Restaurant WiFi Marketing: How to Turn Free WiFi Into Repeat Customers
This authoritative technical reference guide explores the architecture and implementation of restaurant WiFi marketing — the practice of using guest network access as a structured data acquisition and marketing automation channel. It provides IT managers, network architects, and venue operations directors with a tactical blueprint for deploying captive portals, integrating with CRM platforms, and triggering automated campaigns that drive measurable repeat business. From GDPR-compliant data capture to event-driven email workflows, this guide covers the full deployment lifecycle with concrete ROI metrics.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- Authentication Workflows and Data Capture
- Security and Compliance Protocols
- Implementation Guide: Deployment Strategies
- Step 1: Infrastructure Assessment and Sizing
- Step 2: Captive Portal Configuration
- Step 3: CRM and Automation Integration
- Step 4: Campaign Automation Setup
- Best Practices for Enterprise Venues
- Troubleshooting & Risk Mitigation
- Common Failure Modes and Resolutions
- ROI & Business Impact
Executive Summary
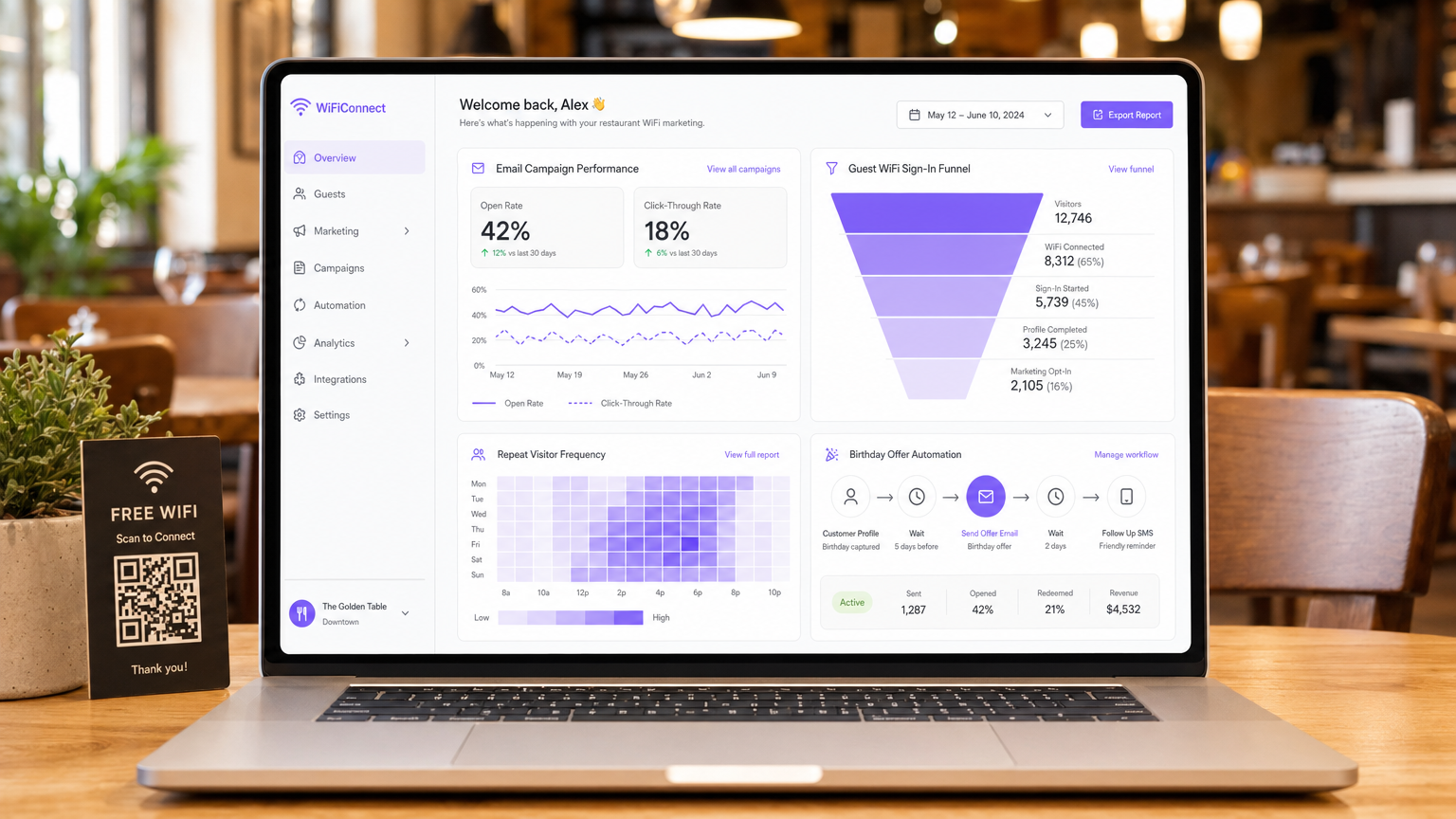
For IT managers, network architects, and CTOs operating in hospitality, retail, and public sector environments, providing guest network access has evolved from a basic utility into a critical data acquisition channel. Understanding what is restaurant WiFi marketing is foundational to extracting ROI from network infrastructure investments. This guide outlines the technical architecture, deployment strategies, and risk mitigation protocols required to turn a cost centre — free guest WiFi — into a measurable driver of repeat business and customer loyalty.
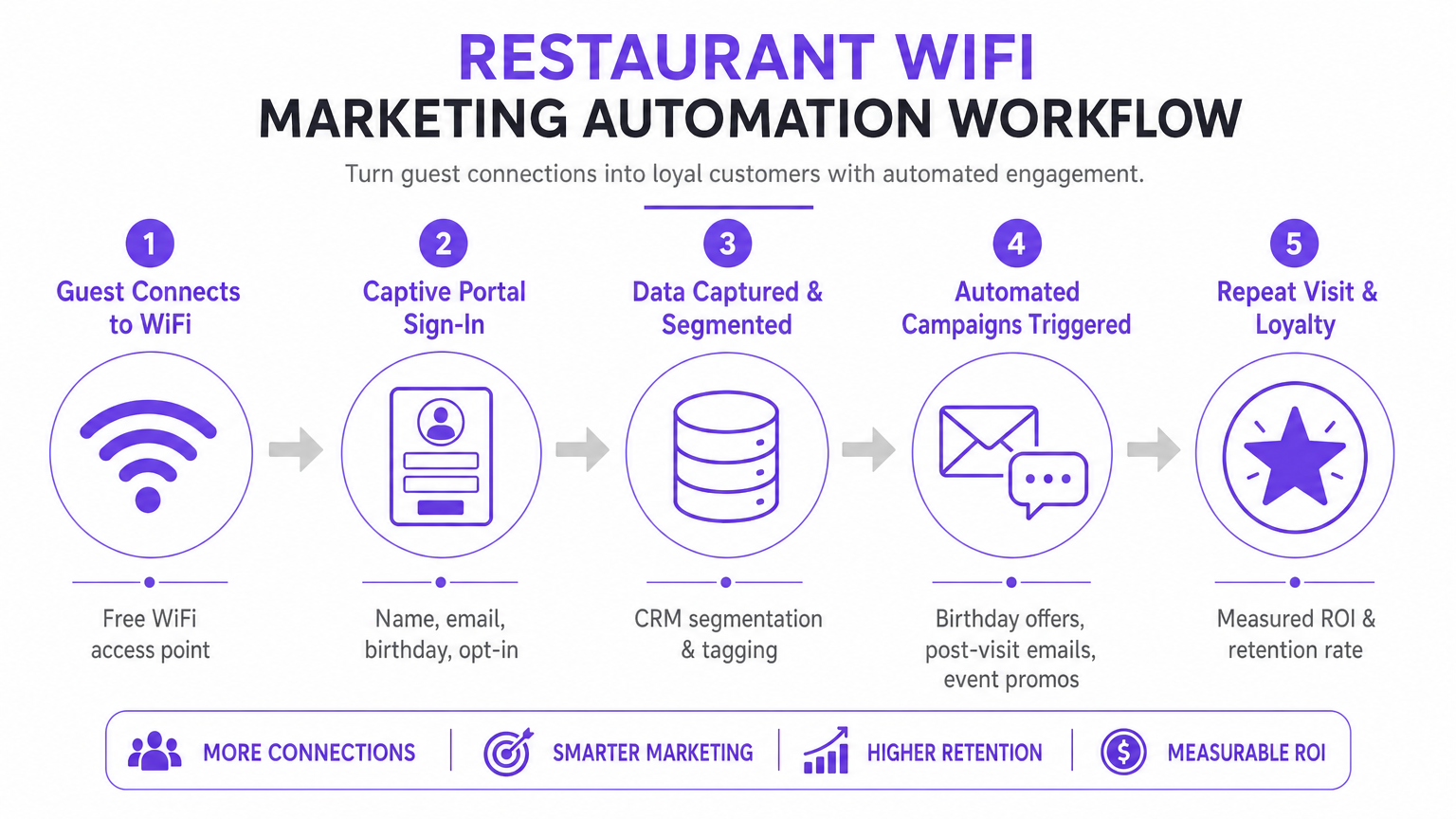
Deploying an enterprise-grade Guest WiFi solution requires more than simply broadcasting an SSID. It demands a robust architecture that integrates seamlessly with CRM platforms, marketing automation tools, and analytics engines, all while adhering to stringent compliance standards including GDPR and PCI DSS. By implementing structured data capture through captive portals, venues can segment users, trigger automated marketing campaigns (post-visit emails, birthday offers, and event promotions), and generate valuable reviews. This guide provides a tactical blueprint for configuring and optimising WiFi marketing workflows to maximise throughput, ensure security, and drive measurable business impact.
Technical Deep-Dive: Architecture and Standards
The foundation of effective guest WiFi marketing lies in a scalable and secure network architecture. At its core, the system relies on a captive portal mechanism that intercepts HTTP/HTTPS requests from unauthenticated devices, redirecting them to a hosted authentication page. This process typically utilises RADIUS (Remote Authentication Dial-In User Service) for centralised Authentication, Authorization, and Accounting (AAA).
Authentication Workflows and Data Capture
When a device connects to the guest SSID, the Wireless LAN Controller (WLC) or access point restricts network access, placing the device in a walled garden. The user is presented with a captive portal, which serves as the primary data acquisition interface. To optimise conversion rates, the portal must support multiple authentication methods:
| Authentication Method | Friction Level | Data Quality | Implementation Complexity |
|---|---|---|---|
| Social Login (OAuth 2.0) | Low | High (demographic-rich) | Medium |
| Form-Based (Email + Opt-In) | Medium | Controlled | Low |
| SMS Verification | Medium-High | High (verified mobile) | Medium |
| Passpoint / Hotspot 2.0 | Very Low | Medium | High |
Social Login (OAuth 2.0) integrations with Google or Facebook provide low-friction access while capturing rich demographic data. This method relies on secure token exchange, eliminating the need for users to create new credentials. Form-Based Authentication allows users to provide their name, email address, and optionally date of birth or phone number. This data is validated and securely transmitted to the centralised database. Seamless Re-authentication (MAC Caching) caches a device's MAC address for a configurable duration (e.g., 30 days), enabling frictionless access and accurate frequency tracking on subsequent visits.
Security and Compliance Protocols
Deploying WiFi for marketing necessitates strict adherence to security and privacy standards. The architecture must segregate guest traffic from corporate networks using VLANs to prevent lateral movement. The implementation must comply with:
- GDPR / CCPA: Explicit, unbundled consent mechanisms must be integrated into the captive portal. Users must actively opt-in to marketing communications, and the platform must provide robust data subject access request (DSAR) capabilities. Marketing consent cannot be bundled with the network access terms of service.
- PCI DSS: If the venue processes payments on the same physical infrastructure, network segmentation and firewall rules must isolate the Cardholder Data Environment (CDE) from the guest network.
- WPA3-Enhanced Open (OWE): Transitioning to secure onboarding protocols provides opportunistic encryption for unauthenticated traffic, mitigating eavesdropping risks on open networks without requiring user credentials.
Implementation Guide: Deployment Strategies
Successful deployment requires a phased approach, focusing on integration and automation. The goal is to establish a seamless data flow from the access point to the marketing automation platform.
Step 1: Infrastructure Assessment and Sizing
Before deploying a captive portal, ensure the underlying RF infrastructure can handle the anticipated client density. Conduct a predictive and active site survey to identify coverage gaps and optimise AP placement. Consider channel utilisation, co-channel interference, and required throughput per device. For enterprise deployments, leveraging a dedicated business internet connection — such as a leased line — ensures guaranteed bandwidth and symmetrical speeds, preventing guest traffic from impacting critical operational systems.
Step 2: Captive Portal Configuration
Design the captive portal with a focus on conversion optimisation. The UI must be responsive and load quickly on mobile devices, as the majority of connections will originate from smartphones. Implement progressive profiling: request basic information (email address, opt-in) during the initial visit, and ask for supplementary data (birthday, phone number) upon subsequent connections. This minimises friction while enriching the customer profile over time.
Step 3: CRM and Automation Integration
The true value of a WiFi Analytics platform is realised through integration. Configure API webhooks or native connectors to synchronise captured data with the venue's CRM (e.g., Salesforce, HubSpot) and marketing automation tools. Establish clear data mapping rules to ensure fields like Last Visit Date and Total Visits are updated in real-time upon each authentication event.
Step 4: Campaign Automation Setup
Configure automated workflows triggered by specific network events. The three core campaigns every deployment should include are:
- The Welcome Campaign: Triggered immediately upon first successful authentication. Delivers a welcome message and a low-barrier offer to incentivise a return visit within a defined window.
- The We Miss You Campaign: Triggered when a device has not been seen on the network for a specified duration (e.g., 45 days). Offers a targeted discount to re-engage lapsed customers at precisely the right moment.
- The Review Generation Campaign: Triggered 2 hours after a user disconnects from the network, leveraging RADIUS Accounting-Stop events or location API webhooks. Solicits feedback via TripAdvisor or Google My Business while the experience is still fresh.
Best Practices for Enterprise Venues
To maximise the efficacy of how to improve customer experience in a restaurant through WiFi marketing, the following vendor-neutral best practices apply across Hospitality , Retail , and Transport environments.
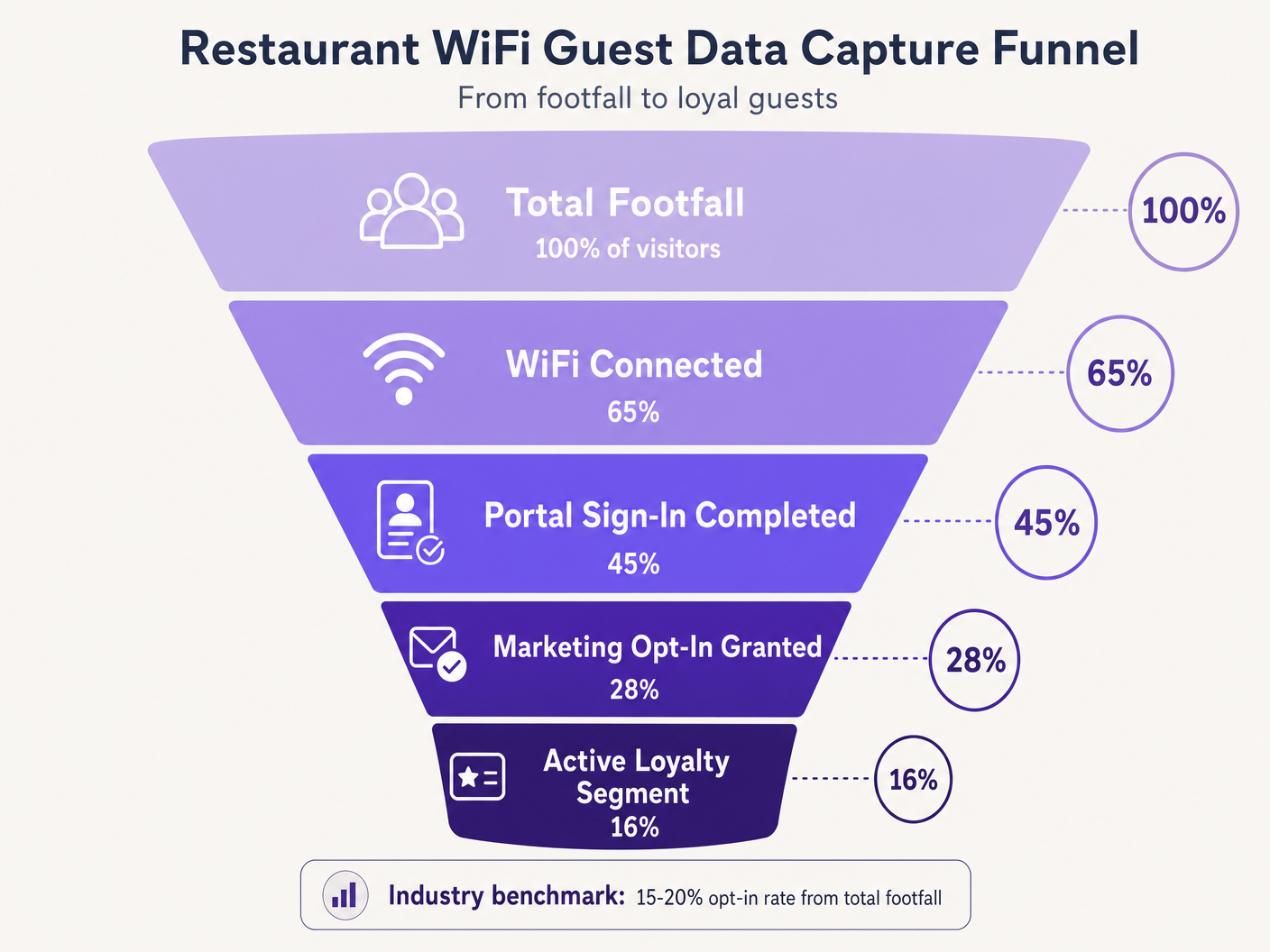
Prioritise the Opt-In. The captive portal's primary objective is acquiring marketing consent. Ensure the value proposition — for example, 'Join our WiFi for exclusive offers and a birthday treat' — is prominently displayed. Industry benchmarks suggest a 15–20% opt-in rate from total footfall is achievable with optimised portals. Venues with poorly designed portals often see rates below 5%.
Leverage Location Analytics. Utilise the wireless infrastructure's location services (RSSI triangulation) to understand dwell times and movement patterns. This data informs operational decisions — staffing levels, layout optimisation, peak-hour management — well beyond pure marketing applications. The WiFi Analytics platform provides the dashboards and reporting layer for this intelligence.
Implement Bandwidth Throttling. Prevent a small number of users from monopolising network resources by implementing per-device bandwidth limits and session timeouts. This ensures a consistent Quality of Experience (QoE) for all guests and protects operational systems from bandwidth saturation.
Cross-Vertical Application. The principles of WiFi marketing extend directly to adjacent sectors. For operators managing licensed premises, the Bar and Pub WiFi: A Complete Setup and Marketing Guide provides a parallel tactical reference. For healthcare and public-sector deployments, compliance requirements are more stringent but the data capture architecture remains fundamentally similar.
Troubleshooting & Risk Mitigation
Deploying guest WiFi introduces specific risks that must be proactively managed before go-live.
Common Failure Modes and Resolutions
| Failure Mode | Root Cause | Resolution |
|---|---|---|
| Captive portal does not appear | Walled garden misconfiguration, SSL cert error | Audit whitelist domains; deploy valid SSL cert on portal |
| Social login fails silently | OAuth provider domains not whitelisted | Add provider auth domains to walled garden |
| Returning guests prompted to re-authenticate | MAC randomisation (iOS 14+, Android 10+) | Implement Passpoint profiles or venue app |
| CRM data sync delays | API rate limits or webhook failures | Implement exponential backoff, dead-letter queues |
| Low opt-in rate | Excessive form fields, poor value proposition | Reduce to email + opt-in; improve portal copy |
MAC Address Randomisation deserves particular attention. Modern mobile operating systems generate randomised MAC addresses to enhance privacy, directly disrupting MAC caching and frequency tracking. Returning guests may be treated as new visitors, skewing analytics and triggering incorrect campaign sequences. The long-term mitigation is transitioning to Passpoint (Hotspot 2.0), which utilises persistent device profiles independent of the MAC address. As Purple's expanding platform strategy demonstrates — including developments discussed in the context of Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers — adapting to evolving privacy standards is critical for sustainable data strategy across all verticals.
ROI & Business Impact
The ultimate goal of deploying a WiFi marketing solution is to generate a measurable return on investment. Success should be quantified using a defined set of KPIs tracked from day one.
| KPI | Definition | Industry Benchmark |
|---|---|---|
| Data Capture Rate | % of total footfall that authenticates | 40–65% |
| Marketing Opt-In Rate | % of authenticated users granting consent | 15–28% |
| Campaign Open Rate | % of campaign emails opened | 35–45% |
| Campaign Conversion Rate | % of recipients redeeming an offer | 8–15% |
| Repeat Visit Uplift | Increase in return visits vs. control group | 12–22% |
By systematically capturing data, segmenting audiences, and automating targeted campaigns, IT and marketing teams can transform their wireless infrastructure from a necessary expense into a strategic asset. For insights into broader connectivity trends impacting venue operations in 2026, incincluding the convergence of in-vehicle and venue WiFi strategies, refer to Wi Fi in Auto: The Complete 2026 Enterprise Guide .
Audio Briefing: A 10-minute consultant briefing on architecting WiFi for marketing ROI — covering architecture, integration, risk mitigation, and rapid-fire Q&A.
Key Terms & Definitions
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before full internet access is granted. It serves as the primary data acquisition and consent interface in a guest WiFi deployment.
The captive portal is the single most important component in a WiFi marketing architecture. Its design directly determines data capture rates and marketing opt-in rates.
MAC Caching
The process of storing a device's Media Access Control (MAC) address in a database after initial authentication, allowing for automatic network access on subsequent visits without re-presenting the captive portal.
Essential for reducing friction for repeat customers and accurately tracking visit frequency. Increasingly challenged by MAC address randomization in modern mobile operating systems.
Walled Garden
A restricted network environment that controls which IP addresses or domains a device can access before completing authentication. In guest WiFi, it defines the resources accessible prior to captive portal sign-in.
Critical configuration required to allow devices to reach the captive portal, social login providers, and necessary backend services before full internet access is granted. Misconfiguration is the leading cause of portal non-appearance.
Progressive Profiling
The technique of gradually gathering customer information across multiple interactions or visits, rather than requesting all details at once during the initial interaction.
Used to maximise initial opt-in rates by keeping the first captive portal interaction brief (email + opt-in only), while building richer customer profiles over subsequent visits.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service.
The underlying protocol used by most enterprise WLC infrastructure to communicate with the central database managing guest access. RADIUS Accounting-Stop messages are used to detect guest departures for event-driven campaign triggers.
OAuth 2.0
An industry-standard authorisation protocol allowing third-party applications to grant limited access to an HTTP service via secure token exchange, without sharing user passwords.
The protocol underlying Social Login options (Log in with Google, Log in with Facebook). Provides low-friction authentication for captive portals while capturing verified demographic data from the identity provider.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance standard enabling automatic, secure network discovery and connection using WPA2/WPA3 enterprise-grade encryption, without requiring manual captive portal interaction.
The strategic long-term alternative to open captive portals, providing persistent device identification that is not affected by MAC address randomization. Higher implementation complexity but superior user experience and data accuracy.
MAC Address Randomization
A privacy feature in modern mobile operating systems (iOS 14+, Android 10+) that generates a unique, randomized MAC address for each network connection, or rotates it periodically.
Directly disrupts MAC caching and frequency tracking in WiFi marketing deployments. Returning guests may be treated as new visitors, skewing analytics and triggering incorrect campaign sequences. Requires Passpoint or app-based identification as a mitigation strategy.
Case Studies
A national restaurant chain with 150 locations is experiencing low data capture rates — under 5% of total footfall — on their existing guest WiFi network. The current setup requires users to fill out a lengthy 6-field form before granting access. The IT team has been asked to improve this to at least 20% capture rate without replacing the underlying WLC infrastructure. How should the architecture be reconfigured?
The implementation requires a shift to progressive profiling and low-friction authentication, achievable without replacing WLC hardware. Step 1: Reconfigure the captive portal application layer to present OAuth 2.0 social login buttons (Google, Facebook) as the primary authentication option. This requires adding the OAuth provider authentication domains to the walled garden whitelist on the WLC. Step 2: For users who prefer form-based authentication, reduce the initial form to two fields only: Email Address and a clearly labelled Marketing Opt-In checkbox. Remove all other fields from the initial interaction. Step 3: Implement MAC caching with a 30-day expiry on the portal backend. Authenticated MAC addresses are stored in the portal database; the WLC checks this list before presenting the portal. Step 4: Configure the portal to present a secondary data capture prompt (birthday, phone number) on the second or third visit, after trust has been established. Step 5: Integrate the portal database with the central CRM via REST API webhooks, ensuring the 'Visit Count' field is incremented on each authentication event to drive the progressive profiling logic.
A large conference centre hosting 200+ events per year wants to implement an automated Review Generation campaign. They need the system to send an email to delegates exactly 2 hours after they leave the venue, with the email content personalised to the specific event they attended. What technical components and configurations are required?
This requires integration between the WLC, the Location Analytics engine, the event management system, and the Marketing Automation platform. Step 1: Configure the WLC to generate RADIUS Accounting-Stop messages when a client device disassociates. Alternatively, configure the location analytics engine to trigger a 'departure' event when a device's RSSI drops below the venue's geofence threshold for a sustained period (e.g., 5 minutes). Step 2: Configure a webhook in the WiFi Analytics platform that fires upon receiving the departure event. The webhook payload must include the user's email address, the venue zone ID, and the timestamp. Step 3: In the event management system, maintain a lookup table mapping venue zone IDs and time windows to specific event names. The marketing automation platform queries this table to enrich the webhook payload with the event name. Step 4: In the Marketing Automation platform, create a workflow that receives the enriched webhook, initiates a 2-hour delay timer, and then dispatches a personalised review request email using the event name as a dynamic content variable. Step 5: Configure suppression lists to prevent the email from sending if the delegate has already submitted a review or if they are flagged as a VIP requiring a personal follow-up.
Scenario Analysis
Q1. A venue reports that iOS users are repeatedly asked to sign in every time they visit, despite MAC caching being enabled with a 30-day expiry. Android users are not experiencing this issue to the same extent. The WLC logs show new MAC addresses for each iOS connection from the same physical device. What is the root cause and what are the available mitigation strategies?
💡 Hint:Consider privacy features introduced in iOS 14 and later regarding hardware identifiers on a per-network basis.
Show Recommended Approach
The root cause is MAC Address Randomization (Private Wi-Fi Address feature in iOS 14+). iOS devices generate a unique, randomized MAC address for each SSID, and may rotate it periodically. Because the cached MAC address no longer matches the device's current randomized address, the WLC treats each connection as a new device and presents the captive portal. Short-term mitigation: instruct users to disable Private Wi-Fi Address for the venue's specific SSID in their iOS network settings. Long-term mitigation: deploy Passpoint (Hotspot 2.0) profiles that provide persistent, certificate-based device identification independent of the MAC address, or develop a venue-specific mobile app that maintains a persistent user session identifier.
Q2. You are designing the walled garden configuration for a new captive portal deployment that utilises Facebook and Google for social login, and hosts the portal UI on a CDN. The portal also uses an external font library. What specific categories of resources must be whitelisted to ensure the authentication process completes successfully?
💡 Hint:Map out the complete sequence of HTTP requests a client device makes from the moment it connects to the SSID to the moment it receives the OAuth callback token.
Show Recommended Approach
The walled garden must whitelist the following resource categories: 1. The captive portal server's own IP range or domain. 2. The CDN domains hosting the portal's HTML, CSS, and JavaScript assets. 3. The external font library domain (e.g., fonts.googleapis.com). 4. The OAuth authentication domains for Facebook (e.g., graph.facebook.com, www.facebook.com ) and Google (e.g., accounts.google.com, oauth2.googleapis.com). 5. Any image or asset CDNs used by the OAuth providers' login buttons. 6. Certificate Revocation List (CRL) or OCSP endpoints to allow the client device to validate the portal's SSL certificate. Missing any of these categories will cause the authentication flow to fail silently or present a broken UI.
Q3. A marketing team wants to trigger an SMS campaign to guests exactly when they walk past a specific dessert counter inside the restaurant. The current infrastructure uses standard 802.11ac access points with RSSI-based location analytics. Is this feasible with the required accuracy and latency? What infrastructure changes, if any, would be required?
💡 Hint:Evaluate the spatial resolution and update latency of standard RSSI-based triangulation versus the precision required for a counter-level trigger.
Show Recommended Approach
No, this is not feasible with standard RSSI-based location analytics. RSSI triangulation typically provides a positional accuracy of 5–10 metres, which is insufficient for distinguishing a specific counter within a restaurant. Furthermore, the polling interval for RSSI updates introduces latency of several seconds, meaning the guest may have already moved past the target area before the trigger fires. To achieve counter-level accuracy with low latency, the infrastructure would need to be augmented with BLE (Bluetooth Low Energy) beacons placed at the dessert counter, or Ultra-Wideband (UWB) technology. The venue app or a BLE-capable device would detect the beacon's proximity signal and trigger the SMS via the marketing automation platform. This requires a venue-specific mobile application and a BLE beacon management system, representing a significant increase in deployment complexity and cost.



