What Is EAP-TLS? Certificate-Based WiFi Authentication Explained
This guide provides a comprehensive technical reference on EAP-TLS (Extensible Authentication Protocol with Transport Layer Security), the most secure 802.1X authentication method available for enterprise WiFi. It covers the X.509 certificate infrastructure required, the mutual authentication handshake, and practical deployment patterns for hospitality, retail, healthcare, and public-sector environments. IT managers, network architects, and CTOs will find actionable guidance on PKI design, MDM-integrated certificate provisioning, RADIUS configuration, and compliance alignment with PCI DSS and GDPR.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- What EAP-TLS Actually Does
- X.509 Certificates and PKI Architecture
- EAP-TLS vs. Other 802.1X Methods
- WPA2 Enterprise and WPA3 Enterprise
- Implementation Guide
- Phase 1: PKI Design and Deployment
- Phase 2: RADIUS Server Configuration
- Phase 3: Certificate Distribution via MDM/SCEP
- Phase 4: Access Point and SSID Configuration
- Phase 5: Client Supplicant Configuration
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- Risk Mitigation for Large-Scale Deployments
- ROI & Business Impact
- Quantifying the Security Investment
- Operational Efficiency Gains
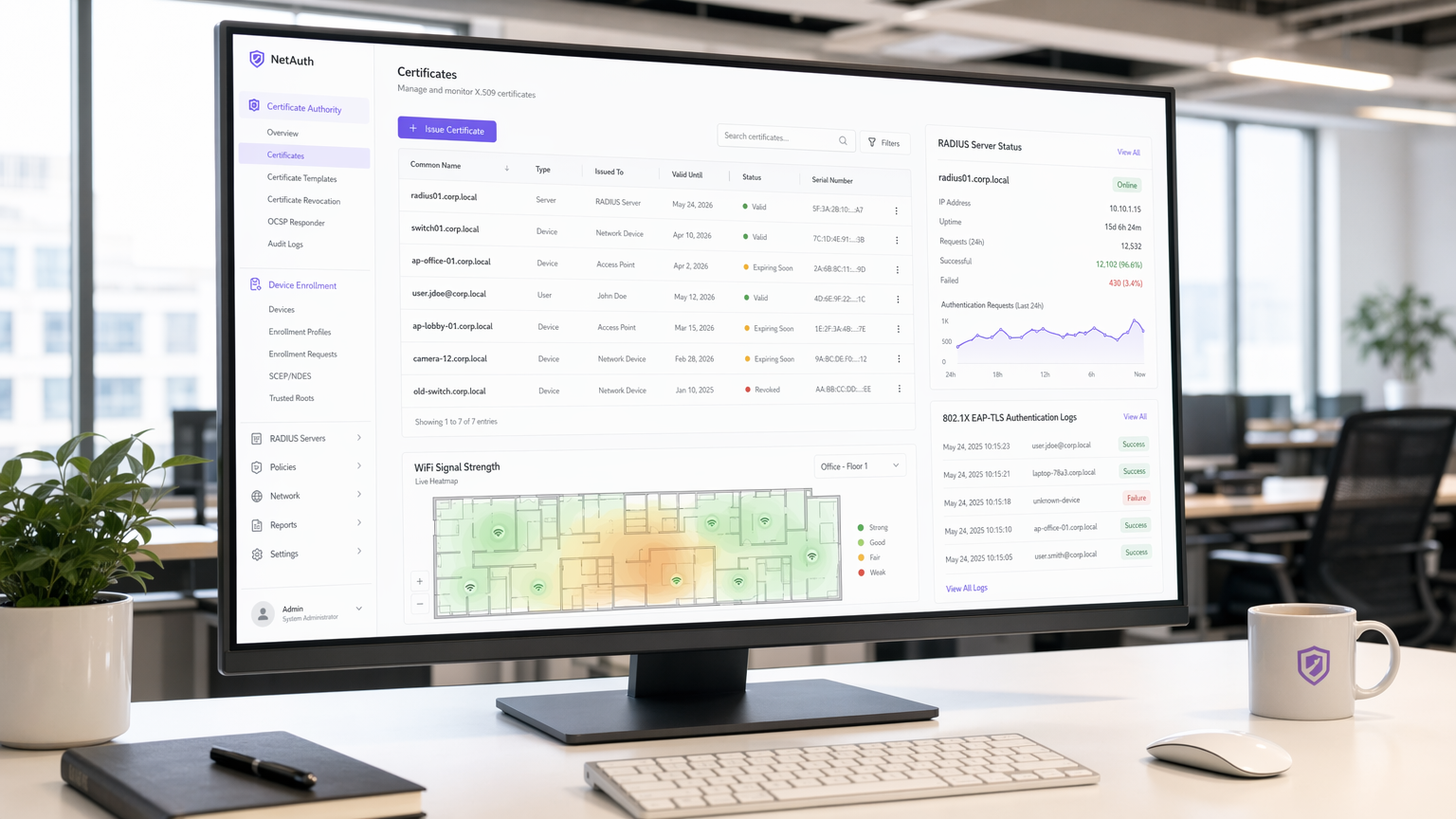
- Purple's Role in Secure Enterprise WiFi
Executive Summary
EAP-TLS (Extensible Authentication Protocol – Transport Layer Security) is the IEEE 802.1X authentication method that eliminates shared credentials from your wireless authentication chain entirely. Where PEAP and EAP-TTLS rely on usernames and passwords transmitted through an encrypted tunnel, EAP-TLS requires both the client device and the RADIUS server to present valid X.509 certificates issued by a trusted Certificate Authority (CA). This mutual authentication model means a stolen password is irrelevant — without a valid, non-revoked certificate, a device cannot join the network.
For venue operators running Guest WiFi across hotels, retail estates, or conference centres, and for IT teams responsible for staff and IoT device networks, EAP-TLS represents the current ceiling of wireless authentication security. It is mandated or strongly recommended by PCI DSS 4.0 for cardholder data environments, by HIPAA for healthcare wireless networks, and is the required method for WPA3 Enterprise 192-bit (Suite B) deployments.
The deployment overhead is real — certificate lifecycle management, PKI infrastructure, and MDM integration are non-trivial — but the security ROI is substantial. This guide walks through the architecture, the handshake, deployment patterns, and the operational practices that determine whether an EAP-TLS rollout succeeds or stalls.
Technical Deep-Dive
What EAP-TLS Actually Does
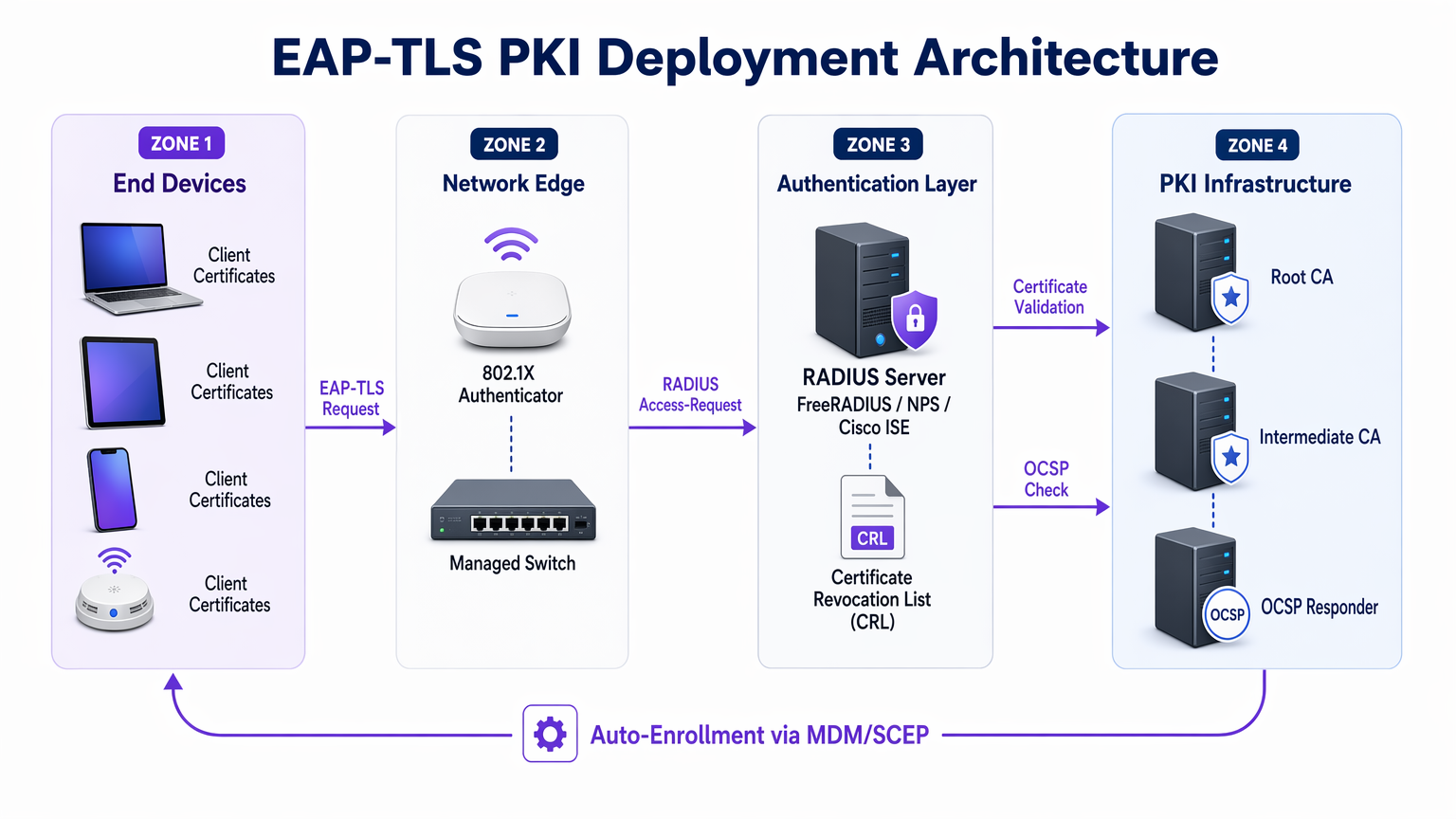
EAP-TLS operates within the 802.1X port-based access control framework. The three actors in every authentication exchange are the supplicant (the client device), the authenticator (the wireless access point or managed switch), and the authentication server (typically a RADIUS server such as FreeRADIUS, Microsoft NPS, or Cisco ISE). The access point does not make authentication decisions itself — it acts as a transparent relay, encapsulating EAP messages in RADIUS packets and forwarding them to the authentication server.
For a deeper understanding of how RADIUS underpins this architecture, see What Is RADIUS? How RADIUS Servers Secure WiFi Networks .
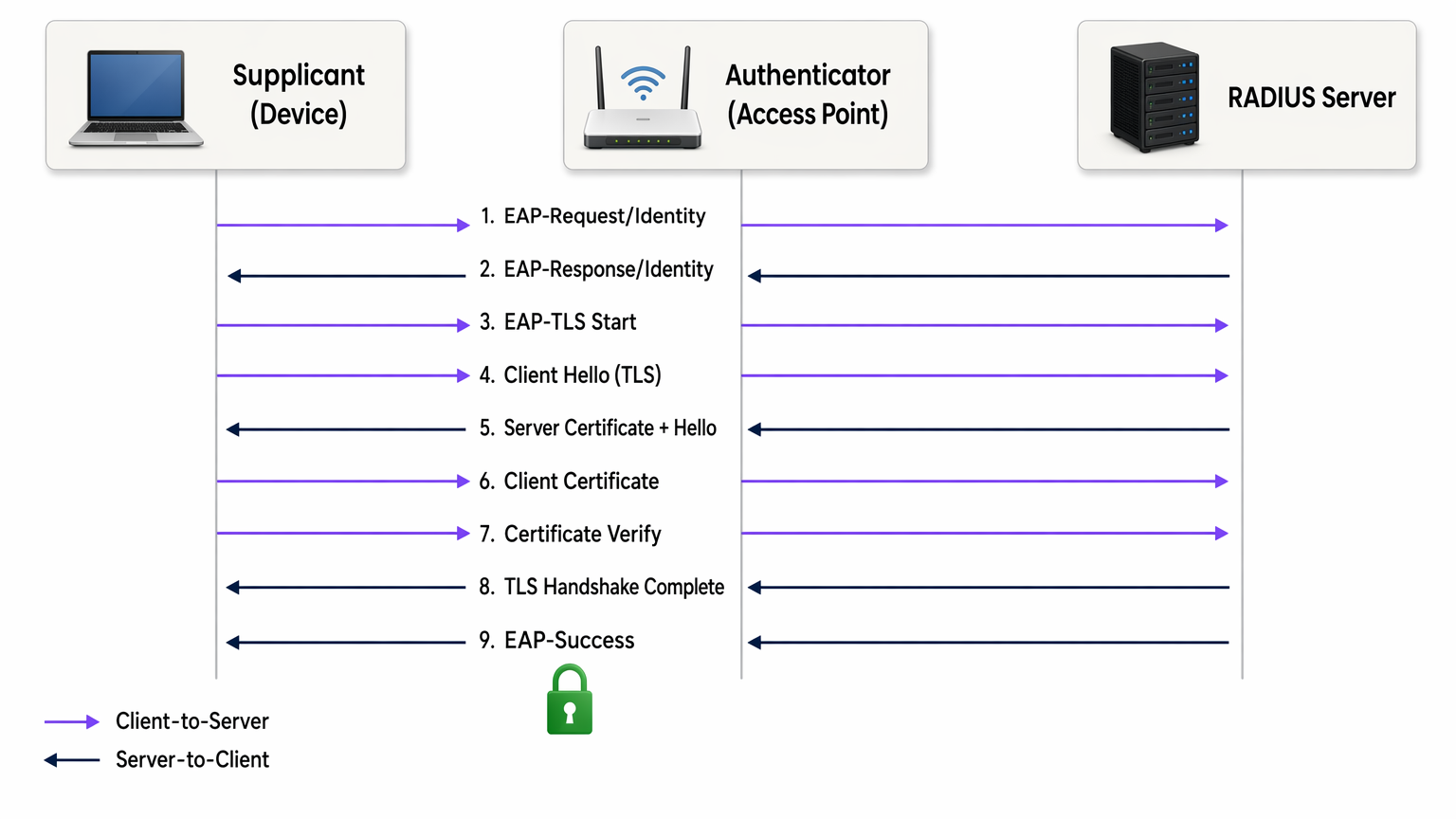
The EAP-TLS handshake proceeds as follows:
- The access point sends an EAP-Request/Identity to the connecting device.
- The device responds with its identity (commonly an anonymous outer identity to protect the username from eavesdropping).
- The RADIUS server initiates the TLS handshake with an EAP-TLS/Start message.
- The client sends a ClientHello, advertising its supported TLS cipher suites.
- The RADIUS server responds with ServerHello, its X.509 server certificate, and a certificate request.
- The client validates the server certificate against its trusted root CA store. If validation fails, the handshake terminates — protecting against rogue access points.
- The client presents its own X.509 client certificate.
- The RADIUS server validates the client certificate: it checks the signature chain back to the trusted root CA, verifies the certificate has not expired, and checks the Certificate Revocation List (CRL) or queries the OCSP responder to confirm the certificate has not been revoked.
- Both sides derive session keys from the TLS master secret. The RADIUS server sends an EAP-Success and the access point opens the controlled port.
The entire exchange takes place before the device is granted any network access. There is no password transmitted at any point. The session keys derived are unique per-session, providing perfect forward secrecy when using ECDHE cipher suites — meaning historical traffic cannot be decrypted even if a certificate is later compromised.
X.509 Certificates and PKI Architecture
The security of EAP-TLS is entirely dependent on the integrity of the underlying PKI. A typical enterprise PKI for EAP-TLS consists of three tiers:
| Tier | Component | Role |
|---|---|---|
| Root CA | Offline root certificate authority | Signs intermediate CA certificates; kept air-gapped |
| Intermediate CA | Online issuing CA | Issues server and client certificates; handles CRL publication |
| End Entities | RADIUS server cert + client certs | Used in the live authentication handshake |
The root CA should be kept offline and air-gapped. Its private key, if compromised, invalidates your entire certificate hierarchy. The intermediate CA handles day-to-day issuance and publishes the CRL. Client certificates are issued to individual devices (not users), typically with a Subject Alternative Name (SAN) containing the device's MAC address or a device identifier from your MDM.
EAP-TLS vs. Other 802.1X Methods

The table above illustrates why EAP-TLS is the recommended choice for regulated environments. PEAP-MSCHAPv2, still the most widely deployed 802.1X method, has known vulnerabilities: the server certificate is frequently not validated by clients (a misconfiguration that enables rogue AP attacks), and MSCHAPv2 itself has been cryptographically broken since 2012. EAP-TLS eliminates both attack surfaces.
WPA2 Enterprise and WPA3 Enterprise
EAP-TLS operates identically over both WPA2 Enterprise (IEEE 802.11i) and WPA3 Enterprise (IEEE 802.11ax). The distinction is in the cipher suite negotiated for the wireless data encryption layer. WPA3 Enterprise mandates Protected Management Frames (PMF) and offers an optional 192-bit security mode (Suite B) which requires EAP-TLS with specific elliptic curve cipher suites (ECDHE + ECDSA or RSA-3072). For most enterprise deployments, WPA3 Enterprise with EAP-TLS and standard AES-256 cipher suites is the appropriate target state.
Implementation Guide
Phase 1: PKI Design and Deployment
Before configuring a single access point, the PKI must be in place. For organisations without an existing internal CA, Microsoft Active Directory Certificate Services (AD CS) is the most common choice in Windows environments. For cross-platform or cloud-native deployments, HashiCorp Vault PKI, EJBCA, or a managed PKI service such as AWS Private CA are viable alternatives.
Key decisions at this stage:
- Certificate validity period: Client certificates of 1–2 years balance security and operational overhead. Shorter periods increase revocation events; longer periods increase the window of exposure for a compromised certificate.
- Key algorithm: RSA-2048 remains widely supported. ECDSA P-256 offers equivalent security with smaller certificate sizes and faster handshakes — recommended for new deployments.
- CRL vs. OCSP: CRL distribution is simpler to implement but introduces latency and caching issues. OCSP provides real-time revocation status. For high-security environments, OCSP stapling on the RADIUS server is the preferred approach.
Phase 2: RADIUS Server Configuration
Your RADIUS server must be configured to:
- Present its server certificate (issued by your internal CA) to connecting clients.
- Trust only your internal root and intermediate CAs for client certificate validation — do not trust public CAs for client authentication.
- Perform CRL or OCSP checks on every client certificate presented.
- Map certificate attributes (Common Name, SAN, or OID extensions) to network policy rules — for example, assigning devices to specific VLANs based on certificate attributes.
For a detailed walkthrough of RADIUS server architecture and configuration, refer to What Is RADIUS? How RADIUS Servers Secure WiFi Networks .
Phase 3: Certificate Distribution via MDM/SCEP
Manual certificate installation does not scale. For any deployment beyond a handful of devices, certificate provisioning must be automated. The standard approach is:
- Managed corporate devices: Integrate your PKI with your MDM platform (Microsoft Intune, Jamf, VMware Workspace ONE). Configure a SCEP or EST profile that automatically requests and installs a client certificate when a device enrols. The certificate is bound to the device's TPM or Secure Enclave where supported, preventing certificate export.
- BYOD and contractor devices: Deploy an onboarding portal (such as Cisco ISE's Guest portal or a dedicated BYOD solution) that walks the user through a one-time certificate installation process. Issue certificates with shorter validity periods and restrict network access via VLAN policy.
- IoT and headless devices: Use SCEP with pre-shared challenge passwords or EST with bootstrap credentials. Certificate renewal should be automated via the same protocol before expiry.
Phase 4: Access Point and SSID Configuration
Configure the corporate SSID with:
- Security: WPA2 Enterprise or WPA3 Enterprise (802.1X)
- EAP type: EAP-TLS
- RADIUS server: Point to your authentication server with shared secret
- VLAN assignment: Enable dynamic VLAN assignment via RADIUS attributes (Tunnel-Type, Tunnel-Medium-Type, Tunnel-Private-Group-ID)
- PMF: Mandatory for WPA3; strongly recommended for WPA2
Phase 5: Client Supplicant Configuration
For Windows devices managed via Group Policy or Intune, deploy a Wired/Wireless Network Policy that specifies EAP-TLS, the trusted root CA, and the certificate selection criteria. On macOS and iOS, deploy a configuration profile. On Android, use the MDM-managed WiFi profile. Critically, enforce server certificate validation — specify the exact CA and server name. Leaving this unchecked is the single most common misconfiguration in 802.1X deployments.
Best Practices
Enforce server certificate validation on all supplicants. The most exploitable misconfiguration in 802.1X deployments is clients that accept any server certificate, enabling rogue access point attacks. Every MDM-deployed WiFi profile should specify the trusted CA and the expected server name (CN or SAN).
Automate certificate renewal before expiry. Set up monitoring to alert when certificates are within 30 days of expiry. Configure SCEP or EST auto-renewal so devices renew certificates without user intervention. A mass certificate expiry event is one of the most disruptive incidents an enterprise network team can face.
Implement OCSP over CRL where possible. CRL files can grow large and are cached by clients, meaning a recently revoked certificate may still be accepted until the cache expires. OCSP provides real-time status and is the preferred revocation mechanism for high-security environments.
Segment your PKI. Use separate intermediate CAs for different certificate classes: one for RADIUS server certificates, one for client device certificates, one for user certificates. This limits the blast radius of a CA compromise and simplifies revocation policy.
Log and monitor authentication events. Your RADIUS server generates an authentication log for every connection attempt. Feed these logs into your SIEM. Patterns such as repeated authentication failures, certificate validation errors, or connections from unexpected MAC addresses are early indicators of misconfiguration or attack.
Align with PCI DSS 4.0. Requirement 8.6 mandates strong authentication for system components. For wireless networks in scope for PCI DSS, EAP-TLS with certificate-based authentication satisfies the requirement for multi-factor authentication at the network layer, as the certificate (something you have) combined with the device's TPM-bound private key (something you are) constitutes two factors.
Troubleshooting & Risk Mitigation
Common Failure Modes
| Failure Mode | Symptom | Root Cause | Resolution |
|---|---|---|---|
| Certificate chain validation failure | EAP-Failure after server cert exchange | Client does not trust the RADIUS server's CA | Push root CA certificate to device trust store via MDM |
| Client cert not presented | Authentication stops after server cert | No client cert installed or wrong cert selected | Verify SCEP enrollment completed; check MDM profile |
| OCSP/CRL unreachable | Intermittent auth failures | RADIUS server cannot reach revocation endpoint | Ensure OCSP/CRL URLs are accessible from RADIUS server; implement local CRL caching |
| Certificate expired | All devices fail authentication simultaneously | Renewal automation not configured | Implement 30-day expiry alerts; configure SCEP auto-renewal |
| Rogue AP attack | Users connect to malicious AP | Server cert validation disabled on supplicant | Enforce server cert validation in all MDM WiFi profiles |
| VLAN assignment failure | Device connects but gets wrong network segment | RADIUS attributes misconfigured | Verify Tunnel-Type (13=VLAN), Tunnel-Medium-Type (6=802), Tunnel-Private-Group-ID (VLAN ID) |
Risk Mitigation for Large-Scale Deployments
For hospitality environments with hundreds of access points across multiple properties, and for retail chains with distributed sites, the primary operational risk is a synchronised certificate expiry event. Stagger certificate issuance dates across device groups so that renewals are distributed over time rather than occurring simultaneously. Maintain a certificate inventory in your MDM and run weekly reports on certificates expiring within 60 days.
For healthcare environments, the additional risk is authentication latency impacting clinical workflows. Optimise your RADIUS server placement to minimise round-trip time. Consider deploying RADIUS proxy servers at each site to reduce WAN dependency for authentication.
ROI & Business Impact
Quantifying the Security Investment
The business case for EAP-TLS over password-based 802.1X is straightforward when framed against breach costs. The average cost of a data breach in the UK in 2024 was £3.58 million (IBM Cost of a Data Breach Report). A significant proportion of enterprise breaches originate from compromised credentials. EAP-TLS eliminates the credential theft vector for network access entirely.
For organisations subject to PCI DSS, a wireless network breach resulting in cardholder data exposure carries fines, forensic investigation costs, and potential card scheme penalties that dwarf the cost of a PKI deployment. The compliance alignment alone justifies the investment for any organisation processing card payments over wireless infrastructure.
Operational Efficiency Gains
Counter-intuitively, a well-implemented EAP-TLS deployment with MDM-integrated certificate provisioning can reduce helpdesk load compared to password-based 802.1X. Password resets, shared credential management, and "why can't I connect to WiFi" tickets are eliminated. The initial deployment effort is front-loaded, but steady-state operations are lower-touch.
For venue operators deploying WiFi Analytics alongside secure staff networks, the segmentation enabled by EAP-TLS and dynamic VLAN assignment means guest traffic, staff traffic, and IoT device traffic can be cleanly separated on the same physical infrastructure — reducing hardware costs while improving security posture.
Purple's Role in Secure Enterprise WiFi
Purple's platform operates at the intersection of Guest WiFi and enterprise network intelligence. For staff and corporate device networks, EAP-TLS provides the authentication layer. Purple's WiFi Analytics platform sits above this, providing visibility into network usage patterns, device dwell times, and venue footfall — data that is only meaningful when the underlying network is properly segmented and authenticated.
For organisations exploring OpenRoaming and Passpoint-based seamless connectivity across venues, Purple acts as a free identity provider under the Connect licence, leveraging the same 802.1X and certificate-based identity frameworks that underpin EAP-TLS. This positions EAP-TLS not just as a security control, but as the foundation for advanced connectivity services across transport hubs, retail estates, and hospitality venues.
For network architects evaluating how SD-WAN and enterprise WiFi security intersect, The Core SD-WAN Benefits for Modern Businesses provides complementary context on how secure authentication integrates with modern WAN architectures.
Key Terms & Definitions
EAP-TLS (Extensible Authentication Protocol – Transport Layer Security)
An 802.1X authentication method defined in RFC 5216 that uses mutual X.509 certificate authentication between the client device and the RADIUS server. Neither side gains network access without presenting a valid, non-revoked certificate signed by a trusted Certificate Authority.
IT teams encounter EAP-TLS when evaluating 802.1X authentication methods for WPA2 Enterprise or WPA3 Enterprise deployments. It is the recommended method for regulated environments (PCI DSS, HIPAA, ISO 27001) and the required method for WPA3 Enterprise 192-bit (Suite B).
X.509 Certificate
A digital certificate standard (defined in ITU-T X.509 and RFC 5280) that binds a public key to an identity (device, server, or user). It contains the subject's identity, the public key, the issuing CA's digital signature, and validity dates. In EAP-TLS, both the RADIUS server and the client device present X.509 certificates during the authentication handshake.
IT teams encounter X.509 certificates when configuring RADIUS servers (server certificate), enrolling devices via MDM (client certificate), and managing PKI infrastructure. Certificate expiry and revocation are the primary operational concerns.
PKI (Public Key Infrastructure)
The combination of hardware, software, policies, and procedures required to create, manage, distribute, store, and revoke digital certificates. In an EAP-TLS deployment, the PKI consists of at minimum a root CA and an issuing CA, plus the CRL/OCSP infrastructure for revocation.
PKI is the foundational dependency for any EAP-TLS deployment. IT teams must design and operate a PKI before EAP-TLS can be deployed. Common PKI platforms include Microsoft AD CS, EJBCA, HashiCorp Vault PKI, and managed services such as AWS Private CA.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol (RFC 2865) providing centralised authentication, authorisation, and accounting (AAA) for network access. In 802.1X/EAP-TLS deployments, the RADIUS server validates client certificates, enforces network policy, and returns VLAN assignment attributes to the access point.
RADIUS is the authentication server component in every 802.1X deployment. Common implementations include Microsoft NPS, FreeRADIUS, Cisco ISE, and Aruba ClearPass. The RADIUS server must be configured to trust the internal CA and perform certificate revocation checks.
Mutual Authentication
An authentication process in which both communicating parties verify each other's identity before establishing a connection. In EAP-TLS, the client validates the RADIUS server's certificate (protecting against rogue APs) and the RADIUS server validates the client's certificate (protecting against unauthorised device access).
Mutual authentication is the key differentiator of EAP-TLS over PEAP and EAP-TTLS. IT teams should emphasise mutual authentication when justifying EAP-TLS to security auditors and compliance teams, as it directly addresses the rogue AP and credential theft threat vectors.
SCEP (Simple Certificate Enrollment Protocol)
A protocol (originally defined by Cisco, standardised in RFC 8894) that enables automated certificate requests and issuance between a client device and a Certificate Authority. In EAP-TLS deployments, SCEP is used by MDM platforms to automatically provision client certificates to managed devices without user intervention.
SCEP is the standard mechanism for zero-touch certificate provisioning in enterprise MDM environments. IT teams configure SCEP profiles in Intune, Jamf, or Workspace ONE to automate client certificate deployment and renewal.
CRL (Certificate Revocation List)
A periodically published list of certificate serial numbers that have been revoked by the issuing CA before their expiry date. RADIUS servers check the CRL to ensure a client certificate presented during EAP-TLS authentication has not been revoked (e.g., due to device theft or employee departure).
CRL management is a critical operational consideration in EAP-TLS deployments. IT teams must ensure the CRL distribution point is accessible from RADIUS servers, that CRLs are published frequently enough to reflect recent revocations, and that RADIUS servers are configured to reject authentication if the CRL cannot be retrieved.
OCSP (Online Certificate Status Protocol)
A real-time certificate revocation checking protocol (RFC 6960) that allows a RADIUS server to query the CA's OCSP responder for the current status of a specific certificate, rather than downloading and parsing a full CRL. OCSP provides lower latency and more current revocation information than CRL-based checking.
IT teams should prefer OCSP over CRL for high-security environments where real-time revocation is important (e.g., immediately revoking a certificate when a device is reported stolen). OCSP stapling, where the RADIUS server caches and presents the OCSP response, reduces latency and eliminates dependency on the OCSP responder being reachable during every authentication.
802.1X (Port-Based Network Access Control)
An IEEE standard that provides an authentication framework for devices attempting to connect to a LAN or WLAN. It defines three roles: supplicant (the connecting device), authenticator (the access point or switch), and authentication server (RADIUS). EAP-TLS is one of several EAP methods that can be used within the 802.1X framework.
802.1X is the overarching framework within which EAP-TLS operates. IT teams encounter 802.1X when configuring WPA2 Enterprise or WPA3 Enterprise SSIDs, and when configuring wired port authentication on managed switches. Understanding 802.1X is a prerequisite for deploying EAP-TLS.
Perfect Forward Secrecy (PFS)
A cryptographic property of key exchange protocols that ensures session keys cannot be derived from the long-term private key. In EAP-TLS with ECDHE cipher suites, each session generates a unique ephemeral key pair, meaning that compromise of the certificate's private key does not expose historical session traffic.
IT teams should specify ECDHE-based cipher suites when configuring EAP-TLS to ensure PFS. This is particularly important in environments where network traffic is recorded and could be subject to future decryption attempts (a 'harvest now, decrypt later' attack scenario).
Case Studies
A 450-room hotel group with 12 properties needs to migrate its staff WiFi from PEAP-MSCHAPv2 to EAP-TLS. The group runs Windows 10/11 laptops managed via Microsoft Intune, plus approximately 200 Android tablets used by housekeeping staff. The IT team has no existing internal PKI. What is the recommended deployment approach?
Step 1 — PKI Deployment (Weeks 1–3): Deploy Microsoft AD CS with a two-tier hierarchy. Stand up an offline root CA on a dedicated server that will be powered down after initial setup. Deploy an online issuing CA (intermediate CA) on a Windows Server VM. Configure the issuing CA to publish CRLs to an internal web server accessible from all RADIUS servers across the 12 properties. Enable the OCSP responder role on the issuing CA server.
Step 2 — RADIUS Infrastructure (Weeks 2–4): Deploy Microsoft NPS (Network Policy Server) at each property, or centralise with NPS proxy servers at each site pointing to a central NPS cluster. Issue a RADIUS server certificate from the internal CA to each NPS instance. Configure NPS network policy: authentication method = EAP-TLS, trusted root CA = internal root CA, certificate validation = enabled, VLAN assignment via RADIUS attributes.
Step 3 — Intune Certificate Profiles (Weeks 3–5): In Microsoft Intune, create a Trusted Certificate profile to push the root CA certificate to all managed devices. Create a SCEP Certificate profile targeting the issuing CA, with subject name format CN={{DeviceId}}, key usage = Digital Signature, extended key usage = Client Authentication. Create a WiFi profile specifying EAP-TLS, the SCEP certificate profile as the client certificate, and the root CA as the trusted server certificate authority.
Step 4 — Android Tablet Enrolment (Weeks 4–6): Enrol Android tablets into Intune via Android Enterprise (Dedicated Device mode). Deploy equivalent Trusted Certificate, SCEP Certificate, and WiFi configuration profiles. Verify certificate installation on a pilot group of 10 tablets before full rollout.
Step 5 — Pilot and Cutover (Weeks 6–8): Run EAP-TLS in parallel with PEAP on a separate SSID at one pilot property. Validate authentication success rates, VLAN assignment, and certificate renewal behaviour. Roll out property by property. Decommission PEAP SSID after 30-day parallel run at each site.
A national retail chain with 280 stores needs to secure its point-of-sale WiFi network to meet PCI DSS 4.0 requirements. Each store has 8–15 Windows-based POS terminals, a mix of managed and unmanaged devices, and a single IT administrator who manages all stores remotely. The chain currently uses a shared WPA2-PSK password across all stores. What is the migration path to EAP-TLS?
Assessment and Scoping: First, define the PCI DSS cardholder data environment (CDE) scope. POS terminals processing card data are in scope; staff break-room devices are not. Segment the network so that only POS terminals are on the EAP-TLS secured SSID. This limits the certificate deployment scope to a known, managed device population.
Centralised PKI and RADIUS: Deploy a cloud-hosted RADIUS service (e.g., Cisco ISE in the cloud, or JumpCloud RADIUS) to eliminate the need for on-premise RADIUS hardware at each store. This is critical for a distributed retail estate where local server management is not feasible. The cloud RADIUS service connects to the internal PKI via a secure tunnel.
MDM-Driven Certificate Deployment: All POS terminals must be enrolled in an MDM (Microsoft Intune or equivalent). Deploy the root CA trust anchor and SCEP certificate profile via MDM policy. The certificate subject should include the store number and terminal ID (e.g., CN=POS-STORE042-TERM003) to enable granular RADIUS policy and audit logging.
SSID Configuration: Configure a dedicated POS SSID at each store access point with WPA2 Enterprise / EAP-TLS. Use dynamic VLAN assignment to place authenticated POS terminals on the CDE VLAN. Implement a separate guest SSID on a completely isolated VLAN for customer WiFi.
Monitoring and Compliance Evidence: Configure RADIUS authentication logs to be forwarded to a central SIEM. Generate monthly reports showing authentication success rates, certificate validity status, and any revocation events. This log data constitutes audit evidence for PCI DSS Requirement 10 (logging and monitoring) and Requirement 8.6 (authentication management).
Scenario Analysis
Q1. Your organisation runs a 600-bed hospital with 1,200 managed Windows laptops and 400 shared Android tablets used by nursing staff. The current WiFi uses PEAP-MSCHAPv2 with Active Directory credentials. A recent penetration test identified that none of the client devices validate the RADIUS server certificate, and the tester successfully performed a rogue AP attack capturing AD credentials. You have been asked to remediate this within 90 days. What is your prioritised remediation plan?
💡 Hint:Consider what can be fixed immediately (configuration change) versus what requires infrastructure work (PKI deployment). Not all remediation steps require EAP-TLS — some can be applied to the existing PEAP deployment while the longer-term migration is planned.
Show Recommended Approach
Immediate (Week 1–2): Fix server certificate validation on existing PEAP deployment. Push a GPO/Intune WiFi profile update to all managed Windows devices that specifies the trusted root CA and the RADIUS server's expected CN/SAN. This immediately closes the rogue AP vulnerability without requiring PKI changes. For Android tablets, push an updated MDM WiFi profile. This addresses the critical finding within days.
Short-term (Weeks 2–8): Deploy internal PKI. Stand up a two-tier AD CS PKI (offline root CA + online issuing CA). Issue a new RADIUS server certificate from the internal CA. Update the NPS configuration. Push the new root CA trust anchor to all devices via MDM.
Medium-term (Weeks 6–12): Migrate to EAP-TLS for managed devices. Configure SCEP profiles in Intune for Windows laptops. Deploy client certificate profiles. Create a new EAP-TLS SSID in parallel with the existing PEAP SSID. Pilot with 50 laptops, validate, then roll out in waves. Shared Android tablets are more complex — evaluate whether Android Enterprise Dedicated Device enrolment is feasible, or whether a certificate-based onboarding portal is more appropriate for shared-use devices.
Key consideration: HIPAA requires appropriate safeguards for wireless networks carrying ePHI. The rogue AP vulnerability is a reportable risk. Document the remediation timeline and interim controls for your compliance officer.
Q2. A conference centre is deploying a new WiFi infrastructure to support both a secure staff network (EAP-TLS) and a guest WiFi network. The venue hosts events for up to 5,000 attendees. The IT manager wants to use the same physical access point infrastructure for both networks. How should the network be architected to achieve this, and what are the key configuration decisions?
💡 Hint:Consider SSID segmentation, VLAN design, and the different authentication requirements for staff (certificate-based) versus guests (captive portal or social login). Think about how Purple's guest WiFi platform integrates with this architecture.
Show Recommended Approach
SSID and VLAN Design: Deploy two SSIDs on the same physical access point infrastructure. SSID 1 (Staff): WPA3 Enterprise / EAP-TLS, broadcasting on 5GHz and 6GHz bands, mapped to Staff VLAN (e.g., VLAN 10). SSID 2 (Guest): WPA3 Personal or Open with OWE (Opportunistic Wireless Encryption), mapped to Guest VLAN (e.g., VLAN 20). The Guest VLAN should have no access to the Staff VLAN or internal infrastructure — only internet access.
Staff Network: Configure RADIUS server with EAP-TLS policy. Issue client certificates to all staff devices via MDM. Use dynamic VLAN assignment to place authenticated staff devices on VLAN 10. Consider deploying a separate SSID for AV/event management equipment on VLAN 30 with EAP-TLS and a separate certificate policy.
Guest Network: Integrate with Purple's Guest WiFi platform for captive portal authentication, social login, or email capture. The guest network operates entirely independently of the EAP-TLS infrastructure. Purple's WiFi Analytics platform provides dwell time, footfall, and engagement data from the guest network.
Capacity Planning: For 5,000 concurrent guests, ensure the guest VLAN's DHCP scope, internet uplink, and access point density are sized appropriately. EAP-TLS authentication adds negligible overhead per-connection but RADIUS server capacity should be validated for peak event load.
Q3. A retail CTO is evaluating whether to deploy EAP-TLS for 350 stores or to continue with WPA2-PSK with a rotated shared key. The IT team is small (3 people) and has no PKI experience. The CTO's primary concern is PCI DSS compliance for the POS network. What is your recommendation, and how do you frame the business case?
💡 Hint:Consider the PCI DSS requirements, the operational capacity of a small IT team, and whether there are managed service options that reduce the PKI burden. The answer is not necessarily 'deploy full EAP-TLS immediately' — a phased or managed approach may be more appropriate.
Show Recommended Approach
Recommendation: EAP-TLS via a managed RADIUS and PKI service, phased over 6 months.
WPA2-PSK is not acceptable for a PCI DSS cardholder data environment. PCI DSS Requirement 8 mandates individual authentication for system components, and a shared PSK does not satisfy this. A breach of the PSK exposes all 350 stores simultaneously. The risk is not theoretical — POS network breaches via compromised WiFi credentials are a documented attack vector in retail.
Managed Service Approach: Rather than building internal PKI expertise, engage a managed RADIUS and PKI provider (e.g., Foxpass, JumpCloud, or SecureW2). These services provide a hosted RADIUS server, a managed CA, and MDM integration out of the box. The IT team configures MDM certificate profiles and access point RADIUS settings — no PKI expertise required. Cost is typically $3–8 per device per month, which is trivial against the cost of a PCI DSS breach.
Business Case: Frame the investment against three cost categories: (1) PCI DSS non-compliance fines and forensic investigation costs following a breach — typically £50k–£500k for a mid-size retailer; (2) card scheme penalties for a cardholder data breach — potentially millions; (3) reputational damage and customer churn. The managed service cost for 350 stores with 15 POS terminals each (5,250 devices) at $5/device/month is approximately $26,250/month — less than the daily cost of a breach investigation.



