Cómo construir una estrategia de experiencia del cliente
Esta guía de referencia técnica proporciona un marco práctico para líderes de TI, arquitectos de red y directores de operaciones de recintos sobre cómo construir una estrategia de experiencia del cliente basada en datos. Cubre la arquitectura completa, desde la autenticación de guest WiFi y el diseño del Captive Portal hasta el análisis espacial, la integración de CRM y un ROI medible, con escenarios de implementación concretos extraídos de entornos de hostelería, comercio minorista y sector público. La plataforma de guest WiFi y análisis de Purple se posiciona en todo momento como la capa de infraestructura habilitadora.
🎧 Escuchar esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectando la Base de Datos de CX
- Mecanismos de Autenticación y Captura de Datos
- Análisis de Ubicación y Seguimiento del Comportamiento
- Guía de Implementación: Desplegando la Estrategia
- Fase 1: Evaluación de la Infraestructura y Diseño de RF
- Fase 2: Configuración del Captive Portal e Integración con CRM
- Fase 3: Línea de base de análisis y segmentación de audiencia
- Fase 4: Activación y Personalización
- Mejores Prácticas para Implementaciones Empresariales
- Resolución de Problemas y Mitigación de Riesgos
- ROI e Impacto Empresarial

Resumen Ejecutivo
Para los líderes de TI empresariales y los directores de operaciones de recintos, construir una estrategia de experiencia del cliente (CX) ya no es únicamente dominio del marketing. A medida que los recintos físicos —desde cadenas minoristas hasta estadios a gran escala— se digitalizan cada vez más, la infraestructura de red subyacente es el motor principal para la adquisición de datos de clientes. Esta guía detalla cómo diseñar una estrategia de CX que aproveche la infraestructura inalámbrica existente para capturar inteligencia procesable, automatizar el compromiso y ofrecer un retorno de la inversión medible.
Al implementar una solución robusta de Guest WiFi , las organizaciones pueden transformar un centro de costes operativos en un activo estratégico. Una estrategia de CX exitosa se basa en la recopilación de datos sin interrupciones, el cumplimiento riguroso (incluyendo GDPR y PCI DSS) y la integración con las plataformas de CRM y automatización de marketing existentes. Este documento proporciona un marco técnico y neutral respecto al proveedor para diseñar, implementar y escalar una arquitectura de experiencia del cliente basada en datos en entornos de Hostelería , Comercio Minorista , Sanidad y Transporte .
Análisis Técnico Detallado: Arquitectando la Base de Datos de CX
La base de cualquier estrategia de CX moderna en un recinto físico es la capacidad de identificar y rastrear de forma fiable a los usuarios a lo largo de su ciclo de vida de visita. Esto requiere una arquitectura de red robusta capaz de manejar un gran número de dispositivos concurrentes mientras enruta sin problemas el tráfico de autenticación a un Captive Portal o proveedor de identidad.
Mecanismos de Autenticación y Captura de Datos
Cuando un usuario se asocia con el guest SSID, el punto de acceso (AP) o el controlador de LAN inalámbrica (WLC) intercepta la solicitud HTTP/HTTPS y la redirige a un Captive Portal. Este portal sirve como el punto principal de ingesta de datos —el umbral digital entre el visitante anónimo y el cliente identificado.
Los modelos de implementación estándar utilizan RADIUS (Remote Authentication Dial-In User Service) para la autenticación, autorización y contabilidad (AAA). Al integrarse con plataformas como WiFi Analytics de Purple, el Captive Portal solicita atributos de usuario específicos —dirección de correo electrónico, datos demográficos o tokens de inicio de sesión social— antes de conceder acceso a la red a través de un mensaje RADIUS Access-Accept. Los datos se escriben simultáneamente en la base de datos de clientes de la plataforma de análisis y, a través de un webhook de API, en el CRM conectado.
Para implementaciones avanzadas, tecnologías como Passpoint (Hotspot 2.0) y OpenRoaming permiten una incorporación segura y sin interrupciones utilizando IEEE 802.1X y cifrado WPA3 Enterprise. Purple actúa como un proveedor de identidad gratuito para OpenRoaming bajo la licencia Connect, lo que permite la autenticación automática sin interacciones repetitivas con el Captive Portal —reduciendo significativamente la fricción mientras se mantiene una atribución de datos segura para los visitantes recurrentes.
Análisis de Ubicación y Seguimiento del Comportamiento
Más allá de la autenticación inicial, el análisis espacial continuo es fundamental para comprender el recorrido completo del cliente dentro del recinto. Esto se logra rastreando el Indicador de Fuerza de Señal Recibida (RSSI) tanto de las solicitudes de sondeo no asociadas como del tráfico de clientes asociados a través de múltiples APs.
Al triangular estas señales, la red calcula los tiempos de permanencia, identifica zonas de alto tráfico y mapea los patrones típicos de flujo de visitantes. Para una precisión más granular, las implementaciones pueden integrar balizas Bluetooth Low Energy (BLE) o sensores Ultra-Wideband (UWB) junto con la capa WiFi, como se detalla en la Indoor Positioning System: UWB, BLE, & WiFi Guide . Estos datos espaciales se agregan y visualizan a través de mapas de calor y flujos de recorrido, proporcionando la evidencia empírica necesaria para optimizar los diseños físicos, los modelos de personal y la ubicación del marketing en el recinto.

Guía de Implementación: Desplegando la Estrategia
Implementar una estrategia de CX impulsada por WiFi requiere una alineación interfuncional entre TI, marketing y operaciones. El despliegue debe seguir un enfoque por fases para garantizar la estabilidad de la infraestructura, la integridad de los datos y resultados medibles en cada etapa.
Fase 1: Evaluación de la Infraestructura y Diseño de RF
Antes de desplegar superposiciones de análisis, el entorno de RF (Radio Frecuencia) subyacente debe soportar cargas de clientes de alta densidad. Realice encuestas de sitio predictivas y activas para garantizar una cobertura de señal adecuada —típicamente -65 dBm o mejor en el dispositivo cliente— y una capacidad de AP suficiente. Para entornos complejos o especializados, como salas de exposición de automóviles, consulte la Wi Fi in Auto: The Complete 2026 Enterprise Guide para obtener orientación específica sobre la implementación.
Parámetros clave de infraestructura a validar antes de continuar:
| Parámetro | Umbral Mínimo | Notas |
|---|---|---|
| Cobertura de Señal | -65 dBm | A la altura del dispositivo cliente |
| Relación AP-a-Cliente | 1:25 (denso) | Ajustar para recintos de eventos |
| Utilización del Canal | <60% | Por AP, 2.4 GHz y 5 GHz |
| Latencia del Captive Portal | <500ms | Tiempo de respuesta de redirección |
| Ida y Vuelta RADIUS | <100ms | Respuesta de autenticación |
Fase 2: Configuración del Captive Portal e Integración con CRM
El Captive Portal debe equilibrar la adquisición de datos con la experiencia del usuario. Implemente un perfilado progresivo —solicitando datos mínimos durante la primera visita y recopilando incrementalmente atributos adicionales en inicios de sesión posteriores. Un portal bien optimizado debería lograr una tasa de conversión de inicio de sesión del 40-60% del total de visitantes del recinto.
Asegure una integración API fluida entre la plataforma de análisis WiFi y el CRM corporativo (Salesforce, HubSpot, Microsoft Dynamics, o equivalente). Esto permite la sincronización de datos en tiempo real y disparadores de marketing automatizados basados en la presencia física — por ejemplo, el envío de un mensaje de bienvenida personalizado cuando un miembro de un programa de fidelización entra en un entorno minorista, o la activación de una encuesta de satisfacción post-visita 30 minutos después de la salida.
Para estrategias de recopilación de datos específicas para el comercio minorista, la Guía del minorista: Cómo recopilar datos de clientes en la tienda proporciona un marco operativo detallado.
Fase 3: Línea de base de análisis y segmentación de audiencia
Una vez que los datos fluyen, establezca métricas de referencia para las tasas de captura de visitantes, los tiempos de permanencia promedio y las frecuencias de visitas repetidas durante un período mínimo de 30 días. Utilice estos datos para construir perfiles de audiencia segmentados. En un contexto de hostelería, por ejemplo, podría segmentar a los usuarios en Viajeros de Negocios (tiempos de permanencia cortos, alta frecuencia de visitas, predominio entre semana) y Huéspedes de Ocio (tiempos de permanencia prolongados, baja frecuencia de visitas, predominio de fin de semana), adaptando las comunicaciones digitales y las experiencias en el lugar en consecuencia.
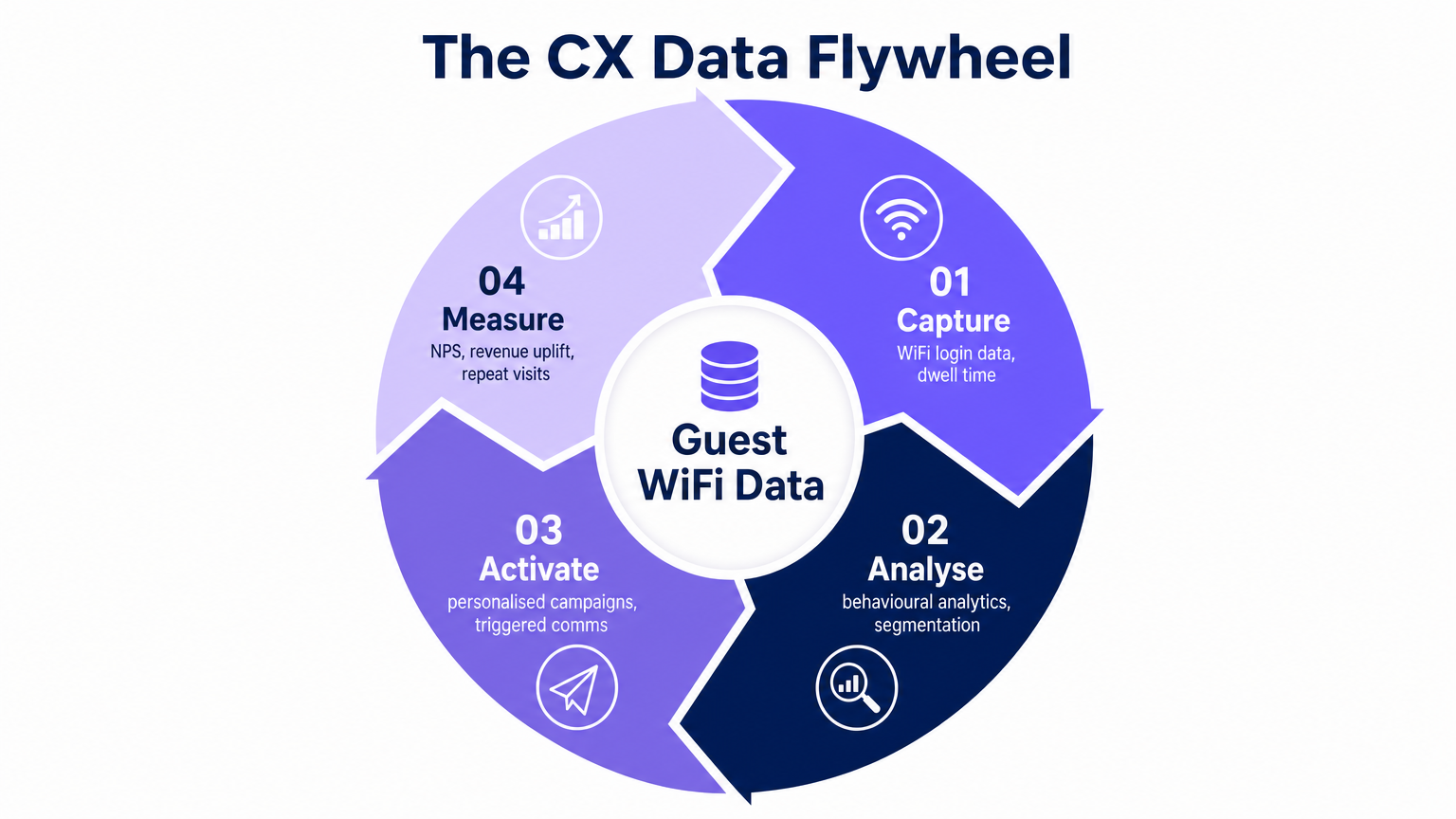
Fase 4: Activación y Personalización
Con los perfiles segmentados establecidos, active los datos a través de comunicaciones dirigidas y personalización en el lugar. Las secuencias de correo electrónico activadas, las campañas de SMS y las notificaciones push de aplicaciones pueden ser impulsadas por eventos de presencia física detectados por la infraestructura WiFi. La capa de integración de IoT que sustenta esta activación se cubre en profundidad en la Arquitectura del Internet de las Cosas: Una Guía Completa .
Mejores Prácticas para Implementaciones Empresariales
Priorice la privacidad y el cumplimiento por diseño. Todos los mecanismos de recopilación de datos deben solicitar explícitamente el consentimiento del usuario de acuerdo con GDPR, CCPA y las regulaciones de privacidad locales aplicables. Implemente la anonimización de direcciones MAC para solicitudes de sondeo no autenticadas en el borde de la red — en el AP o WLC — antes de que cualquier dato llegue a la plataforma de análisis. Los registros de consentimiento deben almacenarse con marcas de tiempo y referencias de versión al aviso de privacidad específico presentado.
Optimice para la autenticación Mobile-First. El captive portal y todas las interacciones digitales posteriores deben ser perfectamente responsivos en iOS y Android. La latencia durante el proceso de autenticación se correlaciona directamente con las tasas de abandono. Apunte a un tiempo de carga del portal de menos de dos segundos en una conexión 4G.
Alinee los KPI de TI y Marketing. TI es responsable del tiempo de actividad de la red, el rendimiento y la latencia de autenticación. Marketing es responsable de las tasas de captura de datos y el rendimiento de la campaña. Una estrategia de CX exitosa requiere objetivos compartidos — métricas como la Tasa de Captura de WiFi (porcentaje de visitantes del lugar que se autentican), el Coste por Visitante Identificado y la Tasa de Visitas Repetidas unen ambas funciones.
Segmente Correctamente su Arquitectura de Red. La red WiFi de invitados debe estar lógicamente aislada de la LAN corporativa utilizando VLANs y reglas estrictas de firewall con estado. Este es un requisito PCI DSS en entornos minoristas y de hostelería donde se procesan datos de tarjetas de pago en el mismo sitio. Las pruebas de penetración regulares del límite de la red son esenciales.
Resolución de Problemas y Mitigación de Riesgos
La implementación de una plataforma integral de análisis de CX introduce modos de fallo específicos que los equipos de TI deben anticipar y mitigar de forma proactiva.
Bajas tasas de captura (inferiores al 20%). Si el porcentaje de visitantes que se autentican en el WiFi es bajo, la causa principal es casi siempre la fricción del captive portal. Audite la UX del portal: reduzca el número de campos obligatorios a uno en la primera visita, añada opciones de inicio de sesión social (Google, Apple, Facebook) y asegúrese de que el intercambio de valor — acceso a internet rápido y fiable a cambio de una dirección de correo electrónico — se comunique claramente en la página de bienvenida.
Datos de ubicación imprecisos. El seguimiento de ubicación basado en RSSI es susceptible a la atenuación de RF por obstáculos físicos (paredes de hormigón, estanterías metálicas, mamparas de vidrio) e interferencias multitrayecto en entornos interiores complejos. Calibre el modelo de RF regularmente y considere complementar el posicionamiento WiFi con balizas BLE en zonas de análisis de alto valor, como expositores de productos o mostradores de servicio.
Fallos en el pipeline de integración. Los límites de tasa de la API o las discrepancias de esquema entre la plataforma de análisis WiFi y el CRM son una fuente común de pérdida de datos. Implemente el manejo de webhooks idempotentes, colas de mensajes fallidos para eventos fallidos y alertas automatizadas cuando el pipeline de eventos caiga por debajo de los umbrales de rendimiento esperados.
Violaciones del límite de seguridad. Las VLANs o reglas de firewall mal configuradas pueden exponer inadvertidamente la red corporativa al tráfico de invitados. Realice auditorías trimestrales de segmentación de red y asegúrese de que todo el enrutamiento inter-VLAN esté explícitamente denegado en el firewall por defecto, permitiendo solo el acceso a internet saliente requerido para el SSID de invitados.
ROI e Impacto Empresarial
La medida definitiva de una estrategia de CX es su impacto en los resultados comerciales. Al digitalizar el espacio físico, las organizaciones pueden aplicar el rigor analítico del comercio electrónico a las operaciones físicas.
| Métrica | Línea de Base Típica | Objetivo Post-Implementación | Método de Medición |
|---|---|---|---|
| Tasa de Captura de WiFi | 10-15% | 40-60% | Plataforma de análisis |
| Tasa de Visitas Repetidas | No medido | +15-25% de aumento | Atribución de CRM |
| Tasa de Apertura de Correo Electrónico | Promedio del sector 20% | 35-45% (activado por ubicación) | Plataforma de marketing |
| Ingresos Adicionales por Visita | Línea de base | +8-12% de aumento | Integración POS |
| Eficiencia en la Asignación de Personal | Programación manual | Impulsado por la demanda (datos de permanencia) | Panel de operaciones |
Valor de Vida del Cliente (CLV) Aumento de valor. Las interacciones personalizadas impulsadas por datos de ubicación y comportamiento aumentan las tasas de visitas repetidas y los valores medios de transacción. Las organizaciones que implementan comunicaciones activadas y basadas en la presencia informan consistentemente aumentos del CLV del 10-20% en el primer año de implementación.
Mejoras en la Eficiencia Operativa. Los mapas de calor y los datos de tiempo de permanencia permiten una asignación de personal basada en la demanda, reduciendo los costes laborales durante los períodos de menor actividad y mejorando la calidad del servicio durante la demanda máxima. En un contexto de estadio, esto se traduce directamente en tiempos de espera reducidos y un mayor gasto por persona en concesiones.
Precisión en la Atribución de Marketing. Al correlacionar los eventos de visitas físicas con la exposición a campañas digitales, los equipos de marketing pueden medir el impacto offline del gasto online con una precisión que antes solo estaba disponible para operadores de e-commerce puros. Esto traslada la conversación de métricas proxy (impresiones, clics) a resultados comerciales concretos (visitas a tiendas, aumento de transacciones).
Términos clave y definiciones
Captive Portal
A web page that a user of a public-access network is required to interact with before internet access is granted. It serves as the primary data ingestion point in a guest WiFi deployment.
IT teams encounter this as the first digital touchpoint in the physical venue. Portal design directly determines WiFi capture rates and data quality.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, expressed in dBm. Used by analytics platforms to estimate the distance between a client device and an access point.
The foundational input for location analytics and zone-based dwell time measurement. Accuracy is typically 3-10 metres in a well-designed RF environment.
OpenRoaming
A global roaming federation service, built on Passpoint (IEEE 802.11u/Hotspot 2.0), that enables automatic and secure WiFi onboarding without captive portal interactions.
Critical for reducing login friction for returning visitors while maintaining secure identity attribution. Purple provides a free identity provider service for OpenRoaming under the Connect licence.
MAC Address Anonymisation
The process of cryptographically hashing a device's Media Access Control address before storage, preventing the identification of individual devices from the stored data.
A mandatory GDPR compliance step when tracking unauthenticated devices via probe requests. Must be implemented at the network edge, not in the analytics database.
Dwell Time
The duration of time a device remains within a specific defined zone or venue, measured from first detection to last detection within that zone.
A primary operational metric for measuring engagement, identifying queue bottlenecks, and optimising staff deployment. Typically measured in minutes.
Progressive Profiling
A data collection methodology that gathers customer attributes incrementally across multiple interactions, rather than requesting all information at a single point.
The standard best practice for captive portal design. Reduces initial login friction while building comprehensive customer profiles over time.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance certification programme based on IEEE 802.11u that enables seamless, secure roaming between Wi-Fi networks using WPA2/WPA3 Enterprise authentication.
Provides enterprise-grade security for guest networks and automates the authentication process for returning users, eliminating repetitive captive portal interactions.
WiFi Capture Rate
The percentage of total venue visitors who successfully authenticate to the guest WiFi network, providing a consented identity record.
The primary KPI for measuring the effectiveness of the captive portal and the health of the first-party data pipeline. Industry benchmarks range from 15% (poor) to 60%+ (optimised).
Spatial Analytics
The analysis of location-based data to understand movement patterns, zone utilisation, and spatial relationships within a physical environment.
Enables venue operators to visualise customer journeys, measure zone conversion rates, and make evidence-based decisions about physical layout and resource allocation.
Casos de éxito
A 200-room hotel is experiencing low guest WiFi adoption rates — under 15% of guests are logging in — and is failing to capture sufficient first-party data to support a new loyalty programme initiative. The hotel uses a legacy captive portal with a six-field registration form.
Step 1 — Diagnose the Friction Point: Pull the captive portal analytics to identify the drop-off rate at each form field. In most cases, the majority of abandonment occurs after the second or third required field. Step 2 — Streamline Authentication: Replace the six-field form with a single-click social login (Google, Apple, or Facebook OAuth) as the primary option, with email-only as a secondary option. This reduces the time-to-internet from 45-60 seconds to under 10 seconds. Step 3 — Implement Progressive Profiling: Configure the analytics platform to request only the email address on the first visit. On the second visit, display a prompt offering 500 loyalty points in exchange for a phone number. On the third visit, request a date of birth for a birthday reward. Step 4 — Deploy OpenRoaming for Returning Guests: For guests who have previously authenticated, configure Passpoint/OpenRoaming so their device reconnects automatically on future visits without seeing the captive portal, while still attributing the visit to their profile. Step 5 — Measure and Iterate: Track the WiFi Capture Rate weekly. Target 40% within 60 days of deployment.
A large retail chain wants to measure the commercial effectiveness of a new store layout in driving traffic to a high-margin accessories display area, and needs to justify the capital expenditure on the refit to the board.
Step 1 — Define the Analytics Zone: Within the WiFi analytics platform, draw a geofence around the accessories display area. Ensure AP coverage within the zone is sufficient for accurate RSSI triangulation (minimum two APs with clear line of sight). Step 2 — Establish a Pre-Refit Baseline: Over a 30-day period before the layout change, measure: Zone Conversion Rate (percentage of total store visitors who enter the accessories zone), Average Dwell Time within the zone, and Bounce Rate (visitors who enter and leave within under 30 seconds). Step 3 — Implement the Layout Change. Step 4 — Measure Post-Refit Performance: Over the equivalent 30-day period post-refit, collect the same metrics. Step 5 — Correlate with POS Data: Integrate the WiFi analytics platform with the POS system to correlate zone dwell time with accessories transaction volume. Calculate the incremental revenue attributable to the layout change. Step 6 — Calculate ROI: Divide the incremental annual revenue by the refit capital cost to produce a payback period for the board presentation.
Análisis de escenarios
Q1. A stadium IT director wants to track queue times at concession stands in real time to dynamically deploy additional staff during peak periods. The venue has standard WiFi coverage across the concourse. What is the most appropriate technological approach, and what are the limitations of relying solely on WiFi RSSI data for this use case?
💡 Sugerencia:Consider the accuracy requirements for measuring a dense, slow-moving queue versus general concourse crowd flow. What is the typical RSSI accuracy range, and is it sufficient for distinguishing a 2-metre queue from a 5-metre queue?
Mostrar enfoque recomendado
Standard WiFi RSSI tracking provides positional accuracy of approximately 3-10 metres in a well-calibrated indoor environment, which is insufficient for precise queue length measurement at a concession stand. The recommended approach is to supplement the WiFi infrastructure with either: (a) BLE beacons mounted directly above each concession counter, providing sub-2-metre accuracy for devices within the queue zone; or (b) overhead stereoscopic cameras with computer vision analytics for people-counting independent of device presence. The WiFi layer remains valuable for macro-level concourse crowd density and flow direction, while the supplementary technology handles the precision queue measurement use case. The integration point is the analytics platform, which should aggregate both data streams into a unified operational dashboard.
Q2. The marketing team at a retail chain wants to send a personalised push notification to a high-value loyalty member the moment they enter the store, before they have interacted with any staff. The current deployment uses a standard captive portal that takes approximately 45 seconds to complete. How should the IT team architect a solution that delivers a sub-10-second entry notification?
💡 Sugerencia:The captive portal authentication flow is too slow for an immediate entry notification. What authentication mechanism eliminates the portal interaction for returning users while still attributing the visit to their identity?
Mostrar enfoque recomendado
The solution requires implementing Passpoint/OpenRoaming for returning loyalty members. The workflow is: (1) On the member's first visit, they complete the standard captive portal and their device credentials are provisioned for Passpoint. (2) On all subsequent visits, the device automatically authenticates via 802.1X/WPA3 Enterprise without displaying the captive portal, completing the authentication handshake in under 2 seconds. (3) The WiFi analytics platform detects the association event and identifies the user via their provisioned identity token. (4) A real-time webhook fires to the marketing automation platform, which dispatches the push notification within 5-8 seconds of the device entering the RF coverage zone. The key architectural requirement is that the loyalty app must have push notification permissions enabled, and the member's device must have the Passpoint profile installed — typically achieved via the loyalty app onboarding flow.
Q3. During a routine network audit at a multi-site retail operator, it is discovered that the guest WiFi analytics platform has been storing raw, unhashed MAC addresses from unauthenticated probe requests for the past 18 months across all 47 stores. What is the primary regulatory risk, what is the immediate remediation action, and what architectural change is required to prevent recurrence?
💡 Sugerencia:Consider the GDPR classification of MAC addresses and the territorial scope of the regulation. What constitutes a 'personal data breach' under Article 33?
Mostrar enfoque recomendado
The primary risk is a material GDPR violation under Article 5(1)(b) (purpose limitation) and Article 5(1)(e) (storage limitation), as raw MAC addresses are classified as personal data under Recital 30 of the GDPR. The 18-month retention of unauthenticated probe data without a lawful basis or consent constitutes unlawful processing. Immediate remediation: (1) Notify the Data Protection Officer and conduct a Data Protection Impact Assessment (DPIA). (2) Assess whether the breach meets the Article 33 threshold for supervisory authority notification (within 72 hours if there is a risk to individuals' rights). (3) Purge all stored raw MAC addresses from the analytics database immediately. Architectural remediation: Configure the analytics platform or WLC to apply a SHA-256 hash with a rotating salt to all MAC addresses at the point of capture — on the AP or controller — before any data is transmitted to the analytics platform. This ensures that no raw MAC address ever enters the data pipeline, making the stored data non-personal by design. Implement a 90-day maximum retention policy for anonymised probe data, enforced by automated database purge jobs.



