Minimiser les distractions des étudiants grâce au blocage des publicités au niveau du réseau
Ce guide de référence technique faisant autorité détaille l'architecture, le déploiement et l'impact commercial du blocage des publicités au niveau du réseau dans les environnements éducatifs. Il fournit aux responsables informatiques et aux architectes réseau des stratégies concrètes pour récupérer de la bande passante, renforcer la conformité et éliminer les risques de malvertising.
Écouter ce guide
Voir la transcription du podcast
- Résumé Exécutif
- Approfondissement Technique
- Architecture de Filtrage au Niveau DNS
- Inspection Proxy et SSL
- Intégration avec le Contrôle d'Accès Réseau (NAC)
- Guide d'Implémentation
- Phase 1 : Audit du Trafic et Établissement de la Ligne de Base
- Phase 2 : Déploiement Pilote
- Phase 3 : Déploiement Complet et Ajustement des Politiques
- Bonnes Pratiques
- Dépannage et atténuation des risques
- ROI et impact commercial
Résumé Exécutif
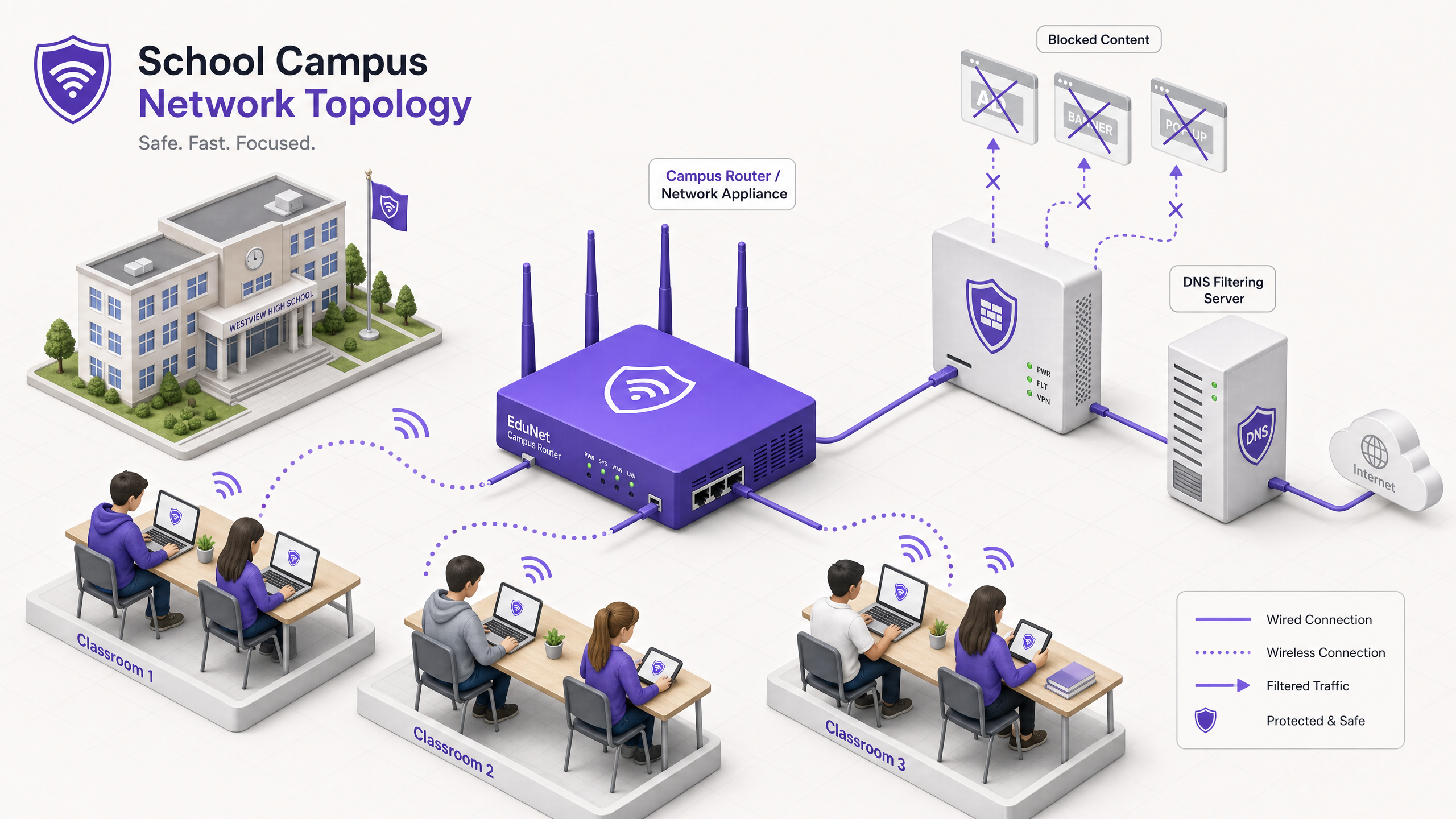
Pour les directeurs informatiques et les architectes réseau gérant des environnements éducatifs, la prolifération des appareils a créé une tempête parfaite de consommation de bande passante, de risques de protection et de lacunes en matière de conformité. Avec des étudiants apportant en moyenne 2,5 appareils sur le campus, la gestion du filtrage basé sur les terminaux n'est plus une stratégie opérationnelle viable.
Le blocage des publicités au niveau du réseau représente un changement fondamental, passant de la gestion des terminaux au contrôle de la couche d'infrastructure. En interceptant le trafic au niveau DNS ou proxy avant qu'il n'atteigne l'appareil client, les équipes informatiques peuvent éliminer unilatéralement jusqu'à 30 % de la consommation de bande passante non éducative, atténuer les risques de malvertising et faire respecter la conformité avec les cadres de protection des données comme le GDPR et le COPPA.
Ce guide de référence technique décrit l'architecture, la méthodologie de déploiement et la mesure du retour sur investissement pour la mise en œuvre du blocage des publicités au niveau du réseau sur les campus K-12 et universitaires, en s'appuyant sur des déploiements réels dans des environnements à haute densité.
Écoutez notre podcast complémentaire pour un aperçu stratégique :
Approfondissement Technique
La mise en œuvre du blocage des publicités au niveau du réseau nécessite une approche architecturale en couches pour gérer la diversité du trafic web moderne, en particulier l'omniprésence du HTTPS et des protocoles DNS chiffrés émergents.
Architecture de Filtrage au Niveau DNS
La couche fondamentale du blocage des publicités réseau est le filtrage DNS. Lorsqu'un appareil client tente de résoudre un domaine associé aux réseaux publicitaires, à la télémétrie ou au suivi, le résolveur DNS du réseau intercepte la requête et la vérifie par rapport à une liste de blocage dynamique.
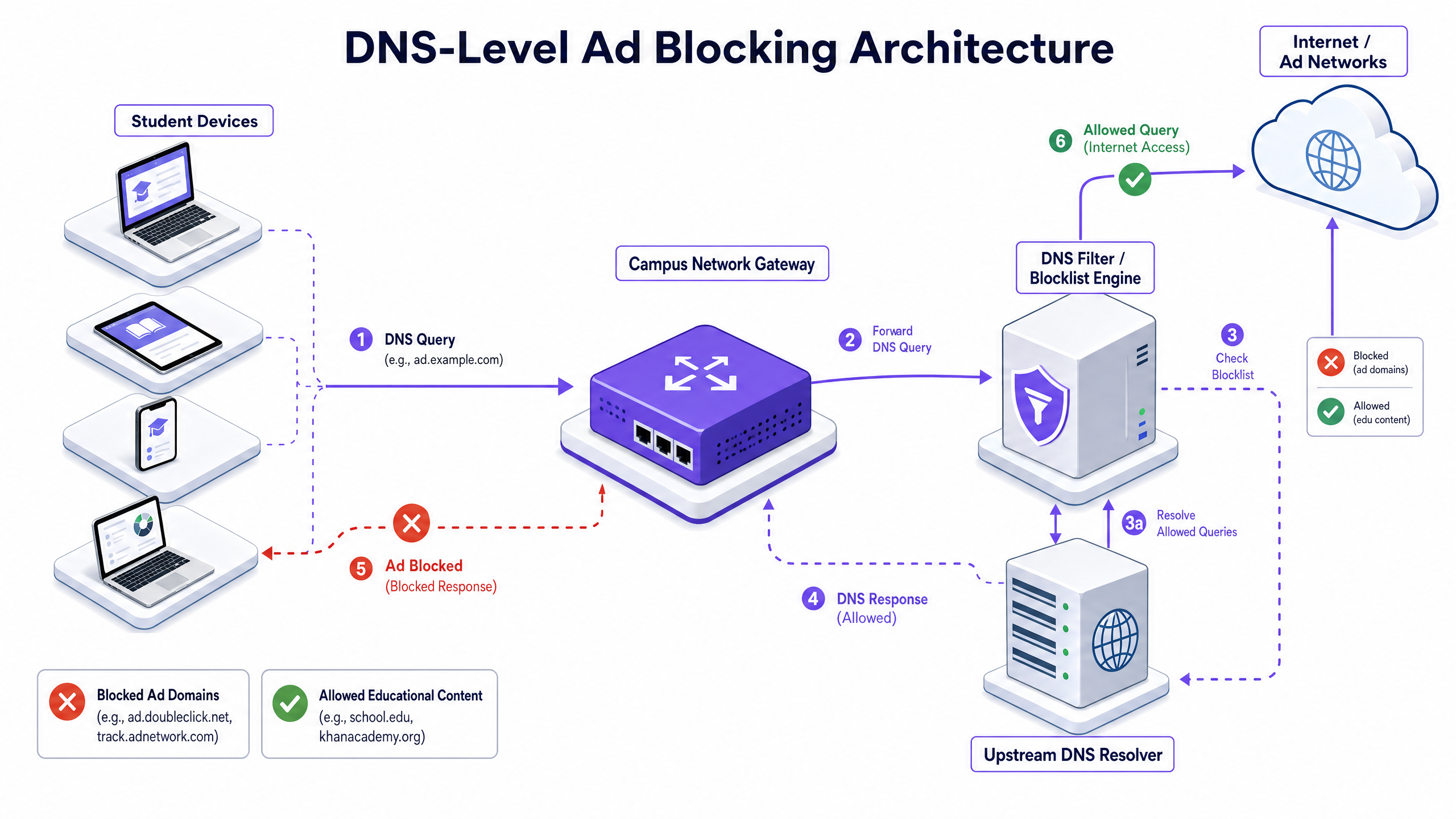
Cette approche est très efficace car elle empêche l'établissement de la connexion. La charge utile de l'annonce n'est jamais téléchargée et le script de suivi ne s'exécute jamais. Cependant, les déploiements modernes doivent tenir compte du DNS-over-HTTPS (DoH) et du DNS-over-TLS (DoT). Si les appareils clients contournent le résolveur local en utilisant un DNS chiffré, la couche de filtrage est contournée. Les architectes réseau doivent configurer les pare-feu périmétriques pour bloquer les points d'extrémité DoH/DoT connus (tels que 8.8.8.8 sur le port 443) afin de forcer le retour au DNS standard (port 53), ou déployer une solution de passerelle qui inspecte nativement le trafic DoH.
Inspection Proxy et SSL
Alors que le filtrage DNS gère la majorité du trafic publicitaire, le proxy HTTP/HTTPS transparent offre un contrôle granulaire sur des URL spécifiques plutôt que sur des domaines entiers. Étant donné que la grande majorité du trafic web est chiffrée, le déploiement de l'inspection SSL (décryptage Man-in-the-Middle) est nécessaire pour l'inspection approfondie des paquets.
Cela nécessite le déploiement d'un certificat racine de confiance sur tous les appareils gérés. Bien que pratique courante dans les environnements d'entreprise, l'inspection SSL dans les environnements éducatifs nécessite une délimitation minutieuse pour éviter de décrypter le trafic sensible (par exemple, les portails bancaires ou de santé) et doit s'aligner sur la politique d'utilisation acceptable de l'organisation.
Intégration avec le Contrôle d'Accès Réseau (NAC)
Un filtrage efficace nécessite des politiques basées sur l'identité. L'intégration avec IEEE 802.1X permet au réseau d'appliquer des politiques de filtrage différenciées basées sur l'utilisateur authentifié ou le profil de l'appareil. Un étudiant se connectant au réseau via WPA3-Enterprise reçoit une politique restrictive, tandis qu'un membre du personnel reçoit une politique différente, et un visiteur sur le réseau Guest WiFi reçoit une politique de conformité de base.
Guide d'Implémentation
Le déploiement du blocage des publicités au niveau du réseau nécessite une approche progressive pour éviter de perturber les activités éducatives légitimes.
Phase 1 : Audit du Trafic et Établissement de la Ligne de Base
Avant d'implémenter des règles de blocage, déployez la solution de filtrage en mode de surveillance passive (journalisation uniquement) pendant 14 à 21 jours. Cela établit une ligne de base des volumes de requêtes DNS actuels et de leur catégorisation. Utilisez ces données pour identifier les principaux réseaux publicitaires et domaines de suivi qui consomment actuellement de la bande passante. Cette ligne de base est essentielle pour le calcul ultérieur du retour sur investissement et le reporting WiFi Analytics .
Phase 2 : Déploiement Pilote
Sélectionnez un segment de réseau représentatif – tel qu'un seul VLAN étudiant ou un bâtiment spécifique – pour la phase pilote. Appliquez les politiques initiales de liste de blocage ciblant les réseaux publicitaires et les traqueurs connus.
Étape Cruciale : Établissez un processus de demande de liste blanche à réponse rapide. Les enseignants rencontreront inévitablement de faux positifs où du contenu éducatif légitime est hébergé sur des domaines catégorisés comme publicitaires ou de suivi. Le service d'assistance informatique doit être prêt à évaluer et à mettre en liste blanche les domaines rapidement pour maintenir la confiance des parties prenantes.
Phase 3 : Déploiement Complet et Ajustement des Politiques
Étendez le déploiement à tous les segments de réseau pertinents, en appliquant des politiques différenciées via l'intégration 802.1X. Surveillez les journaux en continu pendant les premières 48 heures pour identifier tout problème systémique.
Assurez-vous que le déploiement s'aligne sur des politiques de sécurité plus larges, telles que la tenue d'un Explain what is audit trail for IT Security in 2026 pour démontrer la conformité aux exigences de protection.
Bonnes Pratiques
- Défense en Couches : Ne vous fiez pas uniquement au filtrage DNS. Combinez-le avec la gestion des terminaux pour les appareils appartenant à l'école et des règles de pare-feu robustes pour bloquer les tentatives de contournement (par exemple, les protocoles VPN, DoH).
- Sécurité Standardisée : Assurez-vous que tous les nouveaux déploiements sans fil utilisent WPA3 pour protéger contre le vol d'identifiants, qui est un vvecteur pour les étudiants tentant d'accéder aux réseaux du personnel afin de contourner le filtrage.
- Alignement de la conformité : Au Royaume-Uni, assurez-vous que vos politiques de filtrage respectent les exigences de base décrites dans le Conformité IWF pour les réseaux WiFi publics au Royaume-Uni (ou Cumplimiento IWF para redes WiFi públicas en el Reino Unido pour les opérations hispanophones).
- Examen régulier : Les réseaux publicitaires changent constamment de domaines pour échapper aux listes de blocage. Assurez-vous que votre solution de filtrage utilise des flux de renseignements sur les menaces mis à jour dynamiquement plutôt que des listes statiques.
Dépannage et atténuation des risques
| Mode de défaillance | Cause première | Stratégie d'atténuation |
|---|---|---|
| Contournement via DNS chiffré | Les étudiants configurant les navigateurs pour utiliser DoH/DoT (par exemple, Cloudflare, Google DNS). | Bloquez les adresses IP des fournisseurs DoH connus au niveau du pare-feu ; imposez la résolution DNS locale via DHCP. |
| Contournement via VPN | Utilisation de clients VPN commerciaux ou d'extensions de navigateur. | Bloquez les protocoles VPN courants (IPsec, OpenVPN, WireGuard) et les domaines de fournisseurs VPN connus sur les VLAN étudiants. |
| Sur-blocage (faux positifs) | Filtrage heuristique agressif bloquant le contenu éducatif. | Mettez en œuvre un processus de demande de liste blanche rationalisé et soutenu par un SLA pour le personnel enseignant ; testez les politiques de manière approfondie avant un déploiement complet. |
| Fuite IPv6 | Filtrage appliqué uniquement à IPv4, permettant le contournement via la résolution DNS IPv6. | Assurez-vous que la solution de filtrage et l'infrastructure réseau prennent entièrement en charge et appliquent les politiques sur l'ensemble de la pile IPv6. |
ROI et impact commercial
L'analyse de rentabilisation du blocage des publicités au niveau du réseau va au-delà de la simple protection ; elle offre des gains d'efficacité opérationnelle mesurables.
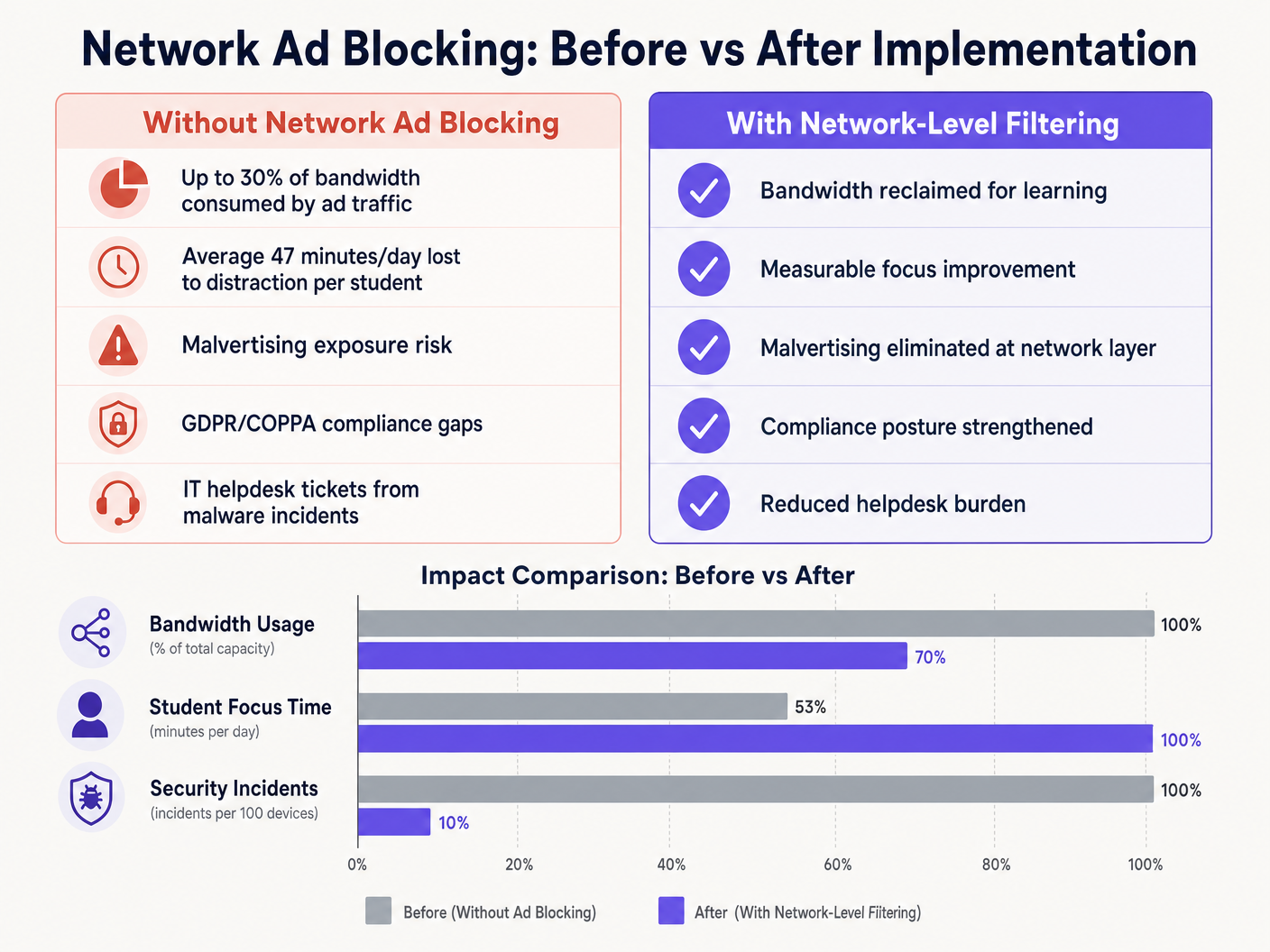
En éliminant les charges utiles publicitaires et les scripts de suivi à la périphérie du réseau, les sites récupèrent généralement 15 % à 30 % de leur bande passante totale. Cette capacité récupérée retarde le besoin de mises à niveau coûteuses des circuits et améliore les performances des applications cloud critiques. De plus, le blocage des domaines de malvertising au niveau DNS réduit considérablement le volume d'incidents de logiciels malveillants, diminuant directement le nombre de tickets du service d'assistance informatique et les coûts de remédiation.
Que ce soit pour un déploiement dans une école, l'optimisation du Wi-Fi de bureau : Optimisez votre réseau Wi-Fi de bureau moderne , ou la gestion d'environnements à haute densité dans le Commerce de détail , le Secteur de la santé , le Secteur de l'hôtellerie , ou le Transport , la compréhension de la couche physique, telle que les Fréquences Wi-Fi : Un guide des fréquences Wi-Fi en 2026 , et la sécurisation de la couche logique par le filtrage DNS sont des composants essentiels de l'architecture réseau moderne.
Définitions clés
DNS Filtering
The process of using the Domain Name System to block malicious websites and filter out harmful or unwanted content by returning a null IP address for blocked domains.
The primary mechanism for network-level ad blocking, operating upstream of client devices.
DNS-over-HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
A common method used to bypass local network DNS filtering policies.
Malvertising
The use of online advertising to spread malware, often through legitimate advertising networks without the publisher's knowledge.
A key security risk mitigated by network-level ad blocking.
SSL Inspection
The process of intercepting, decrypting, and inspecting HTTPS traffic for malicious content or policy violations before re-encrypting and forwarding it.
Required for deep packet inspection of encrypted web traffic, though complex to deploy in BYOD environments.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Used to identify users and devices to apply differentiated filtering policies.
WPA3-Enterprise
The latest generation of Wi-Fi security, providing enhanced cryptographic strength and protecting against dictionary attacks.
Essential for securing campus networks and ensuring users cannot easily spoof identities to bypass filtering.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
Used to segment student, staff, and guest traffic to apply different security and filtering policies.
Transparent Proxy
An intermediary system that sits between a user and a content provider, intercepting requests without requiring client-side configuration.
Used to enforce URL-level filtering policies without deploying endpoint agents.
Exemples concrets
A large multi-academy trust with 15,000 students across 12 campuses needs to implement ad blocking. They currently use a mix of school-issued Chromebooks and a BYOD policy for sixth-form students. The network is struggling with bandwidth congestion during peak hours.
- Deploy a cloud-managed DNS filtering solution across all 12 campuses, pointing all DHCP-assigned DNS settings to the cloud resolvers.
- Configure the firewall to block outbound port 53 traffic to any external IP other than the approved cloud resolvers to prevent manual DNS overrides.
- Block known DoH provider IPs at the firewall.
- Integrate the DNS filtering solution with the trust's Active Directory via 802.1X to apply different filtering policies: a strict policy for the Chromebook VLAN and a slightly more permissive policy for the BYOD VLAN, while maintaining core ad and malvertising blocking across both.
A university campus IT team receives complaints from the Computer Science faculty that the new network ad blocking solution is preventing access to legitimate development tools and APIs used in coursework.
- Review the DNS query logs for the Computer Science VLAN to identify the specific domains being blocked.
- Create a dedicated policy group for the Computer Science faculty and student VLANs.
- Implement a scoped whitelist for the required development domains, applying it only to the Computer Science policy group to maintain security across the rest of the campus.
- Establish a fast-track IT ticketing category specifically for 'Educational Content Blocking' to handle future requests with a 2-hour SLA.
Questions d'entraînement
Q1. You have deployed DNS filtering across the campus network, but monitoring shows that a significant number of student BYOD devices are still loading ads and accessing restricted content. What is the most likely cause, and how should you address it?
Conseil : Consider how modern browsers handle DNS queries independently of the operating system's network settings.
Voir la réponse type
The most likely cause is that modern browsers on the BYOD devices are using DNS-over-HTTPS (DoH) to bypass the local network's DNS resolver. To address this, configure the perimeter firewall to block known DoH provider IP addresses and drop outbound traffic on port 53 that does not originate from the approved campus DNS resolvers. This forces the devices to fall back to the local, filtered DNS infrastructure.
Q2. The school's leadership team wants to block all social media and advertising networks globally across the entire campus to ensure maximum compliance. As the IT Director, why might you advise against a single global policy, and what architecture would you propose instead?
Conseil : Consider the different user groups on campus and their specific needs.
Voir la réponse type
A single global policy will inevitably cause operational friction. Staff may need access to social media for communications or marketing, and certain ad networks may be required for legitimate educational tools. Instead, propose a segmented architecture using 802.1X integration to apply identity-aware policies. Create distinct VLANs and policy groups for Students, Staff, and Guests, applying strict blocking to students while allowing necessary access for staff.
Q3. Before switching the new DNS filtering solution into active enforcement mode, what critical operational process must be established with the IT helpdesk?
Conseil : Think about the impact of false positives on teaching staff.
Voir la réponse type
A rapid-response whitelist request process must be established. Heuristic filtering will inevitably block some legitimate educational resources (false positives). Without a fast, SLA-backed process for teachers to request domains be unblocked, the deployment will disrupt learning and cause stakeholder resistance.