What Is 802.1X Authentication? How It Works and Why It Matters
A comprehensive technical reference guide for IT managers and network architects on IEEE 802.1X authentication. This guide covers the underlying architecture, implementation strategies, security benefits over PSK, and how to effectively deploy enterprise-grade access control alongside guest WiFi solutions.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: How 802.1X Works
- The Three-Party Architecture
- The Authentication Flow
- EAP Methods: Choosing the Right Protocol
- Implementation Guide
- Phase 1: Infrastructure Readiness
- Phase 2: Supplicant Configuration
- Phase 3: Pilot and Rollout
- Integrating with Guest Access
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- Audio Briefing

Executive Summary
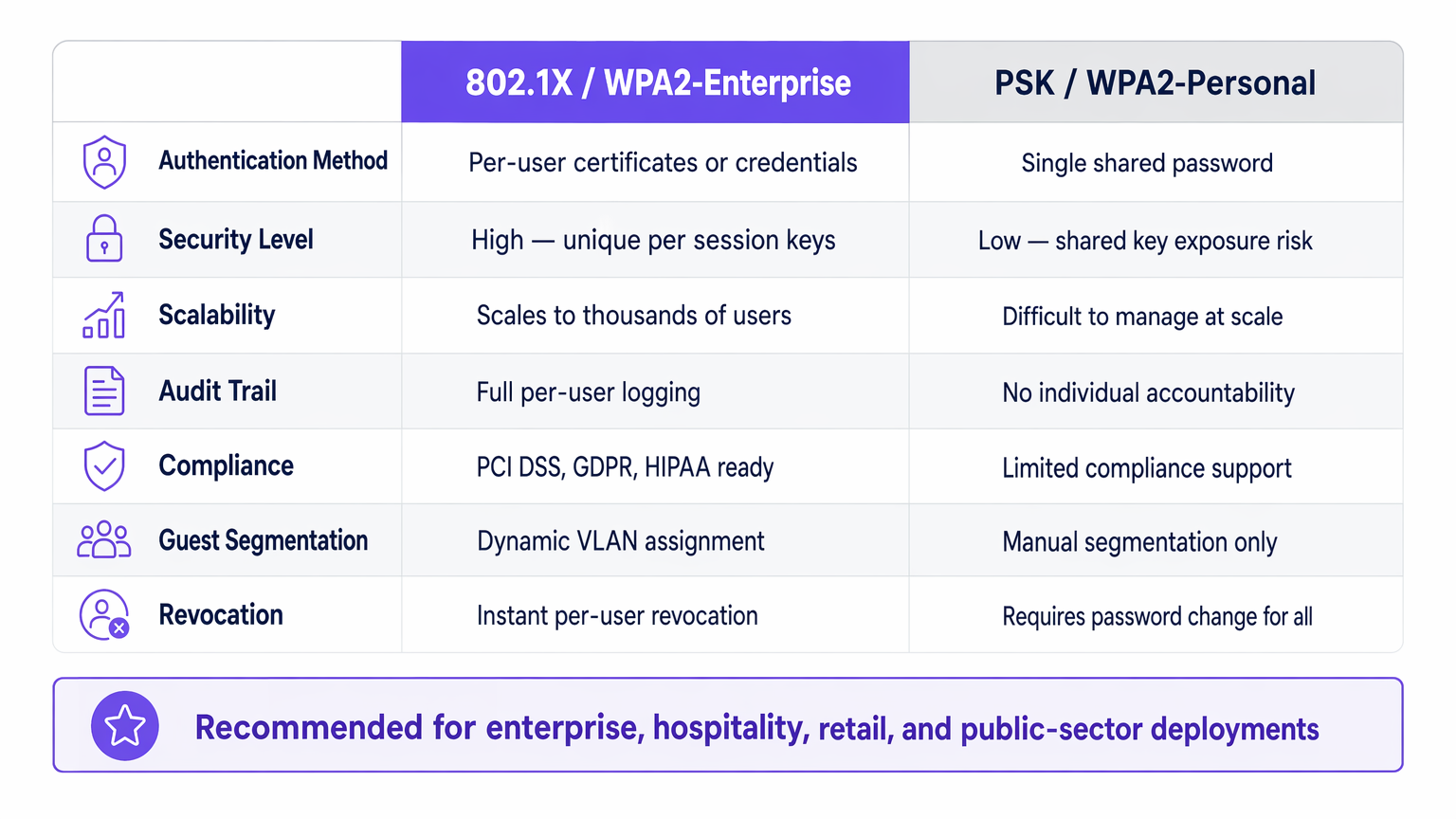
For enterprise IT leaders managing networks across Hospitality , Retail , Healthcare , or Transport venues, securing network access is a foundational requirement. Relying on Pre-Shared Keys (PSK) for corporate access introduces unacceptable risks: lack of individual accountability, complex revocation processes, and shared encryption vulnerabilities.
IEEE 802.1X is the industry-standard framework for port-based network access control. It enforces a rigorous authentication process before a device can communicate on the network, enabling per-user identity verification, dynamic policy enforcement, and compliance with frameworks like PCI DSS and GDPR. This guide explores the mechanics of 802.1X, the differences between common EAP methods, and practical deployment strategies for enterprise environments, including how it integrates with Guest WiFi solutions to provide a holistic access strategy.
Technical Deep-Dive: How 802.1X Works
At its core, 802.1X operates on a three-party model designed to isolate unauthenticated devices from the internal network.
The Three-Party Architecture
- Supplicant: The end-user device (laptop, smartphone, IoT sensor) requesting network access. It must run an 802.1X-compliant software client.
- Authenticator: The network device (wireless access point or managed switch) controlling the physical or logical port. It acts as a gatekeeper, blocking all traffic except EAP (Extensible Authentication Protocol) until authentication succeeds.
- Authentication Server: Typically a RADIUS (Remote Authentication Dial-In User Service) server. It validates the supplicant's credentials against a backend identity store (like Active Directory) and returns a policy decision.
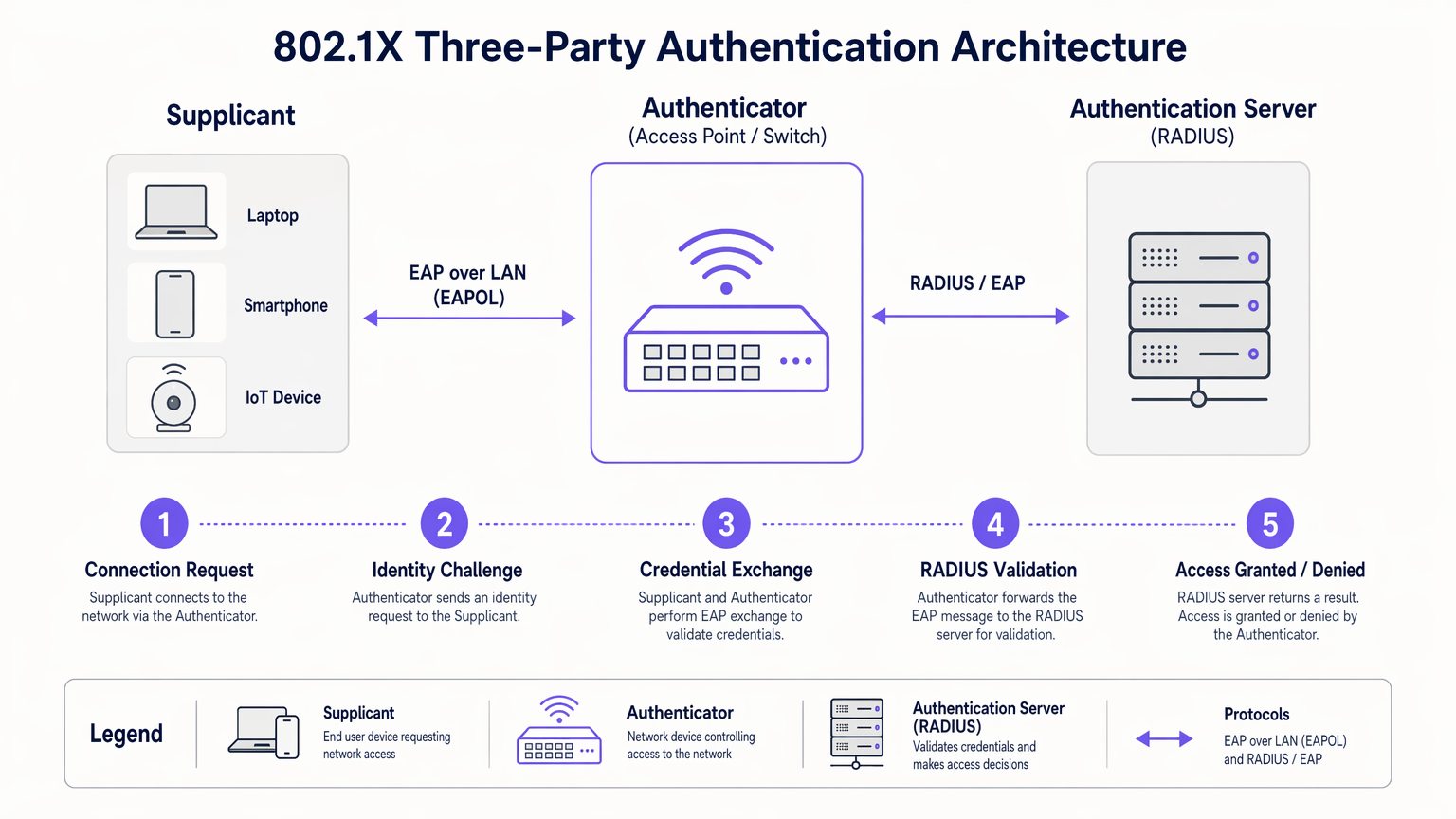
The Authentication Flow
When a supplicant connects to an 802.1X-enabled port or SSID, the authenticator places the port in an unauthorized state. The flow proceeds as follows:
- EAPOL Start: The supplicant sends an EAP over LAN (EAPOL) Start frame to the authenticator.
- Identity Request: The authenticator requests the supplicant's identity.
- Identity Response: The supplicant provides its identity, which the authenticator forwards to the RADIUS server via a RADIUS Access-Request packet.
- EAP Exchange: The RADIUS server and supplicant negotiate an EAP method and exchange credentials securely through the authenticator.
- Access Decision: Upon successful validation, the RADIUS server sends a RADIUS Access-Accept packet to the authenticator. This packet often includes vendor-specific attributes (VSAs) for dynamic VLAN assignment or QoS policies.
- Port Authorized: The authenticator transitions the port to an authorized state, allowing normal network traffic.
EAP Methods: Choosing the Right Protocol
The EAP framework is extensible. The choice of EAP method determines how credentials are exchanged and verified:
- EAP-TLS (Transport Layer Security): The gold standard for security. It requires mutual authentication using digital certificates on both the client and the server. While highly secure, it requires a robust Public Key Infrastructure (PKI).
- PEAP-MSCHAPv2 (Protected EAP): The most common deployment in enterprise environments. It uses a server-side certificate to establish a secure TLS tunnel, inside which the client authenticates using a standard username and password (MSCHAPv2). It balances security with deployment simplicity.
- EAP-TTLS (Tunneled TLS): Similar to PEAP but supports a wider range of inner authentication protocols, including legacy PAP or CHAP, often used in non-Windows environments.
Implementation Guide
Deploying 802.1X requires careful planning to avoid user disruption. A phased approach is critical for success.
Phase 1: Infrastructure Readiness
Before enabling 802.1X on the edge, ensure your core infrastructure is prepared. Deploy a RADIUS server (such as Microsoft NPS or FreeRADIUS) and integrate it with your identity provider. Configure high availability for the RADIUS infrastructure; if the authentication server fails, network access halts.
Phase 2: Supplicant Configuration
Do not rely on users to manually configure their devices. For managed corporate devices, use Group Policy Objects (GPO) or Mobile Device Management (MDM) platforms to push the correct 802.1X profile, including the required EAP method and the trusted root certificate for the RADIUS server.
Phase 3: Pilot and Rollout
Begin with a small pilot group using a dedicated test SSID or a specific switch stack. Monitor the RADIUS logs for authentication failures, particularly those related to certificate trust issues or incorrect credentials. Once the pilot is stable, proceed with a phased rollout across the organization.
Integrating with Guest Access
802.1X is designed for corporate users with known credentials. For visitors, contractors, and customers, you need a parallel strategy. This is where a dedicated Guest WiFi platform becomes essential. While corporate devices authenticate seamlessly via 802.1X onto secure VLANs, guests authenticate via a captive portal, providing valuable first-party data for WiFi Analytics while remaining isolated from internal resources.
Purple's platform can also act as an identity provider for services like OpenRoaming under the Connect license, bridging the gap between seamless public access and secure authentication.
Best Practices
- Enforce Server Certificate Validation: When using PEAP or EAP-TTLS, you must configure supplicants to validate the RADIUS server's certificate. Failing to do so leaves the network vulnerable to rogue access point (Evil Twin) attacks.
- Implement Dynamic VLAN Assignment: Leverage RADIUS attributes to assign users to specific VLANs based on their Active Directory group membership. This reduces the number of SSIDs required and simplifies network segmentation.
- Address IoT Devices with MAB: Many IoT devices (printers, smart TVs) do not support 802.1X supplicants. Use MAC Authentication Bypass (MAB) as a fallback. The authenticator uses the device's MAC address as the username and password. Because MAC addresses can be spoofed, strictly limit the access privileges of MAB-authenticated devices.
Troubleshooting & Risk Mitigation
When 802.1X fails, the RADIUS server logs are your primary diagnostic tool.
- Error: EAP Timeout: The authenticator is not receiving a response from the supplicant. This often indicates the supplicant software is not running, or the device is not configured for 802.1X.
- Error: Unknown User or Bad Password: The user entered incorrect credentials, or the RADIUS server cannot communicate with the backend identity store.
- Error: Certificate Trust Failure: The supplicant rejected the RADIUS server's certificate. Ensure the Root CA certificate that issued the RADIUS server's certificate is installed in the supplicant's trusted root store.
For a broader perspective on network architecture optimization, consider how authentication integrates with modern WAN strategies, as discussed in The Core SD WAN Benefits for Modern Businesses .
ROI & Business Impact
Implementing 802.1X delivers measurable business value beyond raw security:
- Reduced Operational Overhead: Eliminates the need to manually rotate PSKs when employees leave or contractors finish their engagements. Access is revoked instantly by disabling the user's directory account.
- Simplified Compliance: Provides the per-user audit trails and strong access controls required by PCI DSS, HIPAA, and GDPR.
- Enhanced Network Visibility: Integrates identity with network activity, allowing IT teams to trace security events or performance issues to specific users rather than generic IP addresses.
By moving away from shared keys and embracing port-based access control, enterprise networks achieve the granular security required for modern operational demands. For a detailed comparison of wireless security standards, review our guide on WPA, WPA2 and WPA3: What's the Difference and Which Should You Use? .
Audio Briefing
Listen to our 10-minute technical briefing on 802.1X authentication:
Key Terms & Definitions
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational standard replacing shared passwords with per-user authentication in enterprise networks.
Supplicant
The software client on an end-user device that requests network access and handles the EAP exchange.
Required on all laptops, phones, and tablets connecting to an 802.1X network.
Authenticator
The network edge device (switch or access point) that controls the physical or logical port, blocking traffic until authentication is complete.
The enforcement point in the network architecture.
RADIUS Server
Remote Authentication Dial-In User Service. The central server that validates credentials against a directory and returns policy decisions.
The brain of the 802.1X deployment, often implemented via Microsoft NPS or Cisco ISE.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, providing transport for various authentication methods.
The language spoken between the supplicant and the RADIUS server.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the authenticator to place a user into a specific VLAN based on their identity or group membership.
Crucial for network segmentation and compliance without broadcasting dozens of SSIDs.
EAP-TLS
An EAP method requiring mutual certificate-based authentication between the client and the server.
The most secure method, ideal for highly regulated environments like healthcare or finance.
PEAP (Protected EAP)
An EAP method that establishes a secure TLS tunnel using a server certificate, protecting the inner credential exchange (usually a username/password).
The most common deployment method due to its balance of security and operational simplicity.
Case Studies
A 200-room hotel needs to secure its back-of-house operational network (staff tablets, VoIP phones, management laptops) while maintaining a separate, open guest network. They currently use a single PSK for staff.
- Deploy Microsoft NPS (RADIUS) integrated with the hotel's Active Directory.
- Configure the wireless controller to broadcast a new 'Staff_Secure' SSID using WPA2-Enterprise (802.1X).
- Push a PEAP-MSCHAPv2 profile to all managed staff laptops and tablets via MDM.
- For VoIP phones lacking 802.1X support, configure MAC Authentication Bypass (MAB) on the RADIUS server, assigning them to an isolated Voice VLAN.
- Retain the open guest network, securing it with Purple's captive portal for guest isolation and analytics.
A large retail chain is failing PCI DSS compliance because their Point of Sale (PoS) terminals are on the same logical network segment as store manager laptops, using a shared WPA2-Personal key.
- Implement 802.1X across all corporate access points.
- Configure dynamic VLAN assignment on the RADIUS server.
- Create a policy: If the authenticating device is a PoS terminal (authenticated via machine certificate using EAP-TLS), assign it to the highly restricted PCI-VLAN.
- Create a second policy: If the user is a Store Manager (authenticated via PEAP), assign them to the Corp-VLAN with standard internet and intranet access.
Scenario Analysis
Q1. Your organization is migrating from WPA2-Personal to WPA2-Enterprise. You have a mix of corporate-owned Windows laptops and employee-owned BYOD smartphones. You do not have a PKI infrastructure. Which EAP method should you deploy?
💡 Hint:Consider the requirement for client certificates versus server-only certificates.
Show Recommended Approach
PEAP-MSCHAPv2. Since you lack a PKI infrastructure, deploying client certificates for EAP-TLS is not feasible. PEAP only requires a server-side certificate on the RADIUS server, allowing users to authenticate with their standard Active Directory username and password.
Q2. After deploying 802.1X using PEAP, several users report they are prompted with a security warning asking them to 'Trust' a certificate when connecting to the network. What configuration step was missed?
💡 Hint:Think about how the supplicant validates the identity of the RADIUS server.
Show Recommended Approach
The supplicant profile pushed to the devices was not configured to explicitly trust the Root CA that issued the RADIUS server's certificate. Without this configuration, the OS prompts the user to manually verify the server's identity, which is a security risk and poor user experience.
Q3. You need to connect 50 smart TVs in hotel conference rooms to the network. These devices do not support 802.1X supplicants. How can you provide them access while maintaining security?
💡 Hint:Consider alternative authentication methods for headless devices and how to restrict their access.
Show Recommended Approach
Implement MAC Authentication Bypass (MAB). The authenticator will use the smart TV's MAC address to authenticate against the RADIUS server. Crucially, the RADIUS server must be configured to assign these devices to a heavily restricted VLAN (e.g., internet-only, no internal access) to mitigate the risk of MAC address spoofing.



