Proteger Redes WiFi de Convidados: Melhores Práticas e Implementação
Este guia de referência técnica autorizado descreve a arquitetura, autenticação e controlos operacionais necessários para implementar uma rede WiFi de convidados empresarial segura. Fornece melhores práticas acionáveis para líderes de TI aplicarem a segmentação de rede, gerirem a largura de banda e garantirem a conformidade, maximizando a captura de dados.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada
- Segmentação e Isolamento de Rede
- Arquitetura de Captive Portal
- Padrões de Encriptação: WPA3
- Guia de Implementação
- 1. Definir a Topologia
- 2. Selecionar o Método de Autenticação
- 3. Configurar a Gestão de Largura de Banda
- 4. Implementar e Testar
- Melhores Práticas
- Resolução de Problemas e Mitigação de Riscosation
- ROI e Impacto nos Negócios
- Briefing do Podcast

Resumo Executivo
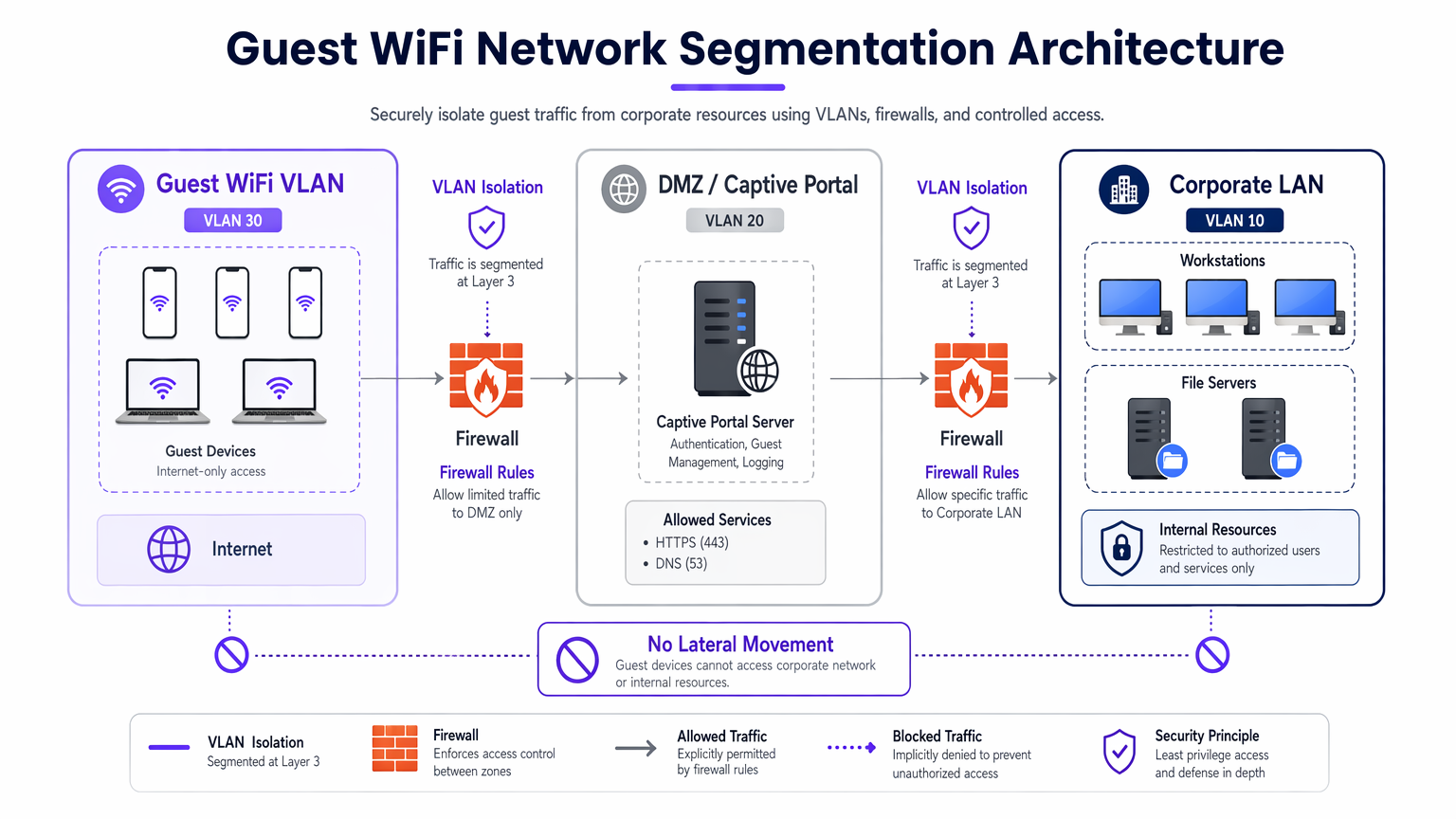
A implementação de uma rede WiFi de convidados segura exige um equilíbrio entre o acesso do utilizador sem atrito e uma segmentação de rede e conformidade robustas. Para CTOs e arquitetos de rede nos setores de retalho, hotelaria e público, o desafio é isolar dispositivos de convidados não fidedignos da infraestrutura corporativa, extraindo o máximo valor da captura de dados primários. Este guia detalha a arquitetura técnica, os frameworks de autenticação e os controlos operacionais necessários para implementar WiFi de convidados de nível empresarial. Cobrimos práticas essenciais, incluindo segmentação VLAN de Camada 3, segurança de Captive Portal, limitação de taxa de largura de banda e padrões de encriptação modernos como WPA3. Ao implementar estas melhores práticas neutras em relação ao fornecedor, as organizações podem mitigar riscos de movimento lateral, garantir a conformidade regulamentar (incluindo GDPR e PCI DSS) e transformar uma potencial responsabilidade de segurança num ativo seguro e gerador de valor.
Análise Técnica Detalhada
A base de qualquer rede WiFi de convidados segura é o isolamento absoluto dos recursos corporativos. Isto requer uma abordagem de defesa em profundidade que abrange várias camadas do modelo OSI.
Segmentação e Isolamento de Rede
Uma implementação robusta exige VLANs dedicadas para o tráfego de convidados, completamente separadas das redes operacionais internas. Por exemplo, o tráfego de convidados pode ser atribuído à VLAN 30, enquanto os dispositivos corporativos residem na VLAN 10. Esta segmentação deve ser imposta na camada do switch gerido, e não apenas no controlador sem fios, para prevenir ataques de "VLAN hopping".
Além disso, o isolamento de cliente (ou isolamento de Camada 2) é crítico. Isto impede que dispositivos conectados ao mesmo Guest WiFi SSID comuniquem entre si. Sem o isolamento de cliente, um único dispositivo comprometido pode analisar a sub-rede local, executar "ARP spoofing" e lançar ataques laterais contra outros convidados.
Arquitetura de Captive Portal
O Captive Portal serve como porta de entrada para autenticação e aplicação de políticas. Para prevenir a interceção de credenciais, o portal deve ser servido exclusivamente via HTTPS, utilizando um certificado TLS válido. O servidor do portal deve residir numa DMZ, isolado de bases de dados internas. Isto garante que, mesmo que o portal seja comprometido, os atacantes não podem aceder à LAN corporativa.
Padrões de Encriptação: WPA3
Redes abertas legadas transmitem dados em texto simples, expondo os utilizadores à escuta passiva. As implementações modernas devem exigir WPA3. Para redes públicas, o WPA3-Enhanced Open (Opportunistic Wireless Encryption) fornece encriptação de dados individualizada sem exigir uma palavra-passe. Para ambientes híbridos, a implementação de Implementing WPA3-Enterprise for Enhanced Wireless Security garante uma encriptação robusta de 192 bits e integra-se com RADIUS/802.1X para controlo de acesso baseado em identidade.
Guia de Implementação
A implementação de uma rede de convidados segura requer uma abordagem sistemática para garantir tanto a segurança quanto a usabilidade.
1. Definir a Topologia
Mapeie todo o caminho dos dados, desde o ponto de acesso até ao gateway de internet. Certifique-se de que as ACLs da firewall negam explicitamente o tráfego da sub-rede de convidados para quaisquer intervalos de IP privados RFC 1918.
2. Selecionar o Método de Autenticação
Escolha um mecanismo de autenticação alinhado com os seus objetivos de negócio e perfil de risco:
- Social Login: Ideal para ambientes de Retalho e Hotelaria onde a redução de atrito e a captura de dados primários para a plataforma de WiFi Analytics são primordiais.
- Verificação por SMS: Fornece um sinal de identidade mais forte e um registo de auditoria, adequado para estádios ou locais públicos que exigem responsabilização.
- Registo por Email: Equilibra a captura de dados com baixo custo de implementação, comum em centros de conferências.
- Acesso Baseado em Tempo: Gera tokens efémeros sem recolher PII, ideal para salas de espera de Saúde ou bibliotecas.

3. Configurar a Gestão de Largura de Banda
Para prevenir o esgotamento da largura de banda e garantir a disponibilidade, implemente políticas de QoS. Aplique limites de taxa por utilizador (por exemplo, 10 Mbps de download / 2 Mbps de upload) no controlador sem fios e restrinja as transferências de ficheiros em massa, priorizando o tráfego DNS e HTTPS.
4. Implementar e Testar
Antes da implementação em produção, realize um teste de segmentação. Conecte um dispositivo ao SSID de convidados e tente fazer ping a servidores internos ou aceder ao DNS corporativo. Qualquer conexão bem-sucedida indica uma falha crítica de segmentação.
Melhores Práticas
- Impor ACLs de Firewall Rigorosas: Negar por padrão todo o tráfego da VLAN de convidados para sub-redes internas. Permitir apenas tráfego de saída em portas essenciais (por exemplo, 80, 443, 53).
- Implementar Filtragem de Conteúdo: Utilize filtragem baseada em DNS para bloquear domínios maliciosos, servidores de comando e controlo de malware e conteúdo inadequado, protegendo tanto os utilizadores quanto a reputação IP do local.
- Auditar Regularmente as Configurações: Realize revisões trimestrais das configurações das portas do switch, regras da firewall e políticas do controlador sem fios para detetar desvios de configuração.
- Manter Registo Abrangente: Registar todos os alugueres DHCP, traduções NAT e eventos de autenticação. Reter estes registos por um mínimo de 12 meses para apoiar investigações forenses e cumprir as regulamentações locais.
Resolução de Problemas e Mitigação de Riscosation
Mesmo redes bem concebidas encontram problemas. Compreender os modos de falha comuns acelera a resolução.
- Pontos de Acesso Maliciosos: Funcionários ou atacantes podem ligar APs não autorizados a portas corporativas. Mitigue isto ativando a autenticação baseada em porta 802.1X em todas as portas de switch com fios e utilizando Sistemas de Prevenção de Intrusão Sem Fios (WIPS) para detetar e conter sinais maliciosos.
- Captive Portal Bypasses: Utilizadores avançados podem tentar contornar portais usando falsificação de MAC ou tunelamento de DNS. Mitigue isto implementando a deteção de aleatorização de endereços MAC e restringindo as consultas DNS de saída apenas a resolvedores aprovados.
- Esgotamento de IP: Ambientes de alta rotatividade, como centros de Transporte , podem esgotar rapidamente os pools de DHCP. Reduza os tempos de concessão de DHCP para 30-60 minutos e garanta que a máscara de sub-rede (por exemplo, /22 ou /21) fornece endereços IP suficientes para a capacidade máxima.
ROI e Impacto nos Negócios
Um guia de rede WiFi segura para convidados não é meramente um centro de custos de TI; é um ativo estratégico.
- Redução de Risco: A segmentação adequada previne violações de dados dispendiosas. O custo médio de uma violação de dados ascende a milhões; isolar o tráfego de convidados mitiga o risco de um dispositivo de visitante comprometido passar para sistemas PoS ou bases de dados internas.
- Monetização de Dados: A autenticação segura e sem atritos (como o Social Login) alimenta plataformas de marketing com dados verificados e de alta qualidade, permitindo campanhas direcionadas e aumentando o valor vitalício do cliente.
- Eficiência Operacional: O onboarding automatizado e a gestão robusta da largura de banda reduzem drasticamente os tickets de suporte de TI relacionados com problemas de conectividade, libertando recursos de engenharia para projetos estratégicos.
Briefing do Podcast
Ouça o nosso briefing técnico abrangente de 10 minutos sobre a segurança de redes de convidados:
Definições Principais
VLAN Segmentation
The logical separation of a physical network into multiple distinct broadcast domains to isolate traffic types.
Essential for keeping untrusted guest devices completely separated from sensitive corporate servers and data.
Client Isolation
A wireless controller feature that prevents devices connected to the same SSID from communicating directly with each other.
Crucial in public venues to stop a malicious guest from scanning or attacking other guests' laptops or phones.
Captive Portal
A web page that users are forced to view and interact with before access to the broader network is granted.
Used to enforce terms of service, capture marketing data, and authenticate users securely over HTTPS.
WPA3-Enhanced Open
A security certification that provides unauthenticated data encryption for open WiFi networks using Opportunistic Wireless Encryption (OWE).
Protects users from passive eavesdropping in coffee shops and airports without the friction of a shared password.
Bandwidth Rate Limiting
The intentional restriction of the maximum speed (throughput) a user or application can consume on the network.
Prevents network congestion and ensures fair access for all guests during high-footfall events.
Rogue Access Point
An unauthorised wireless access point connected to a secure enterprise network, often bypassing security controls.
A major security risk that IT teams must actively monitor for using Wireless Intrusion Prevention Systems (WIPS).
DMZ (Demilitarised Zone)
A perimeter network that protects an organisation's internal local-area network from untrusted traffic.
The correct architectural location to host a captive portal server to minimize risk if the server is compromised.
MAC Spoofing
The technique of altering the Media Access Control address of a network interface to masquerade as another device.
A common method attackers use to bypass captive portals or time-based access restrictions.
Exemplos Práticos
A 400-room luxury hotel needs to provide seamless guest WiFi while ensuring PCI DSS compliance for its separate PoS terminals in the restaurants and bars.
Deploy a dedicated Guest VLAN (e.g., VLAN 40) across all switches and APs. Enable Client Isolation on the wireless controller to prevent guest-to-guest attacks. Configure firewall ACLs to explicitly block all routing between VLAN 40 and the PoS VLAN (e.g., VLAN 20). Implement WPA3-Enhanced Open for the guest SSID to encrypt over-the-air traffic without requiring a password.
A large retail chain wants to offer free WiFi to capture customer data but is experiencing network slowdowns during peak weekend hours due to users streaming HD video.
Implement per-user bandwidth rate limiting (e.g., 5 Mbps) on the wireless controller. Configure Application Visibility and Control (AVC) to throttle streaming media categories (Netflix, YouTube) while prioritising web browsing and social media apps used for the captive portal login.
Perguntas de Prática
Q1. You are deploying guest WiFi at a major stadium. The legal team requires a verifiable audit trail of who connected to the network in case of illegal activity. Which authentication method should you implement?
Dica: Consider which method ties the user to a verifiable real-world identity.
Ver resposta modelo
SMS Verification. This requires the user to possess a physical SIM card and receive a One-Time Passcode (OTP), providing a strong identity signal and a reliable audit trail for law enforcement if required.
Q2. During a penetration test, the assessor connects to the guest WiFi and successfully accesses the management interface of a corporate printer. What is the most likely configuration failure?
Dica: Think about how traffic is routed between different network segments.
Ver resposta modelo
A failure in Layer 3 segmentation or Firewall ACLs. The guest VLAN is likely able to route traffic to the corporate VLAN where the printer resides. The firewall should be configured with an explicit 'deny' rule blocking traffic from the guest subnet to all internal RFC 1918 IP addresses.
Q3. A public library wants to offer free WiFi but absolutely cannot store any Personally Identifiable Information (PII) due to local privacy ordinances. How should they configure access?
Dica: Which method grants access without asking for a name, email, or phone number?
Ver resposta modelo
Time-Based Access using ephemeral tokens or vouchers. The system can generate a temporary access code that expires after a set duration (e.g., 2 hours). This maintains a technical log of connection events without tying them to an individual's PII.
Continue a ler esta série
Como Implementar Restrições de Tempo e de Largura de Banda em WiFi de Convidados
Um guia de referência técnica de autoridade sobre a implementação de restrições de tempo e de largura de banda em redes WiFi de convidados empresariais. Este guia fornece esquemas arquitetónicos práticos, configurações neutras em termos de fornecedor e estudos de caso reais para ajudar os líderes de TI a equilibrar o desempenho da rede, a conformidade de segurança e a experiência do visitante.
Minimizar as Distrações dos Alunos com Bloqueio de Anúncios ao Nível da Rede
Este guia de referência técnica e autoritário detalha a arquitetura, a implementação e o impacto comercial do bloqueio de anúncios ao nível da rede em ambientes educacionais. Fornece a gestores de TI e arquitetos de rede estratégias acionáveis para recuperar largura de banda, reforçar a conformidade e eliminar riscos de malvertising.
WiFi Familiar: Melhores Práticas para Centros Comerciais
Este guia de referência técnica fornece metodologias acionáveis para implementar filtragem de URL baseada em categorias em redes WiFi de convidados em ambientes de retalho. Detalha a arquitetura de rede, a definição de políticas e as estratégias de mitigação de riscos para garantir a conformidade e proteger a reputação da marca.