Accès invité sécurisé : Implémentation du NAC pour les appareils non gérés
Ce guide de référence technique faisant autorité détaille l'architecture, le déploiement et les considérations de conformité pour l'implémentation du contrôle d'accès réseau (NAC) afin de sécuriser les appareils invités non gérés. Il fournit des conseils exploitables aux responsables informatiques pour obtenir un accès invité sécurisé sans compromettre l'infrastructure de l'entreprise.
Listen to this guide
View podcast transcript
- Résumé Exécutif
- Approfondissement Technique : Architecture NAC pour les Appareils Non Gérés
- L'Architecture à Trois Niveaux
- WPA3 et Chiffrement Sans Fil Opportuniste (OWE)
- Randomisation des Adresses MAC et Liaison d'Identité
- Guide d'Implémentation
- Étape 1 : Définir la Segmentation Réseau et les VLAN
- Étape 2 : Déployer et Configurer l'Infrastructure RADIUS
- Étape 3 : Configurer le Captive Portal et le flux d'identité
- Étape 4 : Tests et validation de bout en bout
- Bonnes pratiques et conformité
- Dépannage et atténuation des risques
- ROI et impact commercial

Résumé Exécutif
Pour les entreprises – qu'il s'agisse de l'hôtellerie, du commerce de détail ou du secteur public – offrir un accès WiFi fluide aux invités et aux sous-traitants est une nécessité commerciale. Cependant, les appareils non gérés présentent une surface d'attaque significative. Chaque smartphone, tablette et appareil IoT se connectant à votre réseau est une entité inconnue, fonctionnant en dehors du contrôle de votre infrastructure de gestion des appareils mobiles (MDM). Le défi pour les responsables informatiques est de faciliter cet accès tout en segmentant strictement ces appareils des actifs de l'entreprise et en assurant la conformité avec des cadres comme PCI DSS et GDPR.
Ce guide propose une exploration approfondie de l'implémentation du contrôle d'accès réseau (NAC) spécifiquement pour les appareils non gérés. Nous allons au-delà des clés pré-partagées de base pour explorer la segmentation réseau basée sur l'identité et appliquée par des politiques. En tirant parti des Captive Portals intégrés aux moteurs de politiques basés sur RADIUS, les organisations peuvent appliquer des postures de sécurité rigoureuses sans introduire de friction inacceptable pour l'expérience utilisateur. Nous aborderons la conception architecturale, les méthodologies de déploiement et l'intégration de plateformes comme Guest WiFi pour gérer l'identité et le consentement à grande échelle.
Approfondissement Technique : Architecture NAC pour les Appareils Non Gérés
Le contrôle d'accès réseau est l'application d'un accès basé sur des politiques aux ressources réseau. Alors que le 802.1X traditionnel avec EAP-TLS est la référence pour les appareils gérés – s'appuyant souvent sur le déploiement de certificats via SCEP (voir The Role of SCEP and NAC in Modern MDM Infrastructure ) – cette approche est inapplicable pour les invités temporaires. Les appareils non gérés nécessitent une architecture qui équilibre une sécurité robuste avec un processus d'intégration à faible friction.
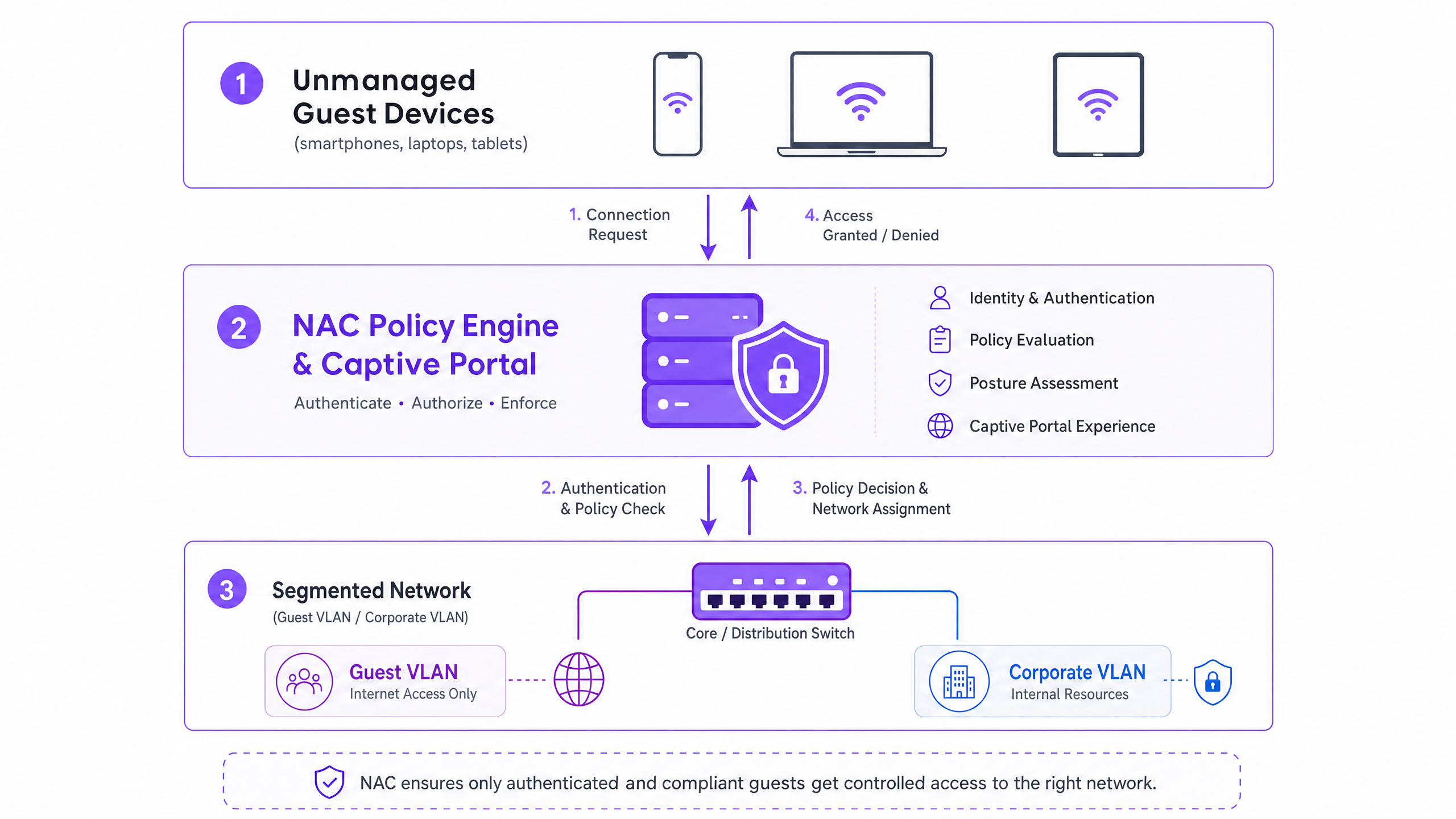
L'Architecture à Trois Niveaux
L'architecture pour un accès invité sécurisé comprend trois couches fonctionnelles :
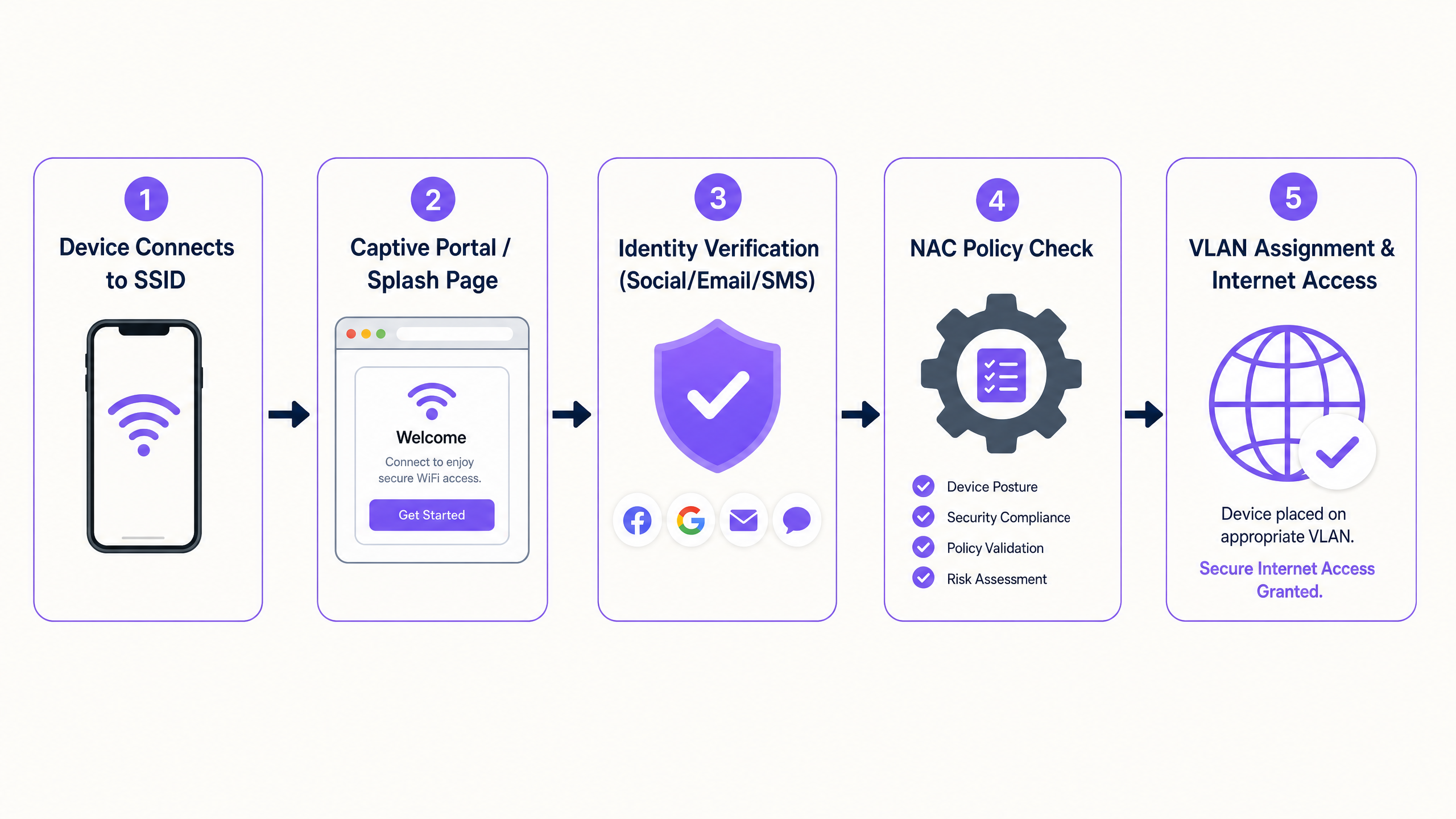
- Authentification et Capture d'Identité : Le 802.1X étant impraticable pour les appareils non gérés, la couche d'authentification repose sur un Captive Portal. Cette interface web intercepte la requête HTTP/HTTPS initiale, redirigeant l'utilisateur vers un flux d'authentification. Ici, des plateformes comme Guest WiFi de Purple fonctionnent comme fournisseur d'identité, capturant les identifiants via la connexion sociale, la vérification par e-mail ou par SMS.
- Moteur de Politiques (RADIUS/NAC) : Une fois l'identité établie, le moteur de politiques évalue la requête par rapport aux règles d'accès définies. Le système détermine le segment réseau approprié en fonction de l'identité authentifiée, du type d'appareil ou de l'heure de la journée.
- Application au Niveau du Réseau Périphérique : Les points d'accès sans fil et les commutateurs de périphérie appliquent la décision de politique. Le système NAC communique via le protocole RADIUS. Lors d'une authentification réussie, un message
Access-Acceptest renvoyé avec des attributs d'affectation de VLAN spécifiques, plaçant l'appareil sur le segment désigné.
WPA3 et Chiffrement Sans Fil Opportuniste (OWE)
La transition vers le WPA3 est essentielle pour la sécurité sans fil moderne. Alors que le WPA3-SAE remplace le vulnérable WPA2-PSK pour les réseaux personnels, le WPA3-OWE (Opportunistic Wireless Encryption) est la norme pour les réseaux invités publics. L'OWE fournit un chiffrement de données individualisé entre l'appareil client et le point d'accès sans nécessiter de mot de passe. Cela élimine la vulnérabilité de transmission en clair inhérente aux SSID invités ouverts traditionnels, offrant une base sécurisée avant même l'application de la politique NAC.
Randomisation des Adresses MAC et Liaison d'Identité
Les systèmes d'exploitation modernes (iOS 14+, Android 10+, Windows 10) implémentent la randomisation des adresses MAC pour protéger la confidentialité des utilisateurs. Les appareils génèrent une adresse MAC unique et aléatoire pour chaque SSID auquel ils se connectent. Cela rompt fondamentalement les politiques NAC héritées qui s'appuient sur l'adresse MAC comme identifiant persistant pour les invités récurrents.
La solution architecturale consiste à déplacer le modèle d'identité de l'appareil vers l'utilisateur. Lorsqu'un invité s'authentifie via le Captive Portal, la session doit être liée à son identité vérifiée (par exemple, e-mail ou numéro de téléphone) plutôt qu'à l'adresse MAC éphémère. La plateforme WiFi Analytics de Purple gère cela nativement, en maintenant des profils utilisateur persistants et des enregistrements de conformité à travers les sessions, quelle que soit la rotation de l'adresse MAC.
Guide d'Implémentation
Le déploiement du NAC pour les appareils non gérés nécessite une approche systématique pour garantir la sécurité sans perturber les opérations.
Étape 1 : Définir la Segmentation Réseau et les VLAN
Avant de configurer les politiques NAC, la segmentation réseau sous-jacente doit être rigoureuse.
- VLAN de Pré-Authentification (Quarantaine) : Les appareils sont placés ici lors de la connexion initiale. Ce VLAN ne doit autoriser que la résolution DNS et le trafic HTTP/HTTPS destiné aux adresses IP du Captive Portal. Tout autre trafic doit être abandonné.
- VLAN Invité : Après l'authentification, les appareils sont déplacés ici. Ce VLAN doit avoir un accès direct à Internet mais refuser strictement tout routage vers les sous-réseaux d'entreprise (espace RFC 1918) et les autres clients invités (isolation des clients).
- VLAN Sous-traitant/Fournisseur : Un segment séparé pour les tiers connus nécessitant un accès à des ressources internes spécifiques, contrôlé par des ACL de pare-feu granulaires.
Étape 2 : Déployer et Configurer l'Infrastructure RADIUS
Le serveur RADIUS agit comme intermédiaire entre votre périphérie réseau et le fournisseur d'identité. Pour les déploiements d'entreprise, l'intégration d'un service RADIUS hébergé dans le cloud avec votre plateforme de Captive Portal réduit les frais généraux d'exploitation et améliore la redondance. Assurez-vous que les secrets partagés RADIUS sont cryptographiquement forts et renouvelés conformément à votre politique de sécurité.
Étape 3 : Configurer le Captive Portal et le flux d'identité
Configurez le captive portal pour gérer le flux d'authentification. Cela inclut la configuration du « walled garden » (la liste des adresses IP et des domaines accessibles avant l'authentification) pour garantir que le portail se charge correctement. Il est crucial que le DNS fonctionne au sein du VLAN de pré-authentification.
Étape 4 : Tests et validation de bout en bout
Les tests doivent valider à la fois l'expérience utilisateur et les limites de sécurité. Vérifiez qu'un appareil de test complète avec succès le flux du captive portal et reçoit l'attribution de VLAN correcte via les attributs RADIUS. Plus important encore, validez la segmentation : tentez de « pinger » ou de router le trafic du VLAN Invité vers une adresse IP d'entreprise connue. Cela doit échouer.
Bonnes pratiques et conformité
- PCI DSS Compliance : Pour les établissements de Retail et d' Hospitality , la norme PCI DSS exige une isolation stricte de l'environnement de données des titulaires de carte (CDE). Le WiFi invité doit être physiquement ou logiquement séparé du CDE, sans routage autorisé. Le NAC applique cela au niveau de la couche d'accès.
- GDPR et confidentialité des données : Lors de la collecte de données d'invités via le portail, un consentement explicite doit être obtenu. Le captive portal doit présenter des conditions d'utilisation et des politiques de confidentialité claires. La plateforme sous-jacente doit prendre en charge les politiques de rétention de données automatisées et les demandes d'accès des personnes concernées.
- Gestion des sessions : Implémentez des délais d'expiration de session appropriés. Pour les environnements de vente au détail, un délai de 2 à 4 heures est typique. Pour l'hôtellerie, alignez la durée de la session sur la durée du séjour de l'invité. Configurez toujours un délai d'inactivité (par exemple, 30 minutes) pour effacer les sessions obsolètes et libérer les baux DHCP.
Dépannage et atténuation des risques
- Mauvaise configuration du Split-Tunnel : Le risque le plus grave est une règle de pare-feu mal configurée permettant le trafic du VLAN Invité vers le réseau d'entreprise. Un audit automatisé régulier des ACL de pare-feu est essentiel.
- Échecs de résolution DNS : Si les invités se plaignent que la « page de connexion ne se charge pas », le problème est presque toujours lié au DNS. Assurez-vous que la portée DHCP pour le VLAN de pré-authentification fournit un serveur DNS fiable et que le pare-feu autorise le trafic DNS (port UDP 53) vers ce serveur.
- Gestion des délais d'expiration RADIUS (Fail-Closed) : Configurez les points d'accès pour qu'ils « échouent en mode fermé » (fail-closed) si le serveur RADIUS devient inaccessible. Les configurations « échouer en mode ouvert » (fail-open) accordent un accès non authentifié pendant une panne, ce qui représente un risque de sécurité inacceptable.
ROI et impact commercial
L'implémentation d'un accès invité sécurisé via le NAC offre une valeur commerciale mesurable :
- Atténuation des risques : Réduction quantifiable de la surface d'attaque en garantissant que les appareils non gérés ne peuvent pas sonder les actifs de l'entreprise.
- Efficacité opérationnelle : L'intégration automatisée réduit les tickets du support informatique liés à l'accès invité.
- Acquisition de données : En utilisant des plateformes comme Purple, le processus d'intégration sécurisé capture simultanément des données de première partie, alimentant la plateforme WiFi Analytics pour stimuler le ROI marketing.
Key Definitions
Network Access Control (NAC)
A security framework that enforces policy-based access to network resources, evaluating identity and posture before granting access.
Used to ensure that unmanaged guest devices are properly segmented and authenticated before accessing the network.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
The primary authentication mechanism for unmanaged devices that cannot use 802.1X certificates.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The protocol used by the NAC policy engine to communicate VLAN assignments to the wireless access points.
Dynamic VLAN Assignment
The process of assigning a network device to a specific Virtual Local Area Network based on authentication credentials rather than the physical port or SSID.
Allows a single guest SSID to securely serve different types of users (guests, contractors) by placing them on different network segments.
WPA3-OWE
Opportunistic Wireless Encryption; a WiFi standard that provides individualized data encryption for open networks without requiring a password.
Secures the wireless transmission for guest networks, preventing passive eavesdropping on public SSIDs.
MAC Address Randomisation
A privacy feature in modern operating systems where the device generates a temporary MAC address for each wireless network it connects to.
Breaks legacy systems that use MAC addresses to track returning guests, necessitating identity-based authentication.
Walled Garden
A restricted environment that controls the user's access to web content and services prior to full authentication.
Required to allow unauthenticated devices to access the captive portal and necessary identity providers (like Facebook or Google) during the login process.
Client Isolation
A wireless network security feature that prevents devices connected to the same access point from communicating directly with each other.
Essential for guest networks to prevent infected guest devices from spreading malware to other guests.
Worked Examples
A large retail chain is rolling out guest WiFi across 500 stores. They need to ensure PCI compliance for their Point of Sale (POS) systems while allowing guests to connect and authenticate via a captive portal. How should the network be segmented and authenticated?
The implementation requires strict logical separation using VLANs and firewall ACLs. 1. The POS systems are placed on a dedicated, highly restricted Corporate VLAN (e.g., VLAN 10). 2. A Pre-Authentication VLAN (VLAN 20) is created for unauthenticated guests, allowing only DNS and HTTPS traffic to the captive portal domain. 3. A Guest VLAN (VLAN 30) is created for authenticated guests, allowing outbound internet access but explicitly denying all RFC 1918 (internal) IP addresses. The NAC system uses RADIUS to move devices from VLAN 20 to VLAN 30 upon successful portal authentication.
A hospital provides WiFi for patients and visitors but is experiencing issues where returning patients must re-authenticate every day because their smartphones randomize their MAC addresses. How can the IT team provide a seamless experience without compromising security?
The IT team must shift the authentication binding from the MAC address to the user identity. They implement a captive portal integrated with a platform like Purple Guest WiFi. When a patient first connects, they authenticate via SMS or email. The platform creates a persistent user profile. Even when the device generates a new MAC address on subsequent visits, the platform recognizes the user upon re-authentication and seamlessly applies the correct NAC policy without requiring a full re-registration.
Practice Questions
Q1. A hotel IT manager is configuring the pre-authentication VLAN for a new captive portal deployment. Guests are reporting that their devices connect to the WiFi, but the login page never appears. What is the most likely configuration error?
Hint: Consider what network services a device needs before it can load a web page via a domain name.
View model answer
The most likely error is a DNS resolution failure within the pre-authentication VLAN. Before a device can load the captive portal, it must resolve the portal's domain name. The DHCP scope for the pre-authentication VLAN must provide a valid DNS server, and the firewall must allow UDP port 53 traffic to that server prior to authentication.
Q2. You are designing the network policy for a stadium. The requirement is to provide internet access to fans while ensuring that the stadium's ticketing scanners (which connect to the same physical access points) have access to internal servers. How do you achieve this securely?
Hint: How can a single physical infrastructure support different logical networks based on identity?
View model answer
Implement dynamic VLAN assignment using 802.1X for the ticketing scanners and a captive portal for the fans. The ticketing scanners authenticate via certificates (802.1X) and are assigned by the RADIUS server to a secure Operations VLAN. Fans connect to an open (or OWE) SSID, authenticate via the captive portal, and are assigned by RADIUS to an isolated Guest VLAN with internet-only access.
Q3. During a security audit, it is discovered that devices on the Guest WiFi can ping the management IP addresses of the network switches. What specific configuration is missing or misconfigured?
Hint: Think about how traffic is controlled between different network segments.
View model answer
The firewall or Layer 3 switch is missing the necessary Access Control Lists (ACLs) to restrict routing from the Guest VLAN. A rule must be implemented that explicitly denies traffic originating from the Guest VLAN subnet destined for any internal subnets (RFC 1918 space), followed by a rule permitting traffic to the internet (0.0.0.0/0).