Sécurisation des réseaux WiFi invités : Bonnes pratiques et implémentation
Ce guide de référence technique faisant autorité décrit l'architecture, l'authentification et les contrôles opérationnels requis pour déployer un WiFi invité d'entreprise sécurisé. Il fournit des bonnes pratiques exploitables pour les responsables informatiques afin d'appliquer la segmentation du réseau, de gérer la bande passante et d'assurer la conformité tout en maximisant la capture de données.
Écouter ce guide
Voir la transcription du podcast
- Résumé Exécutif
- Approfondissement Technique
- Segmentation et Isolation du Réseau
- Architecture du Captive Portal
- Normes de chiffrement : WPA3
- Guide d'implémentation
- 1. Définir la topologie
- 2. Sélectionner la méthode d'authentification
- 3. Configurer la gestion de la bande passante
- 4. Déployer et tester
- Bonnes Pratiques
- Dépannage et atténuation des risquesation
- ROI et impact commercial
- Briefing Podcast

Résumé Exécutif
Le déploiement d'un réseau WiFi invité sécurisé exige un équilibre entre un accès utilisateur fluide et une segmentation réseau et une conformité robustes. Pour les CTOs et les architectes réseau des secteurs de la vente au détail, de l'hôtellerie et des services publics, le défi consiste à isoler les appareils invités non fiables de l'infrastructure d'entreprise tout en extrayant une valeur maximale de la capture de données de première partie. Ce guide détaille l'architecture technique, les cadres d'authentification et les contrôles opérationnels nécessaires pour implémenter un WiFi invité de niveau entreprise. Nous couvrons les pratiques essentielles, y compris la segmentation VLAN de couche 3, la sécurité du Captive Portal, la limitation de débit de bande passante et les normes de chiffrement modernes comme le WPA3. En mettant en œuvre ces bonnes pratiques indépendantes des fournisseurs, les organisations peuvent atténuer les risques de mouvement latéral, assurer la conformité réglementaire (y compris le GDPR et le PCI DSS) et transformer une potentielle vulnérabilité de sécurité en un actif sécurisé et générateur de valeur.
Approfondissement Technique
La base de tout réseau WiFi invité sécurisé est une isolation absolue des ressources de l'entreprise. Cela nécessite une approche de défense en profondeur couvrant plusieurs couches du modèle OSI.
Segmentation et Isolation du Réseau
Un déploiement robuste exige des VLANs dédiés pour le trafic invité, complètement séparés des réseaux opérationnels internes. Par exemple, le trafic invité pourrait être attribué au VLAN 30, tandis que les appareils d'entreprise résident sur le VLAN 10. Cette segmentation doit être appliquée au niveau de la couche du commutateur géré, et pas seulement du contrôleur sans fil, pour prévenir les attaques par saut de VLAN.
De plus, l'isolation client (ou isolation de couche 2) est critique. Cela empêche les appareils connectés au même SSID Guest WiFi de communiquer entre eux. Sans isolation client, un seul appareil compromis peut scanner le sous-réseau local, exécuter l'usurpation ARP et lancer des attaques latérales contre d'autres invités.
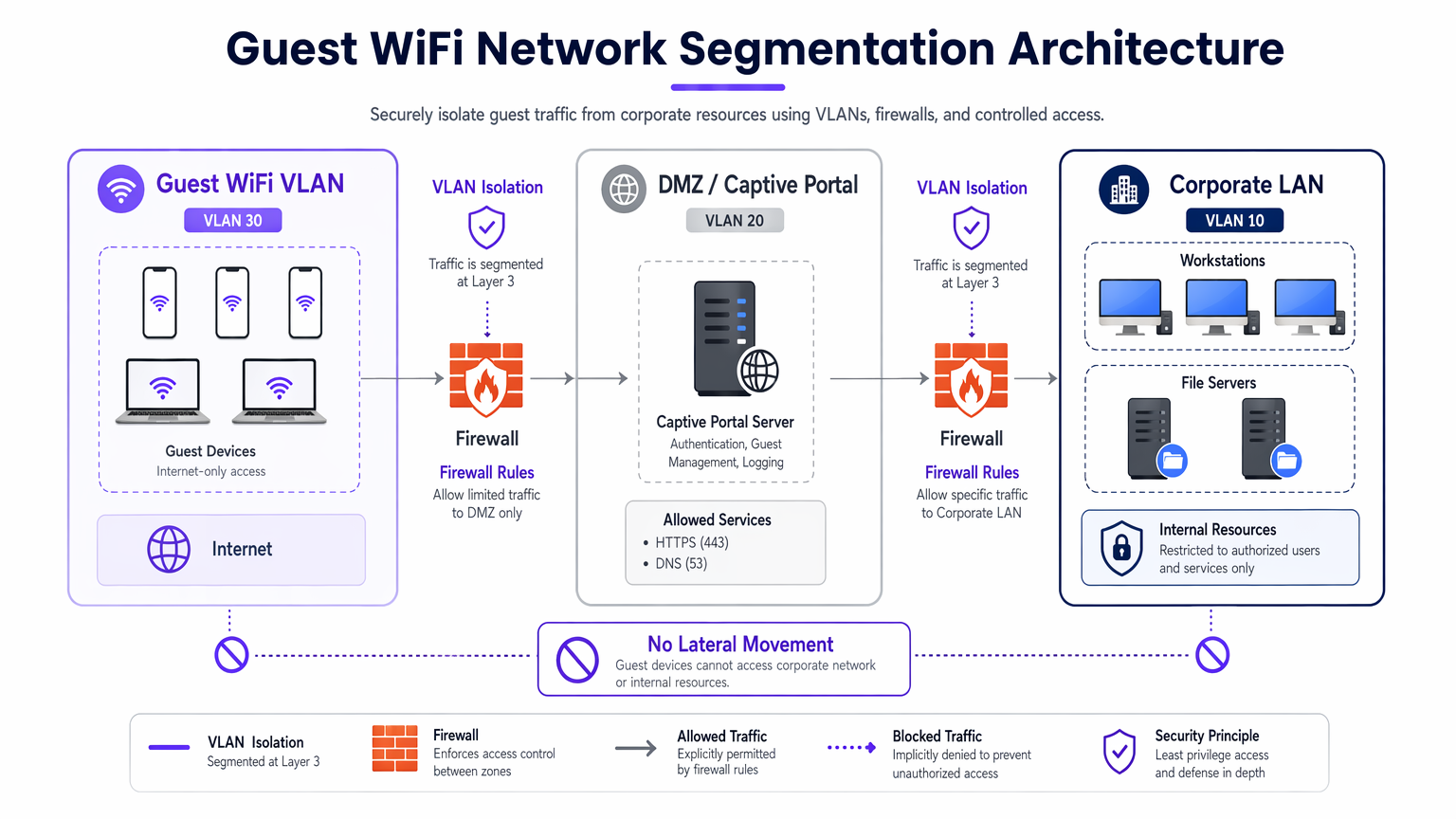
Architecture du Captive Portal
Le Captive Portal sert de passerelle pour l'authentification et l'application des politiques. Pour prévenir l'interception des identifiants, le portail doit être servi exclusivement via HTTPS en utilisant un certificat TLS valide. Le serveur du portail doit résider dans une DMZ, isolé des bases de données internes. Cela garantit que même si le portail est compromis, les attaquants ne peuvent pas pivoter vers le LAN de l'entreprise.
Normes de chiffrement : WPA3
Les réseaux ouverts hérités transmettent les données en clair, exposant les utilisateurs à l'écoute passive. Les déploiements modernes devraient exiger le WPA3. Pour les réseaux publics, WPA3-Enhanced Open (Opportunistic Wireless Encryption) fournit un chiffrement de données individualisé sans nécessiter de mot de passe. Pour les environnements hybrides, le déploiement de Implementing WPA3-Enterprise for Enhanced Wireless Security assure un chiffrement robuste de 192 bits et s'intègre avec RADIUS/802.1X pour un contrôle d'accès basé sur l'identité.
Guide d'implémentation
L'implémentation d'un réseau invité sécurisé nécessite une approche systématique pour garantir à la fois la sécurité et la convivialité.
1. Définir la topologie
Cartographiez l'ensemble du chemin de données, du point d'accès à la passerelle Internet. Assurez-vous que les ACLs du pare-feu refusent explicitement le trafic du sous-réseau invité vers toutes les plages d'adresses IP privées RFC 1918.
2. Sélectionner la méthode d'authentification
Choisissez un mécanisme d'authentification aligné sur vos objectifs commerciaux et votre profil de risque :
- Social Login : Idéal pour les environnements de Retail et d' Hospitality où la réduction des frictions et la capture de données de première partie pour la plateforme WiFi Analytics sont primordiales.
- SMS Verification : Fournit un signal d'identité et une piste d'audit plus solides, adapté aux stades ou aux lieux publics nécessitant une responsabilisation.
- Email Registration : Équilibre la capture de données avec un faible coût de déploiement, courant dans les centres de conférence.
- Time-Based Access : Génère des jetons éphémères sans collecter de PII, optimal pour les salles d'attente Healthcare ou les bibliothèques.

3. Configurer la gestion de la bande passante
Pour prévenir l'épuisement de la bande passante et assurer la disponibilité, implémentez des politiques QoS. Appliquez des limites de débit par utilisateur (par exemple, 10 Mbps en téléchargement / 2 Mbps en téléversement) au niveau du contrôleur sans fil, et restreignez les transferts de fichiers volumineux tout en priorisant le trafic DNS et HTTPS.
4. Déployer et tester
Avant le déploiement en production, effectuez un test de segmentation. Connectez un appareil au SSID invité et tentez de "pinger" les serveurs internes ou d'accéder au DNS de l'entreprise. Toute connexion réussie indique une défaillance critique de la segmentation.
Bonnes Pratiques
- Appliquer des ACLs de pare-feu strictes : Refuser par défaut tout le trafic du VLAN invité vers les sous-réseaux internes. N'autoriser le trafic sortant que sur les ports essentiels (par exemple, 80, 443, 53).
- Implémenter le filtrage de contenu : Utilisez le filtrage basé sur DNS pour bloquer les domaines malveillants, les serveurs de commande et de contrôle de logiciels malveillants, et le contenu inapproprié, protégeant ainsi les utilisateurs et la réputation IP du lieu.
- Auditer régulièrement les configurations : Effectuez des examens trimestriels des configurations des ports de commutateur, des règles de pare-feu et des politiques du contrôleur sans fil pour détecter la dérive de configuration.
- Maintenir une journalisation complète : Enregistrez tous les baux DHCP, les traductions NAT et les événements d'authentification. Conservez ces journaux pendant un minimum de 12 mois pour soutenir les enquêtes forensiques et se conformer aux réglementations locales.
Dépannage et atténuation des risquesation
Même les réseaux bien conçus rencontrent des problèmes. Comprendre les modes de défaillance courants accélère la résolution.
- Points d'accès non autorisés : Les employés ou les attaquants peuvent brancher des points d'accès non autorisés sur les ports de l'entreprise. Atténuez ce risque en activant l'authentification 802.1X basée sur les ports sur tous les ports de commutateur câblés et en utilisant des systèmes de prévention d'intrusion sans fil (WIPS) pour détecter et contenir les signaux non autorisés.
- Contournements de Captive Portal : Les utilisateurs avancés peuvent tenter de contourner les portails en utilisant l'usurpation d'adresse MAC ou le tunneling DNS. Atténuez ce risque en mettant en œuvre la détection de la randomisation d'adresse MAC et en limitant les requêtes DNS sortantes aux résolveurs approuvés uniquement.
- Épuisement des adresses IP : Les environnements à fort roulement comme les pôles de Transport peuvent rapidement épuiser les pools DHCP. Réduisez les durées de bail DHCP à 30-60 minutes et assurez-vous que le masque de sous-réseau (par exemple, /22 ou /21) fournit suffisamment d'adresses IP pour la capacité maximale.
ROI et impact commercial
Un guide pour un réseau WiFi invité sécurisé n'est pas seulement un centre de coûts informatiques ; c'est un atout stratégique.
- Réduction des risques : Une segmentation appropriée prévient les violations de données coûteuses. Le coût moyen d'une violation de données se chiffre en millions ; l'isolation du trafic invité atténue le risque qu'un appareil visiteur compromis ne se tourne vers les systèmes de point de vente (PoS) ou les bases de données internes.
- Monétisation des données : Une authentification sécurisée et sans friction (comme la connexion sociale) alimente les plateformes marketing avec des données vérifiées de haute qualité, permettant des campagnes ciblées et augmentant la valeur vie client.
- Efficacité opérationnelle : L'intégration automatisée et une gestion robuste de la bande passante réduisent considérablement les tickets de support informatique liés aux problèmes de connectivité, libérant ainsi des ressources d'ingénierie pour des projets stratégiques.
Briefing Podcast
Écoutez notre briefing technique complet de 10 minutes sur la sécurisation des réseaux invités :
Définitions clés
VLAN Segmentation
The logical separation of a physical network into multiple distinct broadcast domains to isolate traffic types.
Essential for keeping untrusted guest devices completely separated from sensitive corporate servers and data.
Client Isolation
A wireless controller feature that prevents devices connected to the same SSID from communicating directly with each other.
Crucial in public venues to stop a malicious guest from scanning or attacking other guests' laptops or phones.
Captive Portal
A web page that users are forced to view and interact with before access to the broader network is granted.
Used to enforce terms of service, capture marketing data, and authenticate users securely over HTTPS.
WPA3-Enhanced Open
A security certification that provides unauthenticated data encryption for open WiFi networks using Opportunistic Wireless Encryption (OWE).
Protects users from passive eavesdropping in coffee shops and airports without the friction of a shared password.
Bandwidth Rate Limiting
The intentional restriction of the maximum speed (throughput) a user or application can consume on the network.
Prevents network congestion and ensures fair access for all guests during high-footfall events.
Rogue Access Point
An unauthorised wireless access point connected to a secure enterprise network, often bypassing security controls.
A major security risk that IT teams must actively monitor for using Wireless Intrusion Prevention Systems (WIPS).
DMZ (Demilitarised Zone)
A perimeter network that protects an organisation's internal local-area network from untrusted traffic.
The correct architectural location to host a captive portal server to minimize risk if the server is compromised.
MAC Spoofing
The technique of altering the Media Access Control address of a network interface to masquerade as another device.
A common method attackers use to bypass captive portals or time-based access restrictions.
Exemples concrets
A 400-room luxury hotel needs to provide seamless guest WiFi while ensuring PCI DSS compliance for its separate PoS terminals in the restaurants and bars.
Deploy a dedicated Guest VLAN (e.g., VLAN 40) across all switches and APs. Enable Client Isolation on the wireless controller to prevent guest-to-guest attacks. Configure firewall ACLs to explicitly block all routing between VLAN 40 and the PoS VLAN (e.g., VLAN 20). Implement WPA3-Enhanced Open for the guest SSID to encrypt over-the-air traffic without requiring a password.
A large retail chain wants to offer free WiFi to capture customer data but is experiencing network slowdowns during peak weekend hours due to users streaming HD video.
Implement per-user bandwidth rate limiting (e.g., 5 Mbps) on the wireless controller. Configure Application Visibility and Control (AVC) to throttle streaming media categories (Netflix, YouTube) while prioritising web browsing and social media apps used for the captive portal login.
Questions d'entraînement
Q1. You are deploying guest WiFi at a major stadium. The legal team requires a verifiable audit trail of who connected to the network in case of illegal activity. Which authentication method should you implement?
Conseil : Consider which method ties the user to a verifiable real-world identity.
Voir la réponse type
SMS Verification. This requires the user to possess a physical SIM card and receive a One-Time Passcode (OTP), providing a strong identity signal and a reliable audit trail for law enforcement if required.
Q2. During a penetration test, the assessor connects to the guest WiFi and successfully accesses the management interface of a corporate printer. What is the most likely configuration failure?
Conseil : Think about how traffic is routed between different network segments.
Voir la réponse type
A failure in Layer 3 segmentation or Firewall ACLs. The guest VLAN is likely able to route traffic to the corporate VLAN where the printer resides. The firewall should be configured with an explicit 'deny' rule blocking traffic from the guest subnet to all internal RFC 1918 IP addresses.
Q3. A public library wants to offer free WiFi but absolutely cannot store any Personally Identifiable Information (PII) due to local privacy ordinances. How should they configure access?
Conseil : Which method grants access without asking for a name, email, or phone number?
Voir la réponse type
Time-Based Access using ephemeral tokens or vouchers. The system can generate a temporary access code that expires after a set duration (e.g., 2 hours). This maintains a technical log of connection events without tying them to an individual's PII.
Continuer la lecture de cette série
Minimiser les distractions des étudiants grâce au blocage des publicités au niveau du réseau
Ce guide de référence technique faisant autorité détaille l'architecture, le déploiement et l'impact commercial du blocage des publicités au niveau du réseau dans les environnements éducatifs. Il fournit aux responsables informatiques et aux architectes réseau des stratégies concrètes pour récupérer de la bande passante, renforcer la conformité et éliminer les risques de malvertising.
WiFi familial : Meilleures pratiques pour les centres commerciaux
Ce guide de référence technique fournit des méthodologies exploitables pour la mise en œuvre du filtrage d'URL basé sur des catégories sur les réseaux WiFi invités dans les environnements de vente au détail. Il détaille l'architecture réseau, la définition des politiques et les stratégies d'atténuation des risques afin d'assurer la conformité et de protéger la réputation de la marque.
Accès invité sécurisé : Implémentation du NAC pour les appareils non gérés
Ce guide de référence technique faisant autorité détaille l'architecture, le déploiement et les considérations de conformité pour l'implémentation du contrôle d'accès réseau (NAC) afin de sécuriser les appareils invités non gérés. Il fournit des conseils exploitables aux responsables informatiques pour obtenir un accès invité sécurisé sans compromettre l'infrastructure de l'entreprise.