University WiFi: How to Build a Campus-Wide Wireless Network
This comprehensive guide provides senior IT professionals with actionable strategies for designing, deploying, and managing a robust campus-wide wireless network. It covers hierarchical network architecture, security standards (IEEE 802.1X, WPA3, GDPR), and how to utilise analytics to drive ROI in higher education environments. Whether you are upgrading legacy infrastructure or building from scratch, this guide maps every decision point from site survey to ongoing optimisation.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Network Architecture and Topology
- Security Standards and Authentication
- Implementation Guide
- Phase 1: Site Survey and RF Planning
- Phase 2: Infrastructure and Backhaul Upgrades
- Phase 3: Network Architecture Configuration
- Phase 4: Security and Compliance Hardening
- Phase 5: Analytics Integration and Ongoing Optimisation
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
For higher education institutions, a reliable campus-wide wireless network is no longer an amenity — it is critical infrastructure on a par with power and water. Modern universities must support high-density environments, seamless roaming across vast physical footprints, and secure access for a diverse user base spanning students, faculty, researchers, and guests. This guide provides IT managers, network architects, and CTOs with an authoritative blueprint for deploying and managing a high-performance university WiFi network. By focusing on robust hierarchical architecture, stringent security protocols including IEEE 802.1X and WPA3 Enterprise, and strategic analytics integration, institutions can ensure optimal connectivity while mitigating risk and proving measurable ROI. We explore practical deployment phases from initial site surveys through to ongoing optimisation using platforms like Purple's Guest WiFi and WiFi Analytics .
Technical Deep-Dive
Network Architecture and Topology
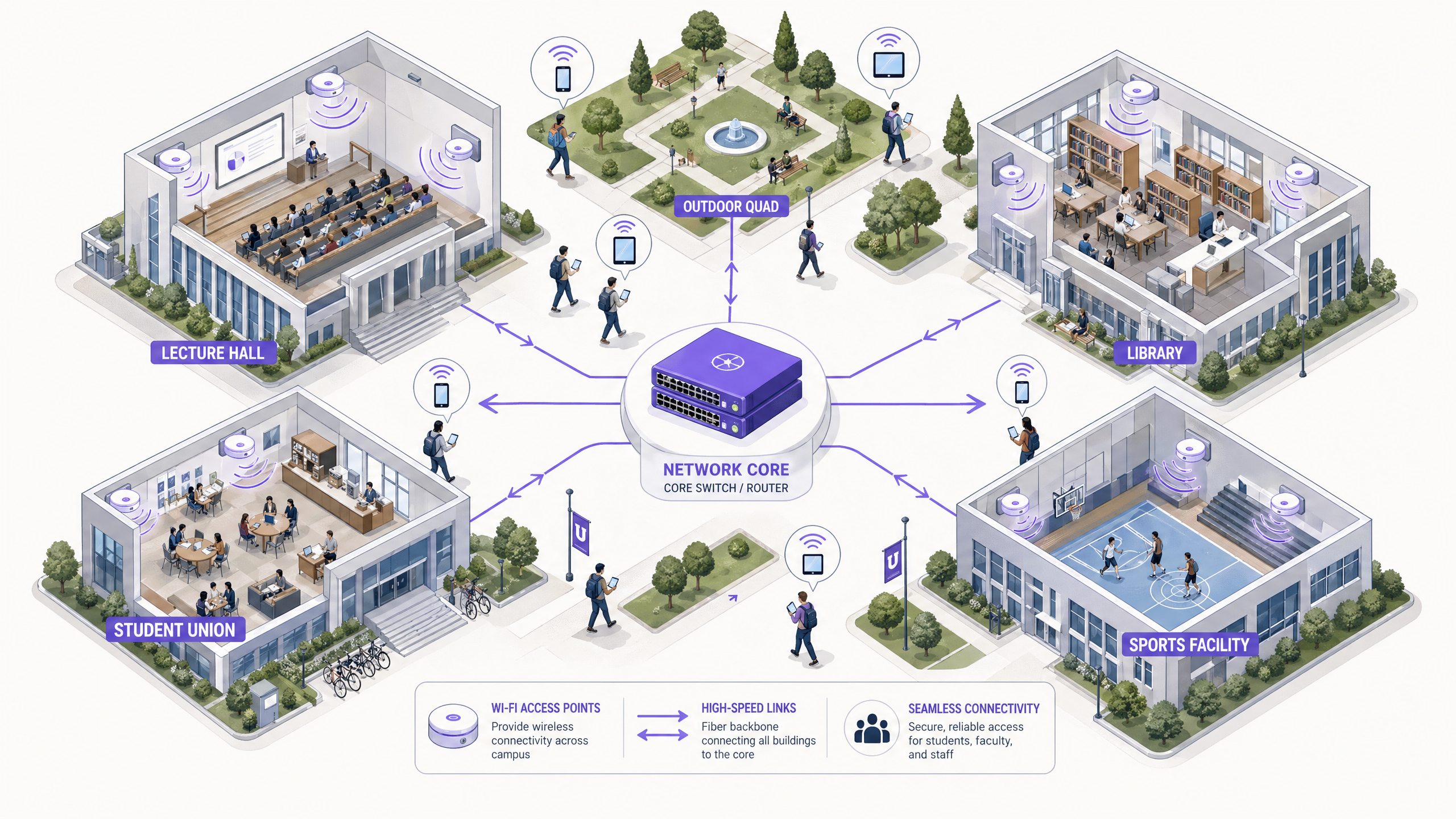
Building a campus-wide wireless network requires a scalable, hierarchical architecture. The standard approach involves three distinct layers: the Core, Distribution, and Access layers.
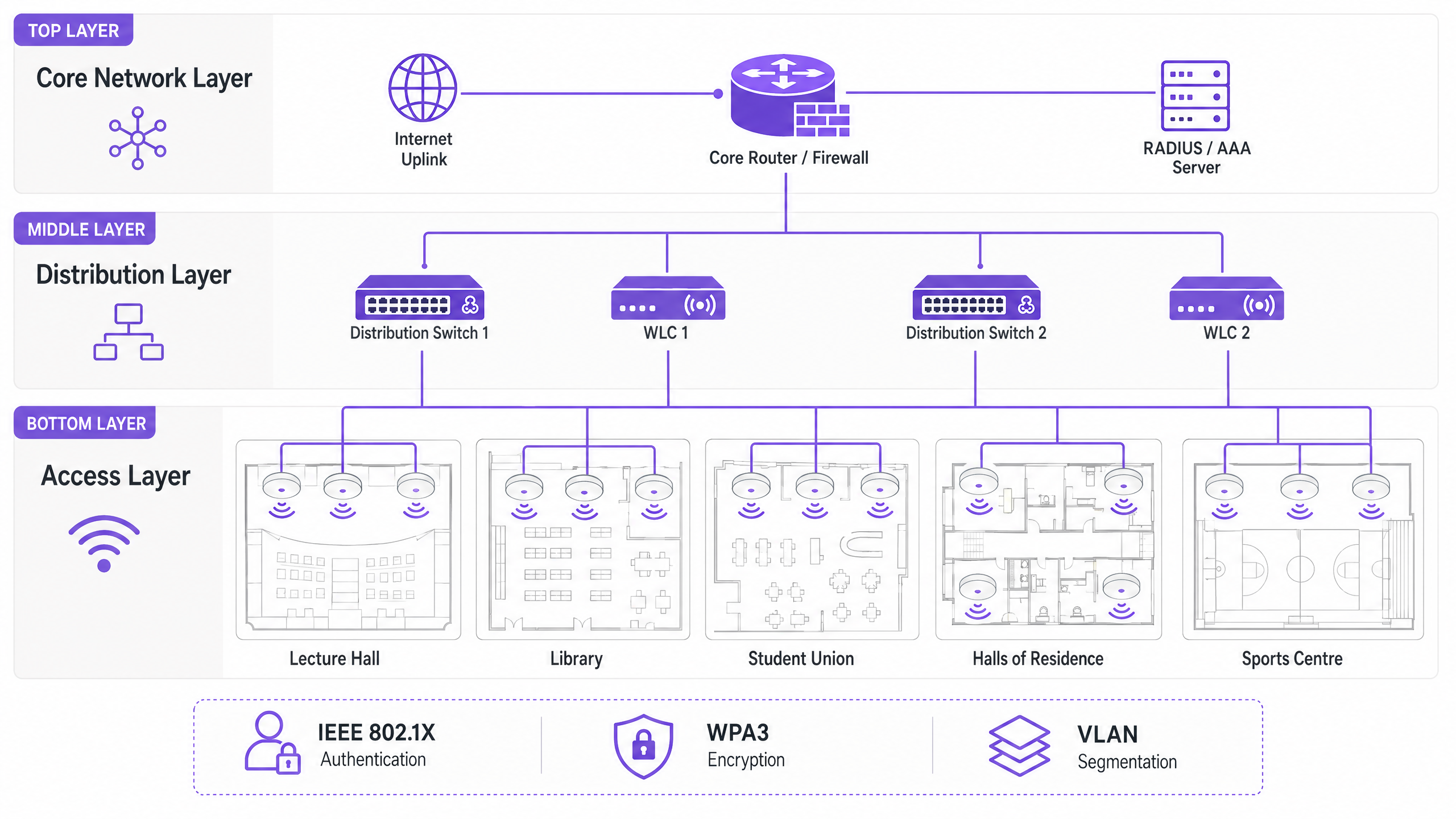
The Core Layer forms the high-speed backbone of the network. It handles the routing of traffic between different parts of the campus and out to the internet. High availability and redundancy are paramount here — core routers and firewalls must be capable of handling massive throughput without introducing latency. Dual-homed uplinks and redundant power supplies are standard practice.
The Distribution Layer acts as the intermediary, aggregating traffic from access switches and enforcing network policies. Wireless LAN Controllers (WLCs) typically reside here, managing the fleet of Access Points (APs), handling RF management, and ensuring seamless roaming for users moving between buildings. This layer is also where Quality of Service (QoS) policies are applied.
The Access Layer is the edge of the network where client devices connect. It consists of PoE (Power over Ethernet) switches and the physical APs deployed across lecture halls, libraries, student unions, and outdoor quads. High-density APs supporting Wi-Fi 6 (802.11ax) or Wi-Fi 6E are essential for areas with high concurrent device counts.
Security Standards and Authentication
Securing a university network involves balancing robust protection with user accessibility across a complex, multi-tenancy environment.
WPA3 Enterprise and IEEE 802.1X are non-negotiable for securing staff and student connections. 802.1X provides port-based Network Access Control (NAC), ensuring that only authenticated users and devices can access the network. It integrates with a central RADIUS server (such as FreeRADIUS or Microsoft NPS) tied to the university's Active Directory or LDAP directory. This means a student's network credentials are the same as their university login — dramatically reducing helpdesk overheads.
Guest Access and Captive Portals serve visitors, conference attendees, and prospective students. A secure captive portal ensures compliance with GDPR while providing a controlled onboarding experience. Integrating with solutions like Purple allows for seamless guest access while capturing valuable first-party data for marketing and operational use. For a deeper look at securing the network foundation, see Protect Your Network with Strong DNS and Security .
VLAN Segmentation is essential for isolating traffic types. Student traffic, faculty resources, IoT devices (smart building sensors, HVAC controllers), and guest access must reside on separate VLANs. This contains potential security breaches, prevents broadcast storms, and enables granular bandwidth management per user class.
Implementation Guide

Phase 1: Site Survey and RF Planning
Never guess AP placement. A comprehensive predictive and active site survey is the single most important investment in the project. Tools such as Ekahau or AirMagnet should be used to map the physical environment, accounting for building materials (concrete, glass, metal), interference sources (legacy Bluetooth devices, microwave ovens, neighbouring networks), and expected user density per zone. The goal is to ensure adequate coverage and capacity without causing co-channel interference. Predictive models should be validated with active surveys once initial APs are deployed.
Phase 2: Infrastructure and Backhaul Upgrades
Before deploying new APs, the underlying wired infrastructure must be assessed and upgraded where necessary. Ensure CAT6A cabling is deployed to support Multi-Gigabit Ethernet (mGig) required by modern Wi-Fi 6/6E APs. Verify that edge switches can deliver sufficient PoE+ or PoE++ power to the new AP models. The core network must have sufficient bandwidth — consider dedicated business internet connections for resilience. For context on backhaul options, review What Is a Leased Line? Dedicated Business Internet .
Phase 3: Network Architecture Configuration
Configure the WLCs and APs according to the ddesigned architecture. Implement QoS policies to prioritise critical traffic (VoIP, video conferencing, research data transfers) over bulk downloads and streaming. Ensure seamless roaming protocols (802.11r for fast BSS transition, 802.11k for neighbour reports, and 802.11v for BSS transition management) are configured correctly, allowing devices to transition between APs without dropping connections.
Phase 4: Security and Compliance Hardening
Deploy WPA3 Enterprise on staff and student SSIDs. Configure IEEE 802.1X with EAP-TLS or PEAP-MSCHAPv2 depending on device management capabilities. Implement a GDPR-compliant captive portal for guest SSIDs. Ensure all management interfaces are secured with strong credentials and certificate-based authentication. Conduct a penetration test before going live.
Phase 5: Analytics Integration and Ongoing Optimisation
Integrate the network with an analytics platform to gain visibility into AP health, client density, roaming patterns, and bandwidth utilisation. Purple's WiFi Analytics platform provides operational dashboards that benefit both the IT team and venue operations. This is not a one-time exercise — RF environments change as buildings are refurbished and device types evolve.
Best Practices
Design for Capacity, Not Just Coverage. In higher education, coverage is easy; capacity is hard. A lecture hall might have strong signal everywhere, but if 300 students connect simultaneously to a single AP, the network will fail. Deploy high-density APs and utilise features like band steering to push capable clients to the less congested 5 GHz or 6 GHz bands. Disable legacy data rates (1, 2, 5.5, and 11 Mbps) to force sticky clients to roam to closer APs.
Implement Continuous Monitoring. The network is not a set-and-forget deployment. Utilise analytics platforms to monitor AP health, client density, and roaming patterns in real time. Purple's analytics can provide insights into how spaces are used, informing future infrastructure decisions and space utilisation strategies.
Leverage OpenRoaming for Seamless Onboarding. For visiting academics and students from partner institutions, implementing OpenRoaming removes the friction of manual network login. Purple acts as a free identity provider for OpenRoaming under the Connect licence, allowing users from participating institutions to connect automatically and securely — a significant enhancement to the visitor experience.
Segment Everything. Never allow guest traffic on the same VLAN as internal resources. Use separate SSIDs, VLANs, and firewall rules for each user class. Apply bandwidth caps to guest VLANs to prevent a single user from saturating the uplink during peak periods.
Troubleshooting & Risk Mitigation
Co-Channel Interference (CCI) occurs when multiple APs on the same channel can hear each other, causing them to take turns transmitting and severely degrading performance. This is the most common cause of poor WiFi in dense deployments. Mitigation involves proper RF planning, utilising dynamic channel assignment (DCA) features on the WLC, and reducing transmit power on APs in dense areas.
Sticky Clients are devices that refuse to roam to a closer AP, maintaining a weak connection to a distant one. This is particularly common with older smartphones and laptops. Mitigation involves adjusting minimum mandatory data rates — disabling lower rates forces the client's driver to seek a better connection.
DHCP Exhaustion is a surprisingly common failure mode in high-turnover areas like outdoor quads and student unions. When the DHCP pool runs out of IP addresses, new devices cannot connect despite having a strong signal. Mitigation involves implementing shorter DHCP lease times (one to two hours) for guest and student VLANs, and ensuring DHCP scopes are correctly sized for peak concurrent device counts.
Rogue Access Points pose a significant security risk. An employee or student plugging in a consumer-grade router creates an unsecured entry point. Mitigation involves enabling rogue AP detection on the WLC and conducting periodic physical audits.
ROI & Business Impact
A robust campus WiFi network delivers measurable returns beyond basic connectivity. By integrating platforms like Purple, universities can quantify the following outcomes:
| Metric | Measurement Approach | Typical Outcome |
|---|---|---|
| Student Satisfaction | NPS surveys, IT helpdesk ticket volume | Reduction in WiFi-related complaints |
| Space Utilisation | Heatmap analytics, dwell time data | Optimised library and study space allocation |
| IT Operational Efficiency | Helpdesk ticket volume, onboarding time | Reduced manual provisioning overhead |
| Guest Data Capture | Captive portal registrations | First-party marketing database growth |
| Network Uptime | SLA monitoring, incident reports | Improved SLA adherence |
The analytics and guest data capabilities of the Purple platform also open revenue opportunities — particularly during large public events on campus, where tiered access models can be deployed. Similar ROI frameworks apply across Retail , Hospitality , Healthcare , and Transport environments where Purple operates. For a broader perspective on large-venue WiFi deployments, see Airport WiFi: How Operators Deliver Connectivity Across Terminals and WiFi Aeroportuale: Come gli Operatori Forniscono Connettività tra i Terminal .
Key Terms & Definitions
IEEE 802.1X
A standard for port-based Network Access Control (NAC) that provides an authentication mechanism for devices wishing to connect to a LAN or WLAN. It requires a supplicant (client device), an authenticator (the AP or switch), and an authentication server (RADIUS).
Used to authenticate students and staff before they are allowed onto the network, integrating with a RADIUS server and Active Directory for credential validation. Eliminates shared PSK passwords and enables per-user policy enforcement.
WLC (Wireless LAN Controller)
A centralised hardware or software appliance that manages and configures multiple Access Points from a single point of control. It handles RF management, roaming, firmware updates, and policy enforcement across the AP fleet.
Essential for large deployments to ensure consistent policy enforcement, dynamic channel assignment, and seamless roaming across the campus. Can be physical hardware or a cloud-managed virtual instance.
Co-Channel Interference (CCI)
Interference that occurs when two or more APs operating on the same frequency channel are within range of each other. Both APs must wait for the channel to be clear before transmitting, severely reducing throughput.
The primary cause of poor performance in dense deployments. Mitigated by careful channel planning, dynamic channel assignment (DCA) on the WLC, and reducing AP transmit power.
Band Steering
A technique used by APs to encourage dual-band capable client devices to connect to the 5 GHz or 6 GHz band rather than the more congested 2.4 GHz band, by delaying or suppressing probe responses on 2.4 GHz.
Critical for maximising capacity and throughput in high-density areas. The 5 GHz and 6 GHz bands offer more non-overlapping channels and higher throughput, but shorter range.
Captive Portal
A web page that users are redirected to before gaining full network access. It typically requires acceptance of terms of service, authentication, or data capture before the user's MAC address is permitted through the firewall.
Used for guest access management, GDPR-compliant data collection, and branded onboarding experiences. Platforms like Purple provide customisable captive portal solutions with analytics integration.
VLAN (Virtual Local Area Network)
A logical grouping of network devices that behave as if they are on the same physical network, regardless of their actual physical location. VLANs are defined at Layer 2 and are used to segment broadcast domains.
Used to isolate different user classes (students, staff, guests, IoT devices) for security and performance. Prevents guest traffic from reaching internal resources and allows per-VLAN bandwidth policies.
PoE (Power over Ethernet)
A technology that passes electrical power along with data on twisted-pair Ethernet cabling, allowing a single cable to provide both data connection and electrical power to devices such as APs.
Allows APs to be installed in locations without dedicated power outlets. IT teams must verify that edge switches have sufficient PoE budget (total watts) to power all connected APs, particularly with power-hungry Wi-Fi 6E models requiring PoE++ (802.3bt).
OpenRoaming
A global WiFi roaming federation built on the Hotspot 2.0 (Passpoint) standard, allowing users to automatically and securely connect to participating networks without manual login, using their existing identity credentials.
Improves the experience for visiting academics and students from partner institutions. Purple can act as an identity provider for OpenRoaming under the Connect licence, enabling automatic secure connections for eligible users.
WPA3 Enterprise
The latest generation of the Wi-Fi Protected Access security protocol for enterprise networks. It uses 192-bit minimum-strength security protocols and mandates the use of Protected Management Frames (PMF), providing stronger protection against offline dictionary attacks.
The recommended security standard for all staff and student SSIDs. Replaces WPA2 Enterprise and provides significantly stronger protection for sensitive research and personal data transmitted over the wireless network.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service.
The backbone of 802.1X authentication on campus networks. The RADIUS server validates credentials against Active Directory and returns the appropriate VLAN assignment and access policy for each authenticated user.
Case Studies
A large university is upgrading its main lecture theatre (capacity 500) to Wi-Fi 6. The previous deployment used 4 APs mounted on the high ceiling, resulting in poor performance and frequent disconnects during peak times. What is the correct approach?
The IT team must shift from a coverage-centric design to a capacity-centric one. First, conduct a new site survey specifically for the lecture theatre, modelling the expected device count (assume 1,000+ devices given 2+ devices per student). Replace the ceiling-mounted omni-directional APs with either under-seat AP deployments or directional (patch) antenna arrays mounted on the side walls, creating smaller, focused micro-cells. Increase the AP count to 8-12 Wi-Fi 6 APs, each serving a defined section of seating. Disable 2.4 GHz radios on alternating APs to reduce co-channel interference, relying primarily on 5 GHz and 6 GHz bands. Implement strict band steering and disable legacy data rates below 12 Mbps. Configure the WLC to use 20 MHz channel widths in the 5 GHz band (rather than 40 or 80 MHz) to allow more non-overlapping channels and reduce interference.
A campus network is experiencing intermittent connectivity issues in the outdoor quad area. Users report strong signal but inability to load web pages during the lunch period (12:00-13:30). What is the diagnostic approach?
Strong signal with no connectivity is a Layer 2/3 issue, not an RF problem. The diagnostic sequence should be: (1) Check the DHCP scope for the outdoor VLAN — query the DHCP server for scope utilisation. If it is above 80%, DHCP exhaustion is the likely cause. Reduce lease times to 1 hour and expand the scope if possible. (2) If DHCP is healthy, check the uplink capacity of the outdoor distribution switch. If the APs are connected via a congested uplink, the bottleneck is wired, not wireless. (3) Analyse the RF environment for external interference using a spectrum analyser — municipal WiFi networks or nearby businesses may be causing noise floor elevation. (4) Review the firewall and NAT table for session exhaustion during peak periods.
Scenario Analysis
Q1. A university is planning to deploy WiFi in a newly constructed outdoor sports stadium with a capacity of 8,000 spectators. The stadium has no roof and an open bowl design. What is the most critical RF consideration and how should AP placement be approached?
💡 Hint:Consider the lack of physical boundaries, signal propagation in an open environment, and the extreme device density during events.
Show Recommended Approach
The most critical consideration is controlling signal propagation and minimising Co-Channel Interference in an environment with no natural RF attenuation. Unlike indoor environments, the open bowl means signals travel freely, causing APs to interfere with each other across the entire space. The correct approach is to use directional (sector) antennas mounted under the seating tiers, pointing downward into the seating rows to create highly focused micro-cells. Transmit power must be carefully tuned to limit cell size. Wi-Fi 6 APs with OFDMA and BSS Colouring features should be specified to handle the extreme device density. Separate SSIDs and VLANs should be configured for event staff, media, and public attendees.
Q2. During a network upgrade, the IT team notices that older IoT devices (legacy HVAC sensors and door access controllers) are failing to connect to the new campus WiFi network after the security upgrade to WPA3 Enterprise.
💡 Hint:Consider the security protocol compatibility of legacy embedded devices and the need to maintain security for other user classes.
Show Recommended Approach
The new network enforcing WPA3 Enterprise is incompatible with older IoT devices that only support WPA2 or earlier protocols. The solution is to create a dedicated, isolated SSID and VLAN specifically for legacy IoT devices, utilising WPA2-PSK with a strong, rotated passphrase, or MAC Authentication Bypass (MAB) for devices that cannot support any EAP method. This VLAN must be tightly firewalled — IoT devices should only be able to communicate with their specific management servers, not the broader campus network. The main student and staff SSIDs remain on WPA3 Enterprise, maintaining security for the primary user population.
Q3. The university wants to monetise its guest WiFi network during large public events (open days, graduation ceremonies, public lectures) while remaining GDPR-compliant. What is the recommended architecture?
💡 Hint:Consider data capture requirements, consent mechanisms, and the difference between free and premium access tiers.
Show Recommended Approach
Deploy a captive portal solution such as Purple integrated with the guest VLAN. Configure a tiered access model: a free tier offering basic internet access (with bandwidth caps) in exchange for email address and explicit GDPR-compliant marketing consent, and an optional premium tier offering higher bandwidth for a fee (processed via a payment gateway integration). The captive portal must display a clear privacy notice and record consent timestamps to satisfy GDPR Article 7 requirements. Captured first-party data feeds into the university's CRM for post-event marketing. All guest traffic must be isolated from internal university systems via firewall rules, and data retention policies must be documented and enforced.
Q4. The IT team receives complaints that WiFi performance in the main library is poor between 10:00 and 14:00 on weekdays, despite the network showing healthy AP status in the management console. How should the team approach diagnosis?
💡 Hint:Consider time-based patterns and what changes between off-peak and peak hours.
Show Recommended Approach
The time-based pattern is the key diagnostic clue — the issue only occurs during peak occupancy hours, suggesting a capacity problem rather than a hardware or configuration fault. The diagnostic sequence should be: (1) Check per-AP client association counts during the problem window — if any AP is serving more than 30-40 clients simultaneously, it is overloaded. (2) Review DHCP scope utilisation for the library VLAN. (3) Check uplink utilisation on the distribution switch serving the library — the wired backhaul may be saturated. (4) Review the channel utilisation and retry rates on the APs using the WLC's RF statistics. The likely resolution is either deploying additional APs to distribute the client load, or implementing stricter band steering and minimum data rate policies to improve per-client throughput.



