What is IPSK? Identity Pre-Shared Keys Explained
This comprehensive technical guide explains Identity Pre-Shared Keys (IPSK/DPSK), detailing how it provides enterprise-grade security and dynamic VLAN steering for multi-dwelling units (MDUs) and student accommodation without the friction of 802.1X.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: What is IPSK and How Does It Work?
- The Architectural Problem with Shared PSKs
- The IPSK Solution
- Comparison: WPA2-Personal vs. IPSK vs. 802.1X
- Implementation Guide: Deploying IPSK in MDU Environments
- 1. Key Generation and Entropy
- 2. Device Limit Enforcement
- 3. Dynamic VLAN Steering Configuration
- 4. Integration with Property Management Systems (PMS)
- Best Practices & Industry Standards
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact
Listen to our senior solutions architect break down IPSK architecture in this 10-minute briefing:
Executive Summary
For property managers and IT directors operating Multi-Dwelling Units (MDUs), particularly in student accommodation, managing wireless access presents a unique challenge. You must balance the consumer-grade onboarding experience residents expect with the enterprise-grade security, accountability, and network segmentation that compliance mandates.
Standard WPA2-Personal (a single shared password) fails to provide user accountability or dynamic network segmentation. Conversely, enterprise 802.1X (RADIUS) provides excellent security but introduces significant friction for onboarding headless devices like gaming consoles, smart TVs, and IoT hardware common in residential environments.
Identity Pre-Shared Keys (IPSK), also known as Dynamic PSK (DPSK), bridges this gap. It provides the seamless onboarding of WPA2-Personal while delivering the per-user accountability, dynamic VLAN steering, and granular lifecycle management typically reserved for 802.1X architectures. This guide details the technical mechanics of IPSK, deployment strategies, and why it is the definitive architecture for modern MDU and student accommodation networks.
Technical Deep-Dive: What is IPSK and How Does It Work?
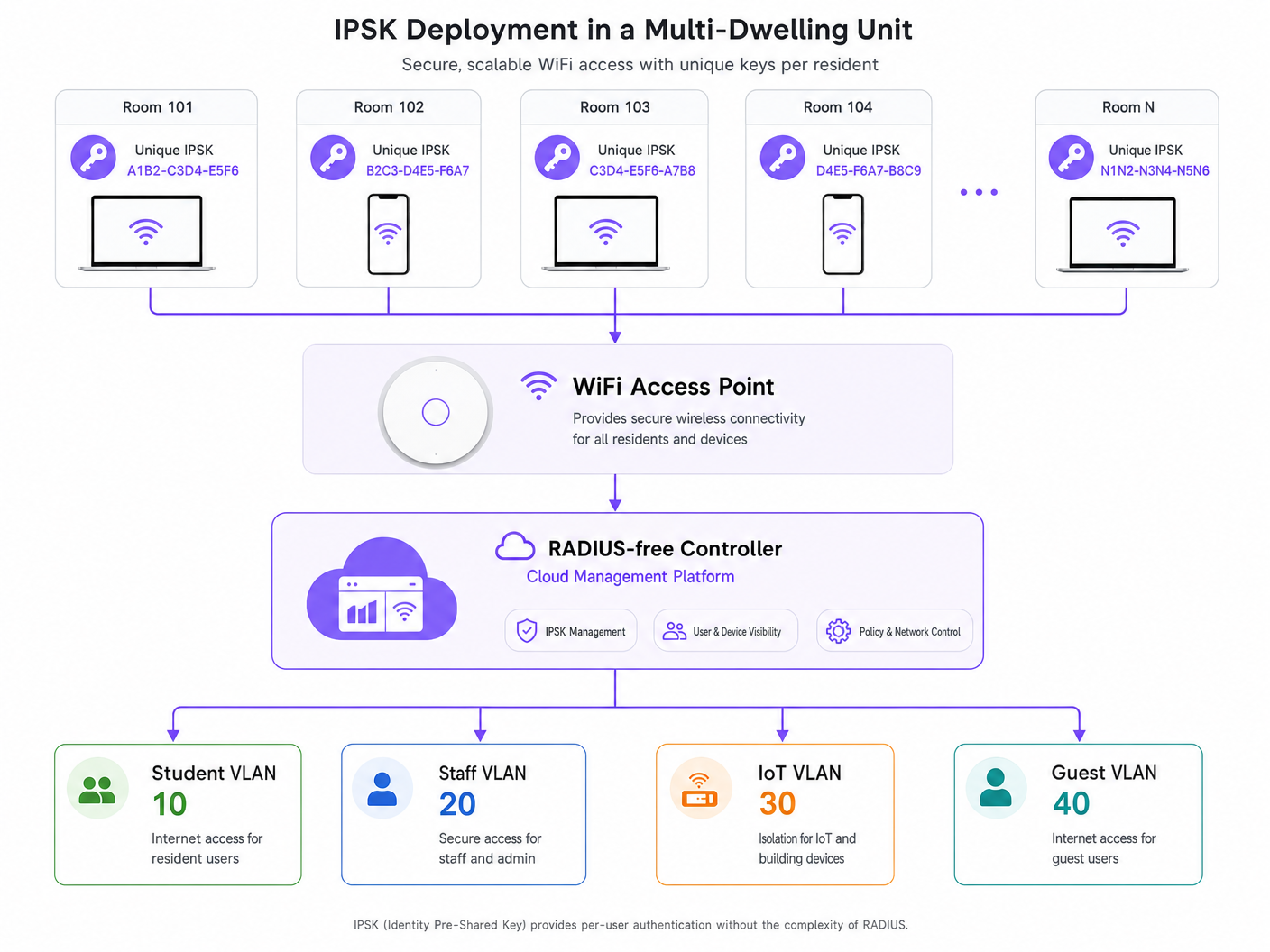
At its core, IPSK is an authentication mechanism that allows a single Service Set Identifier (SSID) to support multiple, unique Pre-Shared Keys (PSKs), where each key is tied to a specific identity (a user, a room, or a device group) at the controller level.
The Architectural Problem with Shared PSKs
In a traditional WPA2-Personal deployment, all clients connecting to the SSID utilize the same passphrase. This creates several architectural vulnerabilities:
- Lack of Identity Context: The network cannot distinguish between Resident A's traffic and Resident B's traffic at the authentication layer.
- Zero Network Segmentation: All devices land in the same broadcast domain (VLAN) unless complex MAC-based overrides are implemented.
- Broken Lifecycle Management: Revoking access for a single compromised device or a departing resident requires changing the global PSK, forcing a disruptive network-wide reconnection event for all users.
The IPSK Solution
IPSK shifts the intelligence from the edge device to the wireless controller or cloud management platform.
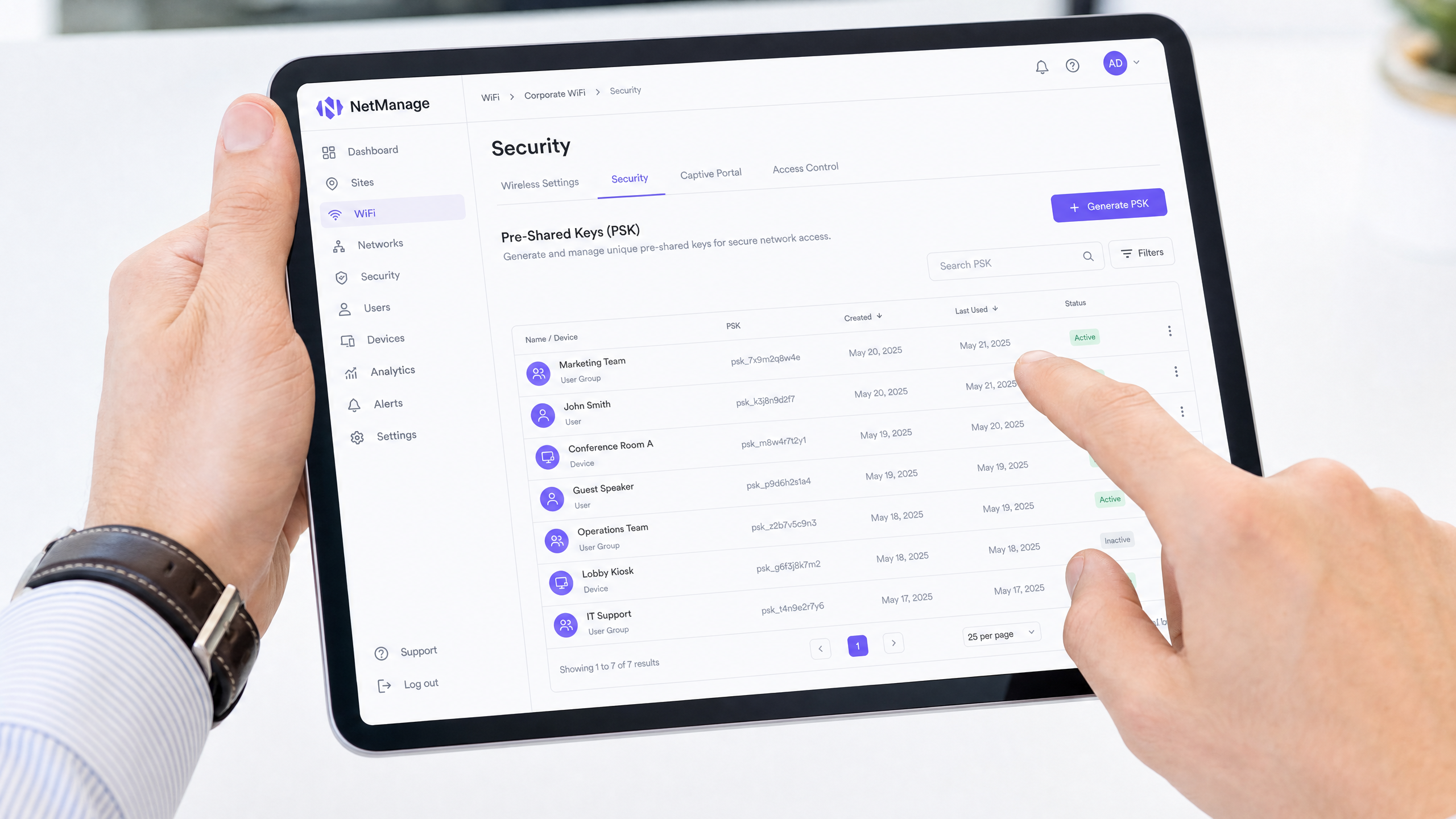
When a device associates with the SSID, it presents its assigned PSK. The access point forwards this request to the controller. The controller queries its internal database (or an external identity provider via API) to validate the key. Upon successful validation, the controller returns the authorization profile associated with that specific key.
This authorization profile typically dictates:
- VLAN Assignment: Dynamically steering the device into a specific network segment (e.g., VLAN 10 for Room 101, VLAN 20 for Room 102).
- Role-Based Access Control (RBAC): Applying specific firewall rules or Access Control Lists (ACLs).
- Rate Limiting: Enforcing bandwidth caps per user or per room.
Because the key is unique to the user, you achieve identity-based networking without requiring 802.1X supplicants on the client devices.
Comparison: WPA2-Personal vs. IPSK vs. 802.1X
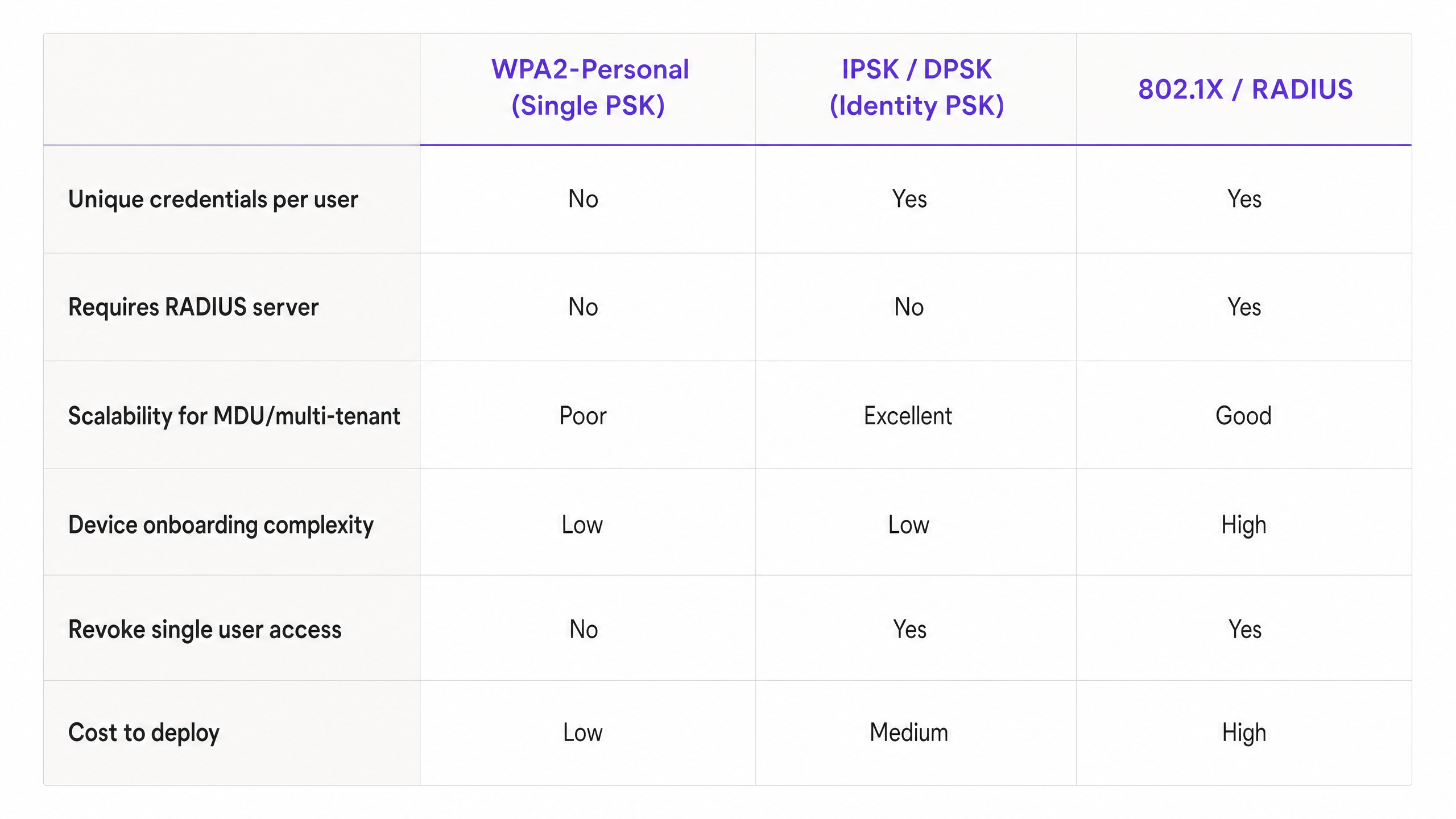
Understanding where IPSK fits requires comparing it against the alternatives. While 802.1X remains the gold standard for corporate carpeted office spaces (see our guide on Office Wi Fi: Optimize Your Modern Office Wi-Fi Network ), it is often inappropriate for MDUs due to device compatibility issues. IPSK delivers the security benefits of 802.1X with the simplicity of WPA2-Personal.
Implementation Guide: Deploying IPSK in MDU Environments
Deploying IPSK effectively requires careful planning around key generation, distribution, and lifecycle management.
1. Key Generation and Entropy
Keys must be cryptographically secure. Avoid using sequential numbers, room numbers, or easily guessable phrases. Generate keys programmatically (minimum 16-20 characters, alphanumeric). If you are utilizing a platform like Purple's Guest WiFi solution, this generation can be automated and tied to the resident's profile.
2. Device Limit Enforcement
A critical implementation step is enforcing a Maximum Device Count per IPSK. If a resident is assigned a key, they should be restricted to a reasonable number of concurrent authentications (e.g., 5 to 8 devices). Failing to enforce this allows a single leaked key to be used by dozens of unauthorized users, degrading network performance and compromising the audit trail.
3. Dynamic VLAN Steering Configuration
Configure your wireless controller to map specific IPSKs to specific VLANs. In a student accommodation setting, the architecture typically looks like this:
- Resident VLANs: Either a unique VLAN per room (micro-segmentation) or a shared resident VLAN with client isolation enabled.
- IoT VLAN: For building management, smart thermostats, and BLE beacons (read more on BLE Low Energy Explained for Enterprise ).
- Staff/Admin VLAN: Secure access for property management.
This approach is detailed further in our comprehensive guide: Designing a Multi-Tenant WiFi Architecture for MDU .
4. Integration with Property Management Systems (PMS)
The true ROI of IPSK is realized when the key lifecycle is automated. Integrate your wireless controller's API with your PMS or tenancy database.
- Provisioning: When a lease is signed, an API call automatically generates an IPSK and emails it to the resident.
- Revocation: When the lease terminates, an API call instantly revokes the key, terminating network access without IT intervention.
Best Practices & Industry Standards
- WPA3 Transition: Ensure your hardware supports WPA3-SAE (Simultaneous Authentication of Equals). WPA3 significantly enhances the security of pre-shared keys by mitigating offline dictionary attacks and providing forward secrecy. Modern IPSK deployments should leverage WPA3 wherever client compatibility allows.
- Client Isolation: If you are placing multiple residents into a shared VLAN rather than per-room VLANs, you MUST enable Client Isolation (Layer 2 isolation) at the AP level to prevent lateral movement and peer-to-peer attacks between residents.
- Compliance: For operators in the Hospitality or MDU sectors, IPSK provides the necessary audit logs to comply with regulations like GDPR, as network flows can be directly attributed to a specific user's credential.
Troubleshooting & Risk Mitigation
Common Failure Modes
1. Controller Scale Limits Risk: Older or entry-level wireless controllers have hard limits on the number of unique PSKs they can store (e.g., max 500 keys per SSID). Mitigation: Verify the maximum supported IPSK scale of your hardware before deployment. For large MDUs, cloud-managed architectures (like Cisco Meraki or Aruba Central) or dedicated policy engines are required.
2. Roaming Latency Risk: If the controller database is slow to respond during AP-to-AP roaming events, voice and video calls will drop. Mitigation: Ensure the controller infrastructure is localized or highly available. Enable Fast BSS Transition (802.11r) if supported by your IPSK implementation.
3. Key Hoarding/Stale Keys Risk: Failing to revoke keys when residents leave results in a bloated database and a massive security vulnerability. Mitigation: Implement automated lifecycle management via API integration with your PMS. Conduct quarterly audits of active keys.
ROI & Business Impact
Transitioning to an IPSK architecture delivers measurable business outcomes for property managers and IT directors:
- Reduced Support Overhead: Eliminating 802.1X supplicant configuration issues and the need for MAC authentication bypass (MAB) for headless devices reduces Helpdesk tickets by up to 60% during the critical September onboarding window.
- Enhanced Monetization: By tying identity to network access, operators can offer tiered bandwidth packages (e.g., basic tier included in rent, premium tier for gamers).
- Actionable Analytics: With identity-aware networking, property managers can leverage WiFi Analytics to understand space utilization, common area dwell times, and overall building engagement, similar to deployments in Retail and Transport .
IPSK is not just a security feature; it is the foundational architecture that enables secure, scalable, and manageable multi-tenant networks.
Key Definitions
IPSK (Identity Pre-Shared Key)
An authentication method that allows multiple unique pre-shared keys to be used on a single SSID, with each key tied to a specific user policy or VLAN.
Used in MDUs to provide per-user security without the complexity of 802.1X.
DPSK (Dynamic Pre-Shared Key)
A vendor-specific (primarily Ruckus) term for the same underlying technology as IPSK.
You will encounter this term when evaluating different vendor data sheets.
Dynamic VLAN Steering
The process where a network controller automatically assigns a connecting device to a specific Virtual LAN based on the authentication credentials provided.
Essential for multi-tenant environments to isolate resident traffic from staff or IoT traffic on the same physical access points.
802.1X
The IEEE standard for port-based Network Access Control, requiring a RADIUS server and client supplicants.
The enterprise alternative to IPSK, but often unsuitable for residential environments due to headless device incompatibility.
Headless Device
A network-connected device lacking a web browser or advanced configuration interface (e.g., gaming consoles, smart TVs, IoT sensors).
These devices drive the requirement for IPSK, as they cannot navigate captive portals or configure 802.1X supplicants.
WPA3-SAE
Simultaneous Authentication of Equals, the secure key establishment protocol used in WPA3 to prevent offline dictionary attacks.
The modern security standard that should be paired with IPSK deployments on compatible hardware.
Client Isolation
A wireless network setting that prevents devices connected to the same AP from communicating directly with each other.
Mandatory security control if multiple residents are placed into a single shared VLAN.
MAC Authentication Bypass (MAB)
A fallback mechanism in 802.1X networks where a device's MAC address is used as its identity credential.
A cumbersome administrative process that IPSK eliminates by providing native PSK support for headless devices.
Worked Examples
A 400-bed student accommodation block currently uses a single WPA2-Personal password. Residents complain about poor performance, and IT cannot prevent departing students from continuing to use the network from the car park. They need to secure the network, segment traffic per room, and support gaming consoles without increasing helpdesk tickets.
Deploy an IPSK architecture on a single SSID. Integrate the wireless controller API with the property management system. Upon lease signing, generate a unique 20-character IPSK per resident. Configure the controller to dynamically steer each resident's key to a unique Per-Room VLAN. Set a device limit of 6 concurrent devices per key. Automate key revocation upon lease termination.
A boutique hotel wants to offer secure, segmented WiFi to guests but cannot rely on captive portals because guests increasingly travel with smart speakers and streaming sticks that cannot navigate web logins.
Implement IPSK tied to the hotel reservation system. When a guest checks in, the PMS triggers an API call to generate a unique IPSK valid only for the duration of their stay. The key is printed on the room key sleeve or sent via SMS. The network dynamically assigns their devices to a private VLAN for that specific room, allowing their phone to cast to the room's smart TV securely.
Practice Questions
Q1. You are designing the network for a 200-unit build-to-rent property. The client wants to use 802.1X for maximum security. However, their demographic research shows residents bring an average of 3 headless devices (smart TVs, consoles) per unit. What is your architectural recommendation?
Hint: Consider the operational overhead of onboarding 600 headless devices onto an 802.1X network.
View model answer
Recommend an IPSK architecture instead of 802.1X. While 802.1X provides excellent security, the 600 headless devices would require MAC Authentication Bypass (MAB), creating a massive administrative burden for the helpdesk. IPSK provides the necessary per-user accountability and VLAN segmentation while allowing headless devices to connect seamlessly using standard PSK methods.
Q2. During an IPSK deployment, the property manager requests that residents be allowed to choose their own custom WiFi passwords to improve the user experience. How do you respond?
Hint: Think about cryptographic entropy and dictionary attacks.
View model answer
Advise strongly against this. User-selected passwords lack sufficient entropy and are vulnerable to dictionary attacks. In an IPSK environment, weak keys compromise the security of the entire SSID. Keys must be programmatically generated (minimum 16-20 random alphanumeric characters) and distributed securely via the property management system integration.
Q3. A network utilizing IPSK is experiencing IP address exhaustion in the main DHCP pool, despite the building only being at 60% occupancy. What configuration oversight likely caused this?
Hint: Think about what happens if a key is shared freely.
View model answer
The network likely failed to enforce a Maximum Device Count per IPSK. Without a device limit, residents can share their unique key with non-residents or connect an unlimited number of devices, rapidly exhausting DHCP scopes and bandwidth. A strict concurrent device limit (e.g., 5-8 devices per key) must be enforced at the controller level.