O WiFi Universitário é Seguro? Um Guia para Estudantes
Uma referência técnica abrangente para gerentes de TI e operadores de locais sobre a arquitetura de segurança do WiFi universitário (eduroam/802.1X). Este guia detalha como funciona a autenticação de nível empresarial, suas armadilhas de implementação e como esses princípios se aplicam a implantações em hospitalidade, varejo e setor público.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: A Arquitetura de Segurança do Campus
- IEEE 802.1X e EAP
- O Modelo de Federação eduroam
- Criptografia por Usuário
- Guia de Implementação: Aplicando a Segurança do Campus à Empresa
- 1. Gerenciamento de Certificados e Configuração de Suplicantes
- 2. Lidando com Dispositivos IoT Headless
- 3. Análise e Visibilidade de Ameaças
- Melhores Práticas para Operadores de Locais
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios
Resumo Executivo
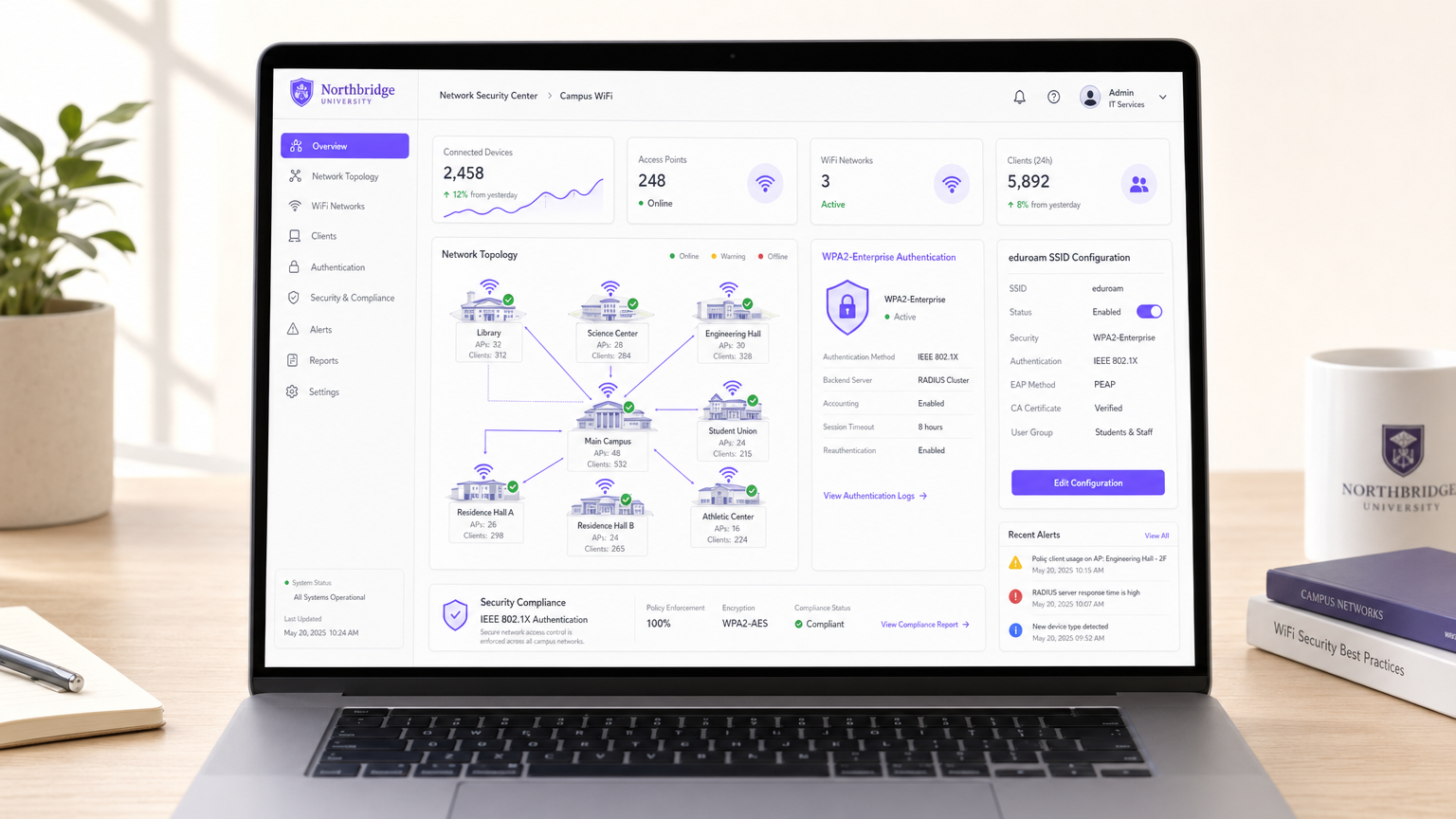
Para diretores de TI e arquitetos de rede que gerenciam grandes locais públicos ou semipúblicos, a pergunta "o WiFi universitário é seguro?" serve como um estudo de caso crítico em mobilidade empresarial. Campi universitários representam alguns dos ambientes de RF mais hostis, densos e complexos do mundo. Eles devem suportar dezenas de milhares de usuários simultâneos, endpoints BYOD (Bring Your Own Device) não gerenciados e requisitos de conformidade rigorosos, tudo isso mantendo um roaming contínuo.
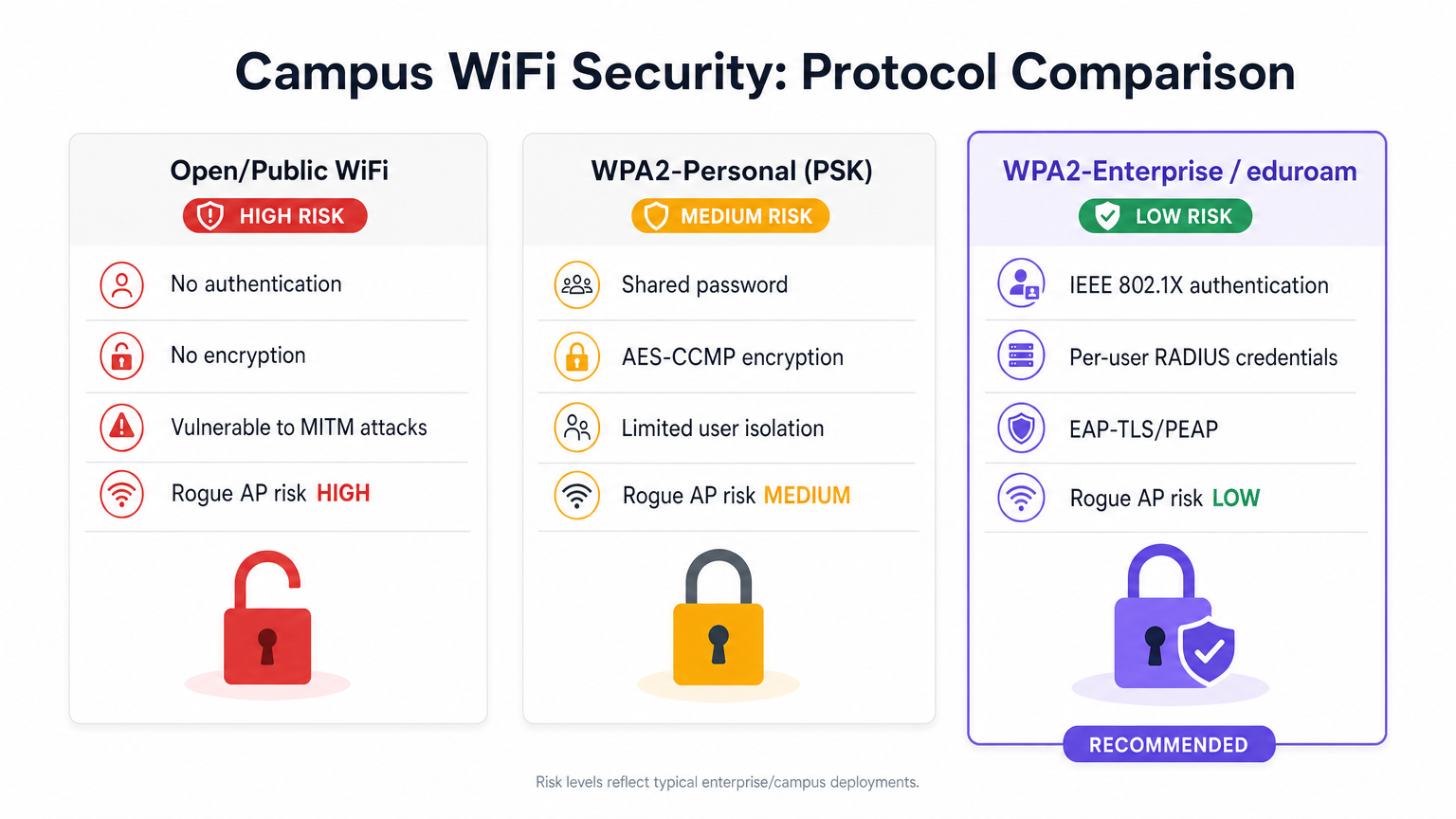
A resposta curta é sim — quando arquitetado em torno de IEEE 802.1X e WPA2/WPA3-Enterprise (comumente via federação eduroam), o WiFi universitário é excepcionalmente seguro. Ele desloca o perímetro de segurança da borda da rede para a sessão individual do usuário, fornecendo criptografia única over-the-air que neutraliza os riscos de escuta passiva inerentes a redes públicas abertas ou implantações de Chave Pré-Compartilhada (PSK) compartilhadas.
Este guia detalha a mecânica técnica da segurança do WiFi no campus, armadilhas comuns de implementação e como CTOs em hospitalidade, varejo e saúde podem aproveitar essas mesmas arquiteturas — frequentemente utilizando plataformas como o Guest WiFi e WiFi Analytics da Purple — para oferecer conectividade segura e sem atritos em escala.
Análise Técnica Aprofundada: A Arquitetura de Segurança do Campus
Ao contrário do captive portal aberto da cafeteria local ou da senha compartilhada de uma pequena empresa, as redes universitárias dependem de protocolos de autenticação de nível empresarial.
IEEE 802.1X e EAP
A base da segurança do WiFi no campus é o controle de acesso à rede baseado em porta IEEE 802.1X, operando em conjunto com o Extensible Authentication Protocol (EAP).
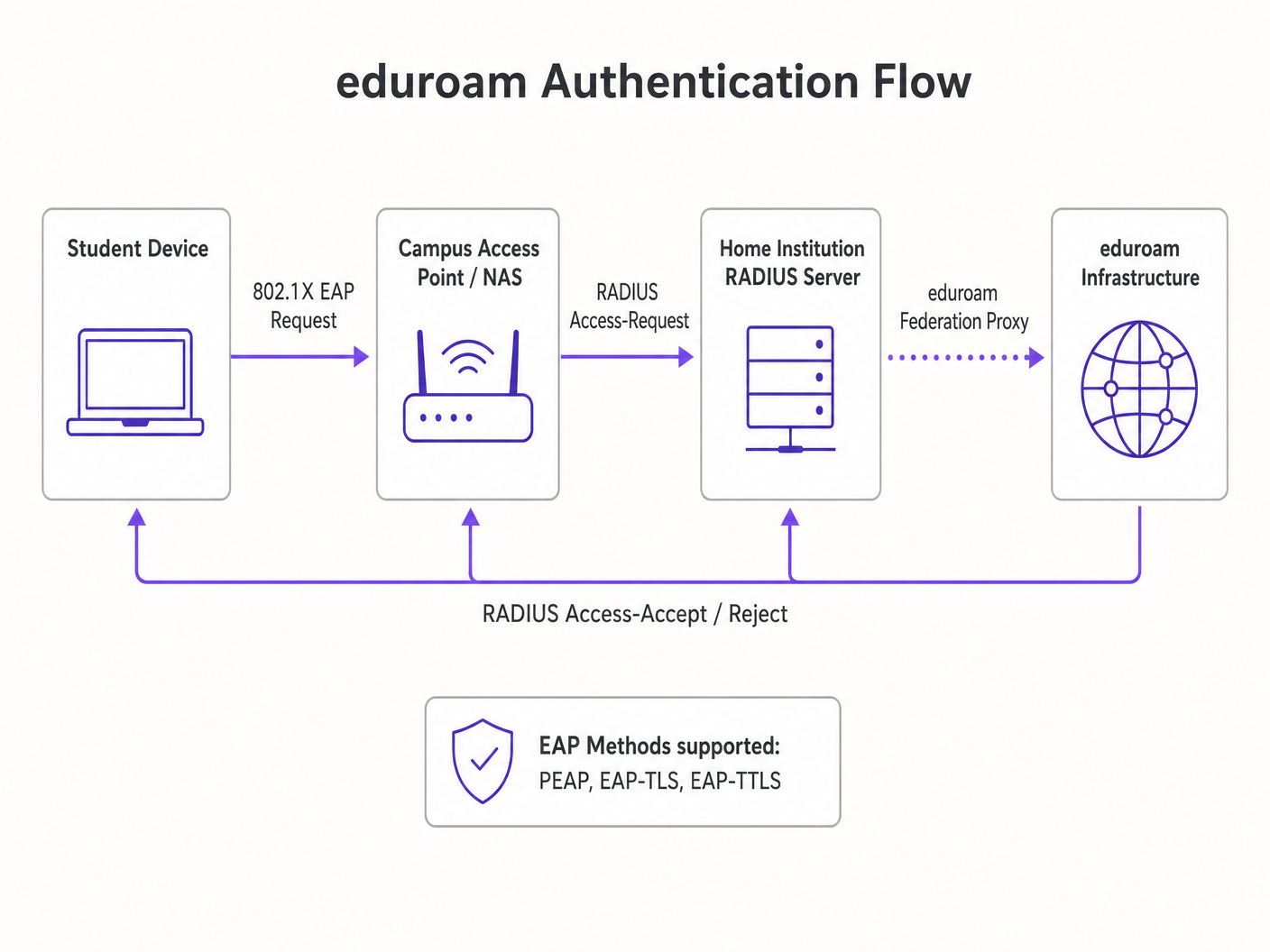
Quando um dispositivo cliente (o suplicante) tenta se associar a um Ponto de Acesso (o autenticador) do campus, o AP bloqueia todo o tráfego IP. Ele só permite o tráfego EAP sobre a LAN (EAPOL) até que o dispositivo se autentique com sucesso contra um servidor RADIUS de backend.
O Modelo de Federação eduroam
A implementação mais prevalente no ensino superior é o eduroam. Esta é uma hierarquia RADIUS federada que permite que estudantes de instituições participantes acessem com segurança o WiFi em qualquer outro campus participante globalmente.
- Roteamento de Autenticação: Se um estudante da Instituição A visita a Instituição B, o AP da Instituição B encaminha a solicitação de autenticação para seu servidor RADIUS local.
- Roteamento de Realm: O servidor RADIUS local lê o realm do usuário (por exemplo,
@institutionA.edu) e encaminha a solicitação para o servidor RADIUS de nível superior nacional, que a roteia para o servidor de origem da Instituição A. - Proteção de Credenciais: A autenticação ocorre diretamente entre o dispositivo do estudante e sua instituição de origem via um túnel criptografado (tipicamente PEAP ou EAP-TLS). O campus visitado nunca vê a senha do usuário.
Criptografia por Usuário
Uma vez autenticado, o servidor RADIUS envia uma mensagem Access-Accept contendo uma Chave de Sessão Mestra (MSK). O AP e o dispositivo cliente usam isso para derivar uma Chave Transiente Pareada (PTK) única.
Isso significa que o tráfego over-the-air de cada usuário é criptografado com uma chave única. Mesmo que um invasor capture o tráfego de RF, ele não pode descriptografar os dados de outros usuários no mesmo SSID. Isso resolve fundamentalmente as falhas de segurança de redes abertas e WPA2-Personal.
Guia de Implementação: Aplicando a Segurança do Campus à Empresa
Para operadores de locais em Varejo ou Hospitalidade , a migração de redes abertas para segurança de nível empresarial requer planejamento cuidadoso.
1. Gerenciamento de Certificados e Configuração de Suplicantes
O calcanhar de Aquiles do PEAP (o método EAP mais comum) é a validação de certificado do lado do cliente. Se o dispositivo de um usuário não estiver configurado para validar estritamente o certificado do servidor RADIUS, ele estará vulnerável a ataques Evil Twin onde um AP malicioso falsifica o SSID.
Recomendação: Utilize plataformas de onboarding (como SecureW2) ou perfis MDM para configurar automaticamente os dispositivos do usuário. O perfil deve especificar o certificado CA exato e o nome do servidor a ser confiado.
2. Lidando com Dispositivos IoT Headless
802.1X requer um suplicante (software que lida com o diálogo de autenticação). Smart TVs, sinalização digital e equipamentos médicos frequentemente não possuem essa capacidade. Esta é uma consideração importante ao implantar WiFi em Hospitais: Um Guia para Redes Clínicas Seguras .
Recomendação: Implemente um SSID paralelo utilizando Múltiplas Chaves Pré-Compartilhadas (MPSK) ou PSK de Identidade (iPSK). Isso atribui uma senha única a cada endereço MAC de dispositivo IoT, mantendo a criptografia por dispositivo e a atribuição dinâmica de VLAN sem exigir 802.1X.
3. Análise e Visibilidade de Ameaças
A criptografia é apenas metade da batalha; a visibilidade é a outra. Redes empresariais devem monitorar comportamentos anômalos, APs maliciosos e falsificação de MAC.
Recomendação: Integre seu Wireless LAN Controller (WLC) com um robusto motor de análise. A plataforma da Purple ingere logs RADIUS, dados DHCP e telemetria de localização (veja nosso Sistema de Posicionamento Interno: Guia UWB, BLE e WiFi ) para fornecer inteligência de segurança acionável juntamente com análises de marketing.
Melhores Práticas para Operadores de Locais
- Implementar Isolamento de Cliente: Configure o WLC para descartar o tráfego peer-to-peer entre clientes na mesma sub-rede. Um laptop comprometido não deve ser capaz de escanear ou atacar outro dispositivo na rede de convidados.rk.
- Direcionamento Dinâmico de VLAN: Use atributos RADIUS para atribuir usuários a VLANs específicas com base em seu grupo de identidade (por exemplo, Funcionários vs. Convidados vs. IoT), aplicando a segmentação de rede na borda.
- Transição para OpenRoaming: Para locais públicos, considere aderir à federação WBA OpenRoaming. Purple atua como um provedor de identidade gratuito para OpenRoaming, oferecendo a experiência de offload contínua e segura do eduroam para ambientes comerciais como centros de Transporte .
Solução de Problemas e Mitigação de Riscos
| Modo de Falha | Sintoma | Estratégia de Mitigação |
|---|---|---|
| RADIUS Timeout | Clientes falham ao autenticar durante horários de pico. | Implemente balanceamento de carga RADIUS e garanta que o provedor de identidade de backend (por exemplo, Active Directory) tenha IOPS suficientes. |
| Ataque Evil Twin | Usuários se conectam a um SSID falsificado e vazam credenciais. | Imponha validação rigorosa de certificados em dispositivos clientes; utilize WIPS (Wireless Intrusion Prevention System) para localizar e suprimir APs desonestos. |
| MAC Spoofing | Dispositivo não autorizado ignora o Captive Portal usando um MAC clonado. | Implemente detecção de tempo de viagem anômalo (um endereço MAC aparecendo em dois APs fisicamente distantes simultaneamente) via plataformas de análise. |
ROI e Impacto nos Negócios
Atualizar para uma arquitetura WiFi 802.1X/Enterprise não é meramente um centro de custo; é um facilitador estratégico.
- Mitigação de Riscos: Reduz drasticamente a superfície de ataque para violações de dados, protegendo a reputação da marca e evitando multas regulatórias (por exemplo, GDPR, PCI DSS).
- Eficiência Operacional: Elimina a sobrecarga do helpdesk de gerenciar senhas compartilhadas rotativas ou lidar com problemas de compatibilidade do Captive Portal.
- Qualidade dos Dados: Ao vincular o acesso à rede a identidades digitais verificadas, em vez de endereços MAC efêmeros, a qualidade dos dados coletados para análise e atribuição melhora significativamente.
Para um aprofundamento em aplicações verticais específicas, consulte nosso guia: O WiFi do Hospital é Seguro? O Que Pacientes e Visitantes Devem Saber (também disponível em hindi: क्या अस्पताल का WiFi सुरक्षित है? मरीजों और आगंतुकों को क्या जानना चाहिए ).
Termos-Chave e Definições
IEEE 802.1X
A network authentication protocol that opens ports for network access only after a user's identity has been successfully authorized via a centralized server.
The fundamental standard required to move a venue from shared passwords to enterprise-grade, per-user security.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server that validates credentials and tells the Access Point which VLAN to assign the user to.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, allowing for various authentication methods like certificates or secure passwords.
The 'language' spoken between the user's device and the RADIUS server during the login process.
eduroam
An international roaming service for users in research, higher education, and further education, providing secure network access across participating institutions.
The primary case study for how federated 802.1X architecture can scale globally.
Supplicant
The software client on an end-user device (laptop, smartphone) that negotiates the EAP authentication with the network.
A common point of failure; if the OS supplicant is misconfigured, the user cannot connect securely.
Evil Twin Attack
A rogue wireless access point that masquerades as a legitimate Wi-Fi network to eavesdrop on wireless communications or steal credentials.
The primary threat vector that proper EAP certificate validation is designed to prevent.
VLAN Steering (Dynamic VLAN Assignment)
The process where the RADIUS server instructs the Access Point to place a specific user into a specific virtual network segment based on their identity or role.
Crucial for network segmentation, ensuring guest devices cannot route traffic to administrative servers.
OpenRoaming
A federation standard created by the WBA that allows mobile users to automatically and securely roam between Wi-Fi networks and cellular networks without captive portals.
The commercial equivalent of eduroam, allowing retail and hospitality venues to offer secure, frictionless connectivity.
Estudos de Caso
A 400-room enterprise hotel currently uses an open captive portal for guest WiFi. They want to upgrade to a secure, encrypted connection for returning loyalty members without requiring them to manually log in on every visit. How should the network architect design this?
The architect should implement Passpoint (Hotspot 2.0) / OpenRoaming. When a loyalty member downloads the hotel's app, it installs an EAP-TLS certificate or a TTLS profile on the device. The hotel's WLC broadcasts the Passpoint ANQP elements. The device recognizes the network, automatically authenticates via 802.1X using the installed profile against the hotel's RADIUS server, and establishes an AES-encrypted connection. No captive portal is required for returning users.
A university IT team is deploying new wireless digital signage across the campus. These devices only support basic WPA2-Personal and cannot run an 802.1X supplicant. How can they secure these devices without creating a vulnerable campus-wide shared password?
The IT team should deploy an MPSK (Multiple Pre-Shared Key) or iPSK (Identity PSK) architecture. They broadcast a single 'Campus-IoT' SSID. However, instead of one global password, the RADIUS server generates a unique, complex PSK for the specific MAC address of each digital sign. When the sign connects, the WLC queries RADIUS, verifies the MAC-to-PSK mapping, and dynamically assigns the device to an isolated 'Digital Signage' VLAN.
Análise de Cenário
Q1. Your enterprise retail client wants to deploy WPA3-Enterprise across 500 stores. However, they have a fleet of legacy barcode scanners that only support WPA2-Personal. How do you architect the wireless network to maximize security for corporate devices while maintaining connectivity for the scanners?
💡 Dica:Consider how you can broadcast SSIDs and segment traffic at the edge.
Mostrar Abordagem Recomendada
Deploy two separate SSIDs. The primary SSID ('Corp-Secure') should be configured for WPA2/WPA3-Enterprise mixed mode utilizing 802.1X/PEAP, authenticating against the corporate RADIUS server for all laptops and modern devices. Deploy a secondary, hidden SSID ('Retail-IoT') utilizing Identity PSK (iPSK) or MPSK. The RADIUS server will assign a unique PSK to each barcode scanner's MAC address and dynamically steer them into an isolated, internet-only VLAN that cannot route to the corporate subnet.
Q2. During an eduroam deployment, users are complaining that their devices frequently prompt them to 'Trust this certificate' when roaming between buildings, leading to confusion and helpdesk tickets. What is the architectural flaw?
💡 Dica:Think about how the supplicant verifies the identity of the authentication server.
Mostrar Abordagem Recomendada
The client devices (supplicants) have not been properly provisioned with a strict certificate trust profile. They are likely configured to 'prompt user' when encountering a new or updated RADIUS certificate. To fix this, the IT team must deploy an onboarding tool (like SecureW2) or an MDM payload that explicitly configures the supplicant to trust only the specific Root CA that signed the RADIUS server's certificate, and strictly match the server's domain name. This eliminates the prompt and prevents Evil Twin attacks.
Q3. A hospital IT director wants to implement Purple's WiFi Analytics but is concerned that moving from an Open Captive Portal to an 802.1X OpenRoaming architecture will break their ability to collect guest data. Is this true?
💡 Dica:How does identity mapping work in federated roaming environments?
Mostrar Abordagem Recomendada
No, it is not true. While OpenRoaming eliminates the traditional captive portal 'splash page', it actually improves data fidelity. When a user connects via OpenRoaming, the identity provider passes specific, verified attributes (like an anonymized identifier or verified email, depending on the terms of service) to the venue's network. Purple's platform ingests this RADIUS accounting data, allowing the hospital to track dwell time, roaming patterns, and return visits with higher accuracy than MAC-based tracking, which is often broken by MAC randomization.



