Zero Trust Network Access: Implementation Strategies and Best Practices
This technical reference guide provides IT leaders and network architects with a pragmatic blueprint for Zero Trust Network Access (ZTNA) implementation in enterprise venues. It covers core architecture, microsegmentation strategies, and step-by-step deployment methodologies to secure complex environments without disrupting operations.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- Identity-Based Access Control
- Device Posture Verification
- Continuous Authentication and Threat Detection
- Implementation Guide
- Phase 1: Discovery and Classification
- Phase 2: Segmentation Design
- Phase 3: Identity Integration
- Phase 4: Policy Rollout (Monitoring Mode)
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
The traditional perimeter-based security model is obsolete. For enterprise venues—from 500-room hotels to sprawling retail estates and high-density stadiums—the assumption that internal network traffic is inherently trustworthy represents a critical vulnerability. Zero Trust Network Access (ZTNA) replaces this flawed assumption with a rigorous, identity-driven framework: verify everything, trust nothing by default, and enforce least-privilege access at every layer.
This reference guide provides IT managers, network architects, and venue operations directors with a pragmatic blueprint for zero trust network access implementation. It strips away academic theory to focus on deployment realities: integrating identity providers, enforcing microsegmentation across complex legacy environments, and managing device posture verification for both managed corporate endpoints and unmanaged guest devices. By implementing these strategies, venues can secure their Guest WiFi infrastructure, isolate payment systems to maintain PCI DSS compliance, and protect critical operational technology without degrading the user experience.
Technical Deep-Dive
A robust Zero Trust Network Access architecture relies on the orchestration of several core components, shifting the security perimeter from the network edge to the individual identity and device.
Identity-Based Access Control
In a ZTNA model, access decisions are predicated entirely on verified identity rather than network location. A user connecting to a switch port in a back office receives no more inherent trust than a guest connecting to a public access point. In venue environments, identity policies must accommodate highly divergent user populations.
For staff and contractors, authentication typically relies on IEEE 802.1X tied to a central directory (e.g., Active Directory or Azure AD). For guest users, identity assertion occurs via captive portals or social login mechanisms. Purple's platform acts as a critical identity provider in this context, capturing verified identity at the point of connection and passing this context to downstream policy enforcement points.
Device Posture Verification
Identity alone is insufficient; the connecting endpoint must also be validated. Device posture verification assesses the security state of the device before granting access. For managed corporate devices, this involves checking for active endpoint protection, OS patch levels, and MDM enrollment.
For unmanaged devices—such as those on Guest WiFi networks—posture checking is limited, necessitating a default-deny policy for internal routing. These devices are placed in an isolated segment with internet-only access. The policy engine evaluates these parameters dynamically at connection time and continuously throughout the session.
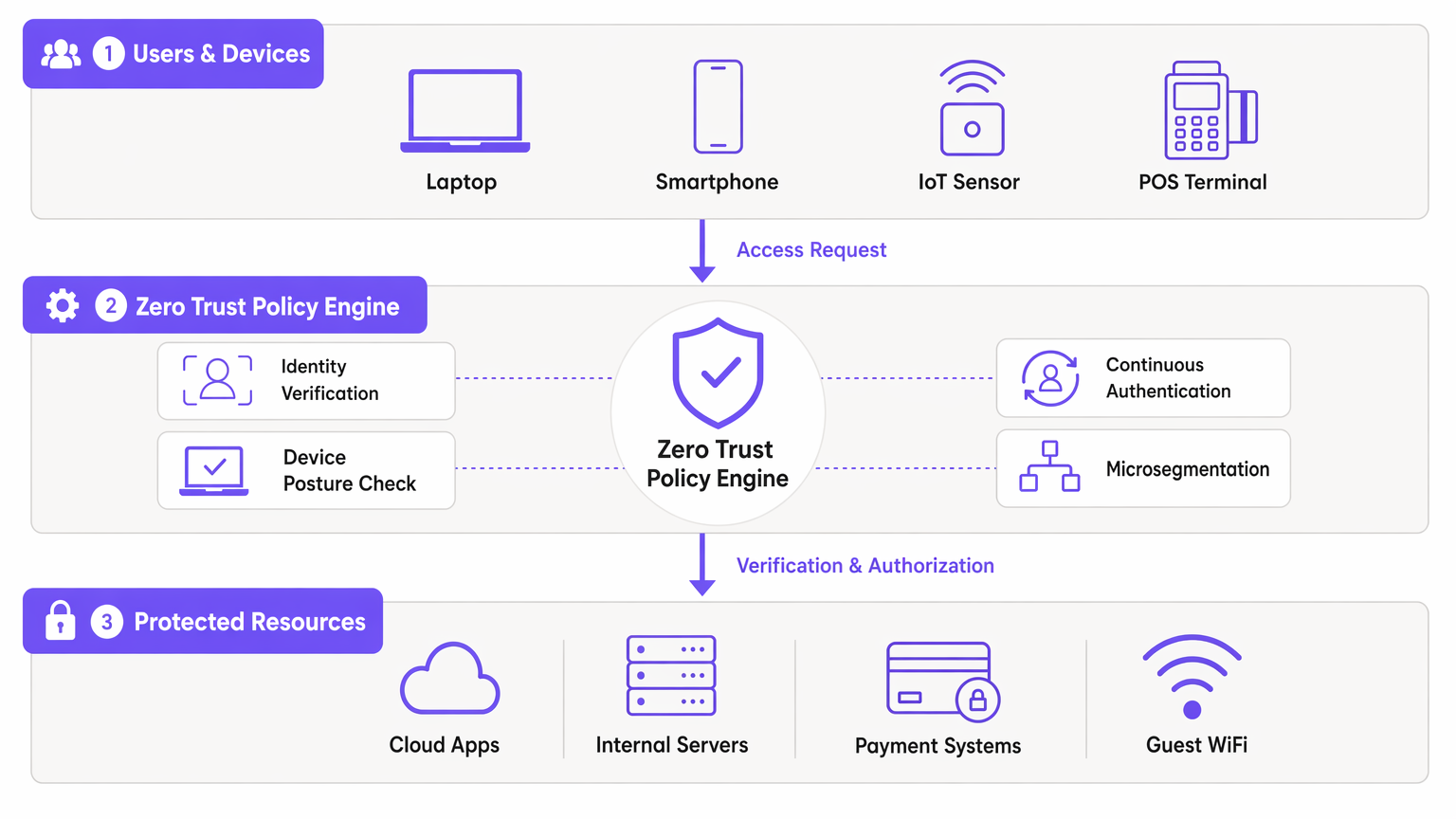
Continuous Authentication and Threat Detection
Traditional networks authenticate once and maintain the session indefinitely. ZTNA mandates continuous authentication. The policy engine monitors session behaviour, data volumes, and protocol usage. Anomalous patterns trigger re-authentication or immediate session termination. This telemetry feeds into SIEM platforms, enabling real-time threat detection and rapid response to lateral movement attempts.
Implementation Guide
Deploying ZTNA in a live venue environment requires a phased, methodical approach to avoid operational disruption.
Phase 1: Discovery and Classification
Before modifying policies, you must establish a comprehensive inventory of all devices, users, and workloads. In venues like Hospitality or Retail , undocumented IoT devices and legacy systems are common. Utilize network discovery tooling to map existing traffic flows and identify all connected endpoints.
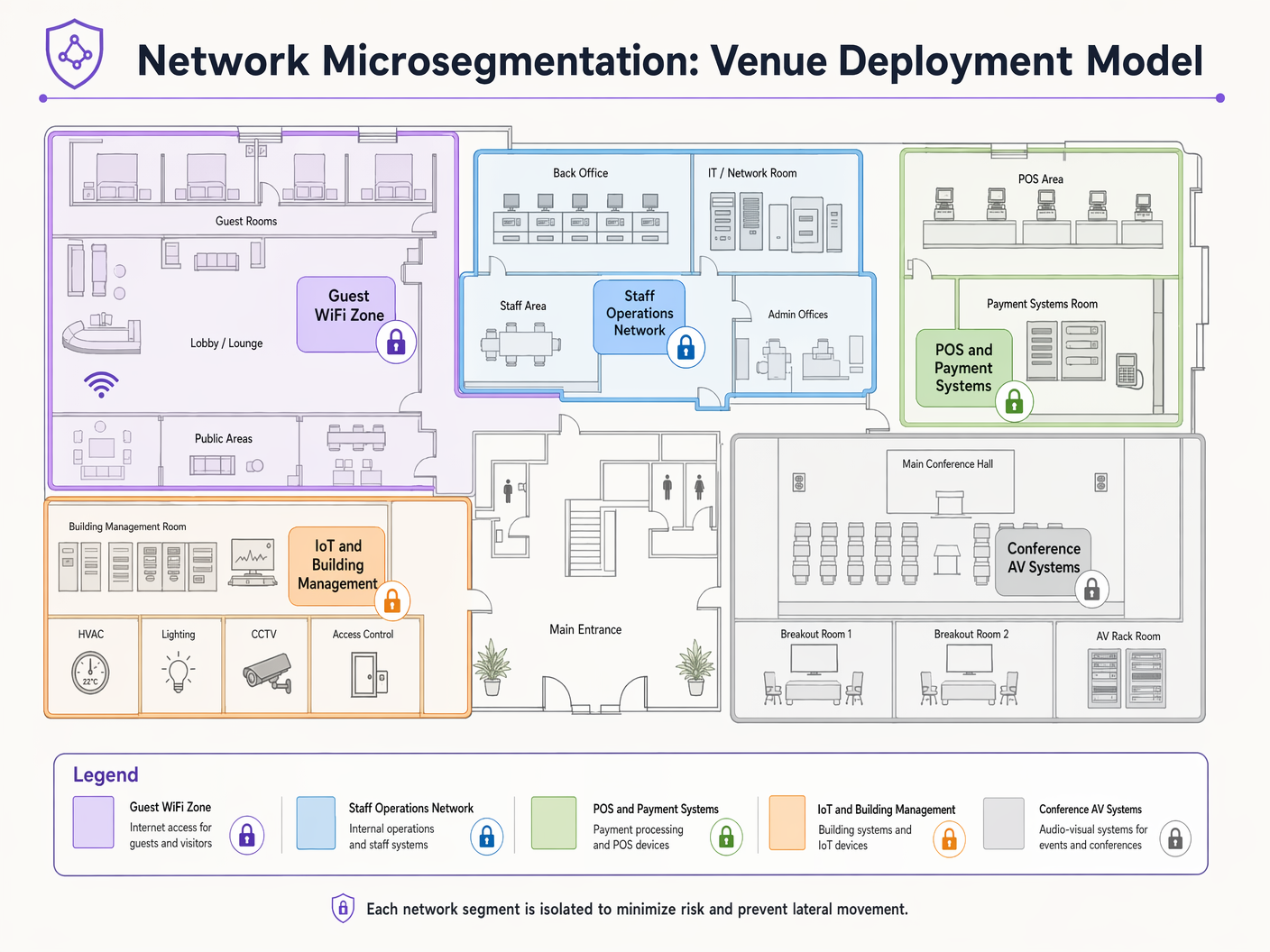
Phase 2: Segmentation Design
Map network segments to business functions and compliance requirements. A typical venue requires distinct segments for:
- Guest WiFi: Internet-only access.
- Staff Operations: Access to internal applications.
- Payment Systems (POS): Strictly isolated for PCI DSS compliance.
- Building Management/IoT: Restricted to necessary control servers.
Define permitted traffic flows between these segments using a default-deny stance.
Phase 3: Identity Integration
Integrate your ZTNA policy engine with your identity providers. Connect corporate directories for staff and configure guest access platforms to assert guest identities. Ensure that profile-based authentication mechanisms are robust and scalable to handle peak venue capacity.
Phase 4: Policy Rollout (Monitoring Mode)
Deploy policies in observe-only mode initially. This provides visibility into traffic that would be blocked, allowing you to refine rules without breaking legitimate business processes. After a 2-4 week monitoring period, transition to enforcement mode.
Best Practices
- Assume Breach: Design your network under the assumption that an attacker has already compromised an endpoint. Microsegmentation is your primary defense against lateral movement.
- Leverage 802.1X and WPA3: Implement robust authentication and encryption at the access layer. Refer to guides on Troubleshooting Windows 11 802.1X Authentication Issues for deployment support.
- Automate Guest Identity: Utilize platforms that seamlessly capture and verify guest identities without introducing excessive friction. See Securing Guest WiFi Networks: Best Practices and Implementation .
- Isolate IoT Devices: IoT sensors and building management systems rarely need internet access or cross-segment routing. Isolate them strictly.
Troubleshooting & Risk Mitigation
The most common failure mode in zero trust network access implementation is aggressive policy enforcement without adequate discovery. This leads to blocked business-critical traffic and project rollback.
Risk: Legacy devices (e.g., old POS terminals or HVAC controllers) may not support modern authentication protocols. Mitigation: Utilize MAC Authentication Bypass (MAB) combined with strict microsegmentation and profiling to securely onboard these devices without compromising the broader ZTNA architecture.
Risk: Guest network performance degrades due to heavy policy enforcement overhead. Mitigation: Offload guest traffic routing directly to the internet at the edge, bypassing deep internal inspection engines unless specific threat intelligence indicates otherwise.
ROI & Business Impact
Implementing ZTNA delivers measurable business value beyond risk reduction:
- Compliance Cost Reduction: By strictly isolating the Cardholder Data Environment (CDE) through microsegmentation, venues significantly reduce the scope and cost of PCI DSS audits.
- Operational Resilience: Containing breaches to a single segment prevents venue-wide outages, protecting revenue streams during peak operational hours.
- Enhanced Analytics: The granular identity and traffic data generated by ZTNA policies enriches WiFi Analytics , providing deeper insights into user behaviour and network utilization.
Key Definitions
Microsegmentation
The practice of dividing a network into isolated segments to reduce the attack surface and prevent lateral movement.
Critical for venue IT teams to isolate POS systems from Guest WiFi and staff networks, ensuring compliance and containing potential breaches.
Device Posture Verification
The process of assessing an endpoint's security state (e.g., OS version, antivirus status) before granting network access.
Used to ensure that unpatched or compromised staff devices cannot access sensitive internal applications.
Continuous Authentication
The ongoing monitoring of a user's session to ensure their identity and behavior remain valid and non-anomalous.
Vital in high-turnover environments like stadiums to detect session hijacking or unusual data exfiltration attempts.
IEEE 802.1X
A standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol used by network architects to authenticate corporate devices securely.
Lateral Movement
Techniques that cyber attackers use to progressively move through a network as they search for key data and assets.
The primary threat that ZTNA and microsegmentation are designed to neutralize in flat legacy networks.
Software-Defined Perimeter (SDP)
A security approach that hides internet-connected infrastructure so that external parties and attackers cannot see it, whether it is hosted on-premises or in the cloud.
Often used as the technical implementation mechanism for deploying ZTNA access policies.
Least-Privilege Access
The security principle of granting users and systems only the minimum level of access necessary to perform their required functions.
The guiding policy framework IT managers must use when defining rules within the ZTNA policy engine.
MAC Authentication Bypass (MAB)
A fallback authentication method that uses a device's MAC address to grant network access when 802.1X is not supported.
Used pragmatically by network teams to onboard legacy IoT devices (like old printers or HVAC systems) into isolated network segments.
Worked Examples
A 400-room hotel needs to deploy new smart TVs in all guest rooms. These devices require internet access for streaming services and local network access to the property management system (PMS) for personalized greetings and billing review. How should this be implemented under a ZTNA model?
- Place all smart TVs in a dedicated 'Guest Room Entertainment' microsegment. 2. Configure policies to allow outbound internet access for streaming. 3. Implement a strict, unidirectional API gateway policy allowing the TVs to query the PMS on specific ports (e.g., HTTPS/443) only for the required endpoints. 4. Deny all lateral traffic between individual TVs and deny all inbound traffic from the internet.
A large retail chain is rolling out mobile Point of Sale (mPOS) tablets for staff on the shop floor. These tablets connect via WiFi. How do you secure this deployment?
- Authenticate the tablets using certificate-based IEEE 802.1X (EAP-TLS). 2. Implement device posture checks via MDM integration to ensure the tablet is compliant (patched, unrooted) before granting access. 3. Assign the tablets dynamically to a highly restricted 'mPOS' VLAN/segment. 4. Allow traffic only to the specific payment gateway IP addresses and internal inventory APIs.
Practice Questions
Q1. A stadium IT director wants to allow third-party vendors (e.g., catering staff) to access their own cloud-based inventory systems via the stadium's WiFi. How should this be configured?
Hint: Consider the difference between corporate data access and internet-only access for third parties.
View model answer
Create a dedicated 'Vendor WiFi' SSID and microsegment. Authenticate vendors using a captive portal or unique pre-shared keys (WPA3-SAE). Configure the segment policy to allow outbound internet access only, strictly denying any routing to the stadium's internal operational networks or POS systems.
Q2. During a ZTNA rollout, the operations team reports that several legacy barcode scanners in the warehouse have stopped working. What is the likely cause and immediate solution?
Hint: Think about what happens when devices cannot support modern authentication protocols.
View model answer
The scanners likely do not support 802.1X authentication and were blocked by the new default-deny policy. The immediate solution is to implement MAC Authentication Bypass (MAB) for the specific MAC addresses of the scanners and place them in a highly restricted microsegment that only allows traffic to the inventory database server.
Q3. A CTO asks you to justify the cost of implementing microsegmentation across a 50-site retail estate. What is the primary business justification?
Hint: Focus on risk containment and compliance impact.
View model answer
The primary justification is risk containment and compliance scope reduction. By microsegmenting the network, a breach in a less secure segment (like an IoT device or Guest WiFi) cannot spread to the Cardholder Data Environment (CDE). This dramatically reduces the scope, complexity, and cost of annual PCI DSS audits, while preventing a localized incident from becoming a company-wide data breach.
Continue reading in this series
Mitigating RADIUS Vulnerabilities: A Security Hardening Guide
This guide provides a comprehensive, actionable reference for IT managers, network architects, and CTOs responsible for enterprise WiFi infrastructure across hospitality, retail, events, and public-sector environments. It covers the full attack surface of RADIUS server deployments — from MD5 collision vulnerabilities and weak shared secrets to unencrypted UDP transport and misconfigured EAP methods — and delivers a prioritised hardening roadmap aligned with IEEE 802.1X, PCI DSS, and GDPR requirements. Organisations that implement these recommendations will materially reduce their exposure to credential-based network attacks, meet compliance obligations, and build a defensible security posture for their guest and corporate WiFi infrastructure.
Mitigating RADIUS Vulnerabilities: A Security Hardening Guide
This guide provides a comprehensive, actionable reference for IT managers, network architects, and CTOs responsible for enterprise WiFi infrastructure across hospitality, retail, events, and public-sector environments. It covers the full attack surface of RADIUS server deployments — from MD5 collision vulnerabilities and weak shared secrets to unencrypted UDP transport and misconfigured EAP methods — and delivers a prioritised hardening roadmap aligned with IEEE 802.1X, PCI DSS, and GDPR requirements. Organisations that implement these recommendations will materially reduce their exposure to credential-based network attacks, meet compliance obligations, and build a defensible security posture for their guest and corporate WiFi infrastructure.
Implementing WPA3-Enterprise for Enhanced Wireless Security
This technical reference guide provides a comprehensive, actionable roadmap for IT leaders transitioning from WPA2 to WPA3-Enterprise. It covers the architectural shifts, mandatory security enhancements like EAP-TLS and PMF, and practical deployment strategies to secure corporate networks across complex enterprise environments.