Power over Ethernet (PoE) for Access Points: An Implementation Guide
This guide provides infrastructure technicians, network architects, and IT decision-makers with a definitive technical reference for deploying Power over Ethernet (PoE) access points across enterprise venues including hotels, retail estates, stadiums, and public-sector facilities. It covers IEEE standards from 802.3af through 802.3bt, power budget calculation, cabling requirements, VLAN segmentation, and security compliance, with concrete implementation scenarios and measurable ROI benchmarks. Understanding PoE architecture is foundational to any [Guest WiFi](/guest-wifi) or [WiFi Analytics](/guest-wifi-marketing-analytics-platform) deployment, as the reliability of the physical layer directly determines the quality of data capture, user experience, and operational uptime.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The IEEE PoE Standards Landscape
- Power Negotiation via LLDP
- WiFi 6, 6E, and 7 Power Requirements
- Power Budget Calculation
- Cabling Architecture for PoE Access Points
- VLAN Segmentation and Network Architecture
- Implementation Guide
- Phase 1: Site Survey and Requirements Gathering
- Phase 2: Switch and Infrastructure Sizing
- Phase 3: Cabling Installation
- Phase 4: Switch Configuration
- Phase 5: Access Point Deployment and Validation
- Best Practices
- Troubleshooting & Risk Mitigation
- Access Point Operating in Degraded Mode
- Switch Port Shutting Down Under Load
- Intermittent Connectivity on Long Cable Runs
- LLDP Power Negotiation Failure
- Security Risk: Unauthorised Device Connection
- ROI & Business Impact
- Quantifying the Cost of Under-Specification
- Analytics Revenue Dependency on Infrastructure Stability
- Infrastructure Investment vs. Operational Cost
- Public Sector and Smart City Context
- Passwordless and Seamless Authentication at Scale

Executive Summary
Power over Ethernet is the foundational infrastructure layer beneath every enterprise wireless deployment. As WiFi 6, WiFi 6E, and WiFi 7 access points demand increasingly higher power budgets — in some cases exceeding 60 watts per device — the consequences of under-specifying your PoE infrastructure have never been more significant. Degraded access points, dropped captive portals, failed analytics pipelines, and unplanned outages are all direct symptoms of poor PoE planning.
This guide gives you the technical framework to make the right decisions: which IEEE standard to specify, how to calculate switch power budgets, what cabling to mandate, and how to architect VLAN segmentation for compliance. It also maps these decisions to real-world business outcomes — from guest satisfaction in hospitality environments to dwell-time analytics in retail deployments. Whether you are commissioning a 50-room hotel refresh or a 2,000-seat conference centre build-out, the principles here apply directly.
Technical Deep-Dive
The IEEE PoE Standards Landscape
The IEEE 802.3 working group has defined four progressive PoE standards, each increasing the maximum power delivery over standard Ethernet cabling. Understanding the distinctions is not academic — specifying the wrong standard at procurement locks your infrastructure into a capability ceiling that will constrain your wireless roadmap for years.
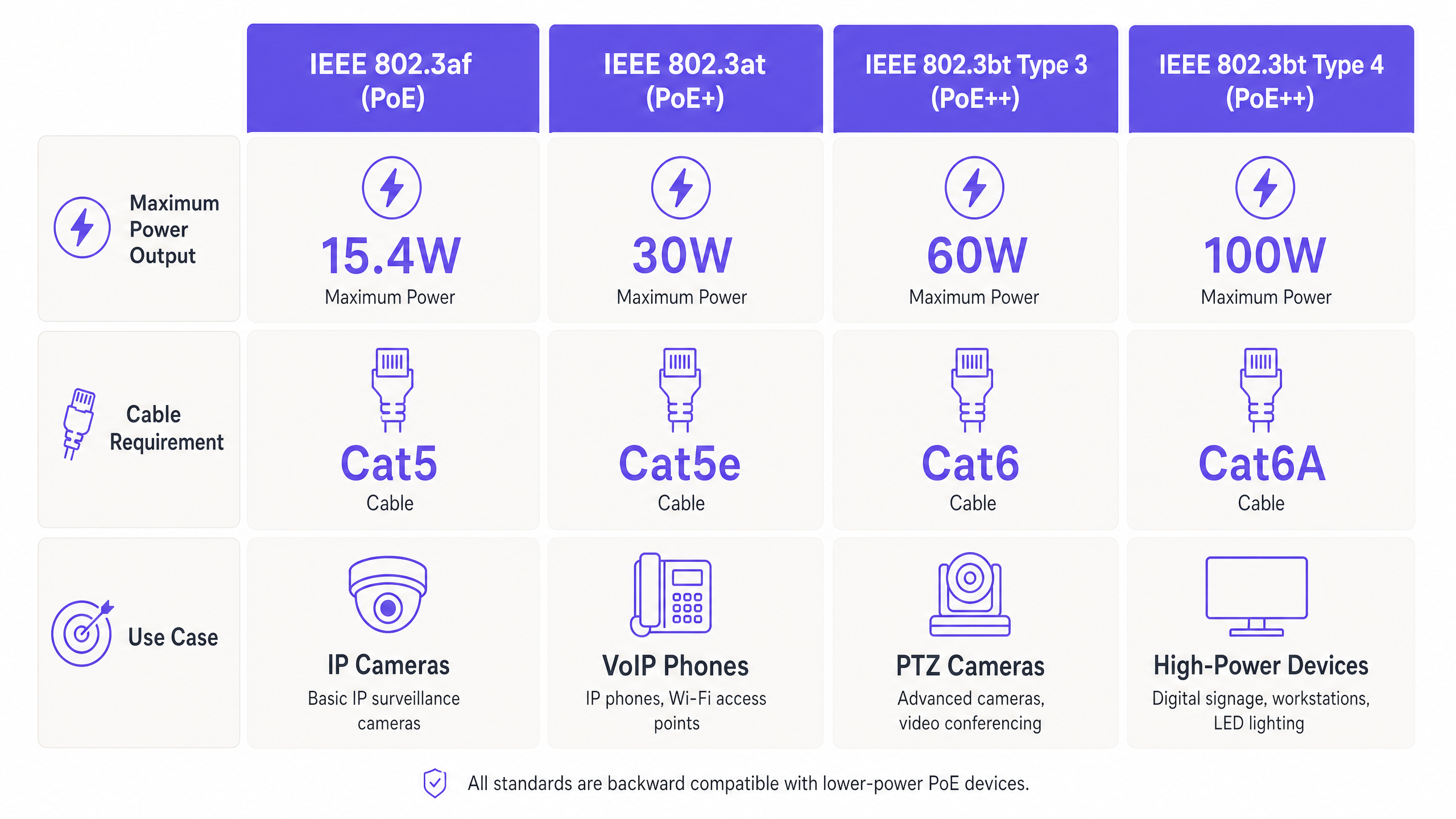
| Standard | Common Name | Max PSE Output | Max PD Receive | Cable Minimum | Pairs Used |
|---|---|---|---|---|---|
| IEEE 802.3af (2003) | PoE | 15.4 W | 12.9 W | Cat 5 | 2 pairs |
| IEEE 802.3at (2009) | PoE+ | 30 W | 25.5 W | Cat 5e | 2 pairs |
| IEEE 802.3bt Type 3 (2018) | PoE++ | 60 W | 51 W | Cat 6 | 4 pairs |
| IEEE 802.3bt Type 4 (2018) | PoE++ | 100 W | 71.3 W | Cat 6A | 4 pairs |
The distinction between PSE (Power Sourcing Equipment — your switch) and PD (Powered Device — your access point) output is critical. Cable resistance causes power loss proportional to run length and conductor gauge. A 30-watt PoE+ port will deliver approximately 25.5 watts to a device at the end of a 100-metre Cat 5e run. For high-density deployments where APs are operating near their power ceiling, this loss margin must be factored into every port calculation.
Power Negotiation via LLDP
Modern PoE switches and access points use the Link Layer Discovery Protocol (LLDP) — specifically the LLDP-MED extension — to negotiate power requirements dynamically. The powered device advertises its maximum and current power draw; the switch allocates accordingly. This prevents over-provisioning on the switch budget and protects devices from receiving excessive voltage. Ensure your switch firmware supports LLDP-MED power negotiation, particularly in mixed-vendor environments where proprietary protocols such as Cisco's CDP may not be available on third-party APs.
WiFi 6, 6E, and 7 Power Requirements
The power requirements of modern enterprise access points have increased substantially with each WiFi generation. A typical WiFi 5 (802.11ac) AP drew 12–18 watts, comfortably within 802.3af limits. A WiFi 6 (802.11ax) tri-band AP with a 2.5GbE uplink typically draws 20–30 watts, requiring PoE+. WiFi 6E APs with 6 GHz radio support commonly require 30–40 watts, pushing into 802.3bt Type 3 territory. Emerging WiFi 7 (802.11be) APs with multi-link operation and 320 MHz channel support are already specifying 40–60 watts in vendor datasheets. Specifying 802.3bt-capable switches today is a forward-looking investment, not a luxury.
Power Budget Calculation
The most common and costly PoE deployment error is failing to calculate total switch power budget against actual device draw. A 48-port PoE+ switch may advertise 30 watts per port, but its total power budget — the aggregate wattage the internal power supply can deliver to all PoE ports simultaneously — is typically 370–740 watts depending on the model. Deploying 30 APs drawing 25 watts each requires 750 watts; a 740-watt budget switch will begin shedding ports under full load.
The correct calculation methodology is:
Required Budget = (Number of APs × Per-AP Maximum Draw) × 1.25 overhead factor
The 25% overhead accounts for power supply efficiency losses, thermal derating at elevated ambient temperatures, and headroom for future device additions. Always validate this figure against the switch vendor's published PoE budget specification, not the per-port maximum.
Cabling Architecture for PoE Access Points
Cabling selection is a thermal and electrical engineering problem, not merely a data throughput question. The IEEE 802.3bt standard mandates minimum conductor specifications because higher wattage generates proportionally more heat in the cable. For bundles of cables running through ceiling voids or conduit, the cumulative thermal load can cause ambient temperature rise that degrades both power delivery and data integrity.
The recommended cabling specification by PoE standard is as follows. For 802.3af deployments, Cat 5e is the minimum viable option, though Cat 6 is recommended for any installation with a planned upgrade path. For 802.3at (PoE+) deployments, Cat 6 should be considered the baseline, with Cat 6A strongly preferred for runs exceeding 60 metres or in high-density cable trays. For 802.3bt deployments at 60 watts or above, Cat 6A is mandatory. The ANSI/TIA-568-B2-1 standard specifies AWG24 conductors as the minimum for PoE applications; AWG23 conductors in Cat 6A provide meaningfully lower resistance and better thermal performance.
For venues such as stadiums and large conference centres — where cable runs from IDF closets to under-seat or ceiling-mounted APs can approach the 100-metre limit — Cat 6A is the only defensible specification. The additional cost per metre is marginal relative to the labour cost of a re-pull.
VLAN Segmentation and Network Architecture
Every enterprise PoE access point deployment must implement VLAN-based network segmentation. The minimum viable architecture separates three traffic domains: management (switch and AP management interfaces, accessible only from the NOC VLAN), corporate (authenticated staff devices, connected via 802.1X to the corporate directory), and guest (unauthenticated or portal-authenticated visitor traffic, isolated from all internal resources).
Purple's Guest WiFi platform operates natively within this architecture. The guest SSID is mapped to a dedicated VLAN, traffic is routed to Purple's cloud infrastructure for captive portal authentication and data capture, and the platform's WiFi Analytics engine processes dwell time, repeat visit rates, and demographic data entirely within the guest traffic domain. This segmentation is not optional — it is a requirement under PCI DSS 4.0 for any venue processing card payments, and it is foundational to demonstrating GDPR compliance for guest data collection.
For healthcare environments, the segmentation model extends further: IoT medical devices, nurse call systems, and patient WiFi must each occupy separate VLANs with explicit firewall policies between them. PoE switches in healthcare deployments should support 802.1X port-based authentication to prevent unauthorised device connection at the physical layer.
Implementation Guide
Phase 1: Site Survey and Requirements Gathering
Before any procurement decision, conduct a structured site survey covering four dimensions. First, map all proposed AP locations against the nearest IDF or MDF, calculating actual cable run distances including routing through conduit and ceiling voids — not straight-line distances. Second, audit existing cabling plant: identify cable category, installation date, and any known fault history. Third, inventory existing switch infrastructure: note PoE capability, per-port wattage, and total power budget. Fourth, document the AP models under consideration and extract their maximum power draw from vendor datasheets under full radio load — not the 'typical' figure.
For transport hubs and large public-sector venues, this survey phase should also include an RF propagation study to determine AP density requirements, which directly drives the total PoE port count and switch sizing.
Phase 2: Switch and Infrastructure Sizing
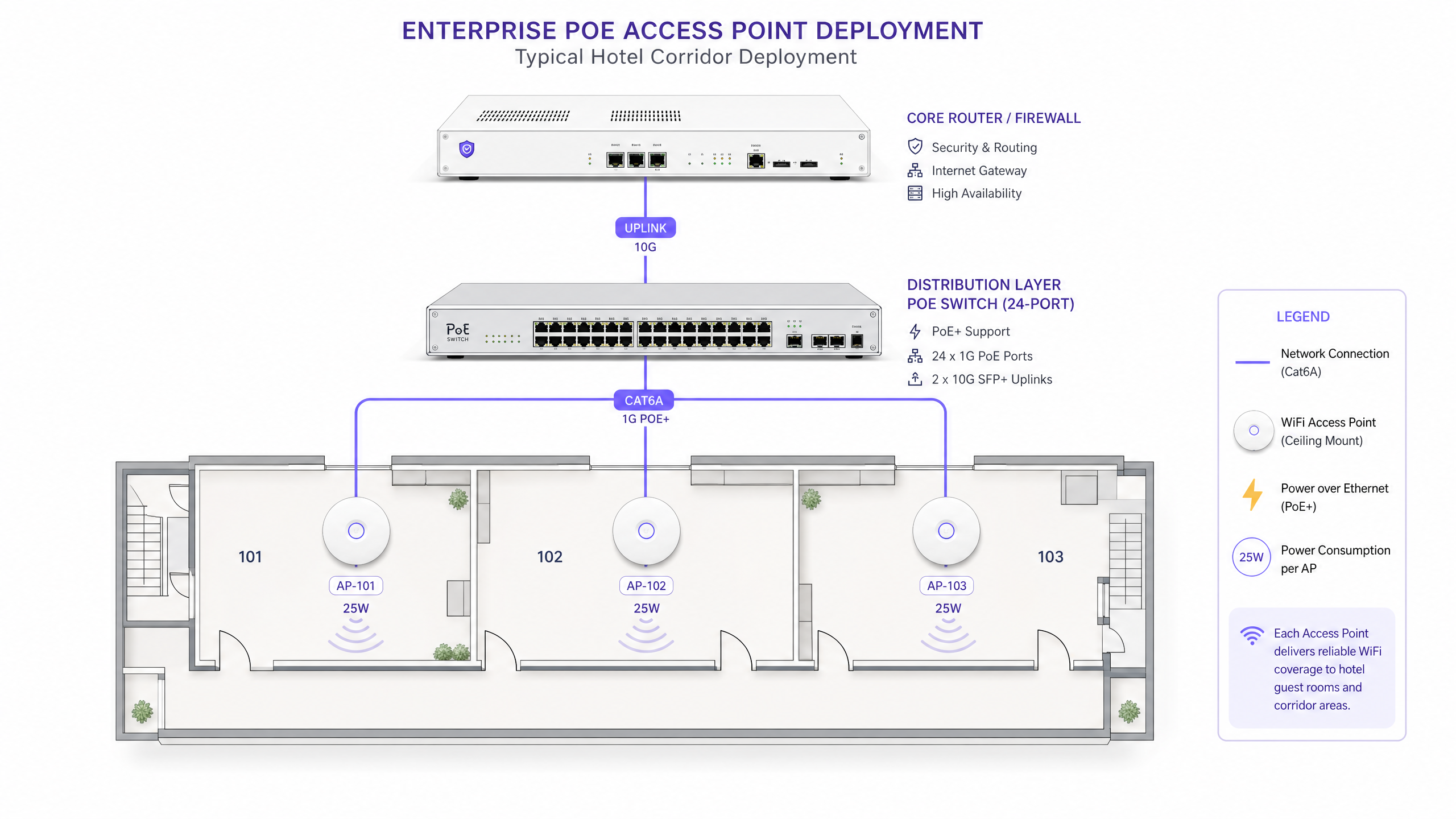
With survey data in hand, size your PoE switches using the budget calculation described above. For multi-floor or multi-building deployments, the standard architecture places a PoE distribution switch in each IDF closet, connected via 10GbE or 25GbE fibre uplinks to a core switch at the MDF. This keeps PoE cable runs short — reducing power loss and thermal load — while concentrating management at the core.
For redundancy in critical environments such as hospitals, airports, or large hospitality venues, specify switches with dual redundant power supplies. A single PSU failure on a 48-port PoE switch can take down an entire floor of access points simultaneously.
Phase 3: Cabling Installation
Install cabling to ANSI/TIA-568-C.2 standards. Key requirements include maintaining minimum bend radius (4× cable diameter for Cat 6A), avoiding cable runs adjacent to high-voltage electrical conduit (maintain a minimum 300mm separation), and not exceeding 50% fill capacity in cable trays to allow adequate airflow and heat dissipation. Test every run with a cable certifier to TIA-568-C.2 channel limits before switch installation — identifying faults at this stage costs minutes; identifying them after AP mounting costs hours.
Phase 4: Switch Configuration
Configure PoE switches with the following baseline settings. Enable LLDP globally and on all access ports. Set PoE priority levels: assign 'critical' priority to APs serving primary coverage areas, 'high' to secondary coverage APs, and 'low' to non-critical devices such as IoT sensors. Configure per-port power limits to match the AP's maximum draw plus a 10% margin — this prevents a single faulty AP from consuming disproportionate budget. Enable SNMP traps for PoE power threshold alerts, and configure your NMS to alert at 80% of total switch budget utilisation.
For 802.1X port security, configure the switch to place unauthenticated devices into a restricted VLAN rather than blocking them entirely — this simplifies troubleshooting while maintaining security posture.
Phase 5: Access Point Deployment and Validation
Mount APs according to the RF survey plan. After physical installation, validate PoE delivery using the switch CLI: confirm the negotiated power class, actual draw, and LLDP power advertisement for each port. Compare actual draw against the vendor datasheet maximum — a significant discrepancy may indicate a cable fault, a power budget constraint, or a firmware issue causing the AP to operate in a degraded power mode.
For platforms like Purple's Guest WiFi , validate the captive portal flow end-to-end from a guest device: confirm SSID visibility, portal redirect, authentication, and data capture before signing off the installation. A PoE-related power degradation that disables the 5GHz radio will not be immediately obvious from the switch CLI but will be visible in Purple's analytics as a sudden drop in connected device count on that AP.
Best Practices
The following vendor-neutral best practices are drawn from IEEE standards, ANSI/TIA cabling specifications, and field experience across enterprise deployments.
Always specify Cat 6A for new installations. Even if your current AP models only require PoE+, the incremental cost of Cat 6A over Cat 6 is typically 15–20% per metre. The cost of re-pulling cabling to support future WiFi 7 APs is orders of magnitude higher. Cat 6A is the correct specification for any installation expected to remain in service for more than five years.
Never rely on per-port wattage figures alone. Always verify the switch's total PoE power budget and calculate aggregate draw. This is the single most common cause of post-installation PoE failures in enterprise deployments.
Implement PoE power monitoring as a standard operational procedure. SNMP-based monitoring of per-port and aggregate PoE utilisation should be part of your standard NMS configuration. Trending this data over time reveals gradual power supply degradation before it causes outages.
Maintain a 20–30% power budget headroom. This is not wasteful over-provisioning — it accounts for PSU efficiency losses, temperature derating, and future device additions. A switch running at 95% of its PoE budget is a maintenance incident waiting to happen.
Separate PoE-powered devices by criticality in your VLAN and QoS policy. Access points serving primary guest WiFi should be on a higher-priority PoE class than IoT sensors or digital signage. When the switch must shed load, you want it to make the right decision automatically.
For further context on how wireless architecture choices interact with venue scale, see our guide on Mesh Network vs Access Points: Which is Better for Large Venues? , which covers the trade-offs between PoE-wired AP deployments and mesh topologies in detail.
Troubleshooting & Risk Mitigation
Access Point Operating in Degraded Mode
Symptom: AP is online but certain features — USB port, secondary radio, multi-gigabit uplink — are unavailable. Root cause: insufficient PoE power delivery. The AP has received less than its minimum operational wattage and has disabled non-essential features to remain online. Diagnosis: check the switch CLI for negotiated power class and actual draw; compare against vendor datasheet. Check cable run length and test cable with a certifier. Resolution: verify switch budget headroom, upgrade cable if necessary, or replace with a switch port supporting a higher PoE standard.
Switch Port Shutting Down Under Load
Symptom: AP ports intermittently lose power, particularly during peak usage hours when all radios are under full load. Root cause: total switch PoE budget exceeded. Diagnosis: check aggregate PoE utilisation via SNMP or CLI; compare against switch rated budget. Resolution: redistribute APs across multiple switches, add a secondary switch, or replace the switch with a higher-budget model. In the interim, reduce per-port power limits on lower-priority devices.
Intermittent Connectivity on Long Cable Runs
Symptom: APs on runs approaching 90–100 metres show intermittent connectivity or degraded throughput. Root cause: voltage drop and heat-related resistance increase on long runs. This is exacerbated by high ambient temperatures in ceiling voids. Diagnosis: cable certification test on the affected run; check ambient temperature at the cable tray. Resolution: install a PoE extender or intermediate switch to break the run, or re-route cabling to reduce run length.
LLDP Power Negotiation Failure
Symptom: AP is powered but draws maximum class power rather than negotiated power, causing budget over-allocation. Root cause: LLDP-MED not enabled on the switch port, or AP firmware does not support LLDP-MED power TLVs. Resolution: enable LLDP globally and per-port on the switch; update AP firmware; verify with a packet capture on the management VLAN that LLDP frames are being exchanged.
Security Risk: Unauthorised Device Connection
Risk: a non-authorised device is connected to a PoE switch port in a public area and gains network access. Mitigation: enable 802.1X port authentication on all access-layer switch ports. Configure MAC Authentication Bypass (MAB) as a fallback for devices that do not support 802.1X supplicants, placing them in a restricted VLAN. For venues deploying Purple's Guest WiFi , the captive portal layer provides an additional authentication checkpoint above the network layer, ensuring that even devices that obtain an IP address cannot access the internet without completing the portal flow.
ROI & Business Impact
Quantifying the Cost of Under-Specification
The business case for correct PoE specification is straightforward when you account for the full cost of failure. An access point operating in degraded mode due to insufficient power may disable its 5GHz radio, halving effective throughput and forcing clients onto the congested 2.4GHz band. In a hotel environment, this directly correlates with guest satisfaction scores — WiFi quality consistently ranks in the top three factors in guest reviews. Purple's data across hospitality deployments shows that venues with stable, high-performance WiFi see measurably higher Net Promoter Scores and repeat booking rates. For more on the relationship between WiFi quality and guest experience, see How To Improve Guest Satisfaction: The Ultimate Playbook .
Analytics Revenue Dependency on Infrastructure Stability
Purple's WiFi Analytics platform captures first-party data on every guest WiFi session: dwell time, visit frequency, demographic data from portal registration, and movement patterns across the venue. This data has direct commercial value — it informs marketing segmentation, staffing decisions, and retail layout optimisation. Every AP that drops offline due to a PoE failure represents a gap in that data. In a 200-store retail estate, even a 2% AP uptime degradation translates to significant data loss across the analytics pipeline.
Infrastructure Investment vs. Operational Cost
The incremental cost of specifying 802.3bt-capable switches over 802.3at switches is typically 15–25% at procurement. The cost of retrofitting a 100-AP deployment with higher-capacity switches two years later — including labour, downtime, and reconfiguration — routinely exceeds the original switch cost. The correct framing for the CTO is not 'do we need this capability today?' but 'will we need this capability within the operational life of this infrastructure?'. For any deployment expected to serve WiFi 6E or WiFi 7 APs, the answer is unambiguously yes.
Public Sector and Smart City Context
For public-sector organisations deploying outdoor or semi-outdoor PoE access points as part of smart city or digital inclusion initiatives, the power budget and cabling considerations are amplified by environmental factors: temperature extremes, moisture ingress, and the absence of nearby electrical infrastructure. Industrial-grade PoE switches with extended temperature ratings and IP-rated enclosures are required. Purple's expanding public-sector practice, as reflected in the appointment of Iain Fox as VP Growth for Public Sector , is directly engaged with these deployment challenges across council, transport, and education environments.
Passwordless and Seamless Authentication at Scale
As venues move toward passwordless guest access — leveraging technologies such as Passpoint and OpenRoaming — the access point infrastructure must support the associated authentication overhead. WPA3 and 802.1X-based authentication place additional processing demands on the AP, which in turn increases power draw. Ensuring your PoE infrastructure has the headroom to support these authentication protocols is part of future-proofing your deployment. For more on how this authentication model works in practice, see How a WiFi Assistant Enables Passwordless Access in 2026 .
Key Definitions
PSE (Power Sourcing Equipment)
The device that supplies power over the Ethernet cable — in enterprise deployments, this is the PoE switch or PoE injector. The PSE detects whether a connected device is PoE-capable before applying power, preventing damage to non-PoE equipment.
IT teams encounter this term when reviewing switch datasheets and power budget specifications. The PSE output wattage is always higher than the PD receive wattage due to cable losses — a distinction critical to accurate power budget calculations.
PD (Powered Device)
The device that receives power over the Ethernet cable — in wireless deployments, this is the access point. The PD communicates its power class and current draw to the PSE via LLDP, enabling dynamic power allocation.
Relevant when reading AP vendor datasheets. The 'required power' figure in an AP datasheet is the PD receive figure, not the PSE output figure. Always verify which figure the vendor is quoting.
PoE Power Budget
The total aggregate wattage a PoE switch can deliver across all its PoE ports simultaneously. This is a hard limit determined by the switch's internal power supply capacity and is distinct from the per-port maximum wattage.
The most commonly misunderstood specification in PoE switch procurement. A 48-port PoE+ switch with a 30W per-port maximum may have a total budget of only 370W — sufficient for approximately 12 APs at full load, not 48.
LLDP-MED (Link Layer Discovery Protocol - Media Endpoint Discovery)
An extension to the IEEE 802.1AB LLDP standard that enables PoE-capable devices to advertise their power requirements and capabilities to the PSE. Allows dynamic power negotiation rather than static class-based allocation.
Relevant during switch configuration and AP commissioning. If LLDP-MED is not enabled on the switch port, the switch will allocate the maximum class power rather than the negotiated amount, consuming more of the power budget than necessary.
4PPoE (4-Pair Power over Ethernet)
The power delivery method introduced in IEEE 802.3bt that uses all four pairs of conductors in an Ethernet cable to carry power, enabling the higher wattage levels of PoE++ (60W and 100W). Earlier standards used only two pairs.
Critical when specifying cabling for 802.3bt deployments. 4PPoE requires that all four pairs in the cable are intact and correctly terminated — a single faulty pair will prevent the device from receiving full power. Cable certification must verify all four pairs.
IDF (Intermediate Distribution Frame)
A secondary wiring closet or rack that aggregates network connections from a floor or zone and connects them via uplink to the main distribution frame (MDF). In PoE deployments, the IDF is where distribution-layer PoE switches are located.
IDF placement is a critical design decision in PoE deployments. Every metre of cable run between an IDF and an AP represents power loss and thermal load. Poorly positioned IDFs force long cable runs that push the limits of PoE power delivery.
PoE Priority Class
A switch configuration parameter that determines which ports receive power first when the switch approaches its total power budget limit. Typically three levels: critical, high, and low. Lower-priority ports are shut down first when budget is exhausted.
Must be configured during switch setup. Access points serving primary coverage areas should be assigned 'critical' priority. Failing to configure priority means the switch makes arbitrary decisions during power budget exhaustion, potentially shutting down mission-critical APs.
802.1X Port Authentication
An IEEE standard for port-based network access control that requires devices to authenticate before being granted network access. In PoE switch deployments, 802.1X prevents unauthorised devices from connecting to access-layer switch ports and gaining network access.
Relevant in any deployment where PoE switch ports are physically accessible to non-IT personnel — retail shop floors, hotel corridors, conference rooms. Without 802.1X, any device plugged into a switch port receives network access. This is a PCI DSS and general security requirement.
Thermal Derating
The reduction in a PoE switch's maximum power output capacity at elevated ambient temperatures. Most enterprise switches are rated for full PoE output at 25°C; above this threshold, the power supply reduces output to prevent overheating.
Relevant in deployments where switches are located in poorly ventilated spaces — ceiling voids, compact wall-mount enclosures, or outdoor cabinets. A switch rated at 740W at 25°C may only deliver 600W at 40°C. Factor thermal derating into power budget calculations for any non-conditioned environment.
Worked Examples
A 200-room hotel is upgrading from legacy WiFi 4 to WiFi 6. The existing cabling plant is Cat 5e, installed approximately 12 years ago. The IT manager needs to deploy 180 access points — one per room plus corridors and public areas — and wants to future-proof for WiFi 6E within three years. The budget is constrained, and a full cabling replacement is not feasible in Phase 1. How should the PoE infrastructure be specified?
The solution requires a phased approach that respects the current cabling constraint while building a credible upgrade path. In Phase 1, specify WiFi 6 APs with a maximum draw of 25 watts or less — this keeps the deployment within 802.3at (PoE+) limits and within the thermal envelope of the existing Cat 5e cabling. Select APs that explicitly support operation at 25.5W (the maximum PD receive for 802.3at) rather than requiring 30W at the PSE port. For the switch layer, specify 802.3bt-capable switches even though Phase 1 APs only require PoE+. The incremental cost is modest, and this avoids a switch replacement in Phase 2. Size each IDF switch at a minimum of 740W total PoE budget for a 24-port switch, supporting up to 24 APs at 25W with a 24% overhead margin. Deploy one switch per floor in IDF closets, connected via 10GbE SFP+ fibre uplinks to the core. In Phase 2 (12–24 months), replace Cat 5e with Cat 6A in sections where WiFi 6E APs will be deployed first — typically high-density public areas: lobby, restaurant, conference rooms. The 802.3bt switches are already in place; simply swap the APs and the infrastructure is ready. Configure VLANs from day one: VLAN 10 for management, VLAN 20 for corporate staff, VLAN 30 for guest WiFi. Map Purple's captive portal to VLAN 30 with a dedicated DHCP scope and upstream routing to Purple's cloud.
A regional retail chain with 85 stores is deploying Purple's Guest WiFi and WiFi Analytics platform across its entire estate. Each store has between 3 and 8 access points depending on floor area. The estate manager wants a standardised PoE switch specification that works across all store sizes, minimises SKU count, and supports the analytics platform reliably. Current cabling is a mix of Cat 5e and Cat 6, installed at various points over the past decade. How should the PoE infrastructure be standardised?
For a retail estate of this scale, standardisation on a single switch SKU is operationally correct — it simplifies spares management, firmware standardisation, and NOC support. The recommended approach is to specify a single 8-port or 16-port managed PoE+ switch (802.3at, minimum 120W total budget) as the standard store unit, with a 24-port variant for larger stores exceeding 6 APs. The 8-port unit at 120W supports up to 4 APs at 25W with a 20% overhead margin; the 16-port unit at 240W supports up to 8 APs. Both units should support 802.3bt on at least 2 ports to accommodate future AP upgrades without a full switch replacement. For cabling, audit each store during the initial deployment visit. Where Cat 5e is present and run lengths are under 60 metres, it is acceptable for current PoE+ APs. Flag stores with Cat 5e runs over 60 metres or with known cable faults for cabling replacement, prioritised by store revenue. Configure all switches with a standardised VLAN template: VLAN 10 management, VLAN 20 guest WiFi (mapped to Purple's platform), VLAN 30 POS systems (isolated from guest traffic per PCI DSS requirements). Deploy a zero-touch provisioning configuration so that replacement switches can be shipped to stores and self-configure on first boot — critical for an 85-store estate where on-site IT support is limited.
Practice Questions
Q1. You are specifying the network infrastructure for a new 350-seat conference centre. The venue will host events ranging from small boardroom meetings to full-capacity conferences with live streaming. The IT team has specified 45 WiFi 6E access points, each with a maximum draw of 35 watts. The venue has no existing cabling. You have been asked to specify the PoE switch infrastructure. What is the minimum total PoE budget required across all switches, and what cable category should be specified?
Hint: Remember to apply the 25% overhead factor to your calculated load, and consider that 35W per AP exceeds the 802.3at maximum PD receive figure of 25.5W.
View model answer
The minimum required PoE budget calculation is: 45 APs × 35W = 1,575W base load. Applying the 25% overhead factor: 1,575W × 1.25 = 1,969W minimum total switch PoE budget across the deployment. Since 35W per AP exceeds the 802.3at PD receive maximum of 25.5W, the switches must support IEEE 802.3bt Type 3 (60W per port). For cabling, Cat 6A is mandatory for 802.3bt deployments and is the correct specification for a new installation regardless. A typical architecture would distribute this across 3–4 IDF locations with 24-port 802.3bt switches (each with a minimum 740W budget), connected via 10GbE fibre uplinks to a core switch. Three 740W switches provide 2,220W of budget, satisfying the 1,969W requirement with adequate headroom.
Q2. During a post-installation audit of a 60-AP retail deployment, you discover that 12 access points on the third floor are operating with their 5GHz radio disabled. The switch shows all ports as 'PoE active' with no errors. The cable runs on the third floor average 85 metres. What is the most likely root cause, and what is the remediation path?
Hint: Consider the relationship between cable run length, power loss, and the AP's behaviour when it receives insufficient power. The switch showing 'PoE active' does not mean the AP is receiving full rated power.
View model answer
The most likely root cause is voltage drop and power loss on the 85-metre Cat 5e or Cat 6 cable runs, resulting in the APs receiving less than their minimum required wattage for full-feature operation. The switch showing 'PoE active' confirms power is being delivered but does not confirm the wattage received at the device. At 85 metres, resistance losses on Cat 5e can reduce delivered power by 15–20% compared to a 30-metre run. If the APs require 25W for full operation (including 5GHz radio), they may be receiving only 20–21W, causing the radio to be disabled as a power-saving measure. Remediation: first, check the switch CLI for per-port actual power draw and compare against the AP's rated maximum. Second, certify the cable runs — look for resistance values above TIA-568-C.2 limits. Third, either replace the cable runs with Cat 6A (lower resistance per metre) or install intermediate PoE extender switches to break the run length. Fourth, verify that LLDP-MED is enabled so the switch allocates the correct power class.
Q3. A hotel group is planning to deploy Purple's Guest WiFi platform across a 150-room property. The network architect has proposed a flat network design with all devices — guest WiFi, POS terminals, IP cameras, and staff devices — on a single VLAN to simplify configuration. The hotel processes card payments at the front desk and restaurant. Identify the compliance and security risks in this design and propose a corrected architecture.
Hint: Consider PCI DSS requirements for cardholder data environments, GDPR obligations for guest data, and the security implications of guest devices sharing a broadcast domain with POS terminals.
View model answer
The flat network design presents multiple critical compliance and security failures. Under PCI DSS 4.0, any network that carries cardholder data must be segmented from all other network traffic. A flat network where guest WiFi devices share a VLAN with POS terminals means the cardholder data environment (CDE) is not isolated — this is a direct PCI DSS violation that would result in a failed QSA assessment and potential loss of card processing capability. Under GDPR, guest data collected via the Purple captive portal must be handled in a controlled environment; a flat network increases the attack surface for data exfiltration. The corrected architecture requires a minimum of four VLANs: VLAN 10 for network management (switches, APs, cameras — accessible only from NOC); VLAN 20 for POS and payment systems (the CDE, with strict firewall rules permitting only payment processor traffic); VLAN 30 for guest WiFi (routed to Purple's platform, no access to internal resources); VLAN 40 for staff corporate devices (authenticated via 802.1X, access to internal systems). Each VLAN requires explicit firewall policy between it and all others, with the CDE VLAN having the most restrictive rules. This architecture satisfies PCI DSS network segmentation requirements and provides a defensible GDPR data handling posture.