Passwordless WiFi: What It Is and How to Implement It
This technical reference guide provides network architects and IT managers with a comprehensive blueprint for transitioning from vulnerable shared passwords to secure, certificate-based WiFi authentication. It covers 802.1X architecture, EAP-TLS deployment strategies, PKI management, and the measurable business impact of reducing helpdesk overhead while enhancing enterprise security posture and compliance readiness.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: The Architecture of Passwordless WiFi
- The 802.1X Tripartite Model
- EAP-TLS: The Gold Standard for Passwordless Authentication
- The Role of Public Key Infrastructure (PKI)
- Implementation Guide: Step-by-Step Deployment
- Phase 1: Infrastructure Assessment and Readiness
- Phase 2: PKI Setup and Certificate Management
- Phase 3: Device Onboarding and Provisioning
- Phase 4: Network Configuration and Testing
- Best Practices for Enterprise Environments
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
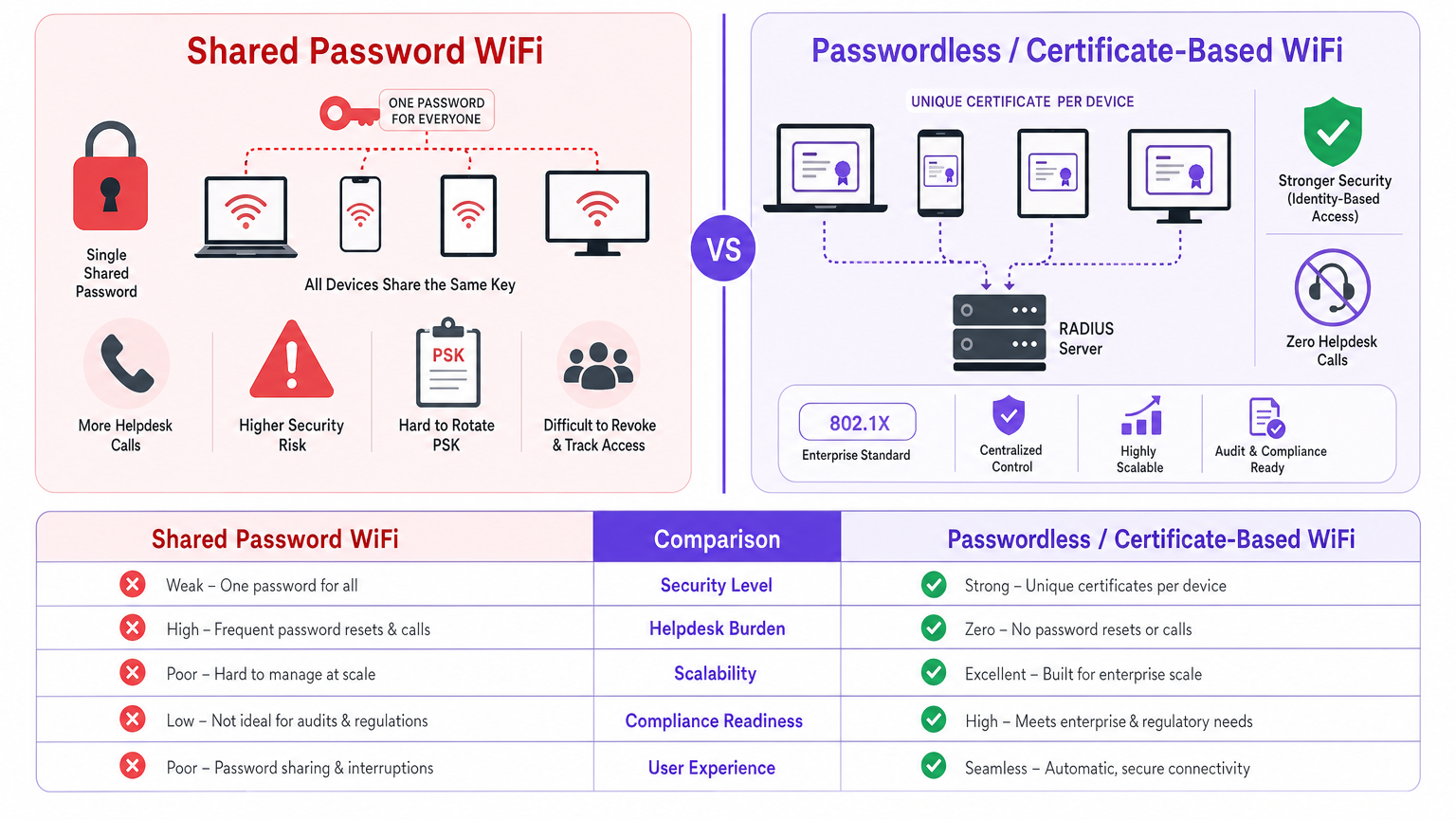
The transition from shared Pre-Shared Keys (PSKs) to certificate-based, passwordless WiFi authentication represents a critical architectural shift for enterprise networks. For IT managers and network architects operating at scale — whether across a 200-room hotel, a national retail chain, or a sprawling public-sector campus — the legacy approach of managing a single password for all guest or BYOD access is no longer viable. It introduces unacceptable security vulnerabilities, complicates compliance with frameworks like PCI DSS and GDPR, and generates a disproportionate volume of helpdesk tickets related to connectivity issues and password rotation.
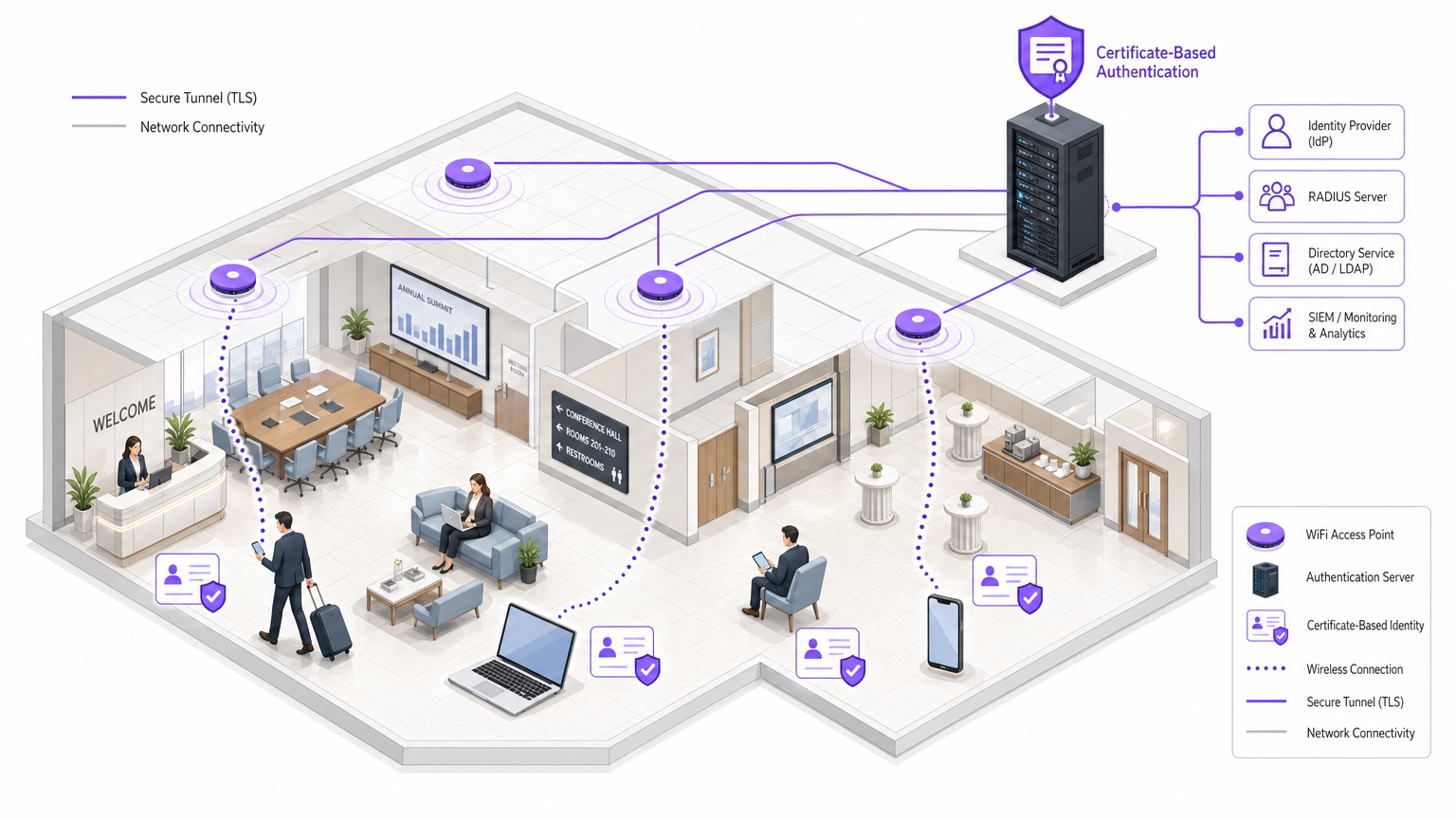
Passwordless WiFi, fundamentally built upon the IEEE 802.1X standard and EAP-TLS (Extensible Authentication Protocol - Transport Layer Security), eliminates these friction points. By issuing unique, cryptographically secure certificates to individual devices, network administrators can enforce granular, identity-aware access control. This guide provides a comprehensive technical reference for implementing passwordless WiFi, detailing the underlying architecture, deployment methodologies, and the measurable return on investment (ROI) achievable through reduced operational overhead and mitigated risk. Furthermore, we explore how integrating a platform like Purple's Guest WiFi can streamline this transition, acting as a robust Identity Provider (IdP) to facilitate seamless, secure onboarding.
Technical Deep-Dive: The Architecture of Passwordless WiFi
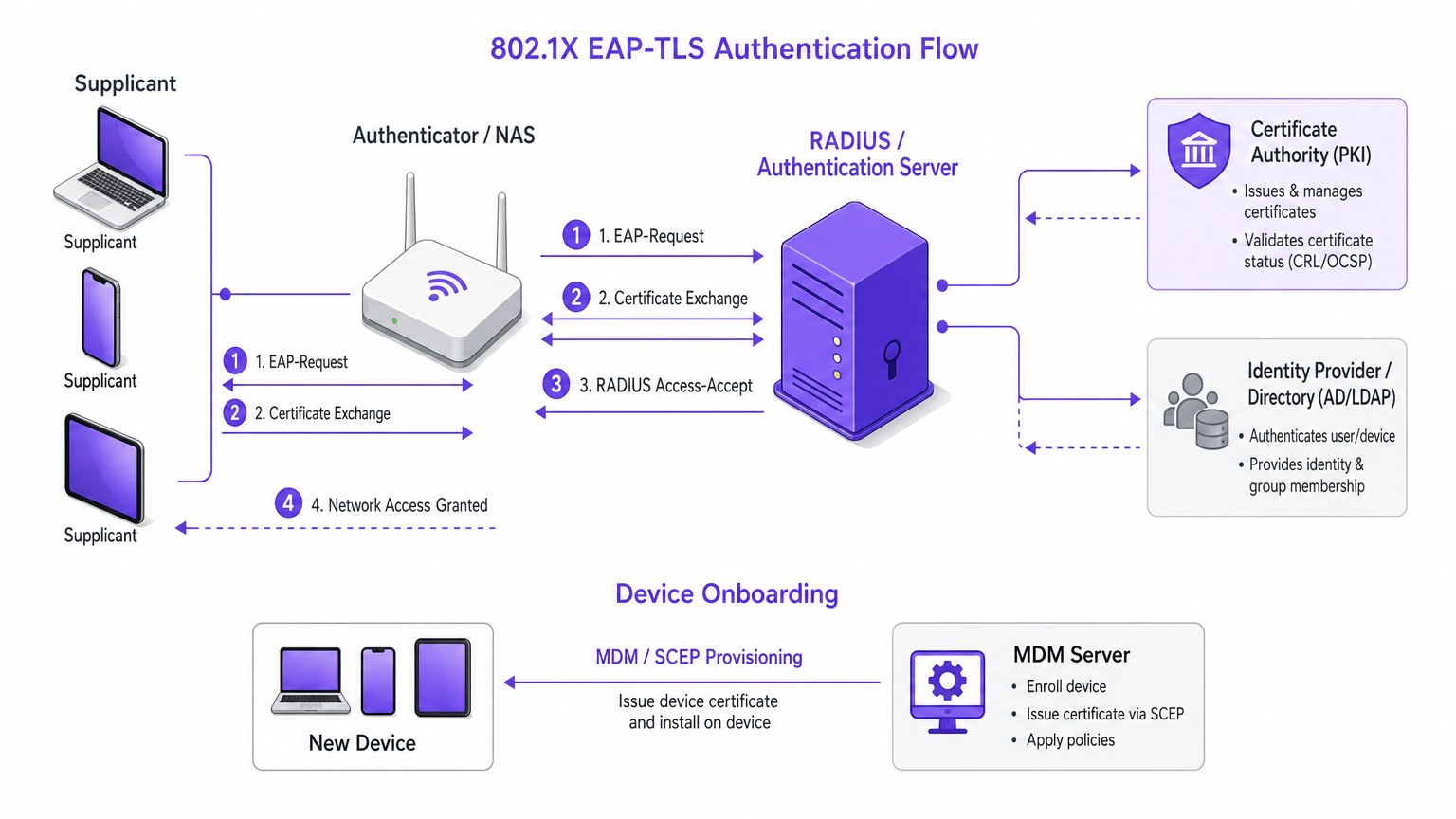
To understand the implementation of passwordless WiFi, one must first deconstruct the core components of the 802.1X authentication framework. Unlike WPA2-Personal, which relies on a shared secret, 802.1X operates on a tripartite model: the Supplicant, the Authenticator, and the Authentication Server.
The 802.1X Tripartite Model
The Supplicant is the client device — a smartphone, laptop, or IoT sensor — attempting to connect to the network. In a passwordless environment, the supplicant must possess a valid digital certificate rather than a password. The Authenticator is typically the Wireless Access Point (WAP) or wireless LAN controller. It acts as a gatekeeper, not evaluating credentials itself, but encapsulating the supplicant's request and forwarding it to the authentication server via the RADIUS protocol. The Authentication Server is the centralized authority — often a RADIUS server integrated with an Identity Provider (IdP) such as Active Directory, LDAP, or a cloud-native directory service. The server validates the certificate presented by the supplicant against its database and a Certificate Revocation List (CRL).
EAP-TLS: The Gold Standard for Passwordless Authentication
While 802.1X supports various Extensible Authentication Protocol (EAP) methods, EAP-TLS is universally recognised as the most secure standard for enterprise deployments. EAP-TLS mandates mutual authentication: the RADIUS server presents its certificate to the supplicant, proving the network is legitimate and preventing evil twin attacks; and the supplicant presents its unique client certificate to the RADIUS server, proving its identity without transmitting any password hashes over the air. This mutual cryptographic handshake establishes a secure TLS tunnel through which the final authorisation and key derivation occur, ensuring maximum data integrity and confidentiality.
The Role of Public Key Infrastructure (PKI)
Implementing EAP-TLS requires a robust Public Key Infrastructure (PKI). The PKI is responsible for generating, issuing, and managing the lifecycle of digital certificates. Historically, managing a local Certificate Authority (CA) was a significant barrier to entry. However, modern cloud-managed PKI solutions and Mobile Device Management (MDM) integrations have automated the provisioning process, allowing certificates to be pushed silently to managed devices via protocols like SCEP (Simple Certificate Enrollment Protocol) or EST (Enrollment over Secure Transport).
For unmanaged devices — BYOD or guest access — onboarding platforms provide a self-service portal where users authenticate once (e.g., via OAuth or SAML against a corporate directory, or via a captive portal for guests) and are subsequently provisioned with a temporary certificate or a secure profile such as Passpoint/Hotspot 2.0.
Implementation Guide: Step-by-Step Deployment
Deploying a passwordless WiFi architecture requires careful planning and phased execution. The following steps outline a vendor-neutral approach suitable for large-scale enterprise environments, such as those found in Healthcare or Transport sectors.
Phase 1: Infrastructure Assessment and Readiness
Before altering authentication methods, ensure the underlying network infrastructure supports the required protocols. Verify that all Wireless LAN Controllers and Access Points support 802.1X and WPA3-Enterprise — legacy hardware may require firmware updates or replacement. Select a robust RADIUS solution capable of handling the expected authentication load; cloud-RADIUS solutions offer high availability and scalability compared to on-premises deployments. Determine the primary source of truth for user identities (e.g., Azure AD, Okta, Google Workspace) and confirm the RADIUS server can communicate with this directory.
Phase 2: PKI Setup and Certificate Management
The foundation of passwordless access is certificate lifecycle management. Deploy a trusted Certificate Authority: for internal corporate devices, an internal CA is sufficient; for guest access or BYOD, consider a public CA or a specialised onboarding service. Define clear certificate validity policies — corporate devices might receive certificates valid for one year, while guest certificates might expire after 24 hours. Configure revocation mechanisms, ensuring the RADIUS server checks Certificate Revocation Lists (CRLs) or uses OCSP to immediately block access for lost or compromised devices.
Phase 3: Device Onboarding and Provisioning
The onboarding experience dictates the success of the deployment. For managed corporate devices, leverage an MDM solution (e.g., Microsoft Intune, Jamf) to silently push the CA certificate and the unique client certificate using SCEP or EST. This requires zero user interaction. For unmanaged BYOD devices, implement a secure onboarding portal where users connect to an open provisioning SSID, authenticate via corporate credentials (SAML/OAuth), and download a configuration profile that installs the necessary certificates and configures the secure SSID. For guest access in environments like Hospitality or Retail , integrate with a platform like Purple's WiFi Analytics . Purple can act as the IdP, allowing guests to authenticate via social login or a customised portal, after which they are seamlessly transitioned to a secure, encrypted connection — often leveraging OpenRoaming or Passpoint standards — without ever typing a network password.
Phase 4: Network Configuration and Testing
Create the new SSID configured for WPA3-Enterprise (or WPA2-Enterprise if legacy support is required) and 802.1X authentication, pointing the authenticator to the RADIUS server. Configure the RADIUS server to return specific attributes upon successful authentication — for example, assigning the user to a specific VLAN based on their group membership, placing staff on a corporate VLAN and guests on an isolated internet-only VLAN. Roll out the secure SSID to a small pilot group first (the IT department is usually ideal) and monitor authentication logs meticulously to identify any certificate validation errors or RADIUS timeouts before a full deployment.
Best Practices for Enterprise Environments
Enforce Mutual Authentication: Never deploy EAP-TLS without requiring the supplicant to validate the server's certificate. Failure to do so exposes the network to Man-in-the-Middle (MitM) attacks.
Implement Strict Certificate Validation: Configure supplicants to explicitly trust only the specific CA that issued the RADIUS server's certificate, and verify the server's Common Name (CN) or Subject Alternative Name (SAN).
Leverage Passpoint (Hotspot 2.0): For public-facing venues, Passpoint is the future of passwordless connectivity. It allows devices to automatically discover and securely connect to authorised networks using credentials provided by their mobile operator or a third-party IdP, functioning much like cellular roaming. Purple's Connect licence facilitates this by acting as an identity provider for services like OpenRoaming.
Segment Traffic: Always use dynamic VLAN assignment via RADIUS to logically separate different classes of users (POS terminals, corporate staff, IoT devices, guests). This limits the blast radius of any potential compromise. For a deeper dive into segmenting specialised networks, see our guide on WiFi in Hospitals: A Guide to Secure Clinical Networks .
Troubleshooting & Risk Mitigation
Even with meticulous planning, issues can arise. Understanding common failure modes is critical for rapid resolution.
Clock Skew is the single most common cause of EAP-TLS authentication failures. Certificate validation relies on accurate timekeeping; if the time on the supplicant, RADIUS server, or CA is out of sync by more than a few minutes, validation will fail silently. Ensure all infrastructure relies on a reliable NTP source.
Certificate Chain Issues occur when the supplicant does not have the complete chain of trust — including intermediate CAs — installed. It will reject the server's certificate. Always ensure the RADIUS server is configured to send the full certificate chain during the EAP exchange.
RADIUS Timeouts can occur if the latency between the authenticator (WAP) and the RADIUS server is too high, causing the EAP handshake to time out. This is common in distributed deployments using a centralised cloud RADIUS. Adjust timeout values on the WLC or consider deploying regional RADIUS proxies.
Stale Certificates: Devices attempting to authenticate with expired certificates will be silently rejected. Implement robust monitoring to alert administrators of impending certificate expirations before they impact users.
For risk mitigation, maintain the legacy PSK network temporarily during the transition, but restrict its bandwidth or access privileges to incentivise migration. Forward all RADIUS authentication logs to a SIEM platform and conduct periodic reviews of the PKI infrastructure and RADIUS policies to ensure alignment with current security standards.
ROI & Business Impact
The transition to passwordless WiFi is a strategic investment with a measurable return across several dimensions.
| Metric | Shared PSK | Certificate-Based (802.1X) |
|---|---|---|
| Helpdesk tickets (connectivity) | High — frequent password resets | Near-zero — automated provisioning |
| Security risk | High — single credential for all | Low — unique, revocable per device |
| Compliance readiness | Poor — no individual accountability | Strong — full audit trail per device |
| Onboarding time (corporate) | Minutes (manual) | Seconds (MDM automated) |
| Credential revocation | Disruptive — requires full PSK rotation | Instant — revoke individual certificate |
Reduction in Helpdesk Overhead: Managing shared passwords is a significant drain on IT resources. Passwordless authentication, particularly when automated via MDM or a self-service onboarding portal, virtually eliminates password-related helpdesk tickets.
Enhanced Security Posture: By eliminating shared secrets, the risk of credential theft and unauthorised network access is drastically reduced. Each device has a unique, cryptographically secure identity that can be instantly revoked if the device is lost or compromised.
Simplified Compliance: Frameworks like PCI DSS require strict access controls and individual accountability. Certificate-based authentication provides a clear audit trail of exactly which device accessed the network and when, simplifying compliance reporting.
Improved User Experience and Data Capture: Once provisioned, the connection process is entirely transparent to the user. In environments like Retail , this frictionless connectivity encourages users to join the network, allowing venues to capture valuable first-party data and drive personalised engagement through platforms like Purple.
For organisations managing complex RF environments, understanding the interplay between authentication and physical infrastructure is crucial. Further reading on infrastructure considerations can be found in Your Guide to a Wireless Access Point Ruckus . Additionally, understanding how broader networking concepts apply can be useful; see our guide on Personal Area Networks (PANs): Technologies, Applications, Security, and Future Trends .
Key Terms & Definitions
802.1X
An IEEE standard for port-based network access control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN. It is the foundational protocol for enterprise-grade, passwordless WiFi.
The core standard that underpins all enterprise WiFi authentication, replacing the shared PSK model.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A highly secure EAP method that requires mutual authentication using digital certificates on both the client and the server. No passwords are transmitted over the air.
Considered the gold standard for wireless security. The method of choice for any organisation serious about eliminating credential-based risk.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service.
The engine that processes authentication requests from Access Points and validates them against a directory. A RADIUS server is a mandatory component of any 802.1X deployment.
Supplicant
The client device (e.g., laptop, smartphone, IoT sensor) attempting to access the network. In 802.1X, the supplicant must present a valid certificate or credential to gain access.
The starting point of every authentication request. Understanding the supplicant's capabilities (e.g., whether it supports EAP-TLS) is critical during the planning phase.
PKI (Public Key Infrastructure)
A set of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates and manage public-key encryption.
The underlying system required to issue and manage the certificates used in EAP-TLS. Without a functioning PKI, certificate-based authentication is not possible.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance standard that streamlines network access, allowing devices to automatically discover and connect to authorised WiFi networks without manual authentication steps.
Enables a seamless, cellular-like roaming experience for users across different venues. Particularly relevant for hospitality, retail, and public-sector deployments.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the Authenticator to place a successfully authenticated user onto a specific Virtual LAN based on their identity or group membership.
Crucial for network segmentation, ensuring that IoT devices, guests, and corporate staff are logically isolated from one another — a key requirement for PCI DSS compliance.
SCEP (Simple Certificate Enrollment Protocol)
A protocol that enables network devices to automatically request and receive digital certificates from a Certificate Authority, typically orchestrated by an MDM solution.
The mechanism that enables zero-touch certificate provisioning for corporate devices, eliminating the need for manual certificate installation.
Case Studies
A national retail chain with 500 locations is currently using a single WPA2-Personal (PSK) network for both store operations (inventory scanners, POS tablets) and corporate staff laptops. The IT director needs to improve security to meet PCI DSS compliance and reduce the operational burden of rotating the PSK every time an employee leaves. How should they implement passwordless WiFi?
- Deploy a Cloud-RADIUS solution integrated with the central Identity Provider (e.g., Azure AD). 2. For corporate laptops, use the existing MDM (Microsoft Intune) to push a unique client certificate via SCEP, configuring devices to connect to a new 'Corp-Secure' SSID using EAP-TLS. 3. For inventory scanners and POS tablets, utilise an onboarding portal to provision device-specific certificates, binding them to a dedicated 'Ops-Secure' VLAN via RADIUS attributes. 4. Retain the PSK network temporarily, but change the password and restrict it to a quarantine VLAN to identify legacy devices that failed to migrate. 5. Once all devices are verified on the 802.1X network, decommission the PSK SSID.
A large conference centre wants to offer seamless, secure WiFi to attendees without printing passwords on badges or requiring them to re-enter a captive portal every day. They want to leverage their existing Purple analytics platform. How can they achieve this?
- The venue implements a Passpoint (Hotspot 2.0) enabled network infrastructure. 2. They utilise Purple's Connect licence, configuring Purple as the Identity Provider (IdP) for OpenRoaming. 3. When an attendee arrives, if their device already has an OpenRoaming profile (e.g., from their mobile carrier or a previous venue), they connect automatically and securely via EAP-TTLS or EAP-TLS. 4. For users without a profile, they connect to a standard onboarding SSID, authenticate once via the Purple captive portal (providing valuable first-party data), and are prompted to download a secure Passpoint profile. 5. For the remainder of the event, and on subsequent visits, the user connects automatically to the secure network without any passwords.
Scenario Analysis
Q1. You are deploying EAP-TLS across a university campus. During the pilot phase, several Windows laptops fail to connect, reporting an authentication error. The RADIUS logs show the server rejected the client certificates. The certificates are valid and issued by the correct internal CA. What is the most likely cause, and how do you resolve it?
💡 Hint:Consider the environmental factors that cryptographic certificate validation relies upon, beyond the certificate content itself.
Show Recommended Approach
The most likely cause is Clock Skew. EAP-TLS certificate validation is highly sensitive to time discrepancies. If the system time on the Windows laptops is significantly out of sync with the RADIUS server or the Certificate Authority, the certificates will be deemed invalid even if they are within their stated validity period. Resolution: ensure all devices and infrastructure components are configured to sync with a reliable NTP server. Verify time synchronisation on the RADIUS server, the CA, and the client devices.
Q2. A hospital IT director wants to implement passwordless WiFi for all clinical devices (infusion pumps, mobile workstations) but is concerned about the administrative overhead of managing certificates for thousands of headless devices that cannot use an onboarding portal. What is the recommended approach?
💡 Hint:Think about automated provisioning protocols used by device management systems, and how certificates can be delivered without user interaction.
Show Recommended Approach
The recommended approach is to leverage a Mobile Device Management (MDM) or Unified Endpoint Management (UEM) solution integrated with the hospital's PKI. Using protocols like SCEP (Simple Certificate Enrollment Protocol) or EST (Enrollment over Secure Transport), the MDM can silently request and install unique client certificates onto the clinical devices over the air, requiring zero manual intervention from IT staff or clinicians. The MDM should also be configured to automatically renew certificates before they expire.
Q3. Your organisation is transitioning from a shared PSK network to an 802.1X EAP-TLS network. You plan to run both SSIDs concurrently for one month. However, you want to ensure that users who have successfully migrated to the secure network do not accidentally fall back to the less secure PSK network. How can you configure the infrastructure to prevent this?
💡 Hint:Consider how the RADIUS server can be used to control access on the legacy network, and what information is available to it about devices that have already been provisioned.
Show Recommended Approach
Implement a RADIUS policy on the legacy PSK network that uses MAC Authentication Bypass (MAB) to identify devices. When a device successfully authenticates via EAP-TLS on the new network, its MAC address is recorded in the RADIUS database. The RADIUS policy for the legacy PSK network can then be configured to deny access — or assign to a quarantine VLAN with restricted bandwidth — for any MAC address known to be provisioned for 802.1X. This forces the device to use the secure SSID and prevents accidental fallback.



