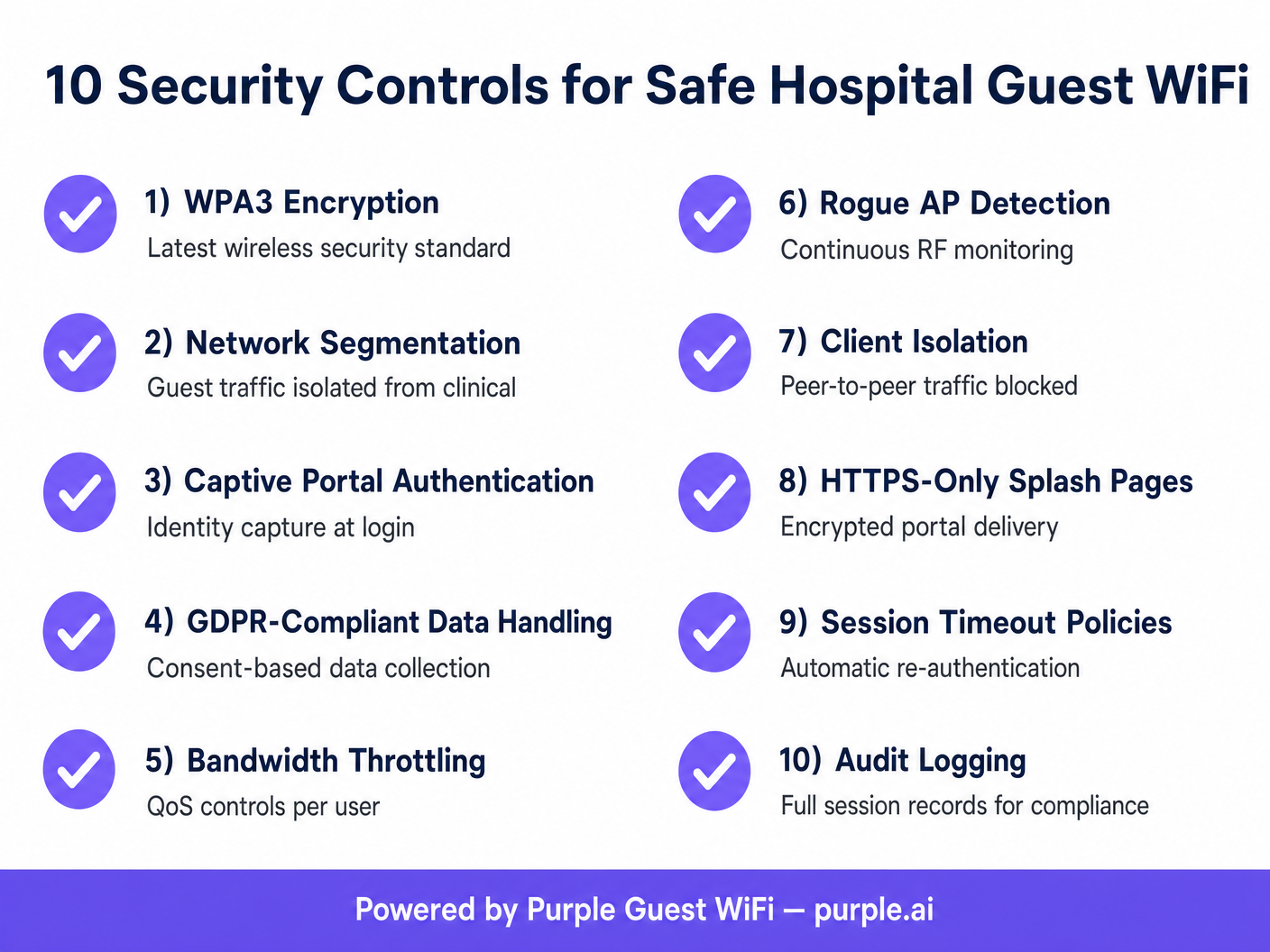
O tráfego de convidados deve ser logicamente separado dos sistemas clínicos (EHR, dispositivos médicos conectados, comunicações do pessoal) usando Redes Locais Virtuais (VLANs) distintas. A rede WiFi do paciente deve ser configurada para encaminhar o tráfego diretamente para o gateway da internet, ignorando completamente as tabelas de encaminhamento internas. Os firewalls devem impor Listas de Controlo de Acesso (ACLs) rigorosas que neguem qualquer tráfego de entrada da VLAN de convidados para as VLANs clínicas.
Padrões de Encriptação
Historicamente, as redes abertas para convidados não forneciam encriptação over-the-air. A adoção de WPA3 (Wi-Fi Protected Access 3) e Opportunistic Wireless Encryption (OWE) transformou este cenário. O WPA3 fornece encriptação de dados individualizada mesmo em redes que não exigem uma chave pré-partilhada, reduzindo significativamente o risco de escuta passiva. Além disso, a integração do Passpoint (Hotspot 2.0) permite um roaming contínuo e encriptado. A Purple atua como um fornecedor de identidade gratuito para serviços como o OpenRoaming sob a licença Connect, permitindo uma autenticação segura baseada em perfis que elimina o atrito das palavras-passe tradicionais, mantendo a segurança de nível empresarial.
Guia de Implementação: Proteger a Experiência do Paciente
A implementação de WiFi seguro em hospitais requer uma abordagem sistemática à gestão de identidades e mitigação de ameaças.
O Papel do Captive Portal
O Captive Portal é o principal ponto de aplicação das políticas de rede de convidados. Não é apenas um exercício de branding; é um mecanismo de conformidade. Ao implementar um Captive Portal através de uma plataforma de WiFi Analytics , as equipas de TI devem garantir que este impõe a entrega apenas por HTTPS para evitar a interceção de credenciais. O portal também deve recolher o consentimento do utilizador em conformidade com o GDPR ou regulamentos de privacidade locais antes de conceder acesso.
Isolamento de Clientes e Mitigação de APs Maliciosos
Para proteger os utilizadores de ataques laterais, o Isolamento de Clientes (também conhecido como Isolamento de AP) deve ser ativado no SSID de convidados. Isto impede que os dispositivos conectados ao mesmo ponto de acesso comuniquem diretamente entre si, neutralizando ameaças peer-to-peer. Além disso, é necessário um monitoramento contínuo de RF para detetar e conter pontos de acesso maliciosos. Se um ator malicioso tentar um ataque de "evil twin" (gémeo malicioso) falsificando o SSID do hospital, o sistema de prevenção de intrusões sem fios (WIPS) deve desautenticar automaticamente os clientes que tentam conectar-se ao AP malicioso.
Melhores Práticas para Equipas de TI na Saúde
- Implementar Filtragem de DNS: Bloquear o acesso a domínios maliciosos conhecidos, sites de phishing e conteúdo inadequado ao nível do DNS. Isto protege a rede contra malware e limita a responsabilidade.
- Impor Qualidade de Serviço (QoS): Aplicar limitação de largura de banda por utilizador para evitar a saturação da rede. Um único utilizador a fazer streaming de vídeo de alta definição não deve degradar o desempenho de toda a rede WiFi do paciente.
- Gestão de Sessões: Configurar políticas agressivas de tempo limite de sessão. Exigir que os utilizadores se autentiquem novamente diariamente para limpar sessões inativas e manter um registo de auditoria preciso dos dispositivos ativos.
- Auditoria Regular: Realizar testes de penetração sem fios trimestrais e rever as regras da firewall para garantir que o isolamento da VLAN permanece intacto.
Para mais informações sobre implementações seguras em ambientes complexos, consulte o nosso guia abrangente WiFi em Hospitais: Um Guia para Redes Clínicas Seguras .
Resolução de Problemas e Mitigação de Riscos
Modos de falha comuns em redes de convidados de hospitais frequentemente resultam de VLANs mal configuradas ou segurança inadequada do portal.
- Modo de Falha: Esgotamento de DHCP: As redes de convidados frequentemente experimentam alta rotatividade. Se os tempos de concessão de DHCP forem muito longos, o pool de IPs esgotar-se-á, impedindo novas conexões. Mitigação: Definir os tempos de concessão de DHCP para a sub-rede de convidados para 1-2 horas.
- Modo de Falha: Desvios de Captive Portal: Utilizadores avançados podem tentar contornar o Captive Portal usando tunelamento de DNS. Mitigação: Bloquear todos os pedidos DNS de saída da VLAN de convidados, exceto aqueles direcionados aos servidores DNS aprovados e filtrados.
Desafios semelhantes são frequentemente observados em outros ambientes de grande afluência; para uma visão comparativa, consulte o nosso guia sobre O WiFi de Cafés e Cafetarias é Seguro? .
ROI e Impacto no Negócio
O retorno do investimento para uma implementação segura de WiFi em hospitaisO retorno é medido na mitigação de riscos e na eficiência operacional. Uma violação originada de uma rede de convidados não segura pode resultar em milhões de dólares em multas, danos à reputação e operações clínicas interrompidas. Ao implementar uma arquitetura robusta e segmentada, os hospitais reduzem os tickets de suporte técnico relacionados a problemas de conectividade e melhoram os índices de satisfação do paciente. Os dados recolhidos através de Captive Portals seguros e conformes também fornecem análises valiosas sobre o fluxo de visitantes e os tempos de permanência, auxiliando no planeamento operacional e na alocação de recursos.
Referências
[1] IEEE Standards Association. "IEEE 802.1X-2020 - IEEE Standard for Local and Metropolitan Area Networks--Port-Based Network Access Control." https://standards.ieee.org/ieee/802.1X/7342/ [2] Wi-Fi Alliance. "Security: WPA3." https://www.wi-fi.org/discover-wi-fi/security
Termos-Chave e Definições
Network Segmentation
The practice of splitting a computer network into subnetworks to improve performance and security.
Critical in hospitals to ensure patient WiFi traffic cannot access clinical EHR systems or medical devices.
Client Isolation
A wireless network security feature that prevents devices connected to the same access point from communicating with each other.
Used on guest networks to prevent lateral attacks and peer-to-peer malware spread.
WPA3
The latest generation of Wi-Fi security, providing robust authentication and individualized data encryption.
Replaces WPA2 to offer better protection against brute-force dictionary attacks on wireless networks.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Used by IT teams to enforce terms of service, capture identity data, and ensure regulatory compliance.
Rogue Access Point
A wireless access point that has been installed on a secure network without explicit authorization from a local network administrator.
A major threat vector; IT teams use WIPS to detect and contain these devices to prevent data interception.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
The fundamental technology used to isolate guest traffic from the clinical network.
OpenRoaming
A roaming federation service that enables an automatic and secure Wi-Fi experience.
Allows patients to connect securely without passwords, using profile-based authentication.
DNS Filtering
The process of using the Domain Name System to block malicious websites and filter out harmful or inappropriate content.
Implemented on guest networks to protect users from malware and the hospital from liability.
Estudos de Caso
A 400-bed regional hospital needs to deploy patient WiFi across all wards and waiting areas. The IT director is concerned about patients inadvertently downloading malware that could spread to other devices on the guest network. How should the network be configured to mitigate this risk?
- Deploy a dedicated Guest SSID mapped to an isolated VLAN. 2. Enable Client Isolation (AP Isolation) on the wireless LAN controller for the Guest SSID to block peer-to-peer communication. 3. Implement DNS-level content filtering to block known malware and phishing domains. 4. Configure the firewall to only allow HTTP (80) and HTTPS (443) traffic outbound from the guest VLAN, blocking all other ports.
During a routine audit, the network team discovers that visitors in the cafeteria are experiencing extremely slow WiFi speeds. Investigation reveals a small number of users are streaming 4K video, saturating the access points. What is the technical solution?
Implement Quality of Service (QoS) and bandwidth throttling on the Guest SSID. Configure a per-user bandwidth limit (e.g., 5 Mbps down / 2 Mbps up) within the wireless controller or via the Purple Guest WiFi platform's policy engine.
Análise de Cenários
Q1. A hospital IT director is planning a network upgrade and wants to implement OpenRoaming for patient WiFi to improve security and user experience. What is the primary benefit of this approach compared to a traditional open network with a captive portal?
💡 Dica:Consider how the over-the-air connection is secured before the user even reaches the portal.
Mostrar Abordagem Recomendada
OpenRoaming provides automatic, profile-based authentication and encrypts the over-the-air connection (typically via Passpoint/802.1X), whereas a traditional open network transmits data in plaintext until the user authenticates at the portal (and even then, only HTTPS traffic is secure). This eliminates the risk of passive eavesdropping on the wireless link.
Q2. During a penetration test, the security team successfully accesses the hospital's IP-based security cameras from the patient WiFi network. What architectural failure does this indicate, and how should it be resolved?
💡 Dica:Think about how different types of traffic should be separated logically.
Mostrar Abordagem Recomendada
This indicates a failure in network segmentation. The patient WiFi and the security cameras are likely on the same VLAN, or the firewall ACLs between their respective VLANs are misconfigured. The resolution is to place the guest WiFi on a dedicated VLAN and implement strict firewall rules that deny all traffic from the guest VLAN to any internal IP ranges, routing guest traffic exclusively to the internet.
Q3. A venue operations director notices that the captive portal is generating warnings in modern web browsers stating the connection is 'Not Secure'. Why is this happening, and what is the technical remediation?
💡 Dica:Consider the protocol used to serve the captive portal page.
Mostrar Abordagem Recomendada
The captive portal is likely being served over unencrypted HTTP rather than HTTPS. Modern browsers flag HTTP login pages as insecure. The remediation is to install a valid SSL/TLS certificate on the wireless controller or the external captive portal server (like Purple's platform) and force all portal traffic over HTTPS (port 443).



