How to Offer Retail Customers a Personalised Experience Using WiFi
This technical reference guide outlines how retail IT and operations teams can leverage existing guest WiFi infrastructure to deliver personalised, location-aware customer experiences. It covers architecture, data capture, CRM integration, and compliance, demonstrating how to turn anonymous footfall into actionable first-party data.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Architecture and Data Flow
- Identity Resolution and MAC Randomisation
- Network Segmentation and Security
- Implementation Guide
- Phase 1: Infrastructure Assessment
- Phase 2: Captive Portal Configuration
- Phase 3: Integration and Segmentation
- Phase 4: Automated Triggers
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary

For IT managers and venue operations directors, the mandate to deliver personalised customer experiences often translates into complex, multi-vendor integration projects. However, the most effective foundation for in-store personalisation is likely already deployed in your ceiling tiles: your enterprise guest WiFi network.
By layering a sophisticated analytics and authentication platform over existing hardware (such as Cisco Meraki, Aruba, or Ruckus), retailers can transform a basic connectivity amenity into a powerful engine for first-party data capture. This guide details how to architect, deploy, and scale a WiFi-driven personalisation strategy. We explore the mechanics of identity resolution via captive portals, the integration of dwell time and spatial analytics into CRM systems, and the automated triggering of contextually relevant offers—all while maintaining strict adherence to GDPR and PCI DSS standards.
Whether you are managing a single flagship store or a sprawling retail estate, the objective remains the same: convert anonymous footfall into known, addressable customers, enabling marketing teams to deliver the right message at the precise moment of highest intent.
Technical Deep-Dive
Architecture and Data Flow
The foundation of WiFi Analytics relies on a robust architecture that securely captures and processes customer data. The typical deployment model involves thin access points (APs) reporting to a cloud or on-premises controller. The analytics platform ingests data from this controller via API or Syslog feeds.
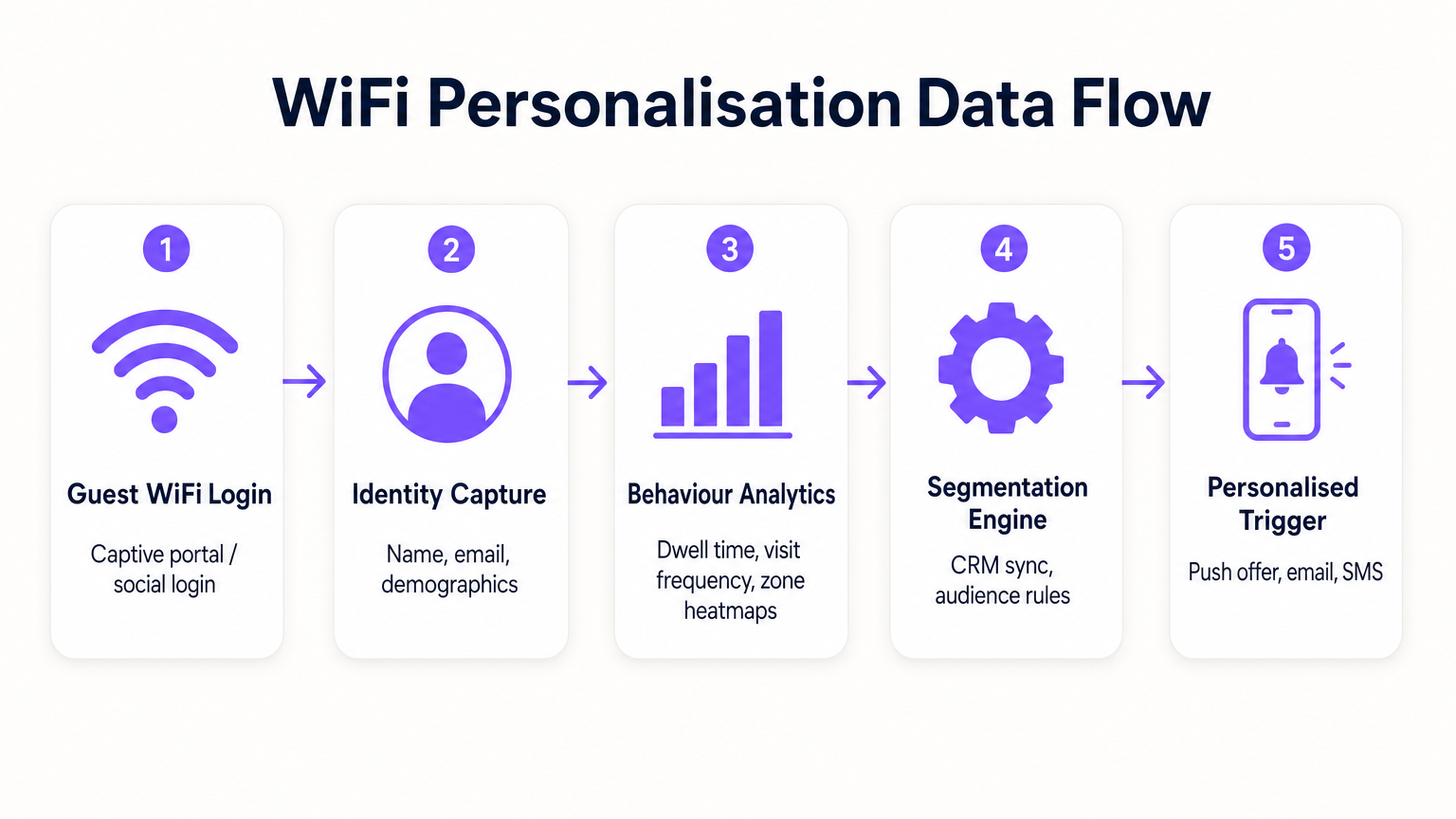
- Probe Requests and Association: Even before authentication, APs detect probe requests from mobile devices, capturing MAC addresses and signal strength (RSSI). This provides baseline footfall and zone data.
- Authentication (The Captive Portal): When a user associates with the Guest WiFi SSID, they are redirected to a captive portal. This is the critical point of identity capture. By offering authentication via email, social media, or SMS, the system links the previously anonymous MAC address to a verified identity.
- Analytics Engine: The platform correlates real-time location data (calculated via trilateration or RSSI heatmapping) with the authenticated identity, building a comprehensive profile of dwell time, visit frequency, and zone preferences.
- Integration Layer: Webhooks or REST APIs push this enriched profile data to external systems (CRM, marketing automation, loyalty platforms).
Identity Resolution and MAC Randomisation
Modern mobile operating systems (iOS 14+, Android 10+) implement MAC address randomisation to prevent persistent tracking. This makes relying solely on MAC addresses for long-term analytics obsolete. The solution is profile-based authentication. Once a user authenticates through the captive portal, their email or phone number becomes the persistent identifier. Subsequent visits, even with a new randomised MAC address, can be linked back to the core profile upon re-authentication, ensuring continuity in the customer record.
Network Segmentation and Security
Security is paramount. Guest traffic must be strictly segregated from the corporate network, typically via dedicated VLANs. This ensures compliance with PCI DSS by preventing any overlap between public internet access and point-of-sale (POS) data environments. The guest SSID should ideally utilize WPA3-Personal or WPA3-Enterprise (where supported) to encrypt over-the-air traffic, protecting user data from interception.
Implementation Guide
Deploying a personalisation strategy requires coordinated effort between IT and marketing.
Phase 1: Infrastructure Assessment
Before deploying advanced analytics, ensure the underlying RF environment is sound. Conduct a site survey to verify coverage density, particularly in high-value zones. Dwell time analytics rely on consistent signal reception; dead zones will skew the data.
Phase 2: Captive Portal Configuration
Design the captive portal to maximize opt-in rates while ensuring GDPR compliance. The value exchange must be clear. Instead of a generic login, offer an incentive: "Connect for exclusive in-store offers." Crucially, consent for network access must be unbundled from consent for marketing communications. The portal should clearly present terms and conditions and privacy policies.
Phase 3: Integration and Segmentation
Connect the WiFi platform to your existing marketing stack. This allows you to combine in-store behavioural data (e.g., "visited the shoe department for 20 minutes") with transactional data (e.g., "purchased trainers last month"). Create actionable segments, such as "High-Value Churn Risk" (frequent past visitors who haven't connected in 60 days).
Phase 4: Automated Triggers
Configure automated workflows. When a customer belonging to a specific segment authenticates, trigger an action via API. This could be an SMS offer, a push notification via the retailer's app, or an email. The latency between authentication and trigger execution should be minimal (under 30 seconds) to ensure the message is received while the customer is still engaged.
For more detailed strategies on building these profiles, refer to our guide on WiFi in Retail Stores: Building Customer Profiles From Footfall Data or the French equivalent, Le WiFi dans les magasins de détail : Créer des profils clients à partir des données de fréquentation .
Best Practices
- Prioritise the Value Exchange: Customers will only part with their data if they perceive a benefit. Ensure the WiFi is fast and reliable, and that any triggered offers are genuinely valuable.
- Respect Frequency Caps: Do not bombard customers with notifications every time they connect. Implement frequency capping (e.g., maximum one message per week) to prevent fatigue and opt-outs.
- Leverage Existing Investments: Avoid rip-and-replace scenarios. Modern analytics platforms integrate seamlessly with leading hardware vendors, allowing you to extract more value from your current infrastructure.
- Cross-Pollinate Data: WiFi data is most powerful when combined with other sources. Integrate with your loyalty program to understand how in-store behaviour correlates with overall customer lifetime value. This approach is highly relevant across various sectors, including Retail , Hospitality , and even Healthcare .
Troubleshooting & Risk Mitigation
- Low Opt-In Rates: If fewer than 20% of visitors are authenticating, review the captive portal design. Simplify the login process, clarify the value proposition, and ensure the portal is mobile-responsive.
- Inaccurate Location Data: If zone analytics appear skewed, verify AP placement and conduct a new RF survey. Interference from physical obstacles or neighbouring networks can impact RSSI calculations.
- Integration Failures: Ensure robust error handling is in place for API connections to CRMs. Monitor webhook delivery success rates and implement retry mechanisms for failed payloads.
- Compliance Risks: Regularly audit your consent flows and data retention policies. Ensure you have a streamlined process for handling Data Subject Access Requests (DSARs) under GDPR.
ROI & Business Impact
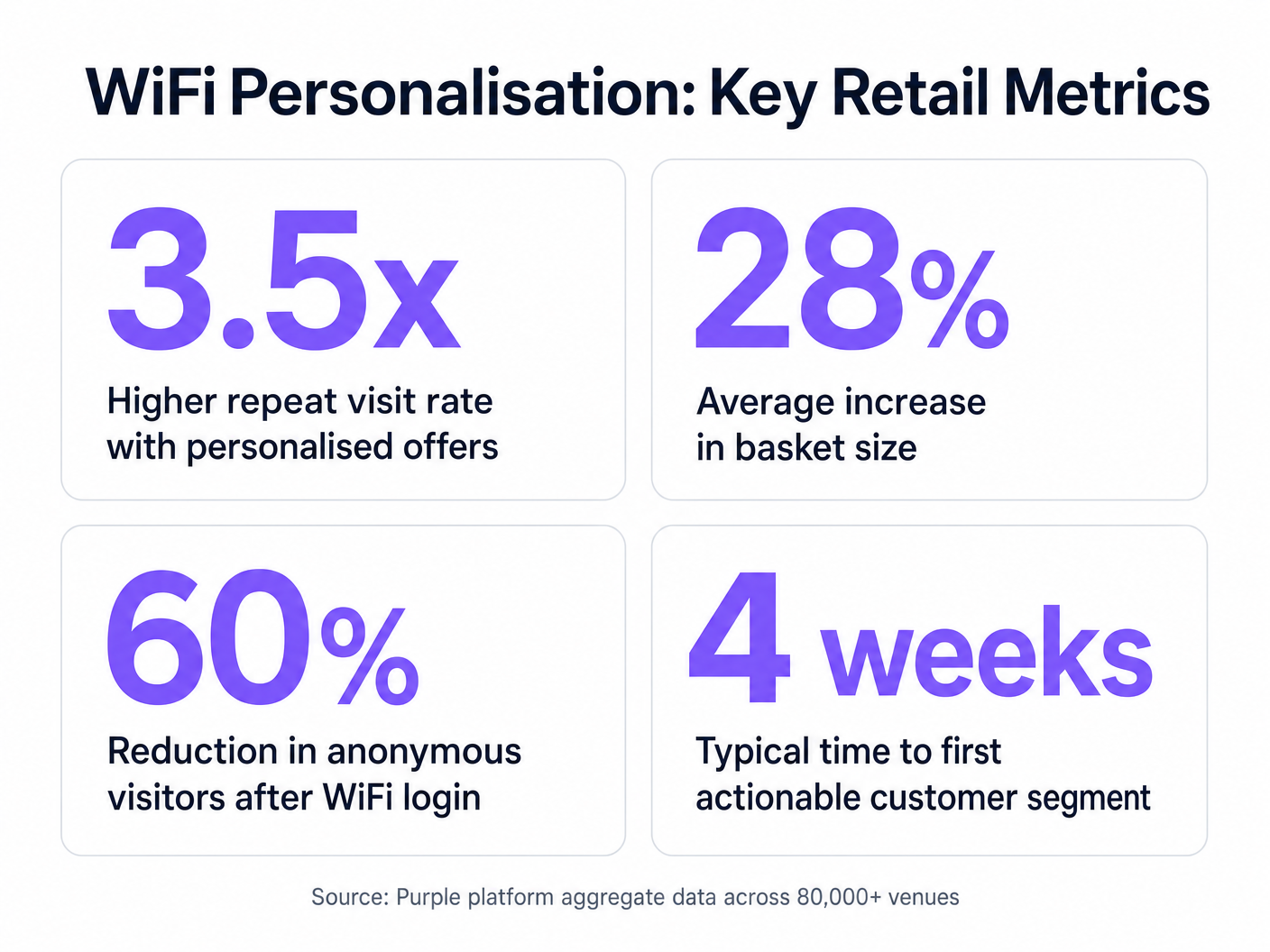
The business case for WiFi-driven personalisation is compelling. By identifying anonymous visitors, retailers can significantly expand their marketable database. Key metrics to track include:
- Database Growth Rate: The volume of net-new verified identities captured per month.
- Conversion Rate of Triggered Offers: The percentage of customers who redeem an offer pushed to them while in-store.
- Increase in Dwell Time: Measuring whether personalised engagement leads to longer store visits.
- Repeat Visit Frequency: Tracking the impact of targeted re-engagement campaigns on customer loyalty.
By moving beyond basic connectivity, IT teams can position themselves as revenue enablers, providing the essential infrastructure for modern, data-driven retail operations.
Key Terms & Definitions
Captive Portal
A web page that a user is forced to view and interact with before access is granted to a public network.
The primary interface for capturing user identity and establishing consent for data processing.
MAC Address Randomisation
A privacy feature where mobile devices use a temporary, randomly generated hardware address when scanning for or connecting to networks.
Forces IT teams to rely on authenticated profiles rather than hardware identifiers for long-term customer tracking.
Dwell Time
The duration a connected or probing device remains within the coverage area of a specific access point or defined zone.
A critical metric for understanding customer engagement with specific displays, departments, or the store as a whole.
Trilateration
A method of determining the location of a device by measuring its signal strength (RSSI) relative to three or more access points.
Used by spatial analytics platforms to generate accurate heatmaps and track customer movement patterns.
Probe Request
A frame sent by a client device to discover available wireless networks in its vicinity.
Allows analytics platforms to estimate footfall and capture anonymous presence data even if the user does not authenticate.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices, isolating their traffic from other devices on the same physical network.
Essential for security and PCI DSS compliance, ensuring guest WiFi traffic is completely segregated from corporate systems.
Webhook
A method for one application to provide real-time information to another application, typically triggered by a specific event.
Used to instantly push authentication events from the WiFi platform to a CRM, enabling real-time triggered marketing.
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal.
The fundamental metric used by access points to estimate the distance of a client device, enabling location analytics.
Case Studies
A mid-sized high street fashion retailer with 50 locations wants to reduce customer churn. They have Cisco Meraki APs deployed but are only offering a simple 'click-to-accept' splash page. How should the IT team approach upgrading this to a personalisation engine?
- Platform Integration: Integrate a dedicated WiFi analytics platform with the existing Meraki dashboard via API. No new hardware is required.
- Portal Upgrade: Replace the 'click-to-accept' page with a branded captive portal offering Social Login (Facebook/Google) or email authentication, coupled with an explicit marketing opt-in checkbox.
- CRM Sync: Configure a webhook to push newly authenticated identities and their visit data into the retailer's CRM (e.g., Salesforce).
- Campaign Execution: The marketing team creates a segment in the CRM for 'Customers who haven't visited in 90 days'. When a customer in this segment connects to the WiFi, an automated email offering a 15% discount is triggered immediately.
A large shopping centre operator needs to understand the flow of visitors between different anchor stores to optimize tenant placement and rent models. They currently rely on manual footfall counting at entrances.
- Network Tuning: The IT team optimizes the AP density to ensure consistent coverage across all concourses and store entrances, focusing on overlapping coverage for accurate trilateration.
- Analytics Deployment: Deploy a spatial analytics platform that ingests probe request data from the APs.
- Zone Mapping: Define specific zones within the analytics dashboard corresponding to key areas (e.g., 'Food Court', 'Anchor Store A', 'North Entrance').
- Data Analysis: Utilize the platform to generate heatmaps and flow diagrams, analyzing the typical paths taken by visitors and the dwell time in specific zones.
Scenario Analysis
Q1. A retail client wants to trigger an immediate SMS discount to any customer who spends more than 15 minutes in the high-margin electronics section. They currently have a single access point covering the entire store. What is the primary technical constraint?
💡 Hint:Consider how the system determines location and dwell time.
Show Recommended Approach
The primary constraint is a lack of spatial resolution. With only a single access point, the system can determine that the customer is in the store (associated with the AP), but it cannot use trilateration to pinpoint their location to a specific zone like the electronics section. The retailer must deploy additional access points to provide overlapping coverage, enabling accurate location analytics.
Q2. The marketing director is concerned that MAC address randomisation in iOS will prevent them from tracking repeat visitors. How should the IT architect respond?
💡 Hint:Focus on the transition from hardware-based tracking to identity-based tracking.
Show Recommended Approach
The architect should explain that while MAC randomisation disrupts passive tracking of anonymous devices, it does not impact authenticated users. By implementing a captive portal that requires email or social login, the system creates a persistent profile based on the user's identity. When the user returns and reconnects (even with a new MAC address), they re-authenticate, and the new session is linked to their existing persistent profile.
Q3. A stadium operator wants to deploy guest WiFi but is concerned about PCI DSS compliance, as POS terminals for concessions share the same physical network switches. What network design principle must be enforced?
💡 Hint:Think about logical separation of network traffic.
Show Recommended Approach
The IT team must enforce strict network segmentation using Virtual Local Area Networks (VLANs). The guest WiFi traffic must be placed on a dedicated VLAN that is completely isolated from the VLAN used by the POS terminals. Firewall rules must ensure that no traffic can route between the guest VLAN and the Cardholder Data Environment (CDE), thereby maintaining PCI DSS compliance.



