Accès Réseau Zero Trust : Stratégies de mise en œuvre et meilleures pratiques
Ce guide de référence technique fournit aux responsables informatiques et aux architectes réseau un plan pragmatique pour la mise en œuvre de l'Accès Réseau Zero Trust (ZTNA) dans les environnements d'entreprise. Il couvre l'architecture de base, les stratégies de micro-segmentation et les méthodologies de déploiement étape par étape pour sécuriser les environnements complexes sans perturber les opérations.
Écouter ce guide
Voir la transcription du podcast
- Résumé Exécutif
- Approfondissement Technique
- Contrôle d'Accès Basé sur l'Identité
- Vérification de la Posture des Appareils
- Authentification Continue et Détection des Menaces
- Guide de Mise en Œuvre
- Phase 1 : Découverte et Classification
- Phase 2 : Conception de la Segmentation
- Phase 3 : Intégration de l'Identité
- Phase 4 : Déploiement des Politiques (Mode Surveillance)
- Meilleures Pratiques
- Dépannage et atténuation des risques
- ROI et impact commercial

Résumé Exécutif
Le modèle de sécurité traditionnel basé sur le périmètre est obsolète. Pour les environnements d'entreprise — des hôtels de 500 chambres aux vastes complexes commerciaux et aux stades à forte densité — l'hypothèse que le trafic réseau interne est intrinsèquement digne de confiance représente une vulnérabilité critique. L'Accès Réseau Zero Trust (ZTNA) remplace cette hypothèse erronée par un cadre rigoureux basé sur l'identité : tout vérifier, ne rien faire confiance par défaut et appliquer le principe du moindre privilège à chaque couche.
Ce guide de référence fournit aux responsables informatiques, aux architectes réseau et aux directeurs des opérations de site un plan pragmatique pour la mise en œuvre de l'accès réseau zero trust. Il s'éloigne de la théorie académique pour se concentrer sur les réalités du déploiement : l'intégration des fournisseurs d'identité, l'application de la micro-segmentation dans des environnements hérités complexes, et la gestion de la vérification de la posture des appareils pour les terminaux d'entreprise gérés et les appareils invités non gérés. En mettant en œuvre ces stratégies, les sites peuvent sécuriser leur Guest WiFi infrastructure, isoler les systèmes de paiement pour maintenir la conformité PCI DSS et protéger les technologies opérationnelles critiques sans dégrader l'expérience utilisateur.
Approfondissement Technique
Une architecture d'Accès Réseau Zero Trust robuste repose sur l'orchestration de plusieurs composants clés, déplaçant le périmètre de sécurité du bord du réseau vers l'identité et l'appareil individuels.
Contrôle d'Accès Basé sur l'Identité
Dans un modèle ZTNA, les décisions d'accès sont entièrement basées sur une identité vérifiée plutôt que sur l'emplacement réseau. Un utilisateur se connectant à un port de commutateur dans un bureau arrière ne reçoit pas plus de confiance intrinsèque qu'un invité se connectant à un point d'accès public. Dans les environnements de site, les politiques d'identité doivent s'adapter à des populations d'utilisateurs très divergentes.
Pour le personnel et les sous-traitants, l'authentification repose généralement sur IEEE 802.1X lié à un annuaire central (par exemple, Active Directory ou Azure AD). Pour les utilisateurs invités, l'assertion d'identité se fait via des Captive Portals ou des mécanismes de connexion sociale. La plateforme de Purple agit comme un fournisseur d'identité critique dans ce contexte, capturant l'identité vérifiée au point de connexion et transmettant ce contexte aux points d'application des politiques en aval.
Vérification de la Posture des Appareils
L'identité seule est insuffisante ; le terminal de connexion doit également être validé. La vérification de la posture des appareils évalue l'état de sécurité de l'appareil avant d'accorder l'accès. Pour les appareils d'entreprise gérés, cela implique de vérifier la protection active des terminaux, les niveaux de correctifs du système d'exploitation et l'inscription MDM.
Pour les appareils non gérés — tels que ceux sur les réseaux Guest WiFi — la vérification de la posture est limitée, nécessitant une politique de refus par défaut pour le routage interne. Ces appareils sont placés dans un segment isolé avec un accès uniquement à Internet. Le moteur de politique évalue ces paramètres dynamiquement au moment de la connexion et en continu tout au long de la session.
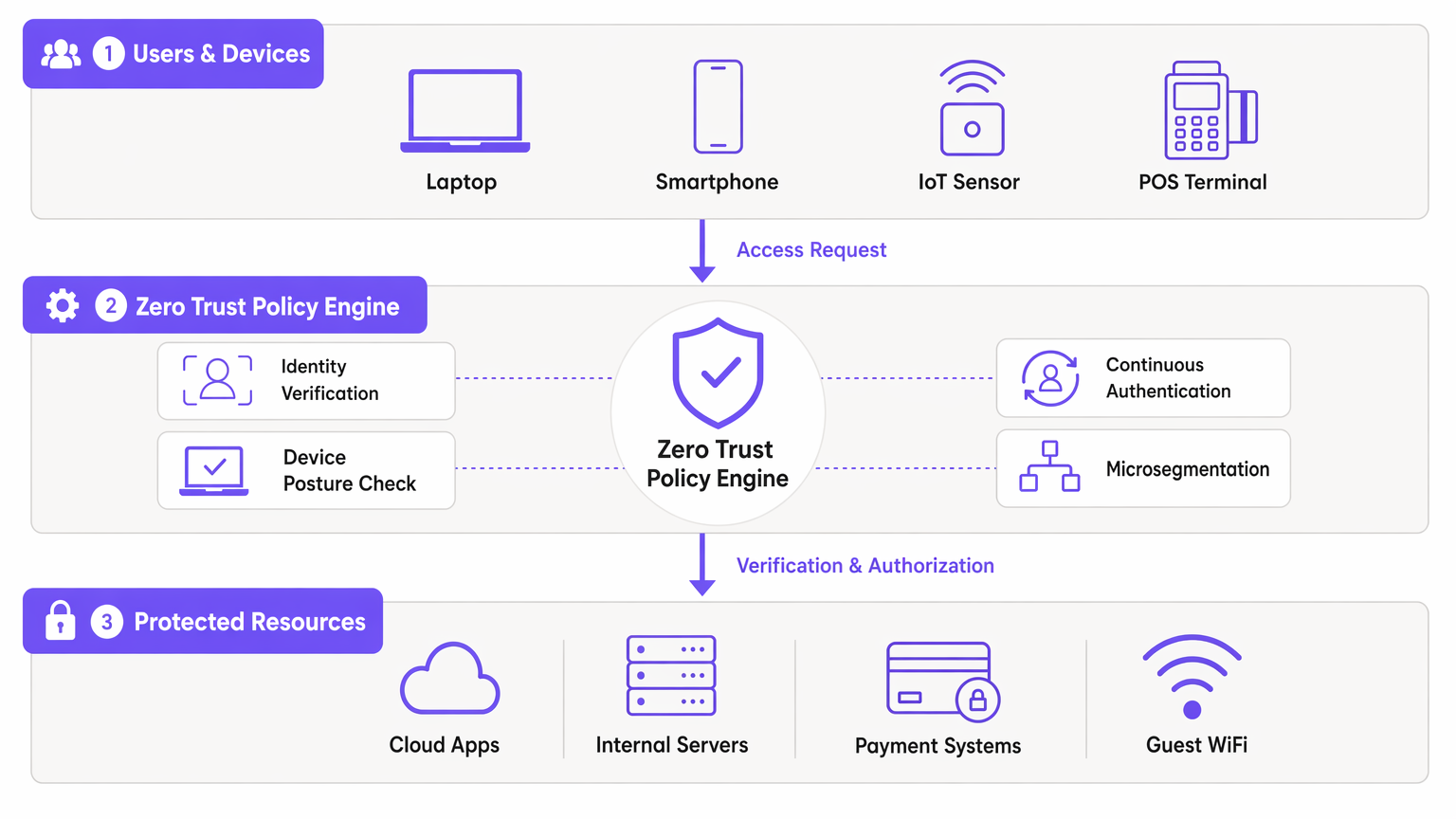
Authentification Continue et Détection des Menaces
Les réseaux traditionnels s'authentifient une seule fois et maintiennent la session indéfiniment. Le ZTNA exige une authentification continue. Le moteur de politique surveille le comportement de la session, les volumes de données et l'utilisation des protocoles. Les schémas anormaux déclenchent une nouvelle authentification ou une terminaison immédiate de la session. Cette télémétrie alimente les plateformes SIEM, permettant une détection des menaces en temps réel et une réponse rapide aux tentatives de mouvement latéral.
Guide de Mise en Œuvre
Le déploiement du ZTNA dans un environnement de site en direct nécessite une approche progressive et méthodique pour éviter toute perturbation opérationnelle.
Phase 1 : Découverte et Classification
Avant de modifier les politiques, vous devez établir un inventaire complet de tous les appareils, utilisateurs et charges de travail. Dans des environnements comme l' Hôtellerie ou le Commerce de Détail , les appareils IoT non documentés et les systèmes hérités sont courants. Utilisez des outils de découverte réseau pour cartographier les flux de trafic existants et identifier tous les terminaux connectés.
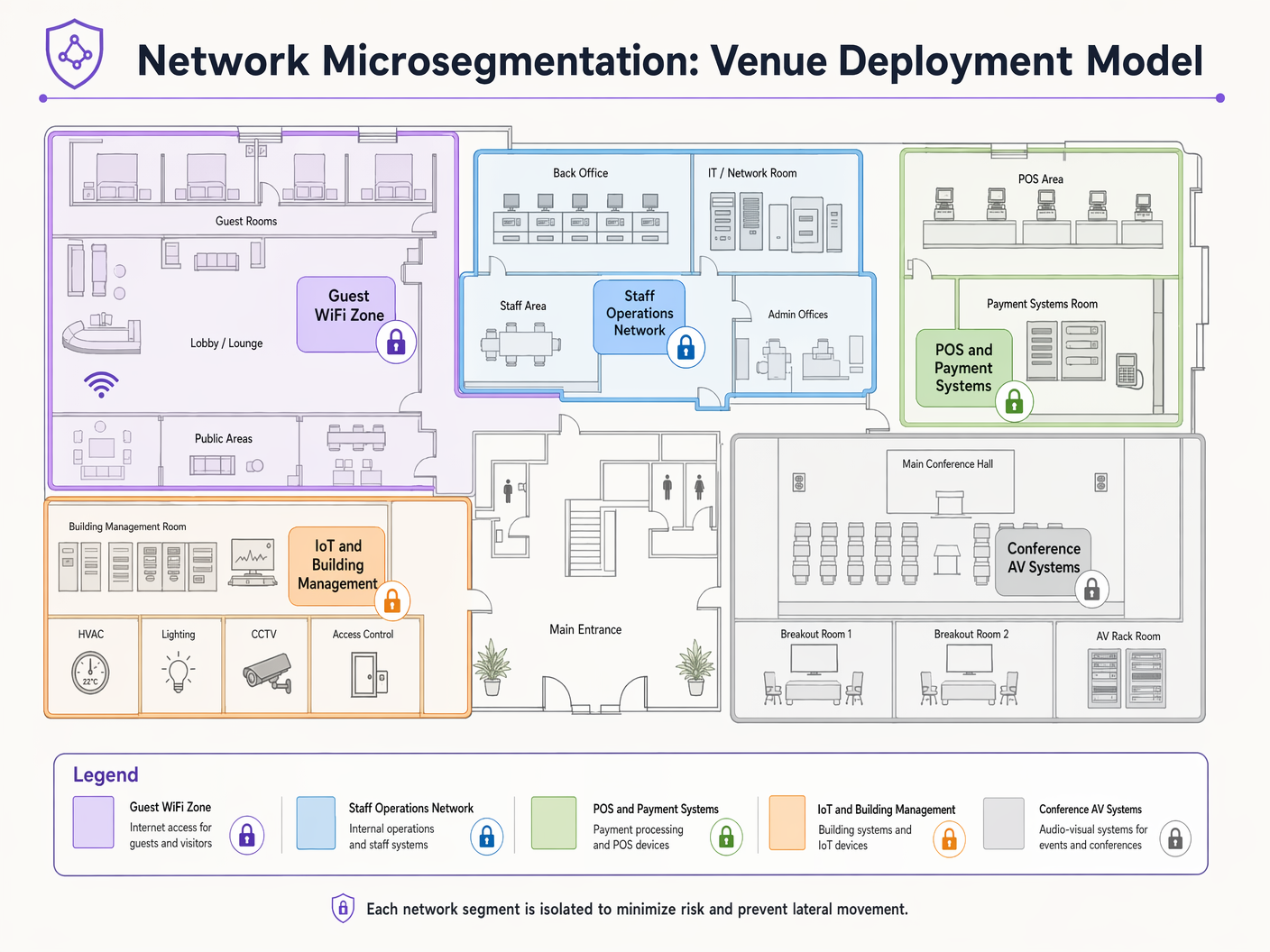
Phase 2 : Conception de la Segmentation
Mappez les segments réseau aux fonctions métier et aux exigences de conformité. Un site typique nécessite des segments distincts pour :
- Guest WiFi : Accès uniquement à Internet.
- Opérations du Personnel : Accès aux applications internes.
- Systèmes de Paiement (POS) : Strictement isolés pour la conformité PCI DSS.
- Gestion des Bâtiments/IoT : Restreint aux serveurs de contrôle nécessaires.
Définissez les flux de trafic autorisés entre ces segments en adoptant une position de refus par défaut.
Phase 3 : Intégration de l'Identité
Intégrez votre moteur de politique ZTNA à vos fournisseurs d'identité. Connectez les annuaires d'entreprise pour le personnel et configurez les plateformes d'accès invité pour affirmer les identités des invités. Assurez-vous que les mécanismes d'authentification basés sur le profil sont robustes et évolutifs pour gérer la capacité maximale du site.
Phase 4 : Déploiement des Politiques (Mode Surveillance)
Déployez les politiques en mode observation uniquement au début. Cela offre une visibilité sur le trafic qui serait bloqué, vous permettant d'affiner les règles sans interrompre les processus métier légitimes. Après une période de surveillance de 2 à 4 semaines, passez en mode application.
Meilleures Pratiques
- Présumer une Violation : Concevez votre réseau en partant du principe qu'un attaquant a déjà compromis un terminal. La micro-segmentation est votre principale défense contre les mouvements latéraux.
- Utiliser 802.1X et WPA3 : Mettez en œuvre une authentification et un chiffrement robustes au niveau de la couche d'accès. Référez-vous aux guides sur Dépannage des problèmes d'authentification 802.1X sous Windows 11 pour le support de déploiement.
- Automatisez l'identité des invités : Utilisez des plateformes qui capturent et vérifient de manière transparente les identités des invités sans introduire de friction excessive. Voir Sécurisation des réseaux WiFi invités : Bonnes pratiques et mise en œuvre .
- Isolez les appareils IoT : Les capteurs IoT et les systèmes de gestion de bâtiment ont rarement besoin d'un accès internet ou d'un routage inter-segments. Isolez-les strictement.
Dépannage et atténuation des risques
Le mode de défaillance le plus courant dans la mise en œuvre de l'accès réseau Zero Trust est l'application agressive des politiques sans découverte adéquate. Cela entraîne le blocage du trafic critique pour l'entreprise et l'annulation du projet.
Risque : Les appareils hérités (par exemple, les anciens terminaux POS ou les contrôleurs HVAC) peuvent ne pas prendre en charge les protocoles d'authentification modernes. Atténuation : Utilisez le MAC Authentication Bypass (MAB) combiné à une microsegmentation et un profilage stricts pour intégrer ces appareils en toute sécurité sans compromettre l'architecture ZTNA plus large.
Risque : Les performances du réseau invité se dégradent en raison d'une surcharge importante liée à l'application des politiques. Atténuation : Déchargez le routage du trafic invité directement vers internet en périphérie, en contournant les moteurs d'inspection interne approfondie, sauf si des informations spécifiques sur les menaces indiquent le contraire.
ROI et impact commercial
La mise en œuvre du ZTNA offre une valeur commerciale mesurable au-delà de la réduction des risques :
- Réduction des coûts de conformité : En isolant strictement l'environnement de données des titulaires de carte (CDE) par microsegmentation, les établissements réduisent considérablement la portée et le coût des audits PCI DSS.
- Résilience opérationnelle : La limitation des brèches à un seul segment prévient les pannes à l'échelle de l'établissement, protégeant les flux de revenus pendant les heures de pointe opérationnelles.
- Analyses améliorées : Les données granulaires d'identité et de trafic générées par les politiques ZTNA enrichissent les analyses WiFi , offrant des informations plus approfondies sur le comportement des utilisateurs et l'utilisation du réseau.
Définitions clés
Microsegmentation
The practice of dividing a network into isolated segments to reduce the attack surface and prevent lateral movement.
Critical for venue IT teams to isolate POS systems from Guest WiFi and staff networks, ensuring compliance and containing potential breaches.
Device Posture Verification
The process of assessing an endpoint's security state (e.g., OS version, antivirus status) before granting network access.
Used to ensure that unpatched or compromised staff devices cannot access sensitive internal applications.
Continuous Authentication
The ongoing monitoring of a user's session to ensure their identity and behavior remain valid and non-anomalous.
Vital in high-turnover environments like stadiums to detect session hijacking or unusual data exfiltration attempts.
IEEE 802.1X
A standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol used by network architects to authenticate corporate devices securely.
Lateral Movement
Techniques that cyber attackers use to progressively move through a network as they search for key data and assets.
The primary threat that ZTNA and microsegmentation are designed to neutralize in flat legacy networks.
Software-Defined Perimeter (SDP)
A security approach that hides internet-connected infrastructure so that external parties and attackers cannot see it, whether it is hosted on-premises or in the cloud.
Often used as the technical implementation mechanism for deploying ZTNA access policies.
Least-Privilege Access
The security principle of granting users and systems only the minimum level of access necessary to perform their required functions.
The guiding policy framework IT managers must use when defining rules within the ZTNA policy engine.
MAC Authentication Bypass (MAB)
A fallback authentication method that uses a device's MAC address to grant network access when 802.1X is not supported.
Used pragmatically by network teams to onboard legacy IoT devices (like old printers or HVAC systems) into isolated network segments.
Exemples concrets
A 400-room hotel needs to deploy new smart TVs in all guest rooms. These devices require internet access for streaming services and local network access to the property management system (PMS) for personalized greetings and billing review. How should this be implemented under a ZTNA model?
- Place all smart TVs in a dedicated 'Guest Room Entertainment' microsegment. 2. Configure policies to allow outbound internet access for streaming. 3. Implement a strict, unidirectional API gateway policy allowing the TVs to query the PMS on specific ports (e.g., HTTPS/443) only for the required endpoints. 4. Deny all lateral traffic between individual TVs and deny all inbound traffic from the internet.
A large retail chain is rolling out mobile Point of Sale (mPOS) tablets for staff on the shop floor. These tablets connect via WiFi. How do you secure this deployment?
- Authenticate the tablets using certificate-based IEEE 802.1X (EAP-TLS). 2. Implement device posture checks via MDM integration to ensure the tablet is compliant (patched, unrooted) before granting access. 3. Assign the tablets dynamically to a highly restricted 'mPOS' VLAN/segment. 4. Allow traffic only to the specific payment gateway IP addresses and internal inventory APIs.
Questions d'entraînement
Q1. A stadium IT director wants to allow third-party vendors (e.g., catering staff) to access their own cloud-based inventory systems via the stadium's WiFi. How should this be configured?
Conseil : Consider the difference between corporate data access and internet-only access for third parties.
Voir la réponse type
Create a dedicated 'Vendor WiFi' SSID and microsegment. Authenticate vendors using a captive portal or unique pre-shared keys (WPA3-SAE). Configure the segment policy to allow outbound internet access only, strictly denying any routing to the stadium's internal operational networks or POS systems.
Q2. During a ZTNA rollout, the operations team reports that several legacy barcode scanners in the warehouse have stopped working. What is the likely cause and immediate solution?
Conseil : Think about what happens when devices cannot support modern authentication protocols.
Voir la réponse type
The scanners likely do not support 802.1X authentication and were blocked by the new default-deny policy. The immediate solution is to implement MAC Authentication Bypass (MAB) for the specific MAC addresses of the scanners and place them in a highly restricted microsegment that only allows traffic to the inventory database server.
Q3. A CTO asks you to justify the cost of implementing microsegmentation across a 50-site retail estate. What is the primary business justification?
Conseil : Focus on risk containment and compliance impact.
Voir la réponse type
The primary justification is risk containment and compliance scope reduction. By microsegmenting the network, a breach in a less secure segment (like an IoT device or Guest WiFi) cannot spread to the Cardholder Data Environment (CDE). This dramatically reduces the scope, complexity, and cost of annual PCI DSS audits, while preventing a localized incident from becoming a company-wide data breach.
Continuer la lecture de cette série
Comment configurer SCEP pour un BYOD sécurisé et l'authentification réseau 802.1X
Ce guide fournit une référence technique complète pour configurer SCEP afin de déployer une authentification réseau 802.1X basée sur des certificats. Il couvre la transition architecturale des mots de passe partagés vers EAP-TLS, l'intégration de la gestion des appareils mobiles (MDM) et une segmentation réseau stricte pour un accès BYOD sécurisé dans les environnements d'entreprise.
Intégration des points d'accès Grandstream GWN avec Purple WiFi
Ce guide de référence technique faisant autorité détaille comment intégrer les points d'accès Grandstream GWN avec la plateforme de Guest WiFi et d'analyse de Purple. Il couvre la configuration du Captive Portal Grandstream, les paramètres RADIUS AAA, la configuration du walled garden, l'authentification sécurisée du personnel en 802.1X avec routage VLAN dynamique, et la segmentation PPSK multi-tenant - fournissant des instructions pratiques, étape par étape, pour les MSP et les équipes informatiques déployant du WiFi pour les invités et le personnel à grande échelle.
Conditions d'utilisation du WiFi pour le personnel : Essentiels juridiques et de conformité
Ce guide présente les aspects juridiques et techniques essentiels pour rédiger et appliquer les conditions d'utilisation du WiFi pour le personnel dans les établissements d'entreprise. Il détaille les éléments à inclure dans une charte d'utilisation acceptable (AUP), comment respecter les exigences du GDPR et de la norme PCI DSS, et comment déployer l'authentification basée sur l'identité et la segmentation du réseau pour protéger les actifs de l'entreprise. Les responsables informatiques, les équipes RH et les directeurs des opérations des hôtels, des chaînes de magasins, des stades et des organisations du secteur public y trouveront des conseils pratiques à mettre en œuvre dès ce trimestre.