Purple vs Tanaza: Captive Portal Platforms Compared
This technical reference guide provides a vendor-neutral comparison of Purple and Tanaza for SMB and mid-market Captive Portal deployments. It evaluates both platforms across technical architecture, hardware compatibility, compliance posture, and pricing to help IT leaders align their network access strategy with measurable business outcomes.
🎧 Listen to this Guide
View Transcript

Executive Summary
For IT managers and network architects evaluating Captive Portal platforms, the choice between Purple and Tanaza represents a fundamental architectural decision. Tanaza operates primarily as a cloud-based network management platform with built-in Captive Portal features, designed for MSPs managing multi-vendor SMB deployments via custom firmware. Purple, conversely, functions as an enterprise-grade guest intelligence layer that sits above existing network infrastructure via external Captive Portal redirects, transforming standard Guest WiFi into a data capture and analytics engine.
This guide breaks down the technical differences, deployment models, and total cost of ownership for both platforms. Whether you are upgrading a single 200-room hotel or deploying across a 50-site Retail chain, understanding where each platform excels will prevent costly architectural refactoring down the line.
Technical Deep-Dive
Architectural Approaches
The most significant differentiator between the two platforms is how they interact with your underlying network hardware.
Tanaza relies on TanazaOS, a Linux-based operating system that must be flashed onto compatible access points (or purchased pre-installed on Tanaza Powered Devices). This gives Tanaza deep control over the access point, enabling zero-touch provisioning, real-time load monitoring, and channel optimisation directly from their cloud dashboard. However, this approach requires replacing the OEM firmware, which can void warranties and limits hardware choices to supported models from vendors like TP-Link, Ubiquiti, and MikroTik.
Purple adopts an overlay architecture. It integrates with over 50 enterprise hardware vendors—including Cisco Meraki, Aruba, Ruckus, and Juniper Mist—via standard external Captive Portal redirects and RADIUS authentication. No firmware modification is required. This makes Purple significantly lower risk for mid-market and enterprise deployments where existing high-performance infrastructure is already in place. For more on how this integrates with broader network design, see our Internet of Things Architecture: A Complete Guide .
Captive Portal Capabilities
Tanaza's built-in splash page provides functional, straightforward guest access. It supports click-through agreements and code-based logins natively. However, it lacks native social login capabilities (Google, Facebook, Apple) and requires third-party integrations like DataWiFi to achieve this.
Purple's Captive Portal is built for data acquisition and marketing compliance. It natively supports a wide array of authentication methods, including social logins, SMS OTP, and email capture with real-time verification. The drag-and-drop builder supports 25 languages and allows for deep brand customisation.
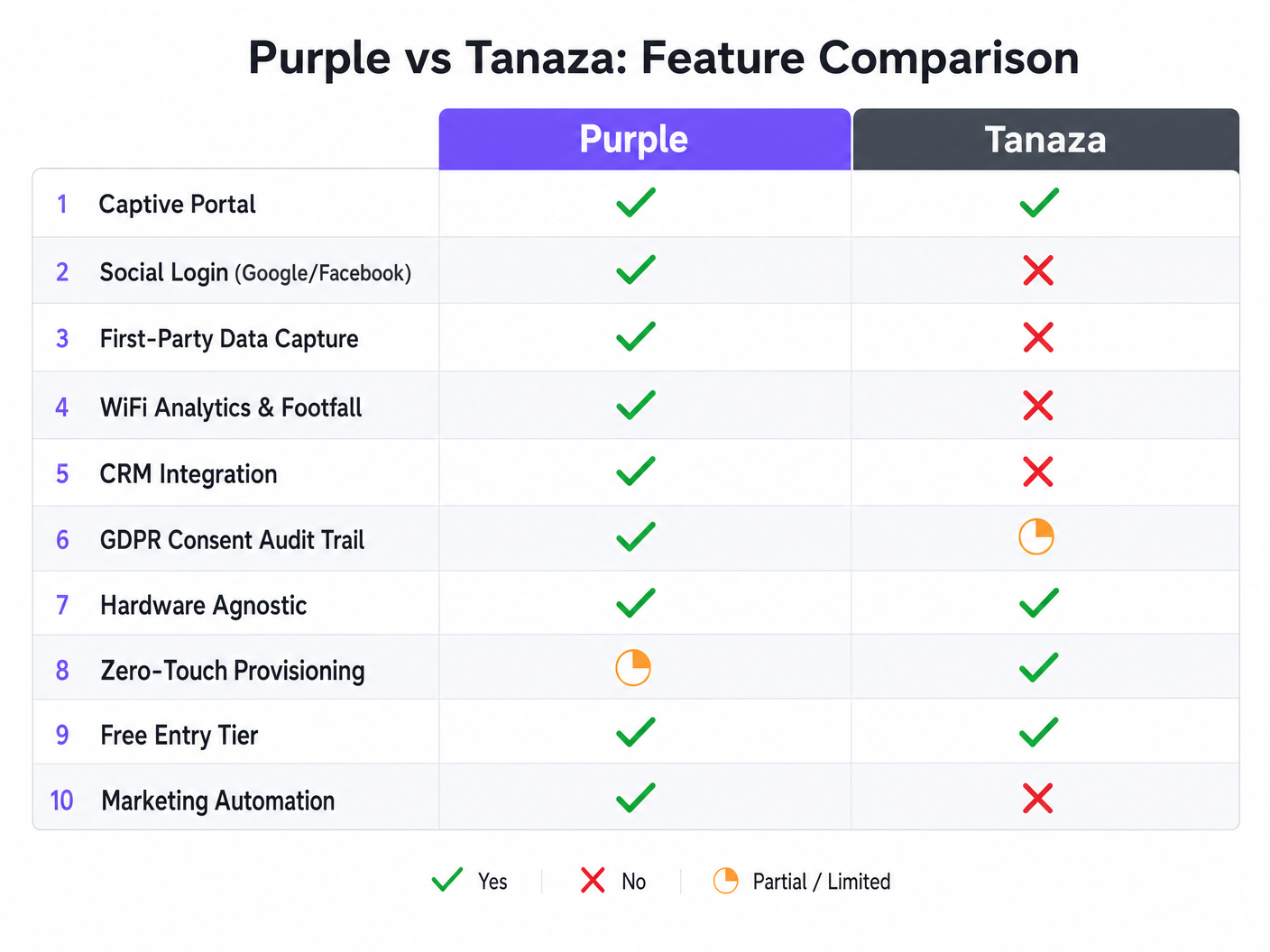
Compliance and Security
When deploying guest networks in Healthcare or public sectors, compliance is non-negotiable. Tanaza allows administrators to configure terms and conditions, but the burden of demonstrating GDPR compliance largely falls on the operator.
Purple embeds compliance into the onboarding flow. It maintains a full audit trail of user consent, handles data retention policies automatically, and provides built-in workflows for right-to-erasure requests. This architecture is designed to meet the strict requirements of GDPR, CCPA, and LGPD out of the box. For specific regional compliance strategies, refer to our Brazil LGPD and Guest WiFi: A Compliance Guide .
Implementation Guide
Deploying Tanaza
- Hardware Selection: Verify your access points are on the Tanaza supported list or purchase Tanaza Powered Devices.
- Firmware Flashing: If using existing hardware, follow the specific flashing instructions to install TanazaOS. This step requires technical proficiency and physical access to the APs or a staging environment.
- Cloud Provisioning: Add the MAC addresses to the Tanaza cloud dashboard.
- Network Configuration: Configure SSIDs, VLAN tagging, and bandwidth limits centrally.
- Portal Setup: Enable the built-in splash page and configure the basic click-through terms.
Deploying Purple
- Infrastructure Integration: Configure your existing WLC or cloud controller (e.g., Meraki Dashboard, Aruba Central) to point to Purple's external Captive Portal URLs and RADIUS servers.
- Portal Design: Use the Purple portal builder to design the splash page, configure social login APIs, and set data capture requirements.
- Compliance Configuration: Set data retention limits and configure the privacy policy links within the Purple dashboard.
- CRM Mapping: Connect Purple to your CRM (e.g., Salesforce, HubSpot) and map the captured demographic data fields to your contact records.
Listen to our senior consultant briefing for a deeper dive into these deployment strategies:
Best Practices
- Define the Business Outcome First: If the goal is purely operational network management for a small deployment, prioritise Tanaza's zero-touch provisioning. If the goal is marketing intelligence and WiFi Analytics , Purple is the required architecture.
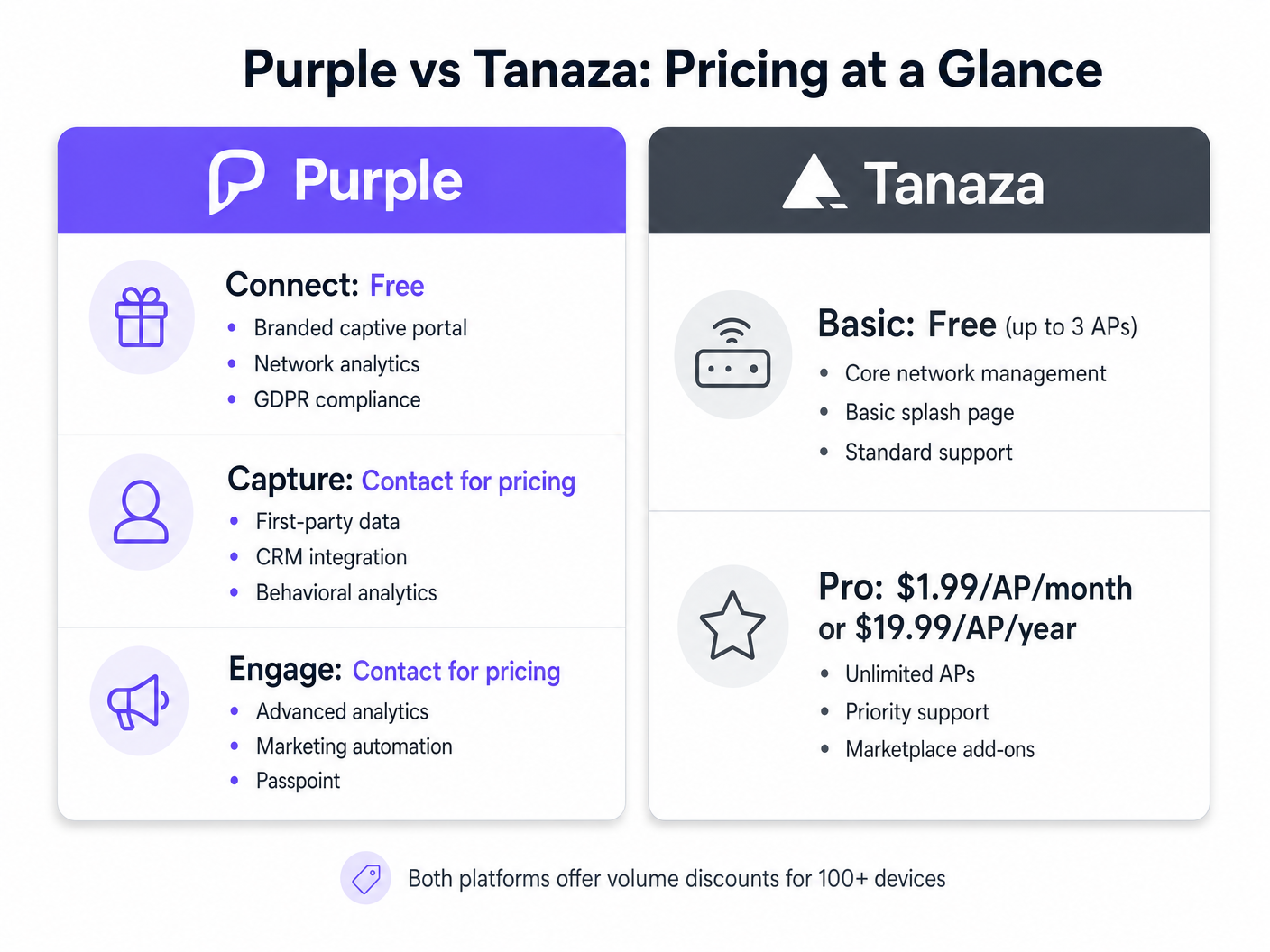
- Evaluate Total Cost of Ownership (TCO): Tanaza's Pro tier charges a flat per-AP monthly fee. Purple ofoffers a robust free tier (Connect) for basic branded access and compliance, with paid tiers (Capture and Engage) scaling based on advanced analytics and CRM integration requirements. Factor in the cost of third-party add-ons if attempting to build marketing features on top of Tanaza.
- Future-Proof Hardware Decisions: Relying on custom firmware limits future hardware flexibility. Overlay architectures preserve your ability to migrate underlying hardware vendors without rebuilding the captive portal experience.
Troubleshooting & Risk Mitigation
Risk: Scope Creep in Marketing Requirements Many IT teams deploy a basic captive portal only to have the marketing department request CRM integration and footfall analytics six months later. Mitigation: If marketing requirements are anticipated, deploy an overlay architecture like Purple from day one to avoid a costly platform migration later.
Risk: Firmware Bricking during Installation Flashing custom firmware onto APs carries a small but non-zero risk of bricking the device. Mitigation: If deploying Tanaza, utilise a staging environment to flash and test APs before shipping them to the deployment site, or purchase pre-flashed Tanaza Powered Devices.
ROI & Business Impact
The return on investment for captive portal platforms is measured differently depending on the architecture chosen.
For Tanaza deployments, ROI is typically measured in operational efficiency. The ability to manage multi-vendor APs from a single pane of glass reduces truck rolls and simplifies troubleshooting for MSPs.
For Purple deployments, ROI is measured in data acquisition and operational intelligence. By capturing verified first-party data and tracking physical dwell times, venues can automate marketing campaigns that drive repeat visits. In Hospitality and retail environments, this transforms the WiFi network from an IT expense into a measurable revenue driver.
Key Terms & Definitions
External Captive Portal
A mechanism where the network controller redirects unauthenticated users to a splash page hosted on an external server, rather than serving the page locally from the access point.
This is the architecture Purple uses to remain hardware-agnostic and scalable across enterprise deployments.
Zero-Touch Provisioning
The ability to configure a network device remotely so that it automatically downloads its configuration from the cloud the moment it is connected to the internet.
Crucial for MSPs deploying Tanaza to multiple remote sites without sending specialized IT staff.
First-Party Data
Information a company collects directly from its customers, such as email addresses and demographics gathered during WiFi authentication.
The primary value driver for marketing teams utilizing Purple's Capture and Engage tiers.
Firmware Flashing
The process of overwriting the original manufacturer's operating system on a hardware device with a custom operating system.
Required when deploying Tanaza on third-party hardware to enable cloud management.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
Used by both platforms to securely authenticate users and enforce bandwidth or time limits.
Dwell Time
The measurable duration a visitor spends within a specific physical location or zone, tracked via their device's WiFi probe requests.
A key operational metric provided by Purple's analytics engine, used heavily in retail and hospitality.
Audit Trail
A secure, immutable record of user actions, specifically relating to when and how a user consented to data processing terms.
Essential for demonstrating compliance with GDPR and other privacy regulations during an audit.
Overlay Architecture
A software or service layer that operates independently of the underlying physical network infrastructure.
Allows platforms like Purple to provide unified analytics across disparate hardware environments.
Case Studies
A 350-room hotel chain needs to deploy a captive portal across 12 properties. They currently use a mix of older Ruckus ZoneDirectors and new Cisco Meraki MR access points. They require GDPR-compliant guest access and want to integrate guest emails with their central HubSpot CRM.
The IT team should deploy Purple using the overlay architecture. They will configure the Ruckus ZoneDirectors and Meraki dashboards to redirect guest traffic to Purple's external captive portal. In the Purple dashboard, they will build a unified splash page, enable the HubSpot native integration, and configure the GDPR consent workflows.
A regional Managed Service Provider (MSP) is deploying WiFi for 40 small independent coffee shops. The shops need basic click-through WiFi access. The MSP wants to minimize hardware costs and manage all 40 sites from a single dashboard.
The MSP should deploy Tanaza. They can purchase cost-effective access points (e.g., TP-Link or Ubiquiti), flash them with TanazaOS in a staging lab, and ship them to the coffee shops for zero-touch provisioning. They will use Tanaza's multi-site dashboard to monitor AP health and configure a basic click-through splash page for each location.
Scenario Analysis
Q1. A stadium IT director wants to monetize their high-density WiFi network by displaying sponsor advertisements on the splash page and capturing fan emails for the ticketing CRM. They have a newly installed Cisco Catalyst network. Which platform should they choose?
💡 Hint:Consider the requirement for CRM integration and the existing enterprise hardware.
Show Recommended Approach
They should choose Purple. Purple integrates natively with Cisco Catalyst WLCs without requiring firmware changes, which is critical for a high-density stadium deployment. Furthermore, Purple's native CRM integrations and advanced splash page builder support the marketing and monetization requirements, whereas Tanaza would require third-party add-ons and firmware flashing that is incompatible with enterprise Cisco controllers.
Q2. A franchise owner of 15 fast-food restaurants needs to replace aging consumer-grade routers. They have a very tight budget, no dedicated IT staff, and just want to offer customers 30 minutes of free WiFi without capturing data. What is the recommended approach?
💡 Hint:Focus on the need for low-cost hardware and simplified multi-site management without marketing needs.
Show Recommended Approach
They should choose Tanaza. The franchise can purchase low-cost hardware like TP-Link or Ubiquiti, utilize Tanaza's zero-touch provisioning for easy deployment without on-site IT staff, and use the built-in splash page to enforce the 30-minute limit. The Tanaza Pro tier provides cost-effective centralized management for this exact scenario.
Q3. An enterprise retail chain operating in the EU is migrating to Juniper Mist access points. They need to ensure their guest WiFi captures explicit, auditable consent for marketing communications to comply with GDPR. How should they architecture this?
💡 Hint:Evaluate how both platforms handle compliance and their compatibility with Juniper Mist.
Show Recommended Approach
They must deploy Purple as an overlay on the Juniper Mist infrastructure. Purple natively supports Juniper Mist via external captive portal integration. More importantly, Purple's architecture is designed to capture and store auditable GDPR consent records per user, providing the necessary legal protection for the retail chain's marketing activities.



