¿Es seguro el WiFi universitario? Una guía para estudiantes
Una referencia técnica exhaustiva para gerentes de TI y operadores de recintos sobre la arquitectura de seguridad del WiFi universitario (eduroam/802.1X). Esta guía desglosa cómo funciona la autenticación de nivel empresarial, sus dificultades de implementación y cómo estos principios se aplican a implementaciones en hostelería, comercio minorista y el sector público.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: La Arquitectura de Seguridad del Campus
- IEEE 802.1X y EAP
- El Modelo de Federación eduroam
- Cifrado por Usuario
- Guía de Implementación: Aplicando la Seguridad del Campus a la Empresa
- 1. Gestión de Certificados y Configuración del Suplicante
- 2. Manejo de Dispositivos IoT sin Interfaz
- 3. Análisis y Visibilidad de Amenazas
- Mejores Prácticas para Operadores de Recintos
- Solución de Problemas y Mitigación de Riesgos
- ROI e Impacto Comercial
Resumen Ejecutivo
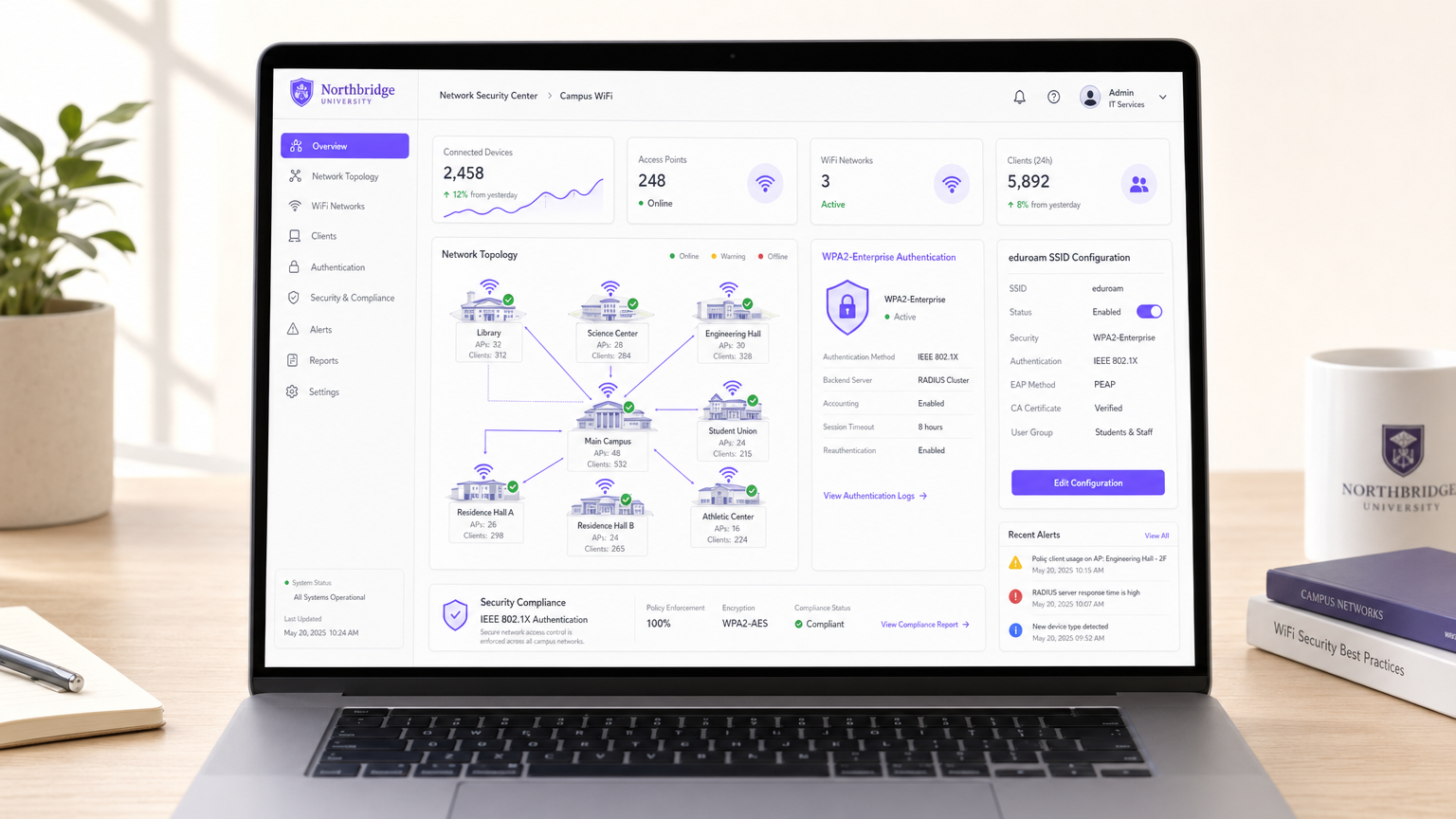
Para directores de TI y arquitectos de redes que gestionan recintos públicos o semipúblicos a gran escala, la pregunta "¿es seguro el WiFi universitario?" sirve como un estudio de caso crítico en la movilidad empresarial. Los campus universitarios representan algunos de los entornos de RF más hostiles, densos y complejos del mundo. Deben soportar decenas de miles de usuarios concurrentes, puntos finales BYOD (Bring Your Own Device) no gestionados y estrictos requisitos de cumplimiento, todo ello manteniendo una itinerancia fluida.
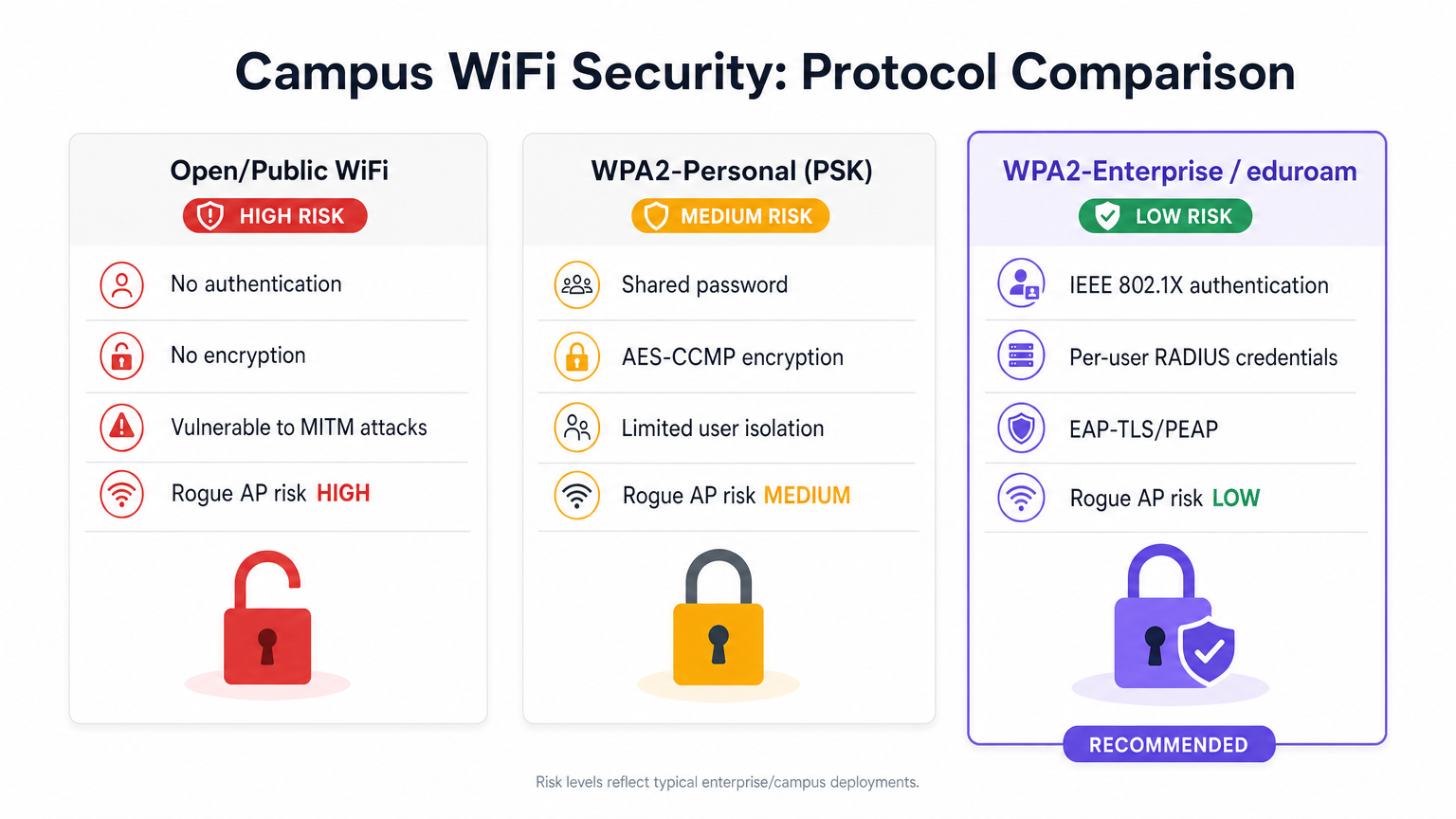
La respuesta corta es sí: cuando se diseña en torno a IEEE 802.1X y WPA2/WPA3-Enterprise (comúnmente a través de la federación eduroam), el WiFi universitario es excepcionalmente seguro. Traslada el perímetro de seguridad del borde de la red a la sesión de usuario individual, proporcionando un cifrado único por aire que neutraliza los riesgos de escucha pasiva inherentes a las redes públicas abiertas o a las implementaciones de clave precompartida (PSK) compartidas.
Esta guía desglosa la mecánica técnica de la seguridad del WiFi en campus, los errores comunes de implementación y cómo los CTO de hostelería, comercio minorista y atención médica pueden aprovechar estas mismas arquitecturas —a menudo utilizando plataformas como Guest WiFi y WiFi Analytics de Purple— para ofrecer conectividad segura y sin fricciones a escala.
Análisis Técnico Detallado: La Arquitectura de Seguridad del Campus
A diferencia del Captive Portal abierto de la cafetería local o la contraseña compartida de una pequeña empresa, las redes universitarias se basan en protocolos de autenticación de nivel empresarial.
IEEE 802.1X y EAP
La base de la seguridad del WiFi en el campus es el control de acceso a la red basado en puertos IEEE 802.1X, que opera en conjunto con el Protocolo de Autenticación Extensible (EAP).
Cuando un dispositivo cliente (el suplicante) intenta asociarse con un Punto de Acceso (el autenticador) del campus, el AP bloquea todo el tráfico IP. Solo permite el tráfico EAP sobre la LAN (EAPOL) hasta que el dispositivo se autentica con éxito contra un servidor RADIUS de backend.
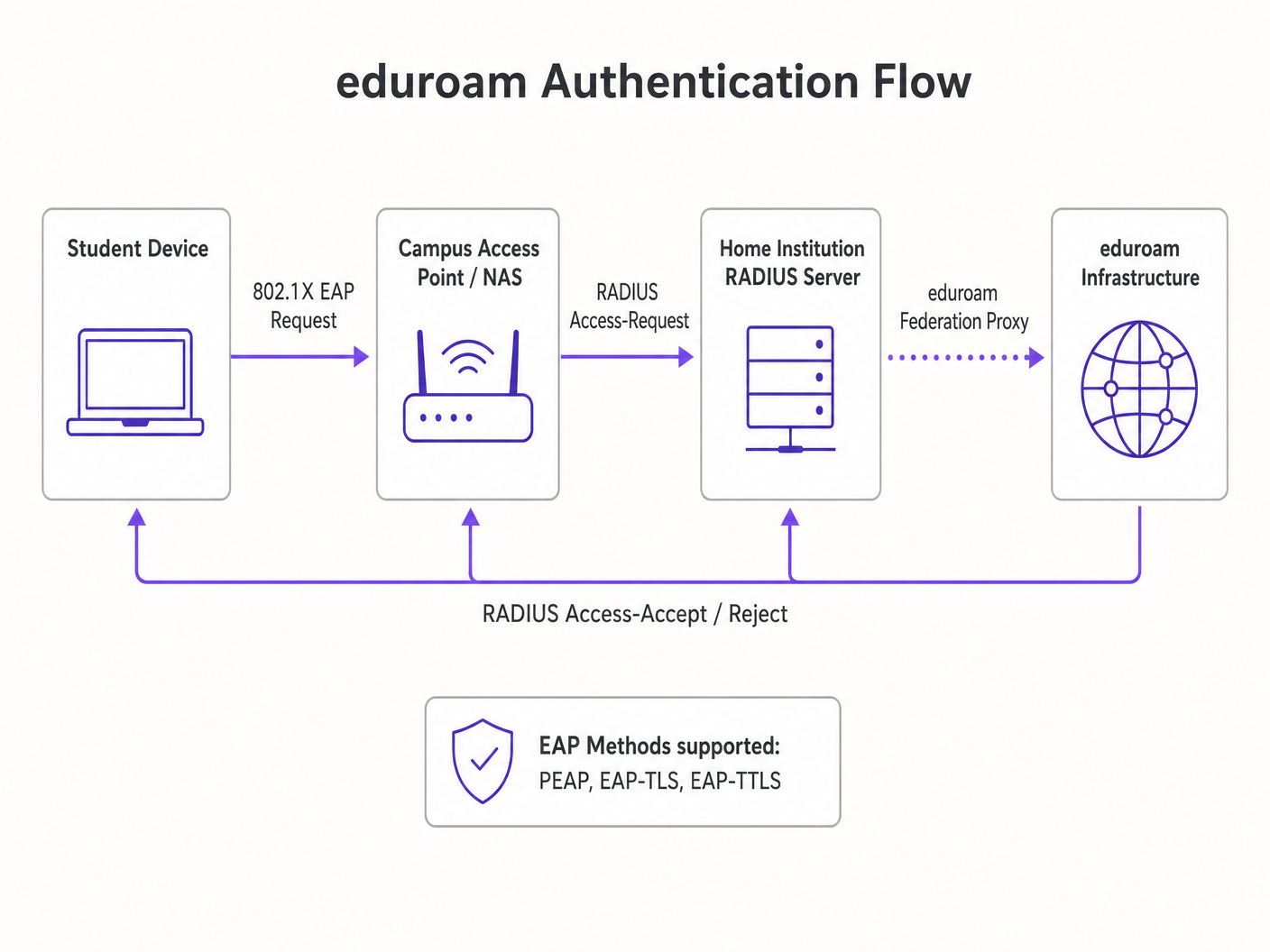
El Modelo de Federación eduroam
La implementación más prevalente en la educación superior es eduroam. Esta es una jerarquía RADIUS federada que permite a los estudiantes de instituciones participantes acceder de forma segura al WiFi en cualquier otro campus participante a nivel mundial.
- Enrutamiento de Autenticación: Si un estudiante de la Institución A visita la Institución B, el AP de la Institución B reenvía la solicitud de autenticación a su servidor RADIUS local.
- Enrutamiento de Realm: El servidor RADIUS local lee el realm del usuario (por ejemplo,
@institutionA.edu) y actúa como proxy de la solicitud al servidor RADIUS nacional de nivel superior, que la enruta al servidor principal de la Institución A. - Protección de Credenciales: La autenticación ocurre directamente entre el dispositivo del estudiante y su institución de origen a través de un túnel cifrado (típicamente PEAP o EAP-TLS). El campus visitado nunca ve la contraseña del usuario.
Cifrado por Usuario
Una vez autenticado, el servidor RADIUS envía un mensaje Access-Accept que contiene una Clave de Sesión Maestra (MSK). El AP y el dispositivo cliente utilizan esto para derivar una Clave Transitoria por Par (PTK) única.
Esto significa que el tráfico por aire de cada usuario está cifrado con una clave única. Incluso si un atacante captura el tráfico de RF, no puede descifrar los datos de otros usuarios en el mismo SSID. Esto resuelve fundamentalmente las fallas de seguridad de las redes abiertas y WPA2-Personal.
Guía de Implementación: Aplicando la Seguridad del Campus a la Empresa
Para los operadores de recintos en Comercio Minorista u Hostelería , migrar de redes abiertas a seguridad de nivel empresarial requiere una planificación cuidadosa.
1. Gestión de Certificados y Configuración del Suplicante
El talón de Aquiles de PEAP (el método EAP más común) es la validación de certificados del lado del cliente. Si el dispositivo de un usuario no está configurado para validar estrictamente el certificado del servidor RADIUS, es vulnerable a ataques de "Evil Twin" donde un AP malicioso suplanta el SSID.
Recomendación: Utilice plataformas de incorporación (como SecureW2) o perfiles MDM para configurar automáticamente los dispositivos de los usuarios. El perfil debe especificar el certificado de CA exacto y el nombre del servidor en el que confiar.
2. Manejo de Dispositivos IoT sin Interfaz
802.1X requiere un suplicante (software que maneja el diálogo de autenticación). Los televisores inteligentes, la señalización digital y el equipo médico a menudo carecen de esta capacidad. Esta es una consideración importante al implementar WiFi en Hospitales: Una Guía para Redes Clínicas Seguras .
Recomendación: Implemente un SSID paralelo utilizando Múltiples Claves Precompartidas (MPSK) o PSK de Identidad (iPSK). Esto asigna una frase de contraseña única a cada dirección MAC de dispositivo IoT, manteniendo el cifrado por dispositivo y la asignación dinámica de VLAN sin requerir 802.1X.
3. Análisis y Visibilidad de Amenazas
El cifrado es solo la mitad de la batalla; la visibilidad es la otra. Las redes empresariales deben monitorear comportamientos anómalos, APs no autorizados y suplantación de MAC.
Recomendación: Integre su Controlador de LAN Inalámbrica (WLC) con un motor de análisis robusto. La plataforma de Purple ingiere registros RADIUS, datos DHCP y telemetría de ubicación (consulte nuestra Guía del Sistema de Posicionamiento Interior: UWB, BLE y WiFi ) para proporcionar inteligencia de seguridad accionable junto con análisis de marketing.
Mejores Prácticas para Operadores de Recintos
- Implementar Aislamiento de Cliente: Configure el WLC para descartar el tráfico peer-to-peer entre clientes en la misma subred. Una laptop comprometida no debería poder escanear o atacar otro dispositivo en la red de invitados.rk.
- Direccionamiento Dinámico de VLAN: Utilice atributos RADIUS para asignar usuarios a VLANs específicas según su grupo de identidad (p. ej., Staff vs. Guest vs. IoT), aplicando la segmentación de red en el borde.
- Transición a OpenRoaming: Para espacios públicos, considere unirse a la federación WBA OpenRoaming. Purple actúa como un proveedor de identidad gratuito para OpenRoaming, ofreciendo la experiencia de descarga fluida y segura de eduroam para entornos comerciales como centros de Transporte .
Solución de Problemas y Mitigación de Riesgos
| Modo de Falla | Síntoma | Estrategia de Mitigación |
|---|---|---|
| RADIUS Timeout | Los clientes no logran autenticarse durante las horas pico. | Implemente el balanceo de carga de RADIUS y asegúrese de que el proveedor de identidad de backend (p. ej., Active Directory) tenga suficientes IOPS. |
| Ataque Evil Twin | Los usuarios se conectan a un SSID falsificado y filtran credenciales. | Aplique una validación estricta de certificados en los dispositivos cliente; utilice WIPS (Wireless Intrusion Prevention System) para localizar y suprimir APs no autorizados. |
| MAC Spoofing | Un dispositivo no autorizado elude el Captive Portal utilizando una MAC clonada. | Implemente la detección de tiempo de viaje anómalo (una dirección MAC que aparece simultáneamente en dos APs físicamente distantes) a través de plataformas de análisis. |
ROI e Impacto Comercial
Actualizar a una arquitectura WiFi 802.1X/Enterprise no es simplemente un centro de costos; es un facilitador estratégico.
- Mitigación de Riesgos: Reduce drásticamente la superficie de ataque para las filtraciones de datos, protegiendo la reputación de la marca y evitando multas regulatorias (p. ej., GDPR, PCI DSS).
- Eficiencia Operativa: Elimina la sobrecarga del servicio de asistencia técnica al gestionar contraseñas compartidas rotativas o al lidiar con problemas de compatibilidad del Captive Portal.
- Calidad de Datos: Al vincular el acceso a la red a identidades digitales verificadas en lugar de direcciones MAC efímeras, la calidad de los datos recopilados para análisis y atribución mejora significativamente.
Para una inmersión más profunda en aplicaciones verticales específicas, revise nuestra guía: ¿Es seguro el WiFi del hospital? Lo que los pacientes y visitantes deben saber (también disponible en hindi: क्या अस्पताल का WiFi सुरक्षित है? मरीजों और आगंतुकों को क्या जानना चाहिए ).
Términos clave y definiciones
IEEE 802.1X
A network authentication protocol that opens ports for network access only after a user's identity has been successfully authorized via a centralized server.
The fundamental standard required to move a venue from shared passwords to enterprise-grade, per-user security.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server that validates credentials and tells the Access Point which VLAN to assign the user to.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, allowing for various authentication methods like certificates or secure passwords.
The 'language' spoken between the user's device and the RADIUS server during the login process.
eduroam
An international roaming service for users in research, higher education, and further education, providing secure network access across participating institutions.
The primary case study for how federated 802.1X architecture can scale globally.
Supplicant
The software client on an end-user device (laptop, smartphone) that negotiates the EAP authentication with the network.
A common point of failure; if the OS supplicant is misconfigured, the user cannot connect securely.
Evil Twin Attack
A rogue wireless access point that masquerades as a legitimate Wi-Fi network to eavesdrop on wireless communications or steal credentials.
The primary threat vector that proper EAP certificate validation is designed to prevent.
VLAN Steering (Dynamic VLAN Assignment)
The process where the RADIUS server instructs the Access Point to place a specific user into a specific virtual network segment based on their identity or role.
Crucial for network segmentation, ensuring guest devices cannot route traffic to administrative servers.
OpenRoaming
A federation standard created by the WBA that allows mobile users to automatically and securely roam between Wi-Fi networks and cellular networks without captive portals.
The commercial equivalent of eduroam, allowing retail and hospitality venues to offer secure, frictionless connectivity.
Casos de éxito
A 400-room enterprise hotel currently uses an open captive portal for guest WiFi. They want to upgrade to a secure, encrypted connection for returning loyalty members without requiring them to manually log in on every visit. How should the network architect design this?
The architect should implement Passpoint (Hotspot 2.0) / OpenRoaming. When a loyalty member downloads the hotel's app, it installs an EAP-TLS certificate or a TTLS profile on the device. The hotel's WLC broadcasts the Passpoint ANQP elements. The device recognizes the network, automatically authenticates via 802.1X using the installed profile against the hotel's RADIUS server, and establishes an AES-encrypted connection. No captive portal is required for returning users.
A university IT team is deploying new wireless digital signage across the campus. These devices only support basic WPA2-Personal and cannot run an 802.1X supplicant. How can they secure these devices without creating a vulnerable campus-wide shared password?
The IT team should deploy an MPSK (Multiple Pre-Shared Key) or iPSK (Identity PSK) architecture. They broadcast a single 'Campus-IoT' SSID. However, instead of one global password, the RADIUS server generates a unique, complex PSK for the specific MAC address of each digital sign. When the sign connects, the WLC queries RADIUS, verifies the MAC-to-PSK mapping, and dynamically assigns the device to an isolated 'Digital Signage' VLAN.
Análisis de escenarios
Q1. Your enterprise retail client wants to deploy WPA3-Enterprise across 500 stores. However, they have a fleet of legacy barcode scanners that only support WPA2-Personal. How do you architect the wireless network to maximize security for corporate devices while maintaining connectivity for the scanners?
💡 Sugerencia:Consider how you can broadcast SSIDs and segment traffic at the edge.
Mostrar enfoque recomendado
Deploy two separate SSIDs. The primary SSID ('Corp-Secure') should be configured for WPA2/WPA3-Enterprise mixed mode utilizing 802.1X/PEAP, authenticating against the corporate RADIUS server for all laptops and modern devices. Deploy a secondary, hidden SSID ('Retail-IoT') utilizing Identity PSK (iPSK) or MPSK. The RADIUS server will assign a unique PSK to each barcode scanner's MAC address and dynamically steer them into an isolated, internet-only VLAN that cannot route to the corporate subnet.
Q2. During an eduroam deployment, users are complaining that their devices frequently prompt them to 'Trust this certificate' when roaming between buildings, leading to confusion and helpdesk tickets. What is the architectural flaw?
💡 Sugerencia:Think about how the supplicant verifies the identity of the authentication server.
Mostrar enfoque recomendado
The client devices (supplicants) have not been properly provisioned with a strict certificate trust profile. They are likely configured to 'prompt user' when encountering a new or updated RADIUS certificate. To fix this, the IT team must deploy an onboarding tool (like SecureW2) or an MDM payload that explicitly configures the supplicant to trust only the specific Root CA that signed the RADIUS server's certificate, and strictly match the server's domain name. This eliminates the prompt and prevents Evil Twin attacks.
Q3. A hospital IT director wants to implement Purple's WiFi Analytics but is concerned that moving from an Open Captive Portal to an 802.1X OpenRoaming architecture will break their ability to collect guest data. Is this true?
💡 Sugerencia:How does identity mapping work in federated roaming environments?
Mostrar enfoque recomendado
No, it is not true. While OpenRoaming eliminates the traditional captive portal 'splash page', it actually improves data fidelity. When a user connects via OpenRoaming, the identity provider passes specific, verified attributes (like an anonymized identifier or verified email, depending on the terms of service) to the venue's network. Purple's platform ingests this RADIUS accounting data, allowing the hospital to track dwell time, roaming patterns, and return visits with higher accuracy than MAC-based tracking, which is often broken by MAC randomization.



