Optimising Hotel WiFi for Business Travelers
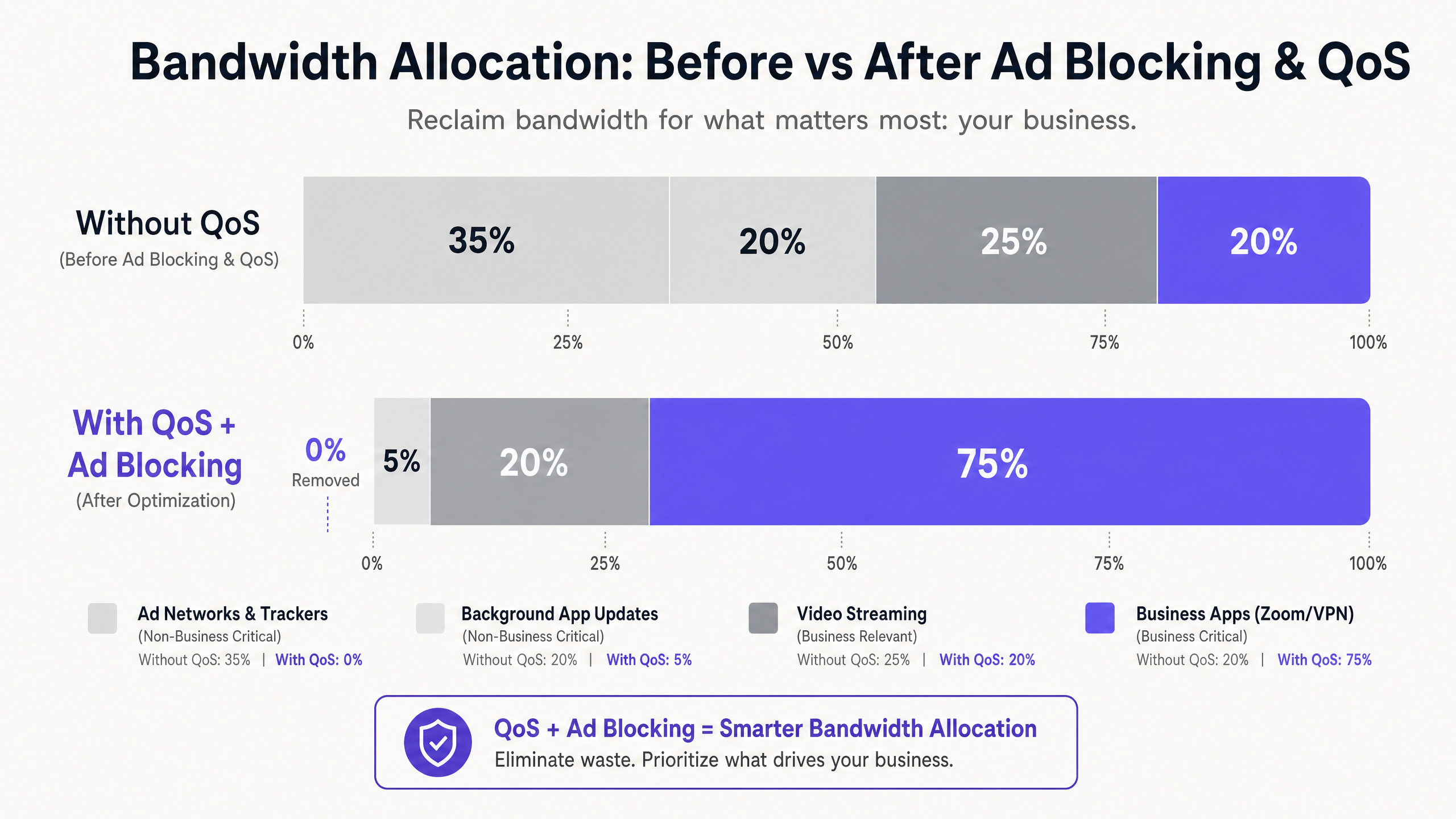
This guide provides actionable, vendor-neutral strategies for hospitality IT leaders to optimise hotel WiFi for business travelers by combining DNS-level ad blocking with end-to-end Quality of Service (QoS) policies. It covers the technical architecture, VLAN segmentation, security compliance, and real-world case studies demonstrating how eliminating background noise can reclaim up to 35% of wasted bandwidth. Venue operations directors and network architects will find concrete implementation steps, decision frameworks, and measurable ROI benchmarks to justify and execute the deployment this quarter.
Listen to this guide
View podcast transcript

Executive Summary
For IT managers and venue operations directors in the Hospitality sector, delivering reliable WiFi is no longer a differentiator — it is a baseline operational requirement. Business travelers demand high-performance connectivity for enterprise VPNs, video conferencing, and cloud-hosted applications. Yet the majority of hotel networks are silently haemorrhaging capacity to invisible background traffic: ad trackers, telemetry beacons, and automatic application updates that can consume up to 35% of total available bandwidth before a single business application has even initialised.
This guide details a proven, vendor-neutral architecture to reclaim that wasted capacity. By deploying DNS-level ad blocking at the network gateway and enforcing end-to-end Quality of Service (QoS) policies mapped through Deep Packet Inspection (DPI), network architects can ensure that latency-sensitive applications — Zoom, Microsoft Teams, IPsec VPNs, and SSL tunnels — receive guaranteed priority throughput. The approach is implementable on existing infrastructure in most cases, delivering measurable ROI through deferred ISP link upgrades and improved corporate guest satisfaction scores.
Technical Deep-Dive
The core challenge in modern hotel WiFi environments is the proliferation of unsolicited background traffic. When any modern device — a business laptop, a smartphone, a tablet — connects to a network, it immediately initiates dozens of background connections. These include advertising SDK polling from installed applications, operating system telemetry, cloud sync services, and automatic update checks. On a flat, unmanaged network with 200 concurrent guests, this background chatter is not merely inconvenient; it is a structural bandwidth problem.
Research into enterprise guest network traffic profiles consistently shows that ad networks and third-party trackers account for between 25% and 40% of DNS query volume on unmanaged hotel networks. Each resolved query may initiate a data transfer, and while individual payloads are small, the aggregate effect across hundreds of simultaneous connections is significant. This is the bandwidth that should be serving a CFO's Zoom board call or a consultant's VPN session to their corporate data centre.
Layer 1: DNS-Based Ad and Tracker Blocking
The most efficient intervention point is DNS resolution. By routing all guest DNS queries through a filtering resolver — whether an on-premises appliance or a cloud-based DNS security service — the network can silently drop requests to known ad servers, tracker domains, and telemetry endpoints before any payload data traverses the WAN link. The efficiency gain here is structural: a blocked DNS query consumes negligible resources compared to the full HTTP/S connection it would otherwise have initiated.
For production hotel deployments, managed DNS filtering services offer regularly updated blocklists with enterprise SLAs, which is preferable to self-managed open-source solutions in environments where uptime is critical. The key configuration requirement is ensuring that the walled garden — the set of domains accessible before captive portal authentication — is explicitly whitelisted and not subject to the general filtering policy. Failure to do this is the most common cause of post-deployment guest complaints.
Layer 2: Deep Packet Inspection and QoS Tagging
Once background noise is reduced at the DNS layer, the remaining traffic must be actively managed by priority. Deep Packet Inspection (DPI) at the edge firewall or Unified Threat Management (UTM) appliance identifies specific application protocols. Modern DPI engines can reliably classify Zoom, Microsoft Teams, Cisco Webex, RTP/SIP voice traffic, IPsec, and SSL VPN sessions by their packet signatures and port patterns, even when standard ports are not used.
Identified business-critical traffic is tagged with Differentiated Services Code Point (DSCP) values in the IP header. The DSCP field provides 64 possible per-hop behaviours, but in practice, most hotel deployments use a simplified three-tier model: Expedited Forwarding (EF, DSCP 46) for voice and video conferencing; Assured Forwarding Class 4 (AF41, DSCP 34) for VPN and business application data; and Best Effort (BE, DSCP 0) for general web browsing and streaming.
Layer 3: Wireless QoS via WMM
The wired QoS configuration is only effective if the wireless access points correctly map the DSCP tags to the appropriate Wi-Fi Multimedia (WMM) access categories. WMM defines four access categories: Voice (AC_VO), Video (AC_VI), Best Effort (AC_BE), and Background (AC_BK). The mapping from DSCP to WMM must be explicitly configured on the AP, as default behaviour varies by vendor. Verify this configuration in your AP management console; it is a common gap that renders an otherwise well-designed QoS policy ineffective at the last hop.
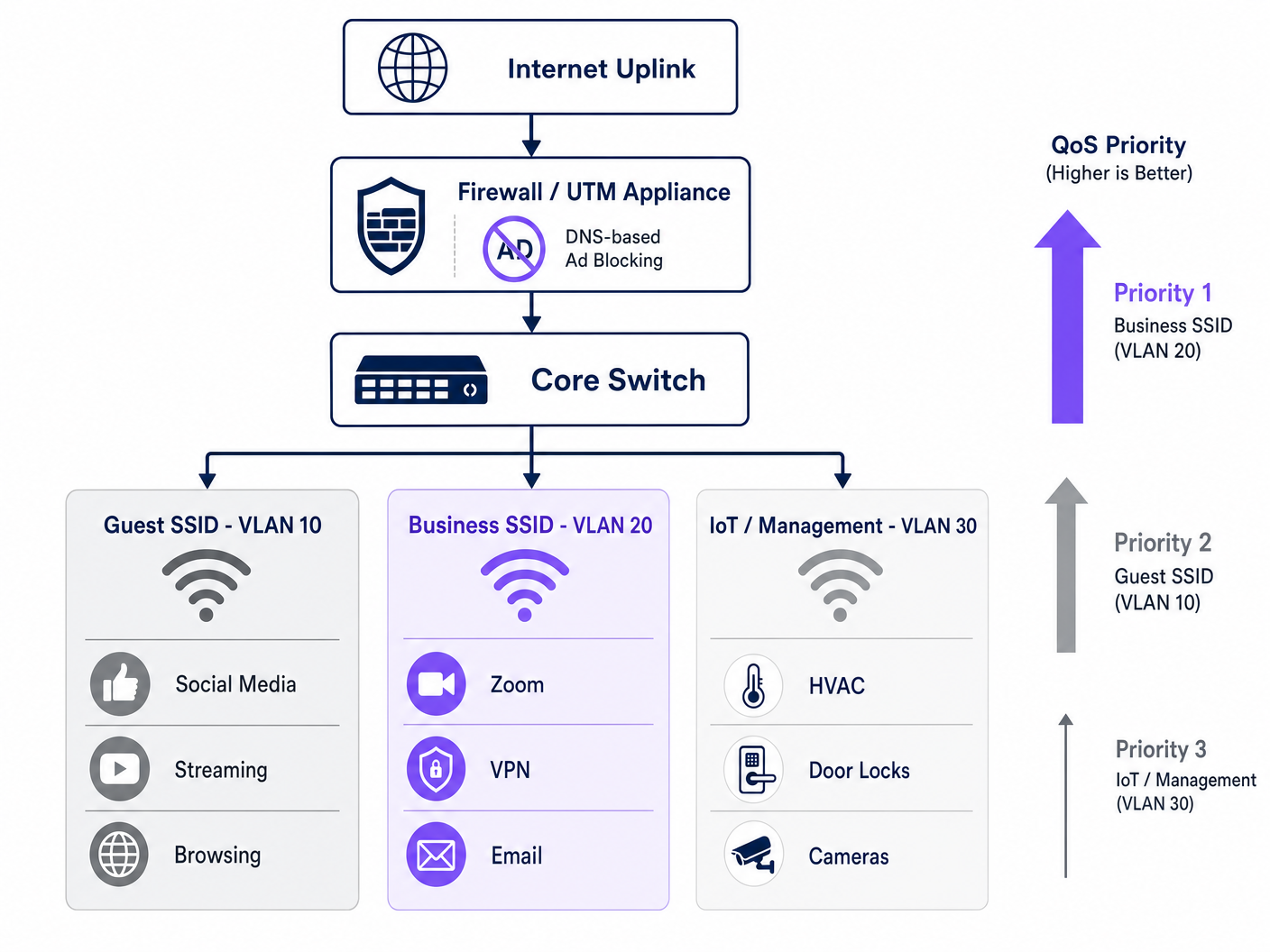
VLAN Segmentation and Security Architecture
A properly optimised hotel network operates across at minimum three logical segments. The Guest SSID (VLAN 10) serves leisure travelers and conference attendees with standard internet access, subject to DNS filtering and rate limiting. The Business SSID (VLAN 20) carries the highest QoS priority and is authenticated via WPA3-Enterprise with IEEE 802.1X, integrating with a RADIUS server for per-user credentials. The IoT and Management VLAN (VLAN 30) isolates smart room devices, HVAC sensors, electronic door locks, and IP cameras from all guest traffic.
This segmentation is not merely a performance optimisation — it is a compliance requirement. Under PCI DSS, any network segment that touches payment card data must be isolated from general-purpose networks with documented firewall rules and access controls. Under GDPR, the personal data collected via Guest WiFi authentication must be handled with appropriate technical safeguards, and network segmentation is a foundational control that demonstrates due diligence. Maintaining a comprehensive audit trail for IT Security in 2026 across all VLANs is essential for demonstrating compliance during assessments.
Implementation Guide
Deploying this architecture requires a structured approach to avoid disrupting live guest services. The following sequence is recommended for a phased rollout.
Phase 1 — Traffic Profiling (Week 1). Before making any changes, deploy a traffic analysis tool on a SPAN port of your core switch to capture a 72-hour baseline. Identify the top 20 bandwidth-consuming domains and application categories. This data justifies the investment and provides a baseline for measuring post-deployment improvement. Many operators leverage WiFi Analytics capabilities to understand device types, dwell patterns, and application usage across their estate.
Phase 2 — Pilot DNS Filtering (Week 2). Implement DNS filtering on a single isolated VLAN — ideally a staff or back-office segment — using a conservative blocklist. Monitor for false positives over 48 hours before expanding to guest segments. Document all domains added to the walled garden whitelist.
Phase 3 — QoS Policy Deployment (Week 3). Configure DPI rules and DSCP tagging on the edge firewall. Verify that DSCP tags are preserved through each switch hop by capturing packets at the distribution layer. Enable WMM on all access points and confirm the DSCP-to-WMM mapping is correctly applied. For guidance on frequency planning and channel management during this phase, refer to Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
Phase 4 — VLAN Restructuring (Week 4). Migrate IoT devices to a dedicated management VLAN. Introduce the Business SSID with WPA3-Enterprise authentication. Communicate the new SSID to corporate accounts and conference organisers.
Phase 5 — Monitoring and Optimisation (Ongoing). Establish KPIs: average Zoom call quality score, VPN connection success rate, peak-hour throughput utilisation, and guest WiFi satisfaction rating. Review and update DNS blocklists monthly.
Best Practices
The following vendor-neutral recommendations reflect current industry standards and are applicable across major hardware platforms including Cisco Meraki, Ubiquiti UniFi, Aruba Networks, and Ruckus.
| Practice | Standard / Reference | Priority |
|---|---|---|
| WPA3-Enterprise on Business SSID | IEEE 802.11i / WPA3 | Critical |
| 802.1X RADIUS authentication | IEEE 802.1X | Critical |
| End-to-end DSCP preservation | RFC 2474 | High |
| WMM enabled on all APs | Wi-Fi Alliance WMM | High |
| Airtime Fairness enabled | Vendor-specific | Medium |
| DNS filtering with managed blocklists | NIST SP 800-81 | High |
| VLAN segmentation (Guest/Business/IoT) | IEEE 802.1Q | Critical |
| PCI DSS network isolation | PCI DSS v4.0 Req. 1 | Critical (if applicable) |
For venues operating Retail environments alongside hospitality spaces — such as hotel lobby shops or integrated conference retail — the same VLAN and QoS principles apply, with the addition of POS traffic receiving its own high-priority queue. The principles discussed in Office Wi Fi: Optimize Your Modern Office Wi-Fi Network are directly transferable to hotel business centre and conference room deployments.
Troubleshooting & Risk Mitigation
The most common failure modes in hotel WiFi optimisation deployments fall into three categories.
Captive Portal Breakage. Symptom: guests cannot reach the login page after DNS filtering is enabled. Root cause: the filtering policy is blocking domains required for the captive portal redirect or the walled garden. Mitigation: audit all domains required for the authentication flow and add them to the pre-authentication whitelist before enabling the general filter. If you are diagnosing broader congestion issues, the guide Why is Our Guest WiFi So Slow? Diagnosing Network Congestion provides a structured diagnostic framework. For Spanish-language operators, the equivalent resource is available at ¿Por qué nuestro WiFi para invitados es tan lento? Diagnóstico de la congestión de la red .
DSCP Tag Stripping. Symptom: QoS is configured on the firewall and APs, but business application performance does not improve under load. Root cause: an intermediate switch is stripping or remarking DSCP tags. Mitigation: capture packets at multiple points in the network path using Wireshark or equivalent. Verify that each switch's QoS trust policy is set to trust DSCP from upstream devices.
IoT Device Instability After Airtime Fairness. Symptom: smart room devices (thermostats, door locks) drop offline intermittently after enabling airtime fairness. Root cause: legacy 802.11b/g IoT devices transmit slowly and receive insufficient airtime under a fairness policy. Mitigation: move IoT devices to a dedicated 2.4GHz SSID on VLAN 30 with airtime fairness disabled. Apply airtime fairness only to the 5GHz guest and business SSIDs.
ROI & Business Impact
The financial case for this investment is straightforward. By reclaiming 20–35% of wasted bandwidth through DNS filtering alone, most hotel properties can defer an ISP link upgrade by 12 to 18 months. At typical enterprise broadband pricing for a 1Gbps dedicated fibre circuit, this represents a capital deferral of £15,000 to £40,000 depending on market and contract terms.
Beyond infrastructure savings, the impact on corporate guest satisfaction is measurable. Hotels that can credibly market reliable, business-grade WiFi command a premium in the corporate travel segment. A consistent improvement in WiFi satisfaction scores — typically measured via post-stay surveys — directly correlates with repeat booking rates from corporate accounts, which represent the highest-margin segment for most full-service hotels.
For Healthcare and Transport venues operating guest or patient WiFi, the compliance benefits are equally significant. Demonstrating a documented, auditable approach to network security and data handling reduces regulatory risk and simplifies compliance assessments.
Key Definitions
DNS Filtering
The process of blocking access to specified domains at the DNS resolution stage, preventing devices from establishing connections to those destinations.
Deployed at the gateway to prevent guest devices from reaching ad networks and tracker domains, reclaiming bandwidth before any payload data is transmitted.
Quality of Service (QoS)
A set of network mechanisms that prioritise certain types of traffic over others to guarantee performance for latency-sensitive applications.
Essential for ensuring that Zoom, VoIP, and VPN traffic receive guaranteed throughput and low latency on a congested hotel network shared by hundreds of users.
Deep Packet Inspection (DPI)
An advanced form of packet filtering that examines the data content of a packet beyond its header to identify the specific application or protocol.
Used by edge firewalls to accurately classify application traffic (e.g., distinguishing a Zoom call from generic HTTPS traffic) so it can be tagged for QoS prioritisation.
DSCP (Differentiated Services Code Point)
A 6-bit field in the IP packet header used to classify and mark packets for per-hop QoS treatment across network devices.
The industry-standard mechanism for tagging packets so that switches, routers, and access points know which traffic is business-critical and should be processed first.
WMM (Wi-Fi Multimedia)
A Wi-Fi Alliance certification that implements QoS on wireless networks by defining four access categories: Voice, Video, Best Effort, and Background.
The wireless equivalent of wired QoS. Must be enabled on all access points and correctly mapped to DSCP values to ensure that wired QoS policies are honoured at the last hop.
Airtime Fairness
A wireless scheduling feature that allocates equal transmission time to all connected clients, rather than equal packet counts, preventing slow legacy devices from monopolising channel capacity.
Critical in hotel environments where a mix of modern business laptops and older devices share the same AP. Prevents a single slow device from degrading the experience for all others.
VLAN (Virtual Local Area Network)
A logical network segment created on a physical switch infrastructure using IEEE 802.1Q tagging to isolate traffic between groups of devices.
Used to separate guest, business, and IoT traffic on the same physical infrastructure. A mandatory control for PCI DSS compliance and a best practice for network security and performance management.
Captive Portal
A web-based authentication gateway that intercepts a new device's HTTP traffic and redirects it to a login or registration page before granting full network access.
The primary touchpoint for guest WiFi authentication and first-party data collection. Must be carefully managed to ensure DNS filtering policies do not block the authentication flow.
Walled Garden
A set of domains and IP addresses that a device can access before completing captive portal authentication, typically including the portal itself and any required third-party authentication services.
Must be explicitly configured when deploying DNS filtering to ensure the authentication flow is not disrupted by the general blocking policy.
IEEE 802.1X
An IEEE standard for port-based Network Access Control that provides an authentication mechanism for devices wishing to connect to a network.
The authentication framework underpinning WPA3-Enterprise deployments. Integrates with a RADIUS server to provide per-user credentials and is the recommended standard for business-grade hotel SSIDs.
Worked Examples
A 400-room city-centre hotel is hosting a major technology conference with 600 registered delegates. The venue has a 1Gbps symmetric fibre uplink. During the first morning of the conference, the network operations team receives a flood of complaints: Zoom calls are dropping, VPN connections are timing out, and the conference app is failing to load. A traffic capture shows the 1Gbps link is at 94% utilisation. How should the IT team respond, both immediately and structurally?
Immediate response (within 30 minutes): Deploy an emergency DNS sinkhole for the top 50 ad network and telemetry domains identified in the traffic capture. This alone should shed 25–35% of current load. Simultaneously, configure emergency QoS rules on the edge firewall to hard-prioritise traffic on UDP ports 8801-8802 (Zoom) and TCP 443 with Zoom's IP ranges, and to rate-limit traffic to known streaming CDN IP ranges to 10Mbps aggregate.
Structural response (post-event): Segment the network into dedicated conference delegate and speaker VLANs. Deploy a managed DNS filtering service with a maintained blocklist. Implement DPI-based QoS with DSCP tagging for all future events. Negotiate a burst capacity agreement with the ISP for high-density event periods. Consider a dedicated 10Gbps event uplink for conferences exceeding 300 delegates.
A 120-room boutique hotel group with properties across three cities wants to standardise their WiFi infrastructure. Each property has a mix of leisure and business guests. The IT director wants to ensure that business guests get a premium experience without investing in new hardware at each site. The existing infrastructure is a mix of Ubiquiti UniFi APs and Cisco Meraki firewalls. What architecture should be recommended?
Recommend a centralised cloud-managed architecture leveraging the existing Meraki firewalls for DNS filtering (via Meraki's built-in content filtering and Umbrella integration) and DPI-based QoS. Configure two SSIDs per property: a standard Guest SSID (WPA3-Personal with captive portal) and a Business SSID (WPA3-Enterprise with 802.1X). Map the Business SSID to a dedicated VLAN with the highest QoS priority tier. On the UniFi APs, enable WMM and configure the DSCP-to-WMM mapping to match the Meraki firewall's tagging policy. Deploy a centralised RADIUS server (or use a cloud RADIUS service) for 802.1X authentication across all three properties. Provide corporate account guests with Business SSID credentials at check-in.
Practice Questions
Q1. You have just enabled DNS filtering on your hotel's guest VLAN. Within 10 minutes, the front desk receives calls from guests saying they cannot connect to WiFi — they are not seeing the login page and are getting a 'No Internet Connection' error. What is the most likely cause and how do you resolve it?
Hint: Consider the sequence of events when a new device joins an open network and attempts to reach the captive portal.
View model answer
The DNS filtering policy is blocking one or more domains required for the captive portal redirect or the walled garden. When a device joins the network, it sends an HTTP probe request to detect the captive portal. If the DNS resolver cannot resolve the redirect domain (because it is on the blocklist or the filter is too aggressive), the device never sees the login page. Resolution: immediately identify the captive portal's redirect domain, authentication server domain, and any social login provider domains (e.g., accounts.google.com for Google login), and add them to the walled garden whitelist. The walled garden must bypass the DNS filter entirely for unauthenticated devices.
Q2. A network architect has configured DPI on the edge firewall to tag Zoom traffic with DSCP EF (46) and has verified the configuration is correct. However, during peak conference hours, business guests still report jitter and dropped calls. A packet capture at the AP shows Zoom traffic arriving with DSCP 0 (Best Effort). What is the most likely cause?
Hint: Remember that QoS is an end-to-end requirement and that each device in the path must be configured to trust and forward priority markings.
View model answer
A switch between the firewall and the access point is stripping or remarking the DSCP tags to 0 (Best Effort). This is a common issue when switches are configured with a default 'untrusted' QoS policy that resets all incoming DSCP values. Resolution: identify the switch(es) in the path between the firewall and the APs, and configure their QoS trust policy to 'trust DSCP' on the uplink ports. Additionally, verify that the access points are configured to map DSCP EF to WMM AC_VO (Voice) and not defaulting to AC_BE.
Q3. You are advising a 250-room hotel that wants to implement Airtime Fairness to improve WiFi performance for business guests. The hotel also has 80 smart room devices (thermostats, motorised blinds) that use 802.11b/g and are currently on the same SSID as guests. What is the risk of enabling Airtime Fairness in this configuration, and what is the recommended approach?
Hint: Consider how Airtime Fairness allocates resources and how the transmission rate of legacy 802.11b devices compares to modern 802.11ac/Wi-Fi 6 devices.
View model answer
Airtime Fairness allocates equal transmission time to all clients, regardless of their data rate. A legacy 802.11b device transmitting at 1–11 Mbps receives the same time slice as a modern Wi-Fi 6 device transmitting at 600+ Mbps. In practice, the legacy device transmits far less data in its time slice, which is acceptable for the device itself, but the problem is that the access point must wait for the slow device to finish its transmission before serving the next client. This can cause the smart room devices to miss their polling windows, leading to intermittent disconnections. The recommended approach is to migrate all IoT devices to a dedicated 2.4GHz SSID on VLAN 30 (IoT/Management) with Airtime Fairness disabled, and enable Airtime Fairness only on the 5GHz guest and business SSIDs where all clients are modern devices.
Q4. A hotel group's CTO asks you to justify the cost of deploying a managed DNS filtering service (£8,000/year) versus continuing with the current unmanaged network. The hotel has a 1Gbps fibre uplink costing £24,000/year. How would you structure the ROI argument?
Hint: Consider both direct infrastructure savings and indirect revenue impact.
View model answer
Structure the ROI argument in two parts. Direct savings: if DNS filtering reclaims 30% of wasted bandwidth, the effective throughput of the existing 1Gbps link increases to the equivalent of approximately 1.3Gbps. This defers the need for a 10Gbps upgrade (typically £45,000–£80,000 capital cost plus increased annual line rental) by at least 18–24 months. The £8,000/year filtering service cost is recovered within the first year through deferred capital expenditure alone. Indirect revenue impact: improved WiFi satisfaction scores in the corporate segment — typically a 15–25% improvement based on comparable deployments — directly influence repeat booking rates from corporate accounts. For a 250-room hotel with 40% corporate occupancy at an average rate of £180/night, even a 2% improvement in corporate repeat bookings represents approximately £65,000 in additional annual revenue. The combined ROI case is compelling and quantifiable within a single financial year.