NAC Posture Assessment: Ensuring Managed Device Compliance Before Network Access
This technical reference guide provides a deep-dive into NAC Posture Assessment, detailing the architecture, standards, and deployment strategies required to enforce managed device compliance. It equips IT managers and network architects with actionable insights to mitigate risks and ensure secure network access across multi-site enterprise environments.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Architecture of Posture Assessment
- The Role of IEEE 802.1X and EAP-TLS
- Posture Check Categories
- WPA3-Enterprise and Cryptographic Strength
- Implementation Guide
- Phase 1: Infrastructure Readiness and PKI Design
- Phase 2: Monitor Mode (Visibility Phase)
- Phase 3: Segmented Enforcement
- Phase 4: Remediation Architecture
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact

Executive Summary
For enterprise IT leaders managing complex, multi-site environments, identity alone is no longer a sufficient metric for network access. Knowing who is connecting is secondary to knowing the security state of the device they are using. Network Access Control (NAC) posture assessment is the mechanism that bridges this gap, ensuring that only managed, compliant devices gain access to corporate infrastructure before they transmit a single packet of production traffic.
This guide provides a comprehensive technical reference on designing, deploying, and managing NAC posture assessment. We explore the underlying architecture—including 802.1X, RADIUS, and EAP-TLS—evaluate the trade-offs between agent-based and agentless interrogation, and outline a phased deployment strategy that minimises operational disruption. Whether you are securing a corporate headquarters, a distributed retail estate, or back-of-house operations in hospitality, implementing robust posture assessment is a critical step in risk mitigation and compliance enforcement.
Listen to our 10-minute technical briefing podcast below for an executive overview of the core concepts and common deployment pitfalls.
Technical Deep-Dive
The Architecture of Posture Assessment
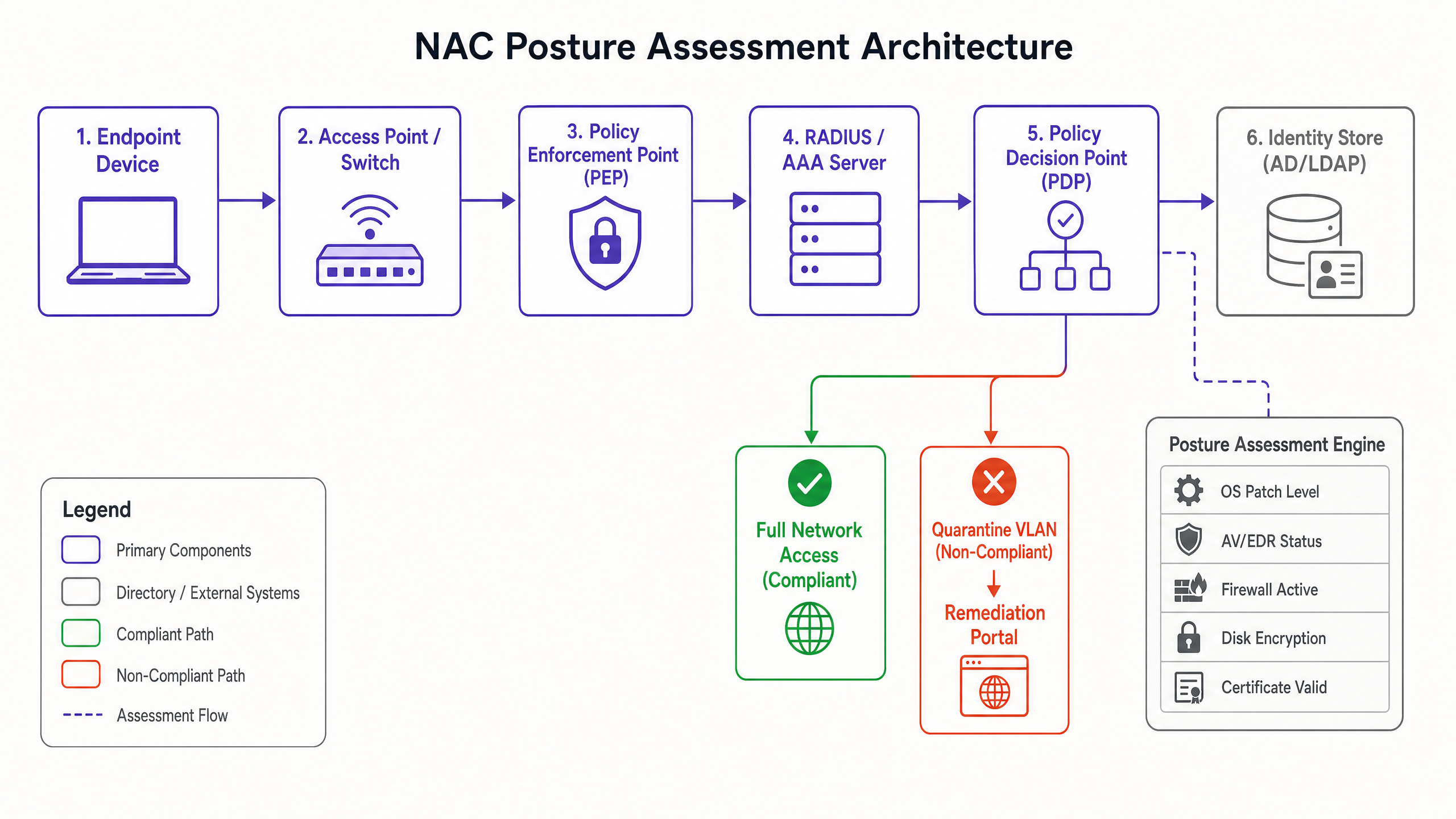
Network Access Control governs device connectivity, but posture assessment is the specific interrogation of a device's security health. The architecture relies on three primary components working in concert:
- Policy Enforcement Point (PEP): This is the physical or logical gatekeeper—typically a wireless access point, a switch port, or a wireless LAN controller. The PEP physically controls the flow of traffic based on instructions from the policy engine.
- Policy Decision Point (PDP): Often integrated within a RADIUS or AAA server, the PDP is the brain of the NAC architecture. It receives posture data, evaluates it against defined compliance policies, and issues enforcement directives to the PEP.
- Posture Assessment Engine: This component collects the actual health data from the endpoint. It can be an agent running locally on the device or an agentless mechanism leveraging network protocols (e.g., SNMP, WMI) or API integrations with Mobile Device Management (MDM) platforms.
The Role of IEEE 802.1X and EAP-TLS
The foundation of enterprise NAC is the IEEE 802.1X standard, which defines port-based network access control. Within this framework, three roles are defined:
- Supplicant: The endpoint device attempting to connect.
- Authenticator: The PEP (switch or access point) facilitating the connection.
- Authentication Server: The RADIUS server validating the credentials.
Communication between the Supplicant and the Authentication Server occurs via the Extensible Authentication Protocol (EAP), tunnelled through the Authenticator. For managed corporate devices, EAP-TLS is the gold standard. It mandates mutual authentication using X.509 digital certificates, ensuring both the device and the network verify each other's identities cryptographically. This prevents credential theft and rogue access point attacks.
Posture Check Categories
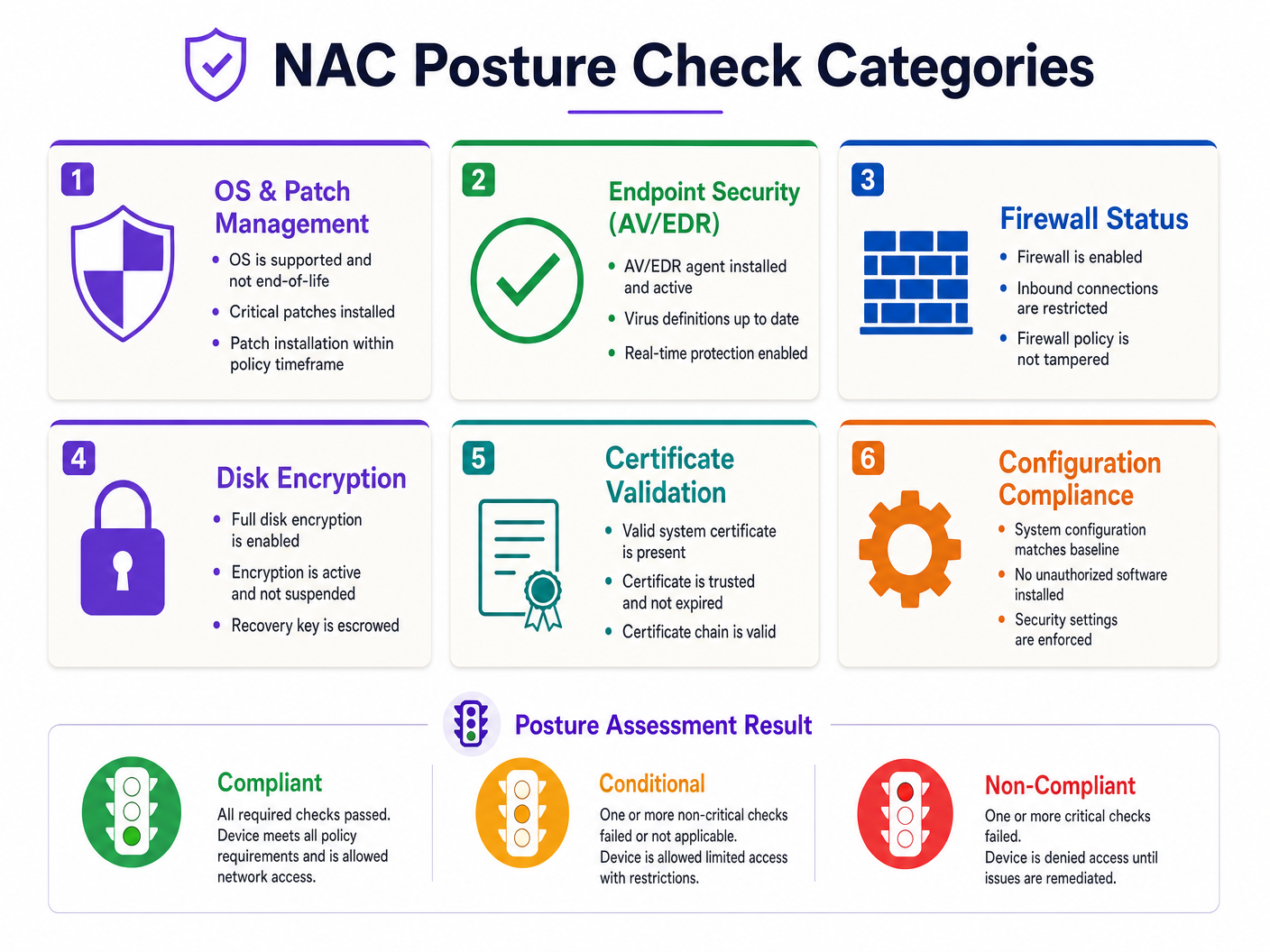
When a device attempts connection, the posture assessment engine evaluates several critical vectors:
- OS & Patch Management: Verifying the operating system is supported and critical patches are applied within the defined SLA.
- Endpoint Security (AV/EDR): Confirming that approved anti-virus or Endpoint Detection and Response agents are installed, active, and holding current definitions.
- Firewall Status: Ensuring the host-based firewall is enabled and its policy has not been tampered with.
- Disk Encryption: Validating that full-disk encryption (e.g., BitLocker, FileVault) is active and not in a suspended state.
- Certificate Validation: Checking the presence and validity of the required machine certificate.
- Configuration Compliance: Ensuring the device's security baseline matches corporate policy (e.g., screen lock timers, disabled USB mass storage).
WPA3-Enterprise and Cryptographic Strength
As network security evolves, so do the underlying cryptographic standards. WPA3-Enterprise, particularly when operating in 192-bit mode, provides significant enhancements over WPA2. It mandates the use of GCMP-256 for encryption and HMAC-SHA-384 for integrity. For organisations handling sensitive data—such as Retail environments subject to PCI DSS or Healthcare facilities under stringent data governance—transitioning to WPA3-Enterprise is a necessary step to future-proof network infrastructure.
Implementation Guide
Deploying NAC posture assessment requires careful planning to avoid widespread network outages. The following phased approach is recommended for enterprise environments:
Phase 1: Infrastructure Readiness and PKI Design
Before enabling posture checks, ensure your underlying infrastructure can support the architecture. If deploying EAP-TLS, a robust Public Key Infrastructure (PKI) is non-negotiable. Certificates must be automatically provisioned and renewed via your MDM or Group Policy. Manual certificate management will inevitably lead to connectivity failures when certificates expire.
Phase 2: Monitor Mode (Visibility Phase)
The most critical phase of any NAC deployment is Monitor Mode. In this phase, the NAC system evaluates device posture and logs the results, but does not enforce policy. The PEP allows full access regardless of the posture outcome.
Run Monitor Mode for a minimum of 2–4 weeks. This provides visibility into the actual compliance state of your estate. You will identify devices failing checks due to broken agents, pending reboots, or misconfigurations. Use this data to remediate the estate proactively.
Phase 3: Segmented Enforcement
Once the compliance baseline is acceptable, begin enforcement. Devices are categorised into three states based on policy evaluation:
- Compliant: The device passes all critical checks and is assigned to the production VLAN with full necessary access.
- Conditional: The device fails a non-critical check (e.g., a minor OS update is pending). It may be granted restricted access (e.g., internet-only) and the user is notified to remediate within a specific timeframe.
- Non-Compliant: The device fails a critical check (e.g., AV disabled). The PEP assigns the device to a Quarantine VLAN.
Phase 4: Remediation Architecture
The Quarantine VLAN must be strictly isolated. It should only permit traffic to a remediation portal, necessary update servers (e.g., Windows Update, AV definition servers), and internal IT support resources. If a quarantined device can route traffic to production subnets, the NAC architecture has failed.
Best Practices
- Continuous Assessment: Legacy NAC evaluates posture only at the time of connection. Modern deployments must support continuous assessment, re-evaluating posture at defined intervals or in response to events (e.g., an EDR alert), and dynamically updating the device's access level via Change of Authorization (CoA).
- Agent vs. Agentless: For managed corporate devices, an agent-based approach provides the deepest visibility and continuous monitoring capabilities. Agentless interrogation is suitable for unmanaged devices or environments where deploying an agent is administratively prohibitive.
- MAC Authentication Bypass (MAB): Devices incapable of 802.1X (e.g., legacy printers, IoT sensors) require MAB. However, MAB is inherently insecure as MAC addresses can be spoofed. MAB devices must be heavily profiled and placed in strictly controlled, isolated VLANs.
- Align with Standards: Base your posture policies on established frameworks such as the CIS Benchmarks. This ensures your compliance checks are vendor-neutral and aligned with industry best practices.
- Isolate Guest Traffic: Corporate NAC posture assessment should never intersect with public access networks. For venues requiring both, utilise a dedicated Guest WiFi platform, such as Purple's WiFi Analytics solution, to manage public access on entirely separate infrastructure.
Troubleshooting & Risk Mitigation
Common Failure Modes
- The 'Big Bang' Enforcement: Transitioning from open access directly to strict enforcement across the entire estate simultaneously is a guaranteed recipe for operational disruption. Always use phased rollouts by site or department.
- PKI Failures: Expired root or intermediate certificates, or failure of the Certificate Revocation List (CRL) / Online Certificate Status Protocol (OCSP) infrastructure, will cause widespread authentication failures. Implement robust monitoring for your PKI.
- Remediation Loops: Ensure that devices in the Quarantine VLAN actually have the necessary network access to download the updates required to become compliant. If they cannot reach the update servers, they remain permanently quarantined.
ROI & Business Impact
Implementing NAC posture assessment delivers measurable business value beyond raw security metrics:
- Risk Mitigation: By ensuring only healthy devices access the network, the lateral spread of malware and ransomware is significantly curtailed, reducing the likelihood of costly data breaches.
- Compliance Verification: For heavily regulated sectors like Hospitality and Transport , automated posture assessment provides continuous evidence of compliance with standards like PCI DSS and GDPR, simplifying audit processes.
- Operational Efficiency: Automating the quarantine and remediation process reduces the burden on the IT helpdesk, allowing engineers to focus on strategic initiatives rather than manually cleaning infected endpoints.
Key Definitions
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol that ensures a device must authenticate before the switch port or access point allows any IP traffic to pass.
EAP-TLS
Extensible Authentication Protocol - Transport Layer Security. An authentication framework that uses X.509 digital certificates for mutual authentication.
The recommended standard for managed corporate devices, as it relies on cryptographic certificates rather than easily compromised passwords.
Posture Assessment
The process of evaluating the security state and configuration of an endpoint device against a defined corporate policy.
Ensures that a device is not only authenticated but is also 'healthy' (patched, encrypted, protected) before being granted network access.
Policy Enforcement Point (PEP)
The network device (switch, wireless controller, or access point) that physically blocks or allows traffic based on the NAC policy.
The component that actually executes the 'allow' or 'quarantine' command issued by the NAC server.
Policy Decision Point (PDP)
The central server or engine (often a RADIUS server) that evaluates authentication requests and posture data to determine access rights.
The brain of the operation that holds the rulebase and decides what level of access a specific device should receive.
MAC Authentication Bypass (MAB)
A fallback authentication method that uses a device's MAC address as its credential when it cannot perform 802.1X.
Used for headless devices like printers or IoT sensors. It is inherently weak and must be combined with strict network segmentation.
Change of Authorization (CoA)
A RADIUS extension that allows the NAC server to dynamically change the authorization state of an active session.
Crucial for continuous assessment; if a device becomes non-compliant while connected, CoA allows the NAC server to instantly move it to a quarantine VLAN without requiring a disconnect.
Quarantine VLAN
A strictly isolated network segment designed to hold non-compliant devices, providing access only to remediation resources.
Prevents an infected or vulnerable device from communicating with production systems while it downloads necessary updates or patches.
Worked Examples
A 400-room hotel requires corporate staff laptops to securely access the back-of-house property management system (PMS). However, the venue also hosts numerous unmanaged IoT devices (smart thermostats, digital signage) that cannot run a NAC agent.
Implement an 802.1X EAP-TLS policy for all corporate staff laptops, enforcing strict posture checks (AV active, disk encrypted, patched). These devices are dynamically assigned to the Corporate VLAN upon successful compliance. For the IoT devices, implement MAC Authentication Bypass (MAB) combined with deep device profiling. Ensure these MAB devices are placed in isolated, dedicated IoT VLANs with ACLs restricting their access solely to the specific controllers they need to communicate with. Under no circumstances should the IoT VLAN route to the Corporate VLAN or the PMS.
A retail chain is rolling out new point-of-sale (POS) terminals across 50 locations. The IT team wants to enforce posture compliance to meet PCI DSS requirements but is concerned about disrupting store operations during the rollout.
Deploy the NAC architecture in Monitor Mode for 30 days. During this period, the NAC system will authenticate the POS terminals and evaluate their posture against the PCI DSS baseline (e.g., firewall active, no unauthorized software) but will log failures without blocking access. The IT team reviews the logs weekly, identifies terminals failing the checks, and remediates them via the MDM platform. Once the compliance rate reaches 100%, the policy is switched to Enforcement Mode site-by-site during maintenance windows.
Practice Questions
Q1. A recently deployed NAC solution in a corporate office is causing widespread connectivity issues. Devices that were compliant yesterday are now being placed in the Quarantine VLAN. The IT helpdesk reports that the devices appear healthy, with AV running and patches applied. What is the most likely architectural failure?
Hint: Consider the lifecycle of the credentials used in EAP-TLS.
View model answer
The most likely cause is a failure in the Public Key Infrastructure (PKI). If the machine certificates used for EAP-TLS authentication have expired, or if the NAC server cannot reach the Certificate Revocation List (CRL) or OCSP responder, the authentication will fail regardless of the device's actual security posture. The NAC system defaults to a fail-closed or quarantine state.
Q2. You are designing the VLAN architecture for a new NAC deployment. The security team insists that the Quarantine VLAN must allow access to the corporate proxy server so users can browse the internet while their devices remediate. Is this a sound design?
Hint: Evaluate the risk of allowing a potentially compromised device access to shared infrastructure.
View model answer
No, this is a flawed design. Allowing a quarantined device access to the corporate proxy introduces significant risk. If the device is infected with malware, it could use the proxy to establish command-and-control communication or attempt to pivot to other internal systems accessible via the proxy. The Quarantine VLAN must be strictly isolated, permitting access only to specific remediation servers (e.g., Windows Update, AV definition servers) and the remediation portal itself.
Q3. A hospital IT team needs to secure network access for a fleet of new wireless medical infusion pumps. These devices do not support 802.1X supplicants and cannot run a posture agent. How should network access be controlled for these devices?
Hint: Consider alternative authentication methods and the principle of least privilege.
View model answer
The devices must be authenticated using MAC Authentication Bypass (MAB). Because MAB is inherently weak (MAC addresses can be spoofed), the network access must be heavily restricted. The infusion pumps should be placed in a dedicated, isolated Medical IoT VLAN. Access Control Lists (ACLs) must be applied to this VLAN, permitting communication only with the specific central management servers required for their operation, and blocking all other lateral movement or internet access.