Comment configurer l'authentification WiFi 802.1X : Un guide étape par étape
Ce guide technique fournit une procédure étape par étape pour configurer l'authentification WiFi d'entreprise 802.1X. Il couvre la configuration du serveur RADIUS, le déploiement de certificats et les stratégies de déploiement pratiques pour les responsables informatiques des sites à forte affluence.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Résumé exécutif
- Approfondissement technique : L'architecture 802.1X
- Les trois composants principaux
- Méthodes EAP : Choisir la bonne posture de sécurité
- Guide de mise en œuvre : Configuration étape par étape
- Étape 1 : Préparation du serveur RADIUS
- Étape 2 : Configuration des politiques
- Étape 3 : Configuration du point d'accès
- Étape 4 : Provisionnement du Supplicant client
- Bonnes pratiques et normes de l'industrie
- Dépannage et atténuation des risques
- ROI et impact commercial
Résumé exécutif
Pour les réseaux d'entreprise, les PSKs (Pre-Shared Keys) partagées ne suffisent plus à sécuriser l'infrastructure d'entreprise. Alors que les organisations sont confrontées à des exigences de conformité plus strictes (PCI DSS, GDPR) et à une surface d'attaque croissante, la transition vers l'authentification 802.1X est un impératif de sécurité critique.
Ce guide fournit une procédure de déploiement pratique et neutre vis-à-vis des fournisseurs pour la configuration de 802.1X sur les points d'accès d'entreprise. Nous couvrons l'architecture de base — Supplicant, Authenticator et Authentication Server — ainsi que la gestion des certificats, la configuration RADIUS et les pièges courants du déploiement. Pour les responsables informatiques et les architectes réseau opérant dans les environnements de vente au détail, d'hôtellerie ou du secteur public, cette référence fournit les étapes concrètes nécessaires pour mettre en œuvre un contrôle d'accès réseau robuste basé sur l'identité, tout en maintenant une séparation stricte entre le trafic d'entreprise et celui des invités.
Écoutez notre briefing podcast ci-dessous pour un aperçu de 10 minutes de l'architecture et des stratégies de mise en œuvre.
Approfondissement technique : L'architecture 802.1X
La norme IEEE 802.1X définit le contrôle d'accès réseau basé sur les ports. Dans un contexte sans fil, elle empêche un appareil client d'envoyer ou de recevoir du trafic de données tant qu'il ne s'est pas authentifié avec succès auprès d'un répertoire central.
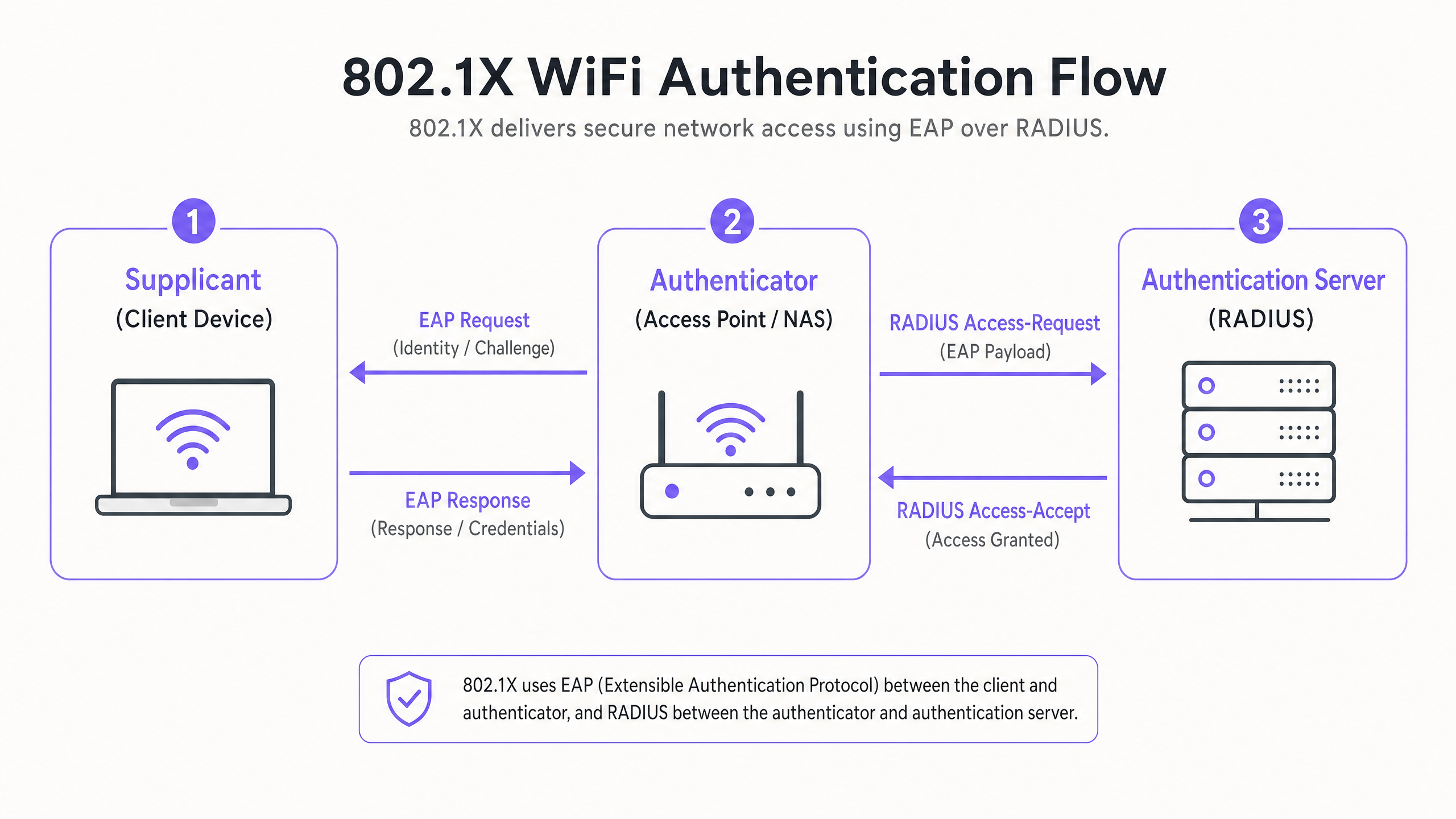
Les trois composants principaux
- Le Supplicant (appareil client) : Le logiciel sur l'ordinateur portable, le smartphone ou l'appareil IoT demandant l'accès. Il doit prendre en charge la méthode EAP (Extensible Authentication Protocol) choisie.
- L'Authenticator (Point d'accès / WLC) : L'appareil réseau agissant comme un gardien. Il ouvre un "port contrôlé" qui n'autorise le trafic EAP qu'après une authentification réussie.
- Le Authentication Server (RADIUS) : Le serveur central (par exemple, Microsoft NPS, FreeRADIUS, Cisco ISE) qui valide les identifiants par rapport à un magasin d'identités (comme Active Directory) et renvoie un message Access-Accept ou Access-Reject.
Méthodes EAP : Choisir la bonne posture de sécurité
Le choix de la méthode EAP dicte votre niveau de sécurité et la complexité du déploiement.
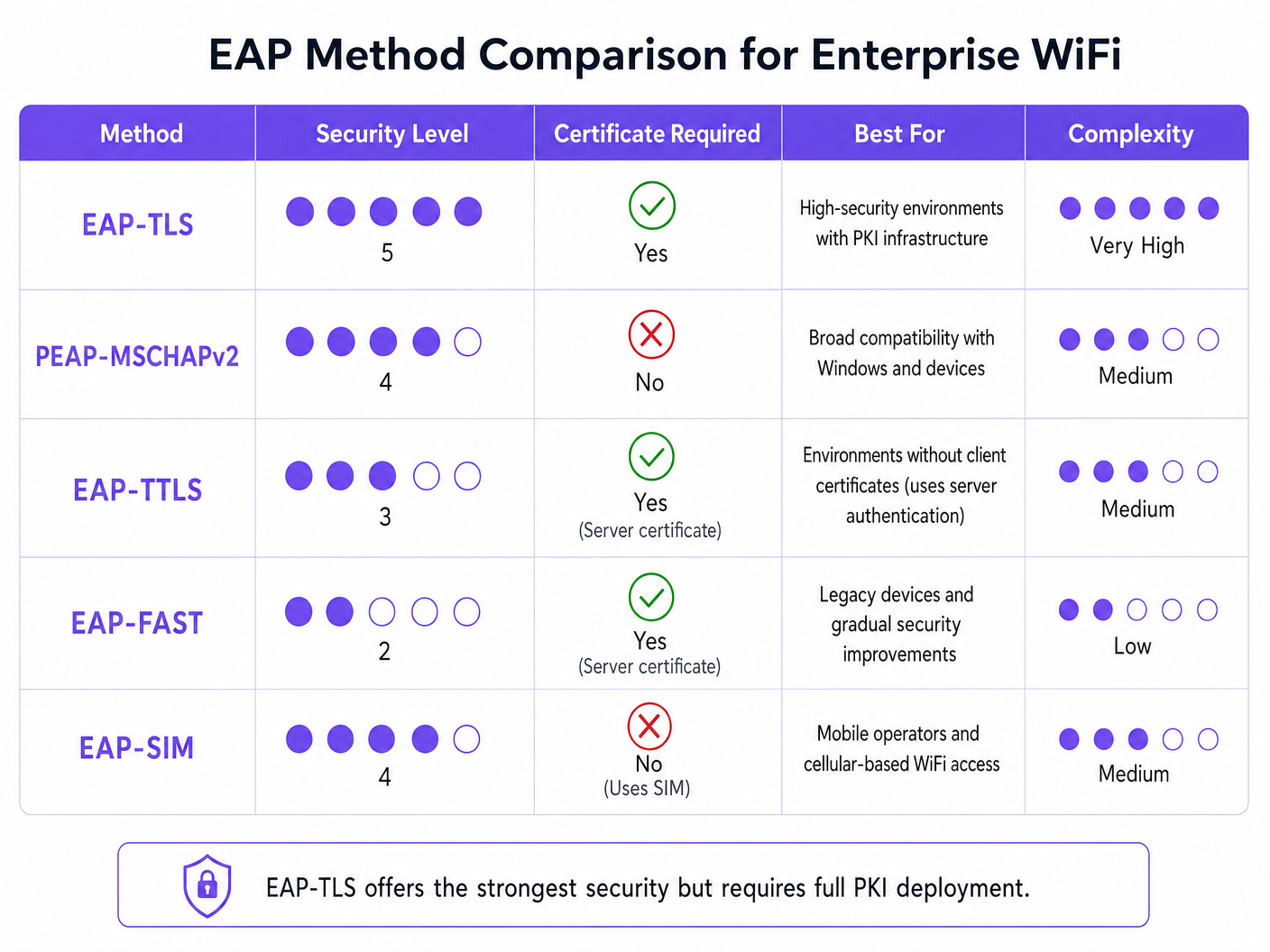
- EAP-TLS (Transport Layer Security) : La norme d'excellence. Nécessite des certificats côté serveur et côté client. Aucun mot de passe n'est transmis. Essentiel pour les environnements à haute sécurité mais nécessite une infrastructure à clé publique (PKI) complète.
- PEAP-MSCHAPv2 (Protected EAP) : Le déploiement d'entreprise le plus courant. Utilise un certificat côté serveur pour créer un tunnel TLS sécurisé, à l'intérieur duquel le client envoie un nom d'utilisateur et un mot de passe. Plus facile à déployer mais vulnérable à la collecte d'identifiants si les appareils clients ne sont pas configurés pour valider strictement le certificat du serveur.
- EAP-SIM/AKA : Utilise les identifiants de la carte SIM pour l'authentification. De plus en plus pertinent pour un onboarding fluide dans les hubs Transport et les grands lieux publics.
Guide de mise en œuvre : Configuration étape par étape
Le déploiement de 802.1X nécessite une configuration coordonnée entre votre serveur RADIUS, vos points d'accès et vos appareils clients.
Étape 1 : Préparation du serveur RADIUS
Que vous utilisiez Microsoft Network Policy Server (NPS) ou une alternative, les principes fondamentaux restent identiques.
- Définir les clients RADIUS : Enregistrez chaque Access Point (ou Wireless LAN Controller) dans votre serveur RADIUS. Attribuez un Shared Secret fort et généré aléatoirement (minimum 22 caractères) pour sécuriser les communications entre l'AP et le serveur RADIUS.
- Installer le certificat du serveur : Pour PEAP ou EAP-TLS, installez un certificat X.509 sur le serveur RADIUS. L'utilisation d'un certificat d'une autorité de certification (CA) publique de confiance simplifie le déploiement pour les environnements BYOD, car le certificat racine est déjà approuvé par les systèmes d'exploitation clients.
Étape 2 : Configuration des politiques
Configurez vos politiques réseau pour dicter les droits d'accès en fonction de l'identité.
- Politiques de demande de connexion : Définissez la manière dont le serveur RADIUS gère les demandes entrantes. Généralement, cela implique de faire correspondre le NAS-Port-Type (Wireless - IEEE 802.11) et d'authentifier les demandes localement.
- Politiques réseau : Mappez les groupes Active Directory aux droits d'accès réseau. Par exemple, mappez le groupe 'Domain Computers' au VLAN d'entreprise. Utilisez les attributs RADIUS (
Tunnel-Type=VLAN,Tunnel-Medium-Type=802,Tunnel-Private-Group-ID=[VLAN_ID]) pour attribuer dynamiquement des VLANs après une authentification réussie.
Étape 3 : Configuration du point d'accès
Configurez le SSID sur votre infrastructure sans fil (par exemple, Meraki, Aruba, Cisco).
- Créez un nouveau SSID et sélectionnez WPA2-Enterprise ou WPA3-Enterprise.
- Saisissez l'adresse IP de vos serveurs RADIUS primaire et secondaire.
- Saisissez le Shared Secret défini à l'étape 1.
- Activez l'attribution dynamique de VLAN si votre serveur RADIUS transmet des attributs VLAN.
Étape 4 : Provisionnement du Supplicant client
C'est l'étape la plus critique et souvent négligée. Ne comptez pas sur les utilisateurs pour configurer manuellement leurs appareils.
- Appareils d'entreprise : Utilisez les Group Policy Objects (GPO) ou votre plateforme Mobile Device Management (MDM) pour pousser le WiFi profile. Le profil doit spécifier la Root CA de confiance et le nom exact du serveur RADIUS pour prévenir les attaques Evil Twin.
- BYOD : Implémentez un portail d'onboarding ou une solution MDM pour pousser des profils sécurisés aux employés-appareils détenus.
Bonnes pratiques et normes de l'industrie
Pour garantir un déploiement robuste, respectez les bonnes pratiques architecturales suivantes :
- Validation stricte des certificats : Ne permettez jamais aux clients d'accepter aveuglément un certificat de serveur. C'est le principal vecteur de collecte d'identifiants PEAP.
- Isoler le trafic invité : Votre infrastructure 802.1X est destinée à l'accès d'entreprise. Le trafic invité doit rester complètement séparé. Mettez en œuvre une plateforme Guest WiFi dédiée avec son propre captive portal et sa couche d'analyse. Comme discuté dans notre guide sur Protégez votre réseau avec un DNS et une sécurité robustes , la séparation logique est fondamentale pour la défense du réseau.
- Mettre en œuvre la redondance : RADIUS est un service critique. Déployez des serveurs RADIUS primaires et secondaires. Dans les environnements distribués comme les grandes chaînes de Retail , envisagez des proxys RADIUS locaux pour assurer la survie en cas de perte de la liaison WAN.
Dépannage et atténuation des risques
Lorsque les déploiements échouent, cela est généralement dû à quelques erreurs de configuration courantes :
- Erreurs de délai d'attente RADIUS : Souvent causées par un Shared Secret non concordant entre le point d'accès (AP) et le serveur RADIUS, ou par des règles de pare-feu bloquant les ports UDP 1812 (Authentification) et 1813 (Comptabilité).
- Rejet du client : Vérifiez les journaux d'événements RADIUS (par exemple, Observateur d'événements Windows -> Vues personnalisées -> Rôles de serveur -> Services de stratégie et d'accès réseau). Recherchez l'ID d'événement 6273. Les causes courantes incluent des certificats clients expirés ou le client ne faisant pas confiance à la chaîne de certificats du serveur.
- Échecs d'attribution de VLAN : Si l'authentification réussit mais que le client n'obtient pas d'adresse IP, vérifiez que le port du commutateur connecté au point d'accès (AP) est configuré comme un port trunk autorisant le VLAN attribué dynamiquement.
ROI et impact commercial
La mise en œuvre du 802.1X génère un ROI opérationnel et de sécurité significatif :
- Atténuation des risques : Élimine le risque qu'un seul PSK compromis ne viole l'ensemble du réseau d'entreprise, soutenant directement les efforts de conformité PCI DSS et GDPR.
- Efficacité opérationnelle : Centralise le contrôle d'accès. Lorsqu'un employé quitte l'entreprise, la désactivation de son compte Active Directory révoque immédiatement son accès WiFi. Il n'est pas nécessaire de faire pivoter les PSK dans toute l'entreprise.
- Visibilité du réseau : Offre une visibilité granulaire sur qui est exactement sur le réseau et quel appareil il utilise, permettant une meilleure planification de la capacité et une chasse aux menaces.
Pour les environnements complexes et à haute densité comme les stades ou les établissements Hospitality , la gestion de la sécurité d'entreprise parallèlement à l'accès invité est un défi. En sécurisant les actifs d'entreprise avec le 802.1X et en tirant parti d'une plateforme WiFi Analytics robuste pour le trafic des visiteurs, les leaders informatiques peuvent offrir une connectivité sécurisée et évolutive qui sert à la fois l'entreprise et ses clients. Pour des informations sur la gestion des environnements à haute densité, consultez notre WiFi pour zoos et parcs à thème : Guide de connectivité pour les lieux à forte affluence .
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enterprise WiFi security, replacing vulnerable shared passwords.
Supplicant
The client device or software application requesting access to the network.
IT teams must manage supplicant configuration via MDM to ensure secure connections.
Authenticator
The network device (Access Point or Switch) that facilitates the authentication process by acting as a proxy between the Supplicant and the Authentication Server.
Configured with the RADIUS server IP and a shared secret to securely forward EAP traffic.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The backend server (like Microsoft NPS) that actually validates the user's credentials against a directory.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, supporting multiple authentication methods.
The 'language' spoken between the Supplicant and the RADIUS server.
EAP-TLS
An EAP method that uses Transport Layer Security, requiring both server and client-side certificates for mutual authentication.
The most secure method available, often mandated for high-security or classified environments.
PEAP
Protected Extensible Authentication Protocol; encapsulates EAP within an encrypted and authenticated TLS tunnel.
The most widely deployed enterprise method, balancing security with ease of deployment by only requiring a server-side certificate.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the Access Point to place an authenticated user onto a specific VLAN based on their directory group membership.
Crucial for segmenting network traffic (e.g., separating HR, Engineering, and IoT devices) while broadcasting only a single corporate SSID.
GuidesSlugPage.workedExamplesTitle
A 300-room luxury hotel needs to secure its back-of-house operational network (staff tablets, VoIP phones, management laptops) while keeping it entirely separate from the guest network. They currently use a single PSK for staff.
- Deploy Microsoft NPS linked to the hotel's existing Active Directory.
- Configure PEAP-MSCHAPv2, using a public certificate (e.g., DigiCert) on the NPS server to simplify tablet onboarding.
- Create an 802.1X SSID ('Hotel_Ops') on the APs.
- Use the hotel's MDM platform to push the 'Hotel_Ops' WiFi profile to all staff tablets and laptops, explicitly configuring the profile to trust the DigiCert root CA and validate the NPS server name.
- Maintain the existing open guest SSID, routing it through Purple's captive portal for terms acceptance and analytics, ensuring guest VLANs cannot route to the operational VLANs.
A university campus is migrating to 802.1X and needs to support a massive BYOD environment for 15,000 students across various operating systems.
- Deploy a robust RADIUS cluster (e.g., FreeRADIUS or Cisco ISE) with load balancing.
- Implement PEAP-MSCHAPv2 for broad device compatibility.
- Deploy an onboarding portal (e.g., SecureW2) that automatically configures the student's device supplicant to use the correct EAP settings and trust the university's RADIUS server certificate.
- Use dynamic VLAN assignment via RADIUS attributes to place students into appropriate subnets based on their campus location to manage broadcast domains.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your organisation is deploying 802.1X using PEAP-MSCHAPv2. During testing, users report they are prompted to 'Accept a Certificate' when connecting for the first time. How should you address this?
GuidesSlugPage.hintPrefixConsider the security implications of allowing users to make trust decisions regarding network infrastructure.
GuidesSlugPage.viewModelAnswer
You must configure the client supplicant profiles (via MDM or Group Policy) to explicitly trust the Root CA that issued the RADIUS server's certificate, and to validate the specific server name. Relying on users to manually accept certificates trains them to ignore security warnings and leaves the network vulnerable to Evil Twin (credential harvesting) attacks.
Q2. You need to secure a fleet of warehouse barcode scanners. They support WPA2-Enterprise but do not have a mechanism to install client certificates or join Active Directory. What is the most secure deployment approach?
GuidesSlugPage.hintPrefixEvaluate the EAP methods that do not require client-side certificates but still provide encrypted authentication.
GuidesSlugPage.viewModelAnswer
Deploy PEAP-MSCHAPv2. Create a dedicated service account in your directory for the scanners. Configure the RADIUS server with a server certificate to establish the TLS tunnel, and configure the scanners to authenticate using the service account credentials inside the tunnel. Ensure the RADIUS policy restricts this service account to a specific, isolated warehouse VLAN.
Q3. After configuring the APs and the RADIUS server, client devices successfully authenticate (verified in RADIUS logs with an Access-Accept), but they fail to receive an IP address and cannot access the network. What is the most likely infrastructure issue?
GuidesSlugPage.hintPrefixAuthentication has succeeded, meaning the 802.1X phase is complete. The issue lies in the subsequent network provisioning phase.
GuidesSlugPage.viewModelAnswer
The most likely issue is a VLAN misconfiguration on the wired network. If the RADIUS server is using dynamic VLAN assignment to place the client on a specific VLAN (e.g., VLAN 20), the switch port connecting the Access Point must be configured as an 802.1Q trunk port that allows VLAN 20. If the VLAN is not trunked to the AP, the client's DHCP requests will be dropped.



