Zero Trust Network Access: Estrategias de Implementación y Mejores Prácticas
Esta guía de referencia técnica proporciona a los líderes de TI y a los arquitectos de red un plan pragmático para la implementación de Zero Trust Network Access (ZTNA) en entornos empresariales. Cubre la arquitectura central, las estrategias de microsegmentación y las metodologías de despliegue paso a paso para asegurar entornos complejos sin interrumpir las operaciones.
Escuchar esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado
- Control de Acceso Basado en la Identidad
- Verificación de la Postura del Dispositivo
- Autenticación Continua y Detección de Amenazas
- Guía de Implementación
- Fase 1: Descubrimiento y Clasificación
- Fase 2: Diseño de Segmentación
- Fase 3: Integración de Identidad
- Fase 4: Despliegue de Políticas (Modo de Monitorización)
- Mejores Prácticas
- Resolución de problemas y mitigación de riesgos
- ROI e impacto empresarial

Resumen Ejecutivo
El modelo de seguridad tradicional basado en el perímetro está obsoleto. Para los entornos empresariales —desde hoteles de 500 habitaciones hasta grandes complejos comerciales y estadios de alta densidad—, la suposición de que el tráfico de red interno es inherentemente fiable representa una vulnerabilidad crítica. Zero Trust Network Access (ZTNA) reemplaza esta suposición errónea con un marco riguroso basado en la identidad: verificar todo, no confiar en nada por defecto y aplicar el acceso de mínimo privilegio en cada capa.
Esta guía de referencia proporciona a los gerentes de TI, arquitectos de red y directores de operaciones de instalaciones un plan pragmático para la implementación de zero trust network access. Elimina la teoría académica para centrarse en las realidades del despliegue: integrar proveedores de identidad, aplicar la microsegmentación en entornos heredados complejos y gestionar la verificación de la postura de los dispositivos tanto para los puntos finales corporativos gestionados como para los dispositivos de invitados no gestionados. Al implementar estas estrategias, las instalaciones pueden asegurar su infraestructura de Guest WiFi , aislar los sistemas de pago para mantener el cumplimiento de PCI DSS y proteger la tecnología operativa crítica sin degradar la experiencia del usuario.
Análisis Técnico Detallado
Una arquitectura robusta de Zero Trust Network Access se basa en la orquestación de varios componentes centrales, trasladando el perímetro de seguridad del borde de la red a la identidad y el dispositivo individuales.
Control de Acceso Basado en la Identidad
En un modelo ZTNA, las decisiones de acceso se basan completamente en la identidad verificada en lugar de la ubicación de la red. Un usuario que se conecta a un puerto de switch en una oficina trasera no recibe más confianza inherente que un invitado que se conecta a un punto de acceso público. En entornos de instalaciones, las políticas de identidad deben adaptarse a poblaciones de usuarios muy divergentes.
Para el personal y los contratistas, la autenticación suele basarse en IEEE 802.1X vinculado a un directorio central (por ejemplo, Active Directory o Azure AD). Para los usuarios invitados, la aserción de identidad se produce a través de Captive Portals o mecanismos de inicio de sesión social. La plataforma de Purple actúa como un proveedor de identidad crítico en este contexto, capturando la identidad verificada en el punto de conexión y pasando este contexto a los puntos de aplicación de políticas posteriores.
Verificación de la Postura del Dispositivo
La identidad por sí sola es insuficiente; el punto final de conexión también debe ser validado. La verificación de la postura del dispositivo evalúa el estado de seguridad del dispositivo antes de conceder el acceso. Para los dispositivos corporativos gestionados, esto implica verificar la protección de puntos finales activa, los niveles de parches del sistema operativo y la inscripción en MDM.
Para los dispositivos no gestionados —como los de las redes Guest WiFi —, la comprobación de la postura es limitada, lo que requiere una política de denegación por defecto para el enrutamiento interno. Estos dispositivos se colocan en un segmento aislado con acceso solo a internet. El motor de políticas evalúa estos parámetros dinámicamente en el momento de la conexión y de forma continua durante toda la sesión.
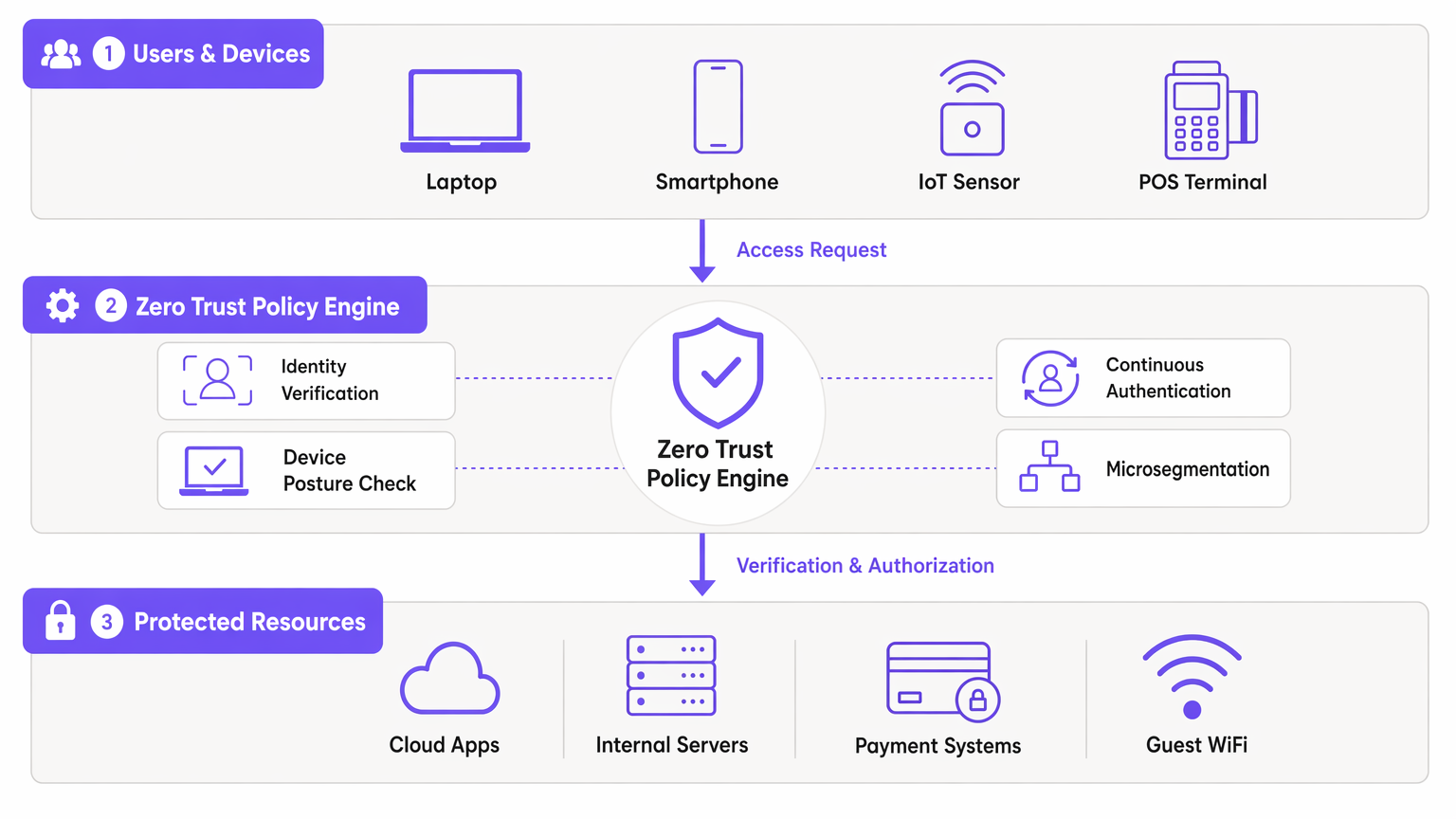
Autenticación Continua y Detección de Amenazas
Las redes tradicionales autentican una vez y mantienen la sesión indefinidamente. ZTNA exige una autenticación continua. El motor de políticas monitoriza el comportamiento de la sesión, los volúmenes de datos y el uso de protocolos. Los patrones anómalos desencadenan una nueva autenticación o la terminación inmediata de la sesión. Esta telemetría se alimenta a las plataformas SIEM, lo que permite la detección de amenazas en tiempo real y una respuesta rápida a los intentos de movimiento lateral.
Guía de Implementación
El despliegue de ZTNA en un entorno de instalaciones en vivo requiere un enfoque por fases y metódico para evitar interrupciones operativas.
Fase 1: Descubrimiento y Clasificación
Antes de modificar las políticas, debe establecer un inventario completo de todos los dispositivos, usuarios y cargas de trabajo. En entornos como Hospitality o Retail , los dispositivos IoT no documentados y los sistemas heredados son comunes. Utilice herramientas de descubrimiento de red para mapear los flujos de tráfico existentes e identificar todos los puntos finales conectados.
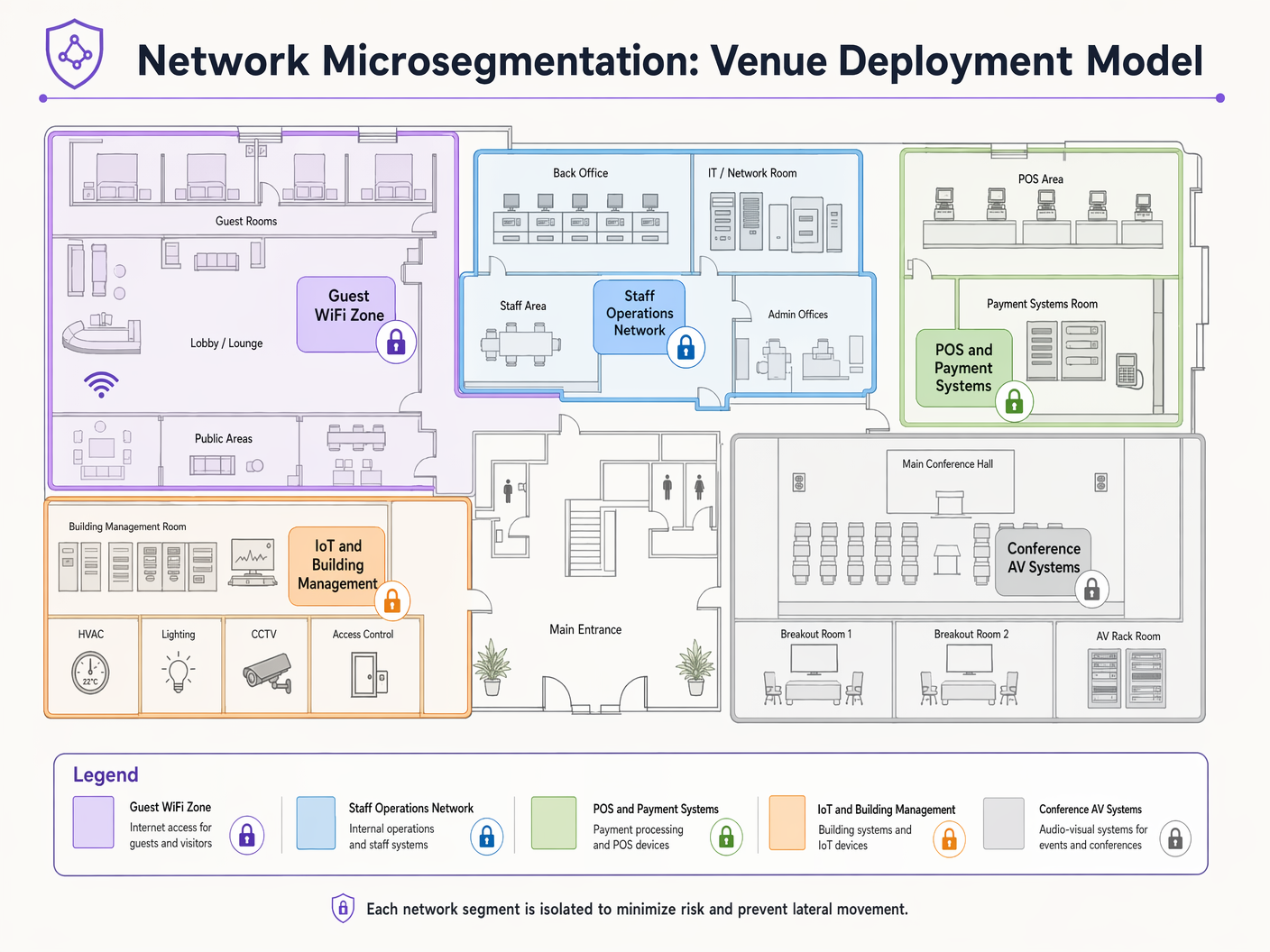
Fase 2: Diseño de Segmentación
Mapee los segmentos de red a las funciones comerciales y los requisitos de cumplimiento. Una instalación típica requiere segmentos distintos para:
- Guest WiFi: Acceso solo a internet.
- Operaciones del Personal: Acceso a aplicaciones internas.
- Sistemas de Pago (POS): Estrictamente aislados para el cumplimiento de PCI DSS.
- Gestión de Edificios/IoT: Restringido a los servidores de control necesarios.
Defina los flujos de tráfico permitidos entre estos segmentos utilizando una postura de denegación por defecto.
Fase 3: Integración de Identidad
Integre su motor de políticas ZTNA con sus proveedores de identidad. Conecte los directorios corporativos para el personal y configure las plataformas de acceso de invitados para afirmar las identidades de los invitados. Asegúrese de que los mecanismos de autenticación basados en perfiles sean robustos y escalables para manejar la capacidad máxima de la instalación.
Fase 4: Despliegue de Políticas (Modo de Monitorización)
Despliegue las políticas en modo de solo observación inicialmente. Esto proporciona visibilidad del tráfico que se bloquearía, lo que le permite refinar las reglas sin interrumpir los procesos comerciales legítimos. Después de un período de monitorización de 2 a 4 semanas, realice la transición al modo de aplicación.
Mejores Prácticas
- Asumir la Brecha: Diseñe su red bajo la suposición de que un atacante ya ha comprometido un punto final. La microsegmentación es su defensa principal contra el movimiento lateral.
- Aprovechar 802.1X y WPA3: Implemente una autenticación y cifrado robustos en la capa de acceso. Consulte las guías sobre Troubleshooting Windows 11 802.1X Authentication Issues para soporte de implementación.
- Automatizar la identidad de los invitados: Utilice plataformas que capturen y verifiquen sin problemas las identidades de los invitados sin introducir una fricción excesiva. Consulte Securing Guest WiFi Networks: Best Practices and Implementation .
- Aislar dispositivos IoT: Los sensores IoT y los sistemas de gestión de edificios rara vez necesitan acceso a internet o enrutamiento entre segmentos. Aíslos estrictamente.
Resolución de problemas y mitigación de riesgos
El modo de fallo más común en la implementación del acceso a la red de confianza cero es la aplicación agresiva de políticas sin un descubrimiento adecuado. Esto conduce al bloqueo del tráfico crítico para el negocio y a la reversión del proyecto.
Riesgo: Los dispositivos heredados (por ejemplo, terminales POS antiguos o controladores HVAC) pueden no ser compatibles con los protocolos de autenticación modernos. Mitigación: Utilice MAC Authentication Bypass (MAB) combinado con una microsegmentación y un perfilado estrictos para incorporar de forma segura estos dispositivos sin comprometer la arquitectura ZTNA más amplia.
Riesgo: El rendimiento de la red de invitados se degrada debido a la sobrecarga de la aplicación de políticas. Mitigación: Descargue el enrutamiento del tráfico de invitados directamente a internet en el borde, evitando los motores de inspección interna profunda a menos que la inteligencia de amenazas específica indique lo contrario.
ROI e impacto empresarial
La implementación de ZTNA ofrece un valor empresarial medible más allá de la reducción de riesgos:
- Reducción de costes de cumplimiento: Al aislar estrictamente el Entorno de Datos del Titular de la Tarjeta (CDE) mediante microsegmentación, los establecimientos reducen significativamente el alcance y el coste de las auditorías PCI DSS.
- Resiliencia operativa: Contener las brechas en un único segmento evita interrupciones en todo el establecimiento, protegiendo los flujos de ingresos durante las horas de máxima actividad operativa.
- Análisis mejorados: Los datos granulares de identidad y tráfico generados por las políticas ZTNA enriquecen WiFi Analytics , proporcionando información más profunda sobre el comportamiento del usuario y la utilización de la red.
Definiciones clave
Microsegmentation
The practice of dividing a network into isolated segments to reduce the attack surface and prevent lateral movement.
Critical for venue IT teams to isolate POS systems from Guest WiFi and staff networks, ensuring compliance and containing potential breaches.
Device Posture Verification
The process of assessing an endpoint's security state (e.g., OS version, antivirus status) before granting network access.
Used to ensure that unpatched or compromised staff devices cannot access sensitive internal applications.
Continuous Authentication
The ongoing monitoring of a user's session to ensure their identity and behavior remain valid and non-anomalous.
Vital in high-turnover environments like stadiums to detect session hijacking or unusual data exfiltration attempts.
IEEE 802.1X
A standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol used by network architects to authenticate corporate devices securely.
Lateral Movement
Techniques that cyber attackers use to progressively move through a network as they search for key data and assets.
The primary threat that ZTNA and microsegmentation are designed to neutralize in flat legacy networks.
Software-Defined Perimeter (SDP)
A security approach that hides internet-connected infrastructure so that external parties and attackers cannot see it, whether it is hosted on-premises or in the cloud.
Often used as the technical implementation mechanism for deploying ZTNA access policies.
Least-Privilege Access
The security principle of granting users and systems only the minimum level of access necessary to perform their required functions.
The guiding policy framework IT managers must use when defining rules within the ZTNA policy engine.
MAC Authentication Bypass (MAB)
A fallback authentication method that uses a device's MAC address to grant network access when 802.1X is not supported.
Used pragmatically by network teams to onboard legacy IoT devices (like old printers or HVAC systems) into isolated network segments.
Ejemplos prácticos
A 400-room hotel needs to deploy new smart TVs in all guest rooms. These devices require internet access for streaming services and local network access to the property management system (PMS) for personalized greetings and billing review. How should this be implemented under a ZTNA model?
- Place all smart TVs in a dedicated 'Guest Room Entertainment' microsegment. 2. Configure policies to allow outbound internet access for streaming. 3. Implement a strict, unidirectional API gateway policy allowing the TVs to query the PMS on specific ports (e.g., HTTPS/443) only for the required endpoints. 4. Deny all lateral traffic between individual TVs and deny all inbound traffic from the internet.
A large retail chain is rolling out mobile Point of Sale (mPOS) tablets for staff on the shop floor. These tablets connect via WiFi. How do you secure this deployment?
- Authenticate the tablets using certificate-based IEEE 802.1X (EAP-TLS). 2. Implement device posture checks via MDM integration to ensure the tablet is compliant (patched, unrooted) before granting access. 3. Assign the tablets dynamically to a highly restricted 'mPOS' VLAN/segment. 4. Allow traffic only to the specific payment gateway IP addresses and internal inventory APIs.
Preguntas de práctica
Q1. A stadium IT director wants to allow third-party vendors (e.g., catering staff) to access their own cloud-based inventory systems via the stadium's WiFi. How should this be configured?
Sugerencia: Consider the difference between corporate data access and internet-only access for third parties.
Ver respuesta modelo
Create a dedicated 'Vendor WiFi' SSID and microsegment. Authenticate vendors using a captive portal or unique pre-shared keys (WPA3-SAE). Configure the segment policy to allow outbound internet access only, strictly denying any routing to the stadium's internal operational networks or POS systems.
Q2. During a ZTNA rollout, the operations team reports that several legacy barcode scanners in the warehouse have stopped working. What is the likely cause and immediate solution?
Sugerencia: Think about what happens when devices cannot support modern authentication protocols.
Ver respuesta modelo
The scanners likely do not support 802.1X authentication and were blocked by the new default-deny policy. The immediate solution is to implement MAC Authentication Bypass (MAB) for the specific MAC addresses of the scanners and place them in a highly restricted microsegment that only allows traffic to the inventory database server.
Q3. A CTO asks you to justify the cost of implementing microsegmentation across a 50-site retail estate. What is the primary business justification?
Sugerencia: Focus on risk containment and compliance impact.
Ver respuesta modelo
The primary justification is risk containment and compliance scope reduction. By microsegmenting the network, a breach in a less secure segment (like an IoT device or Guest WiFi) cannot spread to the Cardholder Data Environment (CDE). This dramatically reduces the scope, complexity, and cost of annual PCI DSS audits, while preventing a localized incident from becoming a company-wide data breach.
Continúe leyendo esta serie
Configuración del redireccionamiento de Captive Portal en controladores de red Enterprise
Esta guía autorizada detalla la arquitectura técnica y los pasos de configuración específicos de cada proveedor necesarios para implementar el redireccionamiento de Captive Portal en controladores de red enterprise. Proporciona orientación práctica para los equipos de TI sobre cómo configurar walled gardens, integrar la autenticación RADIUS y garantizar el cumplimiento de GDPR y PCI DSS.
Guía paso a paso: Configuración de controladores inalámbricos Ruijie para Captive Portals de WiFi de invitados
Esta guía ofrece un recorrido técnico completo para configurar controladores inalámbricos y gateways de Ruijie para implementar Captive Portals de WiFi de invitados de nivel empresarial. Cubre la segmentación de VLAN, la autenticación RADIUS externa a través del protocolo WISPr, la configuración de walled garden y la integración perfecta con la plataforma Identity-Based Networks de Purple para capturar datos de origen (first-party data) y generar un valor comercial medible en entornos de hostelería, retail y sector público.
Guía de configuración de WiFi para invitados empresarial: segmentación de VLAN, seguridad y Captive Portals
Esta guía proporciona un diseño técnico para la implementación de WiFi para invitados empresarial, centrándose en la segmentación de VLAN, los protocolos de seguridad y la arquitectura de captive portal. Detalla cómo aislar el tráfico, aplicar estándares de cifrado y capturar datos de origen de forma segura en entornos complejos.