NHS Staff WiFi: How to Deploy Secure Wireless Networks in Healthcare
This technical reference guide details the architecture, security protocols, and deployment strategies for NHS Staff WiFi, covering 802.1X authentication, VLAN segmentation, BYOD policies, and DSP Toolkit compliance. It provides actionable guidance for IT leaders on deploying enterprise-grade wireless networks that serve clinical, administrative, and guest users on shared physical infrastructure without compromising security. Whether you are planning a new deployment or hardening an existing estate, this guide delivers the decision frameworks and implementation steps needed to act this quarter.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Authentication and Access Control
- Network Segmentation and Trust Zones
- The BYOD Challenge
- Implementation Guide
- Phase 1: Assessment and Design
- Phase 2: Infrastructure Configuration
- Phase 3: Policy Enforcement and Onboarding
- Phase 4: Testing and Validation
- Best Practices
- Troubleshooting & Risk Mitigation
- Authentication Timeouts
- Roaming Issues
- Legacy Device Incompatibility
- Certificate Expiry
- ROI & Business Impact
Executive Summary
Deploying secure, reliable WiFi across NHS estates is no longer an optional amenity — it is critical clinical infrastructure. The shift towards mobile-first patient care, electronic health records (EHR), and connected medical devices demands a wireless architecture that balances seamless roaming with stringent security controls.
For IT managers, network architects, and CTOs, the core challenge is accommodating diverse user groups — clinical staff, administrative personnel, patients, and guests — on shared physical infrastructure without compromising the NHS Data Security and Protection (DSP) Toolkit requirements. This guide details the technical requirements for NHS Staff WiFi, focusing on robust authentication frameworks like IEEE 802.1X, logical network segmentation via VLANs, and the secure onboarding of Bring Your Own Device (BYOD) endpoints.
By moving away from legacy Pre-Shared Keys (PSK) and adopting identity-driven access policies, healthcare organisations can mitigate breach risk, reduce operational friction, and provide the wireless foundation for digital transformation programmes. The commercial case is equally strong: reduced helpdesk overhead, demonstrable DSP Toolkit compliance, and a network capable of supporting future clinical innovation without requiring a full infrastructure rebuild.
Technical Deep-Dive
Authentication and Access Control
The foundation of a secure healthcare wireless network is identity-based access control. Legacy WPA2-Personal networks using Pre-Shared Keys are fundamentally unsuited for clinical environments. They offer no individual accountability, complicate the offboarding process when staff leave, and present a single point of failure if the credential is compromised or shared beyond the intended group.
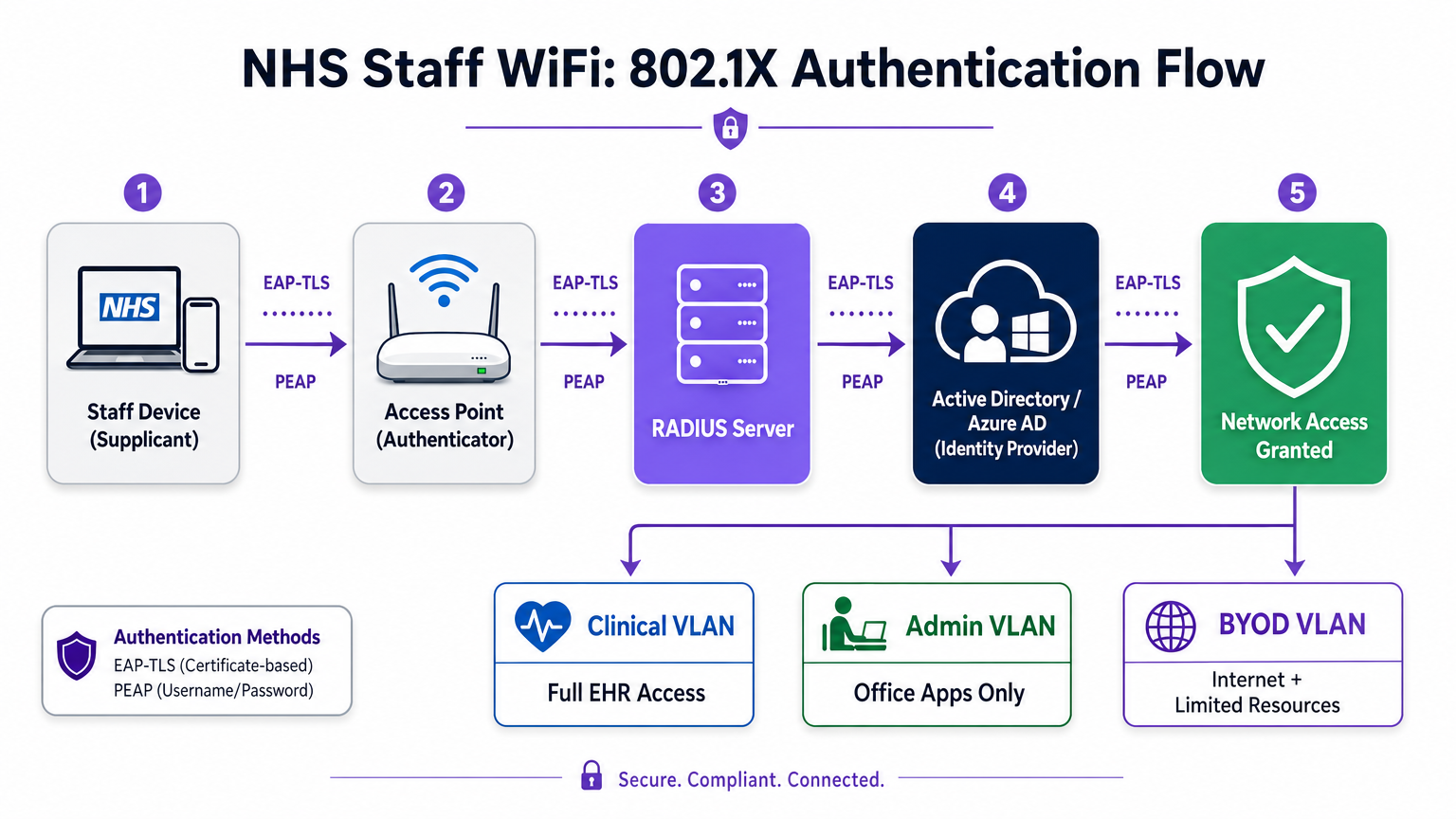
Modern NHS deployments must mandate WPA3-Enterprise (or WPA2-Enterprise as a minimum transition state) using IEEE 802.1X authentication. This framework requires every user or device to present unique credentials before network access is granted, and the result of that authentication determines which logical network segment the device is placed on.
Two EAP methods dominate healthcare deployments:
| EAP Method | Authentication Mechanism | Best Suited For | Security Level |
|---|---|---|---|
| EAP-TLS | Client-side digital certificate | Corporate-managed clinical devices | Highest — no password to phish |
| PEAP-MSCHAPv2 | Username/password in encrypted tunnel | BYOD, admin staff, legacy devices | High — credentials protected by TLS |
EAP-TLS is the gold standard for corporate devices. Certificates are distributed via Mobile Device Management (MDM) platforms, enabling zero-touch authentication — the device authenticates silently in the background. PEAP-MSCHAPv2 securely tunnels Active Directory or Azure AD credentials inside an encrypted TLS session, making it suitable for BYOD scenarios where certificate management is impractical.
Integrating the wireless infrastructure with the organisation's central identity provider (IdP) ensures that access is automatically revoked when a staff member's AD account is disabled, directly satisfying DSP Toolkit requirements for access lifecycle management.
Network Segmentation and Trust Zones
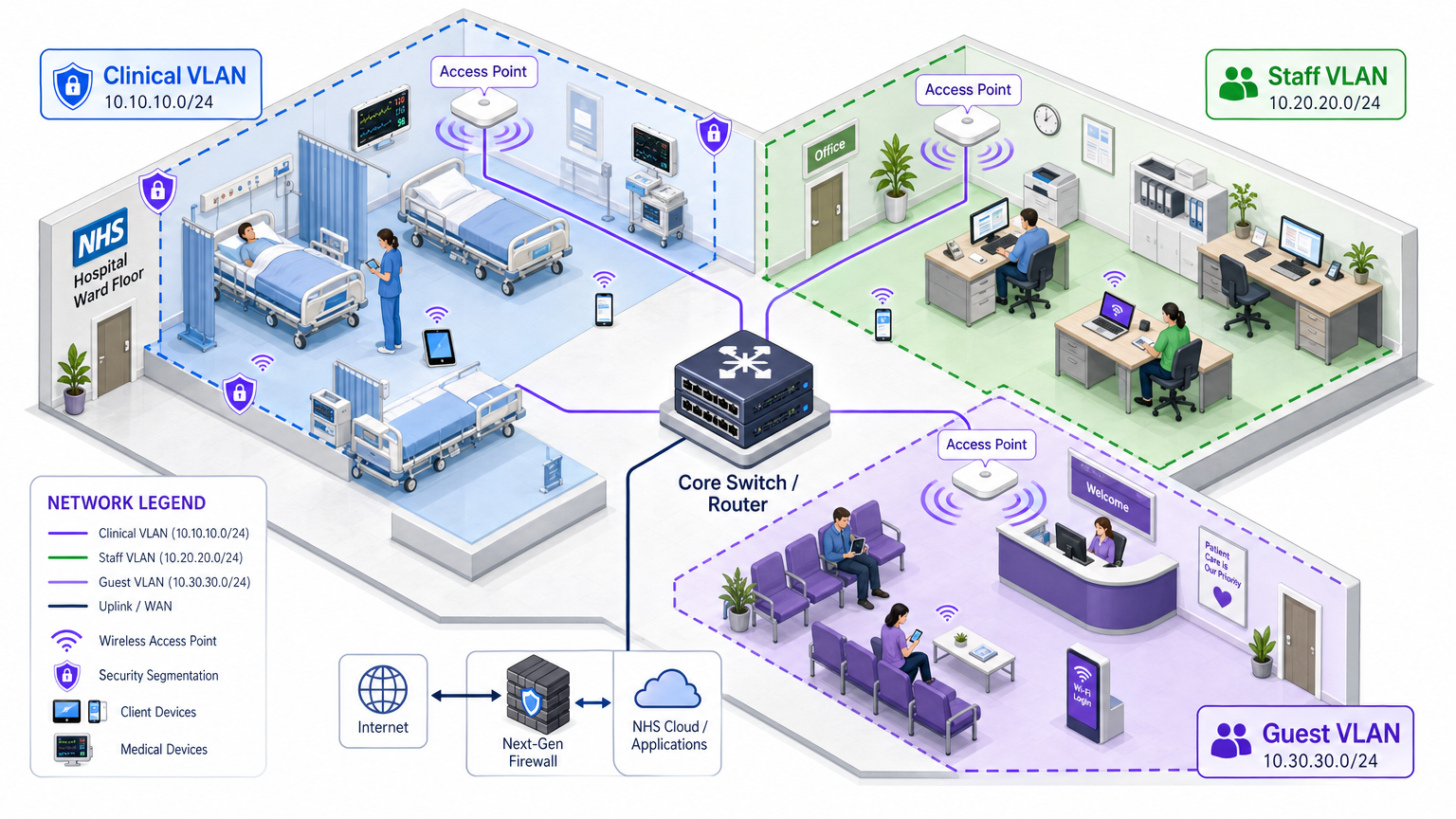
Physical access points broadcast across the entire hospital floor, but logical segmentation ensures that traffic remains isolated based on the principle of least privilege. A flat network architecture in a healthcare setting is a severe security vulnerability, allowing a compromised guest device or vulnerable IoT sensor to potentially pivot to clinical systems.
Best practice dictates creating distinct Virtual Local Area Networks (VLANs) mapped to specific SSIDs, with firewall rules enforcing traffic boundaries between them:
| Zone | SSID | Authentication | Access | QoS Priority |
|---|---|---|---|---|
| Clinical | NHS-Clinical | EAP-TLS (certificate) | EHR, PACS, clinical messaging | Highest |
| Administrative | NHS-Staff | PEAP (AD credentials) | Office apps, internet | Medium |
| Medical IoT | Hidden/MAB | MAC Authentication Bypass | Device controller only | High |
| Guest / Patient | NHS-Guest | Captive portal | Internet only | Low |
| BYOD | NHS-BYOD | PEAP (AD credentials) | Internet, limited VDI | Low |
The Medical IoT VLAN deserves particular attention. Many connected medical devices — infusion pumps, patient monitors, wireless call systems — cannot support 802.1X. MAC Authentication Bypass (MAB) is the fallback, but it must be paired with strict firewall Access Control Lists (ACLs) that restrict these devices to communicating only with their designated management servers.
The BYOD Challenge
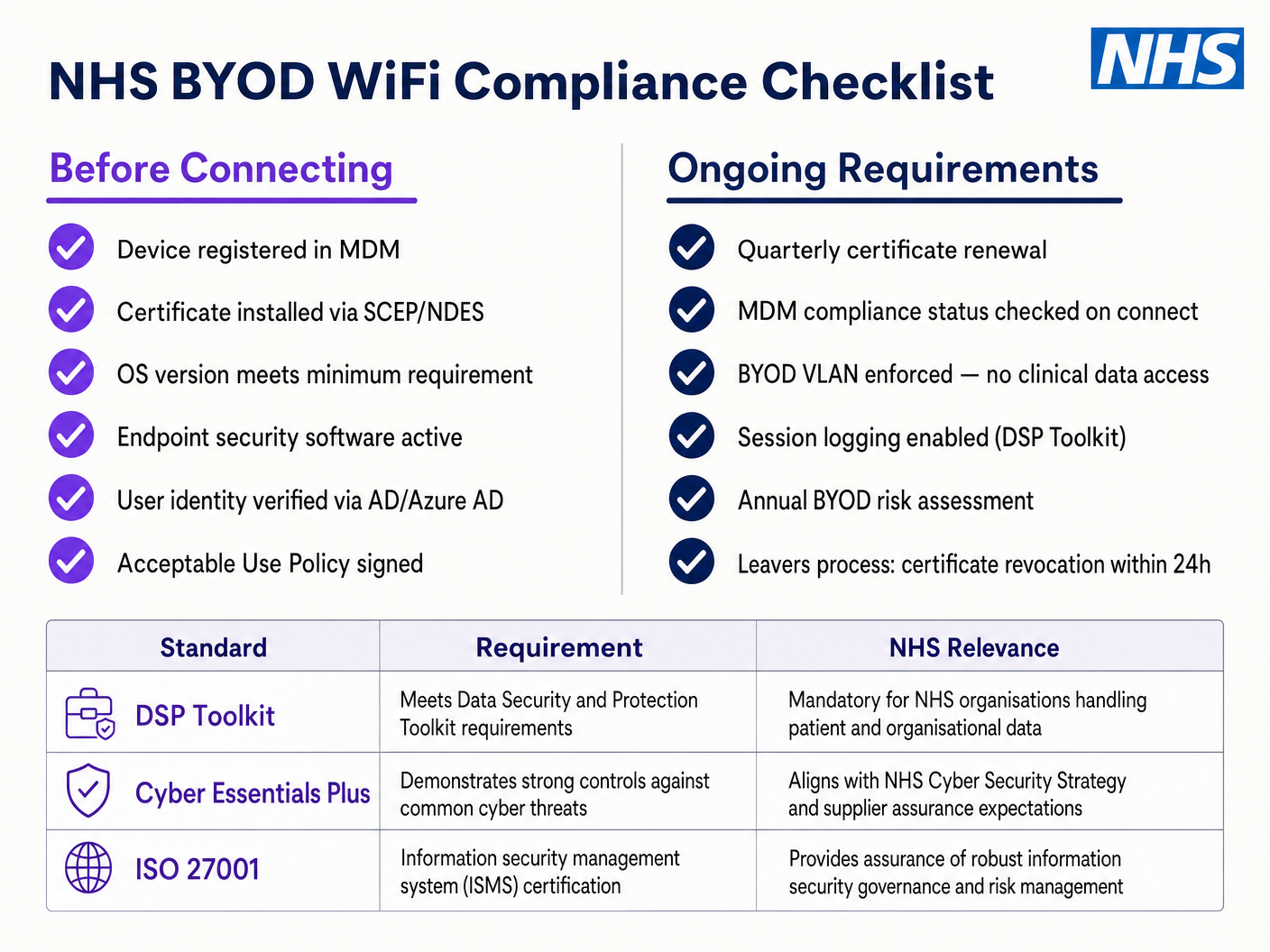
Bring Your Own Device policies are increasingly common for administrative staff and visiting clinicians. However, unmanaged personal devices represent a significant risk if allowed onto trusted network segments.
A secure BYOD deployment involves onboarding these devices onto a dedicated BYOD VLAN. This zone provides internet access and perhaps limited access to specific, non-sensitive internal resources via a secure gateway or Virtual Desktop Infrastructure (VDI). It must absolutely not have direct routing to clinical systems or patient data stores.
Implementation Guide
Deploying a secure NHS Staff WiFi architecture requires a phased approach to minimise disruption to ongoing clinical operations.
Phase 1: Assessment and Design
Begin with a comprehensive wireless site survey. Healthcare environments are notoriously difficult for RF propagation due to lead-lined walls, heavy machinery, and dense occupancy. The design must account for capacity, not just coverage, ensuring sufficient access point density in high-traffic areas like emergency departments and outpatient clinics.
Define the required SSIDs and map them to the corresponding VLANs and security policies. Keep the number of broadcast SSIDs to a minimum — ideally no more than four — to reduce management overhead and minimise beacon frame congestion, which degrades overall network performance.
Phase 2: Infrastructure Configuration
Configure the core switching and routing infrastructure to support the defined VLANs. Implement firewall rules at the boundaries between segments to enforce least privilege. Set up the RADIUS server (e.g., Cisco ISE, Aruba ClearPass, or a cloud-based RADIUS-as-a-Service) and integrate it with the central identity provider. For environments where Purple's platform is deployed, integrating WiFi Analytics at this stage provides visibility into network utilisation, roaming patterns, and capacity hotspots.
Phase 3: Policy Enforcement and Onboarding
Deploy the authentication policies. For corporate devices, utilise the MDM solution to push the necessary wireless profiles and client certificates (for EAP-TLS). This ensures that managed devices connect automatically and securely without user intervention.
For BYOD, establish a clear onboarding workflow — typically an onboarding portal that guides the user through authenticating with their corporate credentials, accepting an Acceptable Use Policy, and moving the device to the secure BYOD VLAN. Purple's Guest WiFi platform can be deployed as the captive portal layer for the patient and guest SSID, handling GDPR-compliant data capture and terms acceptance at scale.
Phase 4: Testing and Validation
Before go-live, conduct end-to-end testing of each authentication path, VLAN assignment, and firewall rule. Specifically validate roaming behaviour by walking the clinical floor with a test device while monitoring for re-authentication events. Confirm that fast roaming protocols (802.11r and 802.11k) are functioning correctly and that application sessions survive AP transitions.
Best Practices
Eliminate Pre-Shared Keys. Transition all staff and clinical networks to 802.1X authentication to ensure individual accountability and centralised access control. This is a non-negotiable requirement for DSP Toolkit compliance.
Enforce Strict Segmentation. Never allow guest, BYOD, or IoT traffic on the same logical segment as clinical data. Use stateful firewalls to control inter-VLAN routing, with explicit deny rules as the default policy.
Prioritise Clinical Traffic. Implement QoS policies on the wireless controllers and switches to prioritise clinical applications — voice over WLAN, EHR access — over guest or administrative traffic, especially during periods of high congestion.
Enable Fast Roaming. Deploy 802.11r (Fast BSS Transition) and 802.11k (Radio Resource Measurement) to ensure clinical staff can move through the facility without experiencing application timeouts or dropped connections.
Continuous Monitoring. Utilise analytics platforms to monitor network health, identify rogue access points, and track user roaming behaviour. Understanding footfall and usage patterns — a technique proven in Retail and Hospitality environments — is equally valuable in a hospital setting for capacity planning and troubleshooting.
Regular Auditing. Conduct annual wireless risk assessments to ensure ongoing compliance with the DSP Toolkit, Cyber Essentials Plus, and ISO 27001 where applicable.
Troubleshooting & Risk Mitigation
Authentication Timeouts
In environments with high client density, RADIUS servers can become overwhelmed, leading to authentication timeouts and dropped connections. Ensure the RADIUS infrastructure is adequately scaled and highly available. Implement load balancing across multiple authentication servers and monitor RADIUS response times as a key operational metric.
Roaming Issues
Clinical staff moving rapidly between wards may experience dropped connections if the wireless infrastructure does not support fast roaming protocols. Enable 802.11r and 802.11k on the wireless controllers and ensure client devices support these standards. Conduct post-deployment roaming surveys to identify and resolve coverage gaps or 'sticky client' issues, where a device clings to a distant, weaker AP rather than roaming to a closer one.
Legacy Device Incompatibility
Older medical devices may not support modern security protocols like WPA3 or 802.1X. Isolate these devices on a dedicated IoT VLAN using MAB. Implement strict firewall rules to restrict their communication to only the necessary management servers. Consider hardware upgrades or wireless bridges for critical devices that cannot be secured natively.
Certificate Expiry
EAP-TLS deployments rely on certificates with defined expiry periods. If certificates expire without renewal, devices will fail to authenticate, causing widespread clinical disruption. Implement automated certificate renewal via SCEP (Simple Certificate Enrolment Protocol) through the MDM platform, and monitor certificate expiry dates proactively.
ROI & Business Impact
Investing in a secure, enterprise-grade wireless architecture delivers measurable returns across clinical, operational, and IT domains.
Clinical Efficiency. Reliable connectivity ensures that clinicians have immediate access to patient records at the point of care, reducing time spent searching for information or dealing with dropped connections. This directly impacts patient throughput and quality of care delivery.
Reduced IT Overhead. Moving away from shared passwords and manual onboarding to automated, certificate-based authentication significantly reduces helpdesk tickets related to password resets and connectivity issues. One NHS Trust reported a 40% reduction in wireless-related helpdesk calls following a migration to 802.1X.
Risk Mitigation. Strict segmentation and robust authentication are foundational to meeting DSP Toolkit requirements, mitigating the financial and reputational risks associated with data breaches or compliance failures. The cost of a data breach far exceeds the investment in a properly architected wireless estate.
Future-Proofing. A well-designed wireless network provides the foundation for future digital health initiatives — location-based services, real-time asset tracking, advanced telehealth applications — aligning with broader strategic goals across Healthcare and related sectors like Transport where mobile connectivity underpins operational efficiency.
For organisations looking to understand how Purple's platform maps to the guest and patient WiFi layer of this architecture, the Healthcare industry page provides a detailed overview of NHS-compatible captive portal, analytics, and GDPR-compliant data handling capabilities. The same analytics principles that drive customer engagement in Retail translate directly into operational intelligence for hospital estates teams.
Key Terms & Definitions
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, requiring each device to present credentials before being granted access.
This is the mandatory standard for replacing insecure shared passwords with individual, identity-based logins for staff and clinical devices. It is the cornerstone of a DSP Toolkit-compliant wireless architecture.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical network segments. VLANs allow network administrators to partition a single switched network to match the functional and security requirements of different user groups.
VLANs are essential for segmenting clinical traffic from guest and administrative traffic, limiting the blast radius of a potential security breach and enforcing the principle of least privilege.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service.
The RADIUS server acts as the decision engine between the wireless access points and the central identity database (Active Directory), deciding who gets access and to which VLAN they are assigned.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
An EAP method that relies on client and server certificates to establish a secure, mutually authenticated connection. Neither party trusts the other without a valid certificate.
The most secure method for authenticating hospital-owned devices. Certificates distributed via MDM ensure that only managed, trusted endpoints can access the clinical network, with no password to phish or share.
MAB (MAC Authentication Bypass)
A method of authenticating devices based on their hardware MAC address, used as a fallback for devices that do not support 802.1X.
Necessary for legacy medical IoT devices that need network access but cannot handle complex authentication protocols. Must always be paired with strict firewall ACLs to contain the device to its permitted communication paths.
DSP Toolkit (Data Security and Protection Toolkit)
An online self-assessment tool mandated by NHS England that all organisations must complete if they have access to NHS patient data and systems. It maps to the National Data Guardian's ten data security standards.
Compliance with the DSP Toolkit is mandatory for NHS organisations and their suppliers. Robust wireless security — including 802.1X, segmentation, and access lifecycle management — is a critical component of demonstrating compliance.
SSID (Service Set Identifier)
The primary name associated with an 802.11 wireless local area network, broadcast by access points to allow client devices to identify and connect to the network.
Hospitals should minimise the number of broadcast SSIDs (e.g., NHS-Clinical, NHS-Guest) to reduce management overhead and RF overhead. Each SSID should map to a specific security policy and VLAN.
QoS (Quality of Service)
Technologies that manage data traffic to reduce packet loss, latency, and jitter on a network by prioritising certain types of traffic over others.
Crucial in healthcare to ensure that life-critical clinical applications and voice communications are always prioritised over less important traffic such as guest video streaming or software updates.
802.11r (Fast BSS Transition)
An IEEE amendment that enables fast roaming between access points by pre-authenticating the client to the target AP before the physical transition occurs, dramatically reducing roaming latency.
Essential for clinical environments where staff are constantly moving. Without 802.11r, devices must perform a full RADIUS re-authentication on every AP transition, which can cause application sessions to time out.
Case Studies
An NHS Trust is deploying new mobile workstations (Workstations on Wheels) across multiple wards. The IT team needs to ensure these devices maintain connectivity as nurses move between access points, while also guaranteeing that only authorised devices can access the clinical VLAN containing the Electronic Health Record system.
The Trust should implement an 802.1X authentication framework using EAP-TLS. The IT team will use their MDM solution to push a unique client certificate and the corresponding wireless profile to each workstation. The wireless controllers will be configured to authenticate these devices against a RADIUS server, which verifies the certificate against the internal PKI. Upon successful authentication, the RADIUS server dynamically assigns the workstation to the dedicated Clinical VLAN via a RADIUS attribute (e.g., Tunnel-Private-Group-ID). To address the roaming requirement, 802.11r (Fast BSS Transition) and 802.11k (Radio Resource Measurement) must be enabled on the wireless infrastructure to allow the workstations to transition seamlessly between access points without performing a full re-authentication cycle against the RADIUS server each time.
A hospital needs to provide internet access for visiting locum doctors using their personal laptops (BYOD). These doctors need to access cloud-based medical reference tools but must be strictly prohibited from accessing the hospital's internal patient databases.
The hospital should deploy a dedicated BYOD SSID mapped to an isolated BYOD VLAN. Authentication should be handled via 802.1X using PEAP-MSCHAPv2, allowing the locums to log in using temporary Active Directory credentials provided by HR upon arrival. The core firewall must be configured with an ACL that explicitly denies any routing from the BYOD VLAN to the Clinical or Administrative VLANs, permitting only outbound traffic to the internet. Additionally, a captive portal can be utilised upon initial connection to enforce an Acceptable Use Policy before granting full internet access. When the locum's temporary AD account is disabled at the end of their engagement, their wireless access is automatically revoked.
Scenario Analysis
Q1. A new wing is being added to the hospital, and the facilities team wants to deploy wireless temperature sensors in the medication storage fridges. These sensors only support WPA2-Personal (Pre-Shared Key) and cannot use 802.1X. How should the network architect integrate these securely?
💡 Hint:Consider the principle of least privilege and how to isolate non-compliant devices from clinical systems.
Show Recommended Approach
The architect should create a dedicated, hidden SSID mapped to a specific 'Facilities IoT' VLAN. The sensors will connect using the PSK. Crucially, strict firewall ACLs must be applied to this VLAN, allowing the sensors to communicate only with their specific central management server and denying all other traffic — particularly routing to the Clinical VLAN or the internet. MAC Authentication Bypass (MAB) should also be configured to ensure only the specific MAC addresses of the purchased sensors are permitted on that VLAN, preventing rogue devices from joining using the same PSK.
Q2. During a busy morning shift, nurses report that their tablets are frequently dropping connection to the EHR system as they walk the length of the ward, requiring them to log in again. The wireless coverage survey shows strong signal strength throughout the ward. What is the likely cause and solution?
💡 Hint:Strong signal does not guarantee seamless transitions between access points. Consider the authentication overhead on each AP transition.
Show Recommended Approach
The likely cause is a lack of fast roaming protocols. As the tablet moves out of range of one AP and connects to the next, it is being forced to perform a full 802.1X re-authentication against the RADIUS server, which introduces enough latency to cause the EHR application session to time out. The solution is to enable 802.11r (Fast BSS Transition) on the wireless controllers, which allows the client to securely roam between APs without the latency of a full re-authentication cycle. 802.11k should also be enabled to help the device identify the optimal target AP before the transition occurs.
Q3. An NHS Trust is preparing for its annual DSP Toolkit assessment. The auditor notes that the administrative staff use a shared password to access the Staff WiFi network. What is the primary risk identified here, and what is the recommended remediation?
💡 Hint:Focus on individual accountability and the access lifecycle when staff leave the organisation.
Show Recommended Approach
The primary risk is a lack of individual accountability and poor access lifecycle management. If an administrative staff member leaves the Trust, the shared password remains valid, potentially allowing unauthorised access. Furthermore, it is impossible to audit which specific user performed an action on the network. The remediation is to deprecate the shared password (PSK) network and migrate administrative staff to an 802.1X authenticated network using PEAP-MSCHAPv2 with their Active Directory credentials. This ensures individual accountability and automatic access revocation when their AD account is disabled upon leaving, directly addressing the DSP Toolkit's requirements for access control and audit logging.



