WiFi dans les trains : Le guide complet pour les opérateurs ferroviaires et les passagers
Ce guide de référence détaille l'architecture, les défis de déploiement et les opportunités commerciales du WiFi passager dans les trains. Conçu pour les dirigeants informatiques et opérationnels, il aborde l'agrégation du backhaul, la segmentation du réseau et la manière de transformer une obligation de conformité en analyses passagers exploitables.
🎧 Écouter ce guide
Voir la transcription
- Résumé Exécutif
- Plongée Technique : L'Architecture à Trois Couches
- Couche 1 : Backhaul WAN et Agrégation
- Couche 2 : Le Réseau Embarqué et la Segmentation
- Couche 3 : Accès Passager et Matériel de Cabine
- Guide d'Implémentation : Déploiement et Conformité
- ROI et Impact Commercial : Transformer les Données en Intelligence
- Écoutez le briefing
Résumé Exécutif
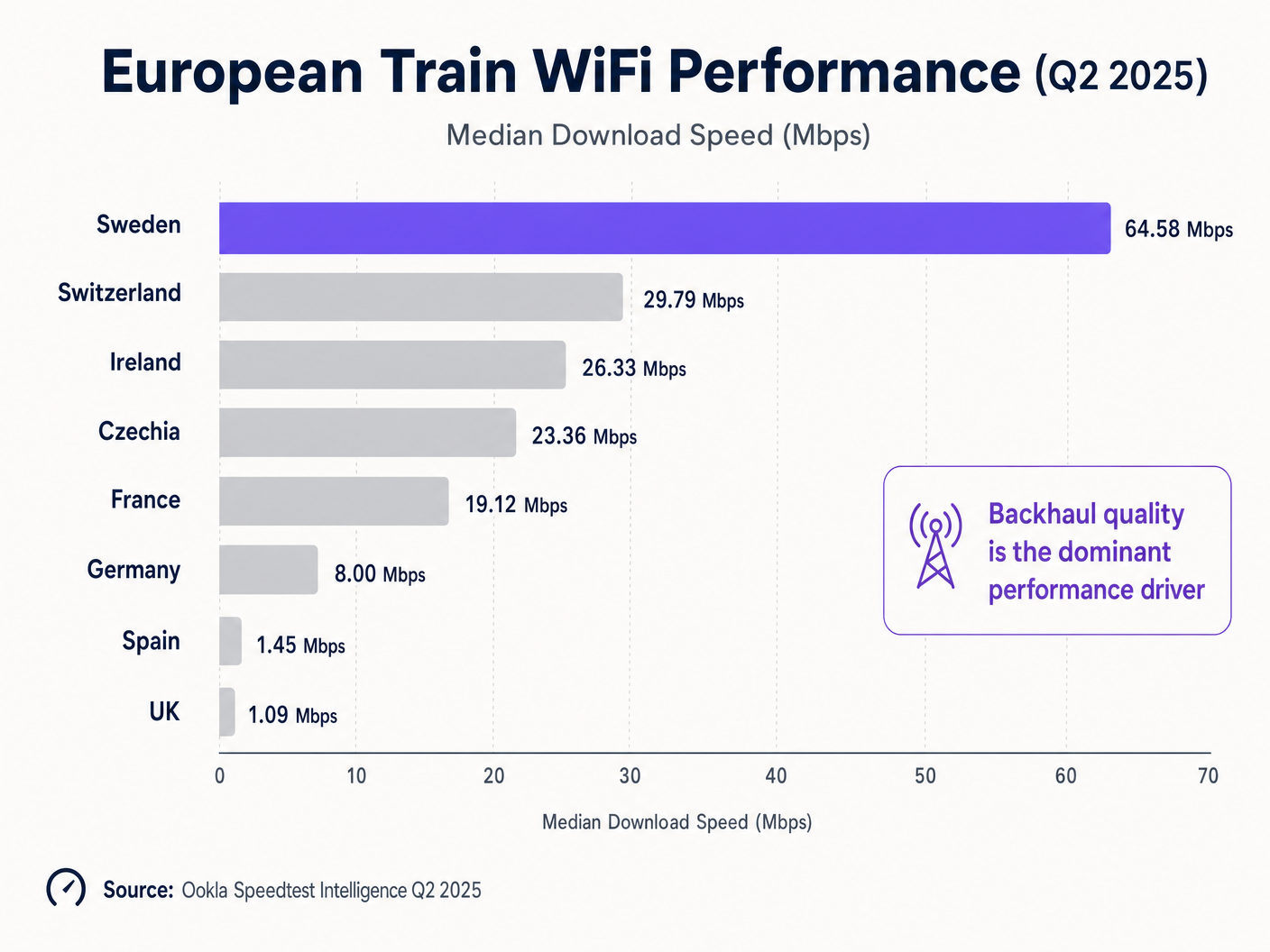
Pour les opérateurs ferroviaires, un WiFi de haute qualité dans les trains est passé d'un avantage pour les passagers à une infrastructure opérationnelle essentielle. L'écart entre les déploiements de pointe et les systèmes hérités est frappant : les données d'Ookla pour le T2 2025 montrent que la Suède offre des vitesses de téléchargement médianes de 64,58 Mbps, tandis que le Royaume-Uni stagne à 1,09 Mbps [1]. Cette différence de 59 fois n'est pas principalement un problème technologique ; c'est un échec d'architecture et de stratégie d'investissement.
Ce guide fournit un modèle neutre vis-à-vis des fournisseurs pour les directeurs informatiques, les architectes réseau et les responsables des opérations de site. Nous analysons l'architecture à trois couches requise pour une connectivité embarquée résiliente, explorons l'exigence de sécurité critique de la segmentation du réseau et démontrons comment des plateformes comme Guest WiFi transforment les données de connexion brutes en intelligence commerciale exploitable. Que vous gériez une ligne interurbaine à grande vitesse ou un service de banlieue régional, les principes d'agrégation du backhaul et de capture de données conforme au GDPR restent identiques.
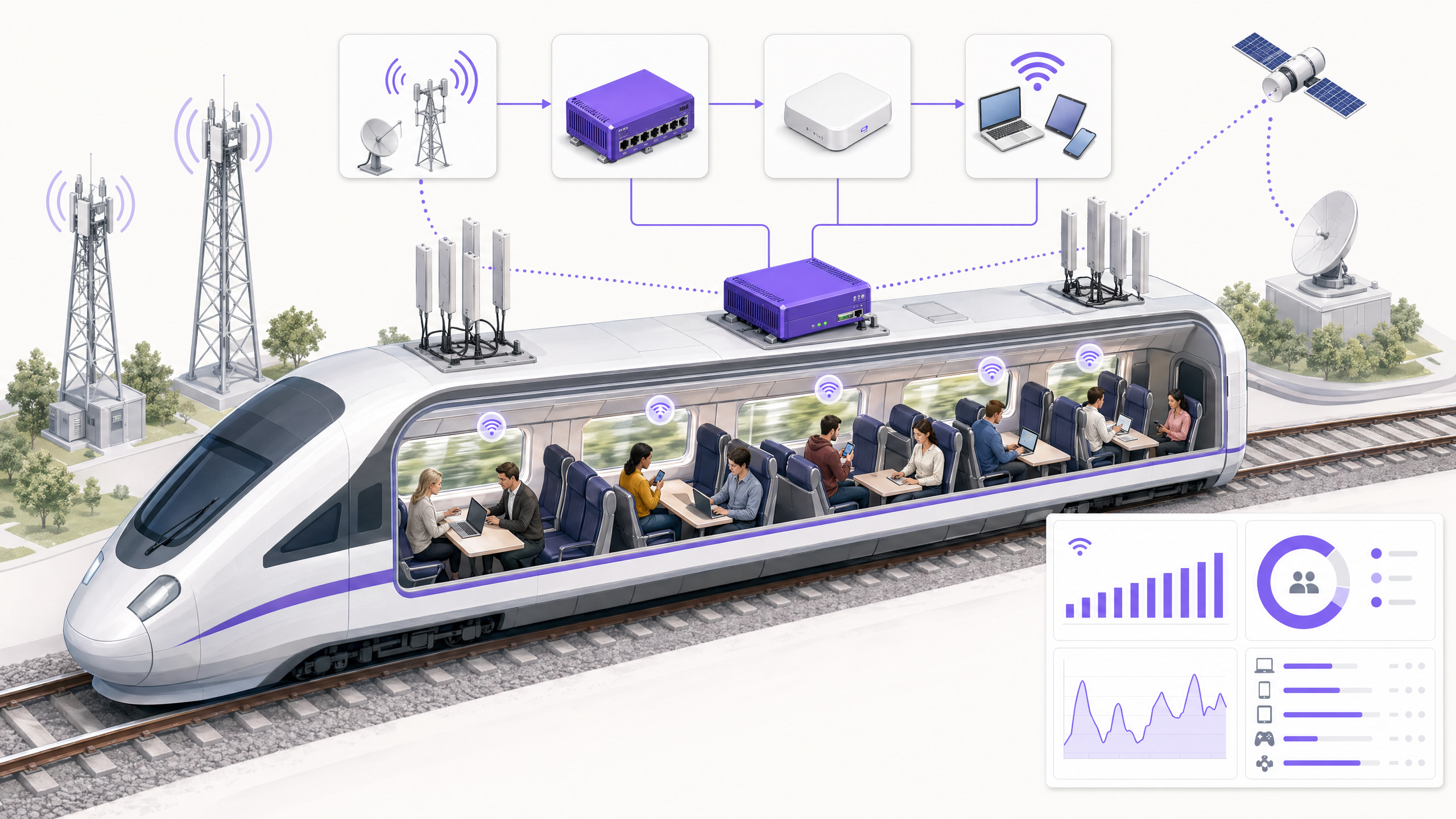
Plongée Technique : L'Architecture à Trois Couches
Un déploiement WiFi moderne dans les trains est fondamentalement différent des déploiements statiques que l'on trouve dans le Commerce de Détail ou l' Hôtellerie . Le réseau doit maintenir la persistance de session tout en se déplaçant à 300 km/h, en passant d'une cellule de voie à l'autre et en pénétrant le matériel roulant fortement isolé.
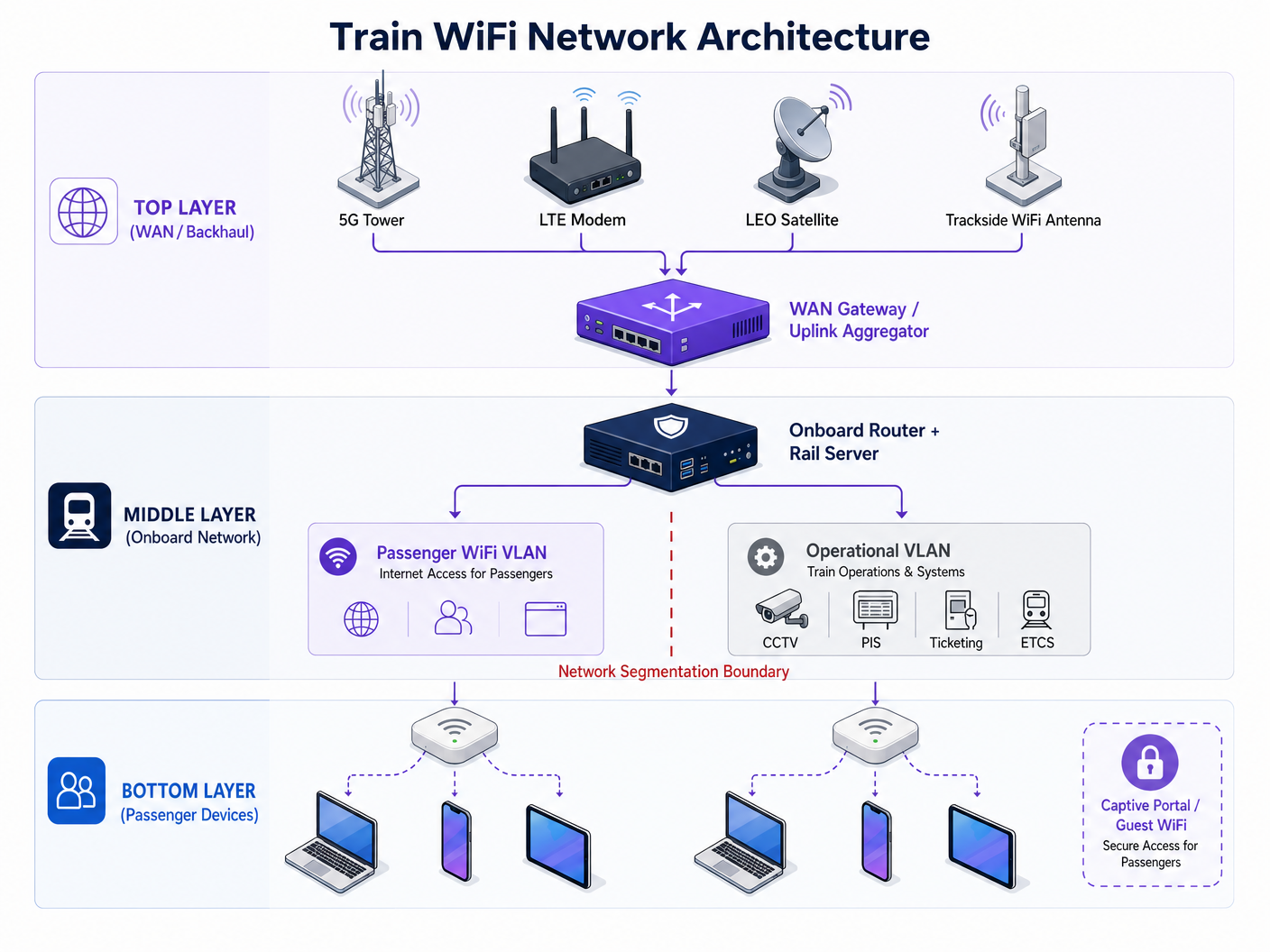
Couche 1 : Backhaul WAN et Agrégation
Le plafond de votre expérience passager est entièrement dicté par votre capacité de backhaul. Un seul modem LTE avec une antenne montée sur le toit n'est plus viable. Les architectures modernes utilisent une WAN Gateway pour agréger plusieurs liaisons montantes :
- Agrégation Cellulaire : Combinaison de connexions 4G/5G de plusieurs opérateurs de réseaux mobiles (MNO) pour atténuer les zones blanches de couverture d'un seul réseau.
- Infrastructure Latérale de Voie : Réseaux sans fil dédiés 5 GHz ou 60 GHz déployés le long du corridor ferroviaire.
- Satellite LEO : Constellations en orbite terrestre basse (par exemple, Starlink) offrant un débit de 100-200 Mbps dans les sections rurales ou transfrontalières où le cellulaire terrestre échoue [2].
Couche 2 : Le Réseau Embarqué et la Segmentation
La WAN Gateway alimente un routeur embarqué et un serveur ferroviaire. Cette couche gère la tâche critique de la Segmentation du Réseau.
> "Le WiFi passager doit fonctionner sur un VLAN complètement isolé, sans chemin de routage vers le réseau opérationnel qui transporte les flux CCTV, les systèmes d'information passagers (PIS) ou les données de signalisation du système européen de contrôle des trains (ETCS)."
Une cyberattaque en 2024 sur un réseau WiFi passager au Royaume-Uni a démontré les risques graves d'une segmentation inadéquate, où des vulnérabilités exposées au public ont compromis une infrastructure terminale plus large [3]. La mise en œuvre de l'authentification basée sur les ports IEEE 802.1X et de règles de pare-feu inter-VLAN strictes est une exigence de sécurité non négociable. De plus, le serveur ferroviaire offre un hébergement d'applications conteneurisées, permettant aux services de mise en cache de contenu local et de portail captif de fonctionner même lorsque la connectivité backhaul est interrompue.
Couche 3 : Accès Passager et Matériel de Cabine
La dernière couche est constituée des points d'accès (AP) distribués dans toutes les voitures. Le matériel hérité est un frein important aux performances. En Allemagne, la mise à niveau du WiFi 4 (802.11n) vers le WiFi 5 (802.11ac) a entraîné une amélioration de la vitesse de 241 %, tandis que le déplacement du trafic de la bande 2,4 GHz vers 5 GHz a généré une augmentation de 328 % [1]. Pourtant, près de 40 % des connexions ferroviaires européennes reposent encore sur le WiFi 4.
Guide d'Implémentation : Déploiement et Conformité
Le déploiement du WiFi dans les trains est un projet d'intégration de systèmes complexe. Les étapes suivantes décrivent une stratégie de déploiement robuste :
- Réaliser un Audit du Backhaul : Avant de spécifier les AP de cabine, auditez votre itinéraire pour détecter les lacunes de couverture cellulaire. Concevez votre stratégie d'agrégation de liaisons montantes autour de ces zones blanches.
- Spécifier des Fenêtres Perméables aux RF : Les fenêtres de train modernes utilisent des revêtements métalliques pour l'efficacité thermique, ce qui peut atténuer les signaux cellulaires de 20 à 30 dB. Des antennes montées sur le toit alimentant des AP internes sont obligatoires pour surmonter cela.
- Mettre en Œuvre un Portail Captif Robuste : Le portail captif est l'interface principale entre le passager et l'opérateur. Il doit capturer en toute sécurité les identifiants vérifiés (e-mail ou connexion sociale) tout en présentant les conditions de service.
- Assurer la Conformité au GDPR : Les opérateurs doivent établir une base légale pour le traitement des données des passagers. Le consentement doit être donné librement et enregistré sans ambiguïté. Protégez Votre Réseau avec un DNS et une Sécurité Robustes est une considération essentielle ici.
ROI et Impact Commercial : Transformer les Données en Intelligence
Fournir du WiFi gratuit représente une dépense opérationnelle significative. Pour générer un ROI, les opérateurs doivent exploiter la couche de connexion pour collecter des données de première partie.
Lorsque les passagers s'authentifient via un portail captif conforme, les opérateurs peuvent créer des profils riches de comportement de voyage. C'est là que WiFi Analytics devient transformateur. En analysant les fréquences de connexion, les temps d'arrêt dans des gares spécifiques et les schémas d'occupation des voitures, les opérateurs obtiennent une intelligence opérationnelle qui rivalise avec les informations recueillies dans les pôles de Transport et les aéroports.
Par exemple, comprendre qu'une cohorte spécifique de voyageurs d'affaires se connecte systématiquement sur le service de 07h30 permet des communications marketing ciblées et à forte valeur ajoutée ou l'intégration de programmes de fidélité. Cette approche basée sur les données transforme le réseau WiFi en fd'un centre de coûts à un actif générateur de revenus.
Écoutez le briefing
Pour une analyse plus approfondie de l'architecture et de la stratégie commerciale, écoutez notre briefing technique complet :
Références : [1] Ookla Speedtest Intelligence, "Fast Trains, Slow Wi-Fi: The Reality of Onboard Connectivity in Europe and Asia", T2 2025. [2] Essais industriels, Intégration de satellites LEO pour la mobilité, 2024-2025. [3] Railway Technology, "UK passenger wifi network hacked", Septembre 2024.
Termes clés et définitions
WAN Aggregation
The process of combining multiple Wide Area Network connections (e.g., two 5G connections and a satellite link) into a single logical connection to increase throughput and resilience.
Critical for trains moving through varying cellular coverage areas to prevent dropped connections.
Network Segmentation (VLAN)
Dividing a computer network into smaller, isolated sub-networks. Virtual Local Area Networks (VLANs) keep traffic separated logically even if it shares the same physical switches.
Essential for preventing a compromised passenger device from accessing critical train control systems.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Used to enforce terms of service, collect user data, and secure GDPR consent.
RF Attenuation
The reduction in signal strength as radio waves pass through a medium.
Modern train windows with metallic thermal coatings cause massive RF attenuation, requiring roof-mounted antennas.
LEO Satellite
Low Earth Orbit satellites that operate much closer to Earth than traditional geostationary satellites, offering lower latency and higher bandwidth.
Increasingly used as a backhaul solution for trains in rural or cross-border areas.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Used to secure the operational network interfaces on the train from unauthorized access.
Rail Server
A ruggedized onboard computer designed to host containerized applications locally on the train.
Used to host local entertainment, caching, and captive portal services to reduce reliance on the WAN link.
First-Party Data
Information a company collects directly from its customers and owns.
The primary commercial output of a properly configured Guest WiFi network.
Études de cas
A regional rail operator running 4-carriage commuter trains through a mix of dense urban areas and deep rural valleys is experiencing severe passenger complaints regarding WiFi dropouts. Their current setup uses a single 4G LTE modem per train. How should they redesign their architecture?
- Upgrade the WAN Backhaul: Replace the single LTE modem with a WAN Gateway capable of uplink aggregation. Install dual-SIM routers using two different Mobile Network Operators (MNOs) to provide failover in urban areas.
- Address Rural Gaps: For the deep valleys where cellular coverage is non-existent, integrate a LEO satellite terminal (e.g., Starlink Mobility) into the WAN Gateway as a secondary aggregated link.
- Local Caching: Deploy an onboard rail server to cache the captive portal and key journey information locally, ensuring the passenger UI remains responsive even during brief total connection losses in tunnels.
An intercity rail franchise is upgrading its fleet and wants to use the new onboard WiFi to gather passenger analytics for marketing, similar to how [Retail](/industries/retail) venues operate. What compliance and technical steps must they take?
- Captive Portal Deployment: Implement a robust captive portal that requires users to authenticate via email or social login before accessing the internet.
- GDPR Compliance: Ensure the portal explicitly asks for opt-in consent for marketing communications. Pre-ticked boxes must not be used. The system must log the timestamp and version of the privacy policy consented to.
- Analytics Integration: Route the authenticated session data into a centralized WiFi Analytics platform to track journey frequency, dwell time, and cross-reference with ticketing data where permissible.
Analyse de scénario
Q1. Your CTO wants to upgrade all carriage access points to WiFi 6 to solve passenger complaints about slow internet speeds. Your current backhaul is a single 4G connection. What is the correct architectural response?
💡 Astuce :Consider where the actual bottleneck in the data flow is occurring.
Afficher l'approche recommandée
Advise the CTO to halt the AP upgrade and invest the budget in a WAN Gateway capable of uplink aggregation. Upgrading to WiFi 6 will improve local device-to-AP speeds within the carriage, but the total throughput to the internet remains choked by the single 4G connection. Fix the backhaul bottleneck first.
Q2. During a network design review, an engineer suggests routing the train's CCTV data through the same router interfaces as the passenger WiFi to save on cabling costs. How do you respond?
💡 Astuce :Consider the security implications of mixing public and operational traffic.
Afficher l'approche recommandée
Reject the proposal immediately. Passenger WiFi and operational systems like CCTV must be strictly segmented into isolated VLANs with deny-all firewall rules between them. Mixing this traffic creates a critical security vulnerability, potentially allowing a malicious actor on the public WiFi to access or disrupt train operations.
Q3. The marketing team wants to automatically subscribe all passengers who use the free WiFi to a weekly newsletter to boost engagement. What must you configure on the captive portal to ensure this is legal?
💡 Astuce :Review the requirements for lawful data processing under GDPR.
Afficher l'approche recommandée
You must configure the captive portal to include an explicit, unticked opt-in checkbox for marketing communications. Automatic subscription or pre-ticked boxes violate GDPR requirements for freely given, unambiguous consent. The system must also log the timestamp of this consent for audit purposes.



