Zero Trust Network Access: Estratégias de Implementação e Melhores Práticas
Este guia de referência técnica fornece a líderes de TI e arquitetos de rede um plano pragmático para a implementação de Zero Trust Network Access (ZTNA) em ambientes corporativos. Ele abrange a arquitetura central, estratégias de microssegmentação e metodologias de implantação passo a passo para proteger ambientes complexos sem interromper as operações.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada
- Controle de Acesso Baseado em Identidade
- Verificação da Postura do Dispositivo
- Autenticação Contínua e Detecção de Ameaças
- Guia de Implementação
- Fase 1: Descoberta e Classificação
- Fase 2: Design de Segmentação
- Fase 3: Integração de Identidade
- Fase 4: Lançamento da Política (Modo de Monitoramento)
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios

Resumo Executivo
O modelo de segurança tradicional baseado em perímetro está obsoleto. Para ambientes corporativos — desde hotéis de 500 quartos a grandes propriedades de varejo e estádios de alta densidade — a suposição de que o tráfego de rede interno é inerentemente confiável representa uma vulnerabilidade crítica. Zero Trust Network Access (ZTNA) substitui essa suposição falha por uma estrutura rigorosa e orientada por identidade: verifique tudo, não confie em nada por padrão e aplique o acesso de menor privilégio em todas as camadas.
Este guia de referência fornece a gerentes de TI, arquitetos de rede e diretores de operações de locais um plano pragmático para a implementação de Zero Trust Network Access. Ele remove a teoria acadêmica para focar nas realidades da implantação: integrar provedores de identidade, aplicar microssegmentação em ambientes legados complexos e gerenciar a verificação da postura do dispositivo para endpoints corporativos gerenciados e dispositivos de convidados não gerenciados. Ao implementar essas estratégias, os locais podem proteger sua infraestrutura de Guest WiFi , isolar sistemas de pagamento para manter a conformidade com PCI DSS e proteger tecnologias operacionais críticas sem degradar a experiência do usuário.
Análise Técnica Detalhada
Uma arquitetura robusta de Zero Trust Network Access depende da orquestração de vários componentes centrais, deslocando o perímetro de segurança da borda da rede para a identidade e o dispositivo individual.
Controle de Acesso Baseado em Identidade
Em um modelo ZTNA, as decisões de acesso são inteiramente baseadas em identidade verificada, e não na localização da rede. Um usuário conectando-se a uma porta de switch em um escritório de retaguarda não recebe mais confiança inerente do que um convidado conectando-se a um ponto de acesso público. Em ambientes de locais, as políticas de identidade devem acomodar populações de usuários altamente divergentes.
Para funcionários e contratados, a autenticação geralmente depende de IEEE 802.1X vinculado a um diretório central (por exemplo, Active Directory ou Azure AD). Para usuários convidados, a asserção de identidade ocorre por meio de captive portals ou mecanismos de login social. A plataforma Purple atua como um provedor de identidade crítico neste contexto, capturando a identidade verificada no ponto de conexão e passando esse contexto para os pontos de aplicação de políticas a jusante.
Verificação da Postura do Dispositivo
A identidade sozinha é insuficiente; o endpoint de conexão também deve ser validado. A verificação da postura do dispositivo avalia o estado de segurança do dispositivo antes de conceder acesso. Para dispositivos corporativos gerenciados, isso envolve a verificação de proteção de endpoint ativa, níveis de patch do sistema operacional e registro em MDM.
Para dispositivos não gerenciados — como aqueles em redes Guest WiFi — a verificação de postura é limitada, exigindo uma política de negação por padrão para roteamento interno. Esses dispositivos são colocados em um segmento isolado com acesso apenas à internet. O motor de políticas avalia esses parâmetros dinamicamente no momento da conexão e continuamente durante a sessão.
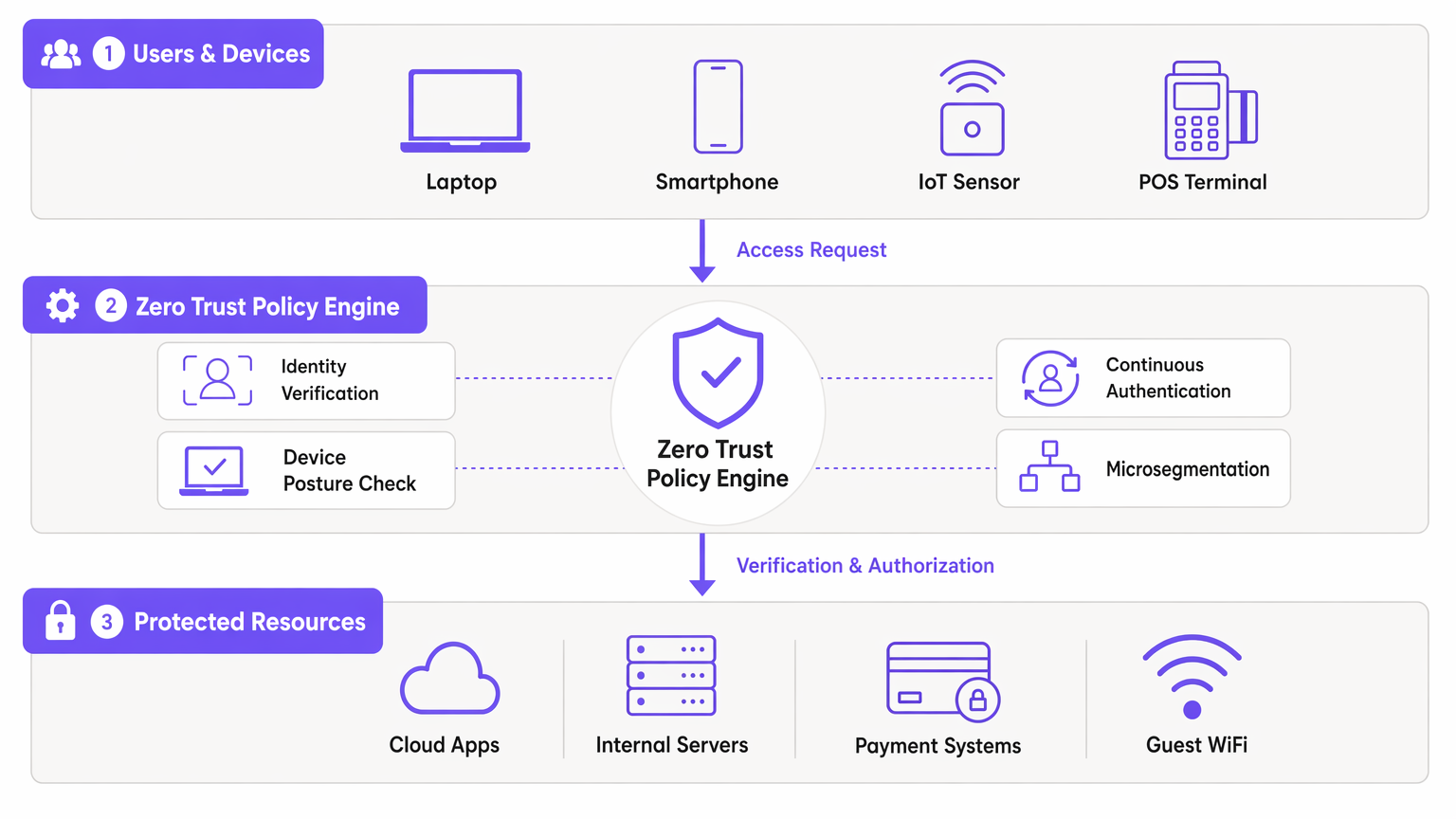
Autenticação Contínua e Detecção de Ameaças
Redes tradicionais autenticam uma vez e mantêm a sessão indefinidamente. O ZTNA exige autenticação contínua. O motor de políticas monitora o comportamento da sessão, volumes de dados e uso de protocolo. Padrões anômalos acionam reautenticação ou término imediato da sessão. Essa telemetria alimenta plataformas SIEM, permitindo a detecção de ameaças em tempo real e resposta rápida a tentativas de movimento lateral.
Guia de Implementação
A implantação de ZTNA em um ambiente de local em operação requer uma abordagem faseada e metódica para evitar interrupções operacionais.
Fase 1: Descoberta e Classificação
Antes de modificar as políticas, você deve estabelecer um inventário abrangente de todos os dispositivos, usuários e cargas de trabalho. Em locais como Hospitality ou Retail , dispositivos IoT não documentados e sistemas legados são comuns. Utilize ferramentas de descoberta de rede para mapear os fluxos de tráfego existentes e identificar todos os endpoints conectados.
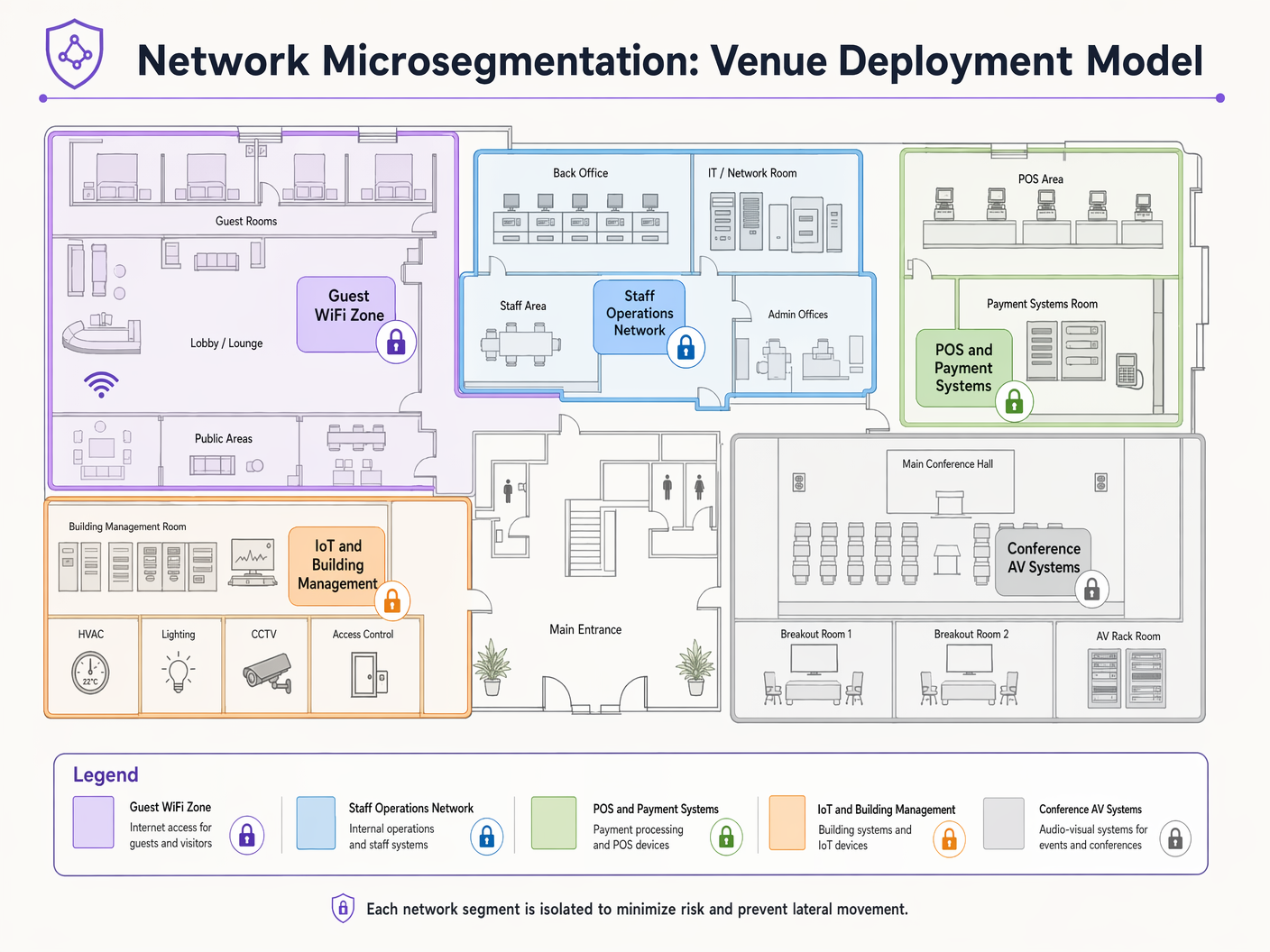
Fase 2: Design de Segmentação
Mapeie os segmentos de rede para funções de negócios e requisitos de conformidade. Um local típico requer segmentos distintos para:
- Guest WiFi: Acesso apenas à internet.
- Operações da Equipe: Acesso a aplicativos internos.
- Sistemas de Pagamento (POS): Estritamente isolados para conformidade com PCI DSS.
- Gerenciamento de Edifícios/IoT: Restrito a servidores de controle necessários.
Defina os fluxos de tráfego permitidos entre esses segmentos usando uma postura de negação por padrão.
Fase 3: Integração de Identidade
Integre seu motor de políticas ZTNA com seus provedores de identidade. Conecte diretórios corporativos para funcionários e configure plataformas de acesso de convidados para afirmar as identidades dos convidados. Garanta que os mecanismos de autenticação baseados em perfil sejam robustos e escaláveis para lidar com a capacidade máxima do local.
Fase 4: Lançamento da Política (Modo de Monitoramento)
Implante as políticas inicialmente no modo somente observação. Isso fornece visibilidade do tráfego que seria bloqueado, permitindo que você refine as regras sem interromper processos de negócios legítimos. Após um período de monitoramento de 2 a 4 semanas, faça a transição para o modo de aplicação.
Melhores Práticas
- Assuma a Violação: Projete sua rede sob a premissa de que um invasor já comprometeu um endpoint. A microssegmentação é sua principal defesa contra o movimento lateral.
- Aproveite 802.1X e WPA3: Implemente autenticação e criptografia robustas na camada de acesso. Consulte guias sobre Solução de problemas de autenticação 802.1X no Windows 11 para suporte de implantação.
- Automatize a Identidade do Convidado: Utilize plataformas que capturem e verifiquem identidades de convidados de forma contínua, sem introduzir atrito excessivo. Ver Protegendo Redes WiFi de Convidados: Melhores Práticas e Implementação .
- Isole Dispositivos IoT: Sensores IoT e sistemas de gerenciamento de edifícios raramente precisam de acesso à internet ou roteamento entre segmentos. Isole-os estritamente.
Solução de Problemas e Mitigação de Riscos
O modo de falha mais comum na implementação de acesso à rede de confiança zero é a aplicação agressiva de políticas sem descoberta adequada. Isso leva ao bloqueio de tráfego crítico para os negócios e ao retrocesso do projeto.
Risco: Dispositivos legados (por exemplo, terminais POS antigos ou controladores HVAC) podem não suportar protocolos de autenticação modernos. Mitigação: Utilize MAC Authentication Bypass (MAB) combinado com microsegmentação e perfilagem rigorosas para integrar esses dispositivos de forma segura, sem comprometer a arquitetura ZTNA mais ampla.
Risco: O desempenho da rede de convidados degrada devido à sobrecarga pesada da aplicação de políticas. Mitigação: Descarregue o roteamento de tráfego de convidados diretamente para a internet na borda, ignorando motores de inspeção interna profunda, a menos que informações específicas de ameaças indiquem o contrário.
ROI e Impacto nos Negócios
A implementação de ZTNA oferece valor de negócio mensurável além da redução de riscos:
- Redução de Custos de Conformidade: Ao isolar estritamente o Ambiente de Dados do Titular do Cartão (CDE) através da microssegmentação, os locais reduzem significativamente o escopo e o custo das auditorias PCI DSS.
- Resiliência Operacional: Conter violações a um único segmento evita interrupções em todo o local, protegendo fluxos de receita durante as horas de pico operacional.
- Análise Aprimorada: Os dados granulares de identidade e tráfego gerados pelas políticas ZTNA enriquecem Análise de WiFi , fornecendo insights mais profundos sobre o comportamento do usuário e a utilização da rede.
Definições principais
Microsegmentation
The practice of dividing a network into isolated segments to reduce the attack surface and prevent lateral movement.
Critical for venue IT teams to isolate POS systems from Guest WiFi and staff networks, ensuring compliance and containing potential breaches.
Device Posture Verification
The process of assessing an endpoint's security state (e.g., OS version, antivirus status) before granting network access.
Used to ensure that unpatched or compromised staff devices cannot access sensitive internal applications.
Continuous Authentication
The ongoing monitoring of a user's session to ensure their identity and behavior remain valid and non-anomalous.
Vital in high-turnover environments like stadiums to detect session hijacking or unusual data exfiltration attempts.
IEEE 802.1X
A standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol used by network architects to authenticate corporate devices securely.
Lateral Movement
Techniques that cyber attackers use to progressively move through a network as they search for key data and assets.
The primary threat that ZTNA and microsegmentation are designed to neutralize in flat legacy networks.
Software-Defined Perimeter (SDP)
A security approach that hides internet-connected infrastructure so that external parties and attackers cannot see it, whether it is hosted on-premises or in the cloud.
Often used as the technical implementation mechanism for deploying ZTNA access policies.
Least-Privilege Access
The security principle of granting users and systems only the minimum level of access necessary to perform their required functions.
The guiding policy framework IT managers must use when defining rules within the ZTNA policy engine.
MAC Authentication Bypass (MAB)
A fallback authentication method that uses a device's MAC address to grant network access when 802.1X is not supported.
Used pragmatically by network teams to onboard legacy IoT devices (like old printers or HVAC systems) into isolated network segments.
Exemplos práticos
A 400-room hotel needs to deploy new smart TVs in all guest rooms. These devices require internet access for streaming services and local network access to the property management system (PMS) for personalized greetings and billing review. How should this be implemented under a ZTNA model?
- Place all smart TVs in a dedicated 'Guest Room Entertainment' microsegment. 2. Configure policies to allow outbound internet access for streaming. 3. Implement a strict, unidirectional API gateway policy allowing the TVs to query the PMS on specific ports (e.g., HTTPS/443) only for the required endpoints. 4. Deny all lateral traffic between individual TVs and deny all inbound traffic from the internet.
A large retail chain is rolling out mobile Point of Sale (mPOS) tablets for staff on the shop floor. These tablets connect via WiFi. How do you secure this deployment?
- Authenticate the tablets using certificate-based IEEE 802.1X (EAP-TLS). 2. Implement device posture checks via MDM integration to ensure the tablet is compliant (patched, unrooted) before granting access. 3. Assign the tablets dynamically to a highly restricted 'mPOS' VLAN/segment. 4. Allow traffic only to the specific payment gateway IP addresses and internal inventory APIs.
Questões práticas
Q1. A stadium IT director wants to allow third-party vendors (e.g., catering staff) to access their own cloud-based inventory systems via the stadium's WiFi. How should this be configured?
Dica: Consider the difference between corporate data access and internet-only access for third parties.
Ver resposta modelo
Create a dedicated 'Vendor WiFi' SSID and microsegment. Authenticate vendors using a captive portal or unique pre-shared keys (WPA3-SAE). Configure the segment policy to allow outbound internet access only, strictly denying any routing to the stadium's internal operational networks or POS systems.
Q2. During a ZTNA rollout, the operations team reports that several legacy barcode scanners in the warehouse have stopped working. What is the likely cause and immediate solution?
Dica: Think about what happens when devices cannot support modern authentication protocols.
Ver resposta modelo
The scanners likely do not support 802.1X authentication and were blocked by the new default-deny policy. The immediate solution is to implement MAC Authentication Bypass (MAB) for the specific MAC addresses of the scanners and place them in a highly restricted microsegment that only allows traffic to the inventory database server.
Q3. A CTO asks you to justify the cost of implementing microsegmentation across a 50-site retail estate. What is the primary business justification?
Dica: Focus on risk containment and compliance impact.
Ver resposta modelo
The primary justification is risk containment and compliance scope reduction. By microsegmenting the network, a breach in a less secure segment (like an IoT device or Guest WiFi) cannot spread to the Cardholder Data Environment (CDE). This dramatically reduces the scope, complexity, and cost of annual PCI DSS audits, while preventing a localized incident from becoming a company-wide data breach.
Continue a ler esta série
Como Configurar SCEP para BYOD Seguro e Autenticação de Rede 802.1X
Este guia fornece uma referência técnica abrangente para configurar o SCEP para implantar autenticação de rede 802.1X baseada em certificados. Ele aborda a transição arquitetônica de senhas compartilhadas para EAP-TLS, integração com Gerenciamento de Dispositivos Móveis (MDM) e segmentação estrita de rede para acesso BYOD seguro em ambientes corporativos.
Guia de Configuração de WiFi de Visitantes Corporativo: Segmentação de VLAN, Segurança e Captive Portals
Este guia fornece um modelo técnico para a implantação de WiFi de visitantes corporativo, com foco em segmentação de VLAN, protocolos de segurança e arquitetura de captive portal. Ele detalha como isolar o tráfego, aplicar padrões de criptografia e capturar dados primários de forma segura em locais complexos.
Como configurar WiFi de convidados e Captive Portals na Ruijie Networks
Este guia técnico detalha a configuração de WiFi de convidados e Captive Portals em hardware da Ruijie Networks, abrangendo tanto portais em nuvem nativos quanto integrações RADIUS externas. Ele fornece aos gerentes de TI e arquitetos de rede etapas práticas para isolamento de VLAN, configuração de walled garden e integração de plataformas de terceiros para impulsionar análises e receita.