WiFi Passager : Comment les Opérateurs de Transport Utilisent les Données WiFi pour Comprendre les Trajets
Ce guide technique explique comment les opérateurs de transport exploitent l'infrastructure WiFi passager pour capturer des analyses opérationnelles. Il couvre l'architecture technique, les meilleures pratiques de déploiement et les applications concrètes pour mesurer l'affluence, le temps de présence et les schémas de trajet.
🎧 Écouter ce guide
Voir la transcription
- Résumé Exécutif
- Approfondissement Technique : Architecture et Flux de Données
- Surmonter la Randomisation des Adresses MAC
- Guide d'Implémentation : De l'Infrastructure aux Insights
- Bonnes Pratiques et Cas d'Utilisation Opérationnels
- Étude de Cas Réelle : Réseau Ferroviaire Interurbain
- Étude de cas réelle : Opérations de terminal de ferry
- Dépannage et atténuation des risques
- ROI et impact commercial

Résumé Exécutif
Pour les opérateurs de transport — qu'ils gèrent des réseaux ferroviaires interurbains, des flottes de bus urbains ou des services de ferry maritimes — le WiFi passager est souvent considéré strictement comme un coût opérationnel ou un service aux passagers. Cependant, lorsqu'elle est intégrée à une couche d'analyse de niveau entreprise, cette infrastructure existante se transforme en un puissant outil d'intelligence opérationnelle. En capturant les métadonnées de connexion des appareils, les opérateurs peuvent cartographier l'affluence des passagers, mesurer les temps de présence dans les zones de gare et suivre les schémas de trajet sans dépendre uniquement des données de billetterie.
Ce guide fournit aux responsables informatiques, aux architectes réseau et aux directeurs des opérations un cadre pratique pour le déploiement et l'exploitation de l'analyse WiFi passager. Nous explorons l'architecture technique sous-jacente requise pour capturer les signaux des appareils en toute sécurité, les cas d'utilisation opérationnels qui génèrent un ROI mesurable, et les exigences de conformité nécessaires pour traiter ces données dans les cadres GDPR et de protection des données.
Écoutez le briefing de notre consultant senior sur ce sujet :
Approfondissement Technique : Architecture et Flux de Données
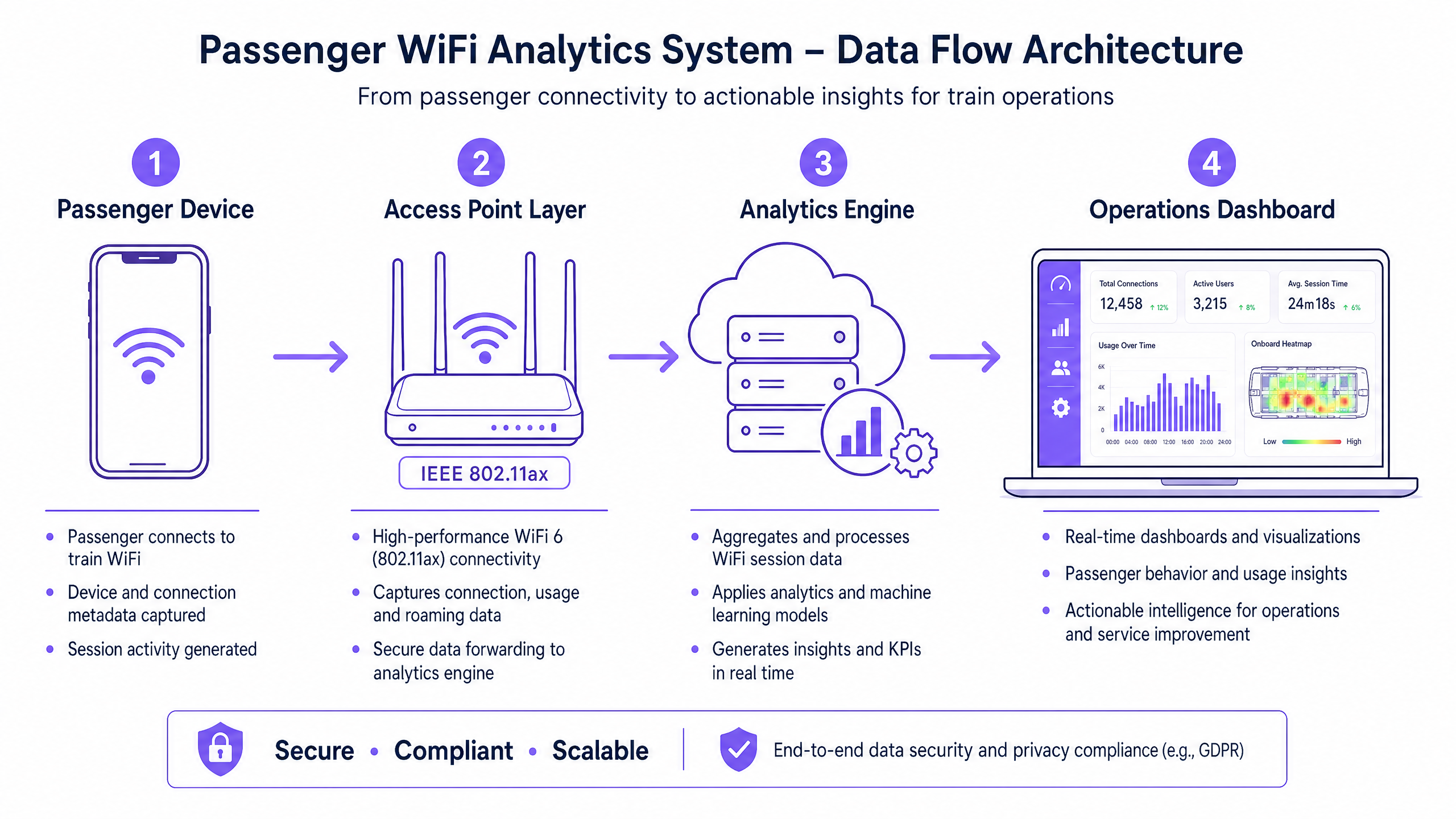
La base de toute capacité d'analyse WiFi passager est la capacité du réseau à capturer et traiter les métadonnées des appareils en toute sécurité. L'architecture se compose généralement de quatre couches principales :
- Couche de Point d'Accès (Edge) : Matériel physique déployé dans les gares et le matériel roulant. Les déploiements modernes utilisant IEEE 802.11ax (WiFi 6) offrent un support client haute densité et capturent des métadonnées essentielles, y compris les adresses MAC, la force du signal (RSSI) et les horodatages de connexion.
- Couche de Collecte de Données (Contrôleur) : Un contrôleur centralisé géré dans le cloud agrège les journaux de session bruts et les transferts d'itinérance de la couche de point d'accès.
- Moteur d'Analyse : Des plateformes comme la couche WiFi Analytics de Purple traitent les journaux bruts, appliquant des modèles d'apprentissage automatique pour filtrer les appareils du personnel et les signaux transitoires, transformant les données brutes en métriques significatives (par exemple, temps de présence, affluence).
- Tableau de Bord des Opérations : La couche de visualisation où les planificateurs de réseau et les gestionnaires de gare consomment les informations via des tableaux de bord et des cartes thermiques en temps réel.
Surmonter la Randomisation des Adresses MAC
Un défi technique critique dans l'analyse WiFi moderne est la randomisation des adresses MAC. Depuis iOS 14 et Android 10, les appareils randomisent leurs adresses MAC par réseau pour améliorer la confidentialité. Bien que cela n'ait pas d'impact sur l'affluence agrégée ou les métriques de temps de présence (car la session reste cohérente pendant une seule visite), cela limite la capacité à suivre anonymement les visiteurs récurrents au fil du temps.
La solution architecturale est le Guest WiFi authentifié. En acheminant les utilisateurs via un Captive Portal qui nécessite une authentification (par exemple, e-mail ou connexion sociale), le système crée un profil utilisateur persistant et consenti. Ce profil ancre les données de session à un utilisateur connu, contournant les limitations de la randomisation des adresses MAC tout en maintenant une conformité stricte avec les réglementations de protection des données.
Guide d'Implémentation : De l'Infrastructure aux Insights
Le déploiement de l'analyse WiFi passager nécessite une approche structurée pour garantir la précision des données et la sécurité du réseau.
- Mener des Audits RF Complets : La précision de l'analyse dépend entièrement de la couverture réseau. Les zones mortes dans les halls de gare ou sur les quais entraînent des sessions interrompues et des données de trajet fragmentées. Effectuez des études de site RF approfondies pour assurer une couverture continue dans toutes les zones passagers.
- Standardiser l'Intégration des Données : Les réseaux de transport comportent souvent du matériel hétérogène (par exemple, Cisco Meraki dans les gares, différents fournisseurs sur le matériel roulant). Implémentez une couche API agnostique vis-à-vis des fournisseurs pour normaliser les journaux de session avant qu'ils n'atteignent le moteur d'analyse.
- Mettre en Œuvre des Contrôles de Sécurité Robustes : Les réseaux destinés aux passagers sont des surfaces d'attaque à haut risque. Appliquez WPA3 lorsque la compatibilité client le permet, mettez en œuvre une isolation client stricte (isolation de couche 2) pour empêcher les mouvements latéraux entre les appareils des passagers, et déployez le filtrage DNS pour bloquer les domaines malveillants. Pour en savoir plus sur la sécurisation de ces environnements, consultez notre guide Protégez Votre Réseau avec un DNS et une Sécurité Robustes .
- Définir l'Architecture Zonale : Segmentez vos emplacements physiques en zones logiques (par exemple, hall, zone commerciale, quai). Cela permet une analyse granulaire du temps de présence, permettant aux opérateurs de différencier un passager qui navigue dans une zone commerciale de celui qui attend sur un quai pendant un retard de service.
Bonnes Pratiques et Cas d'Utilisation Opérationnels
Les opérateurs de transport exploitent l'analyse WiFi pour améliorer l'efficacité dans plusieurs domaines opérationnels. De la même manière que les sites de Retail et d' Hospitality utilisent les données d'affluence pour optimiser la dotation en personnel, les opérateurs de transport utilisent ces informations pour gérer la demande de pointe.
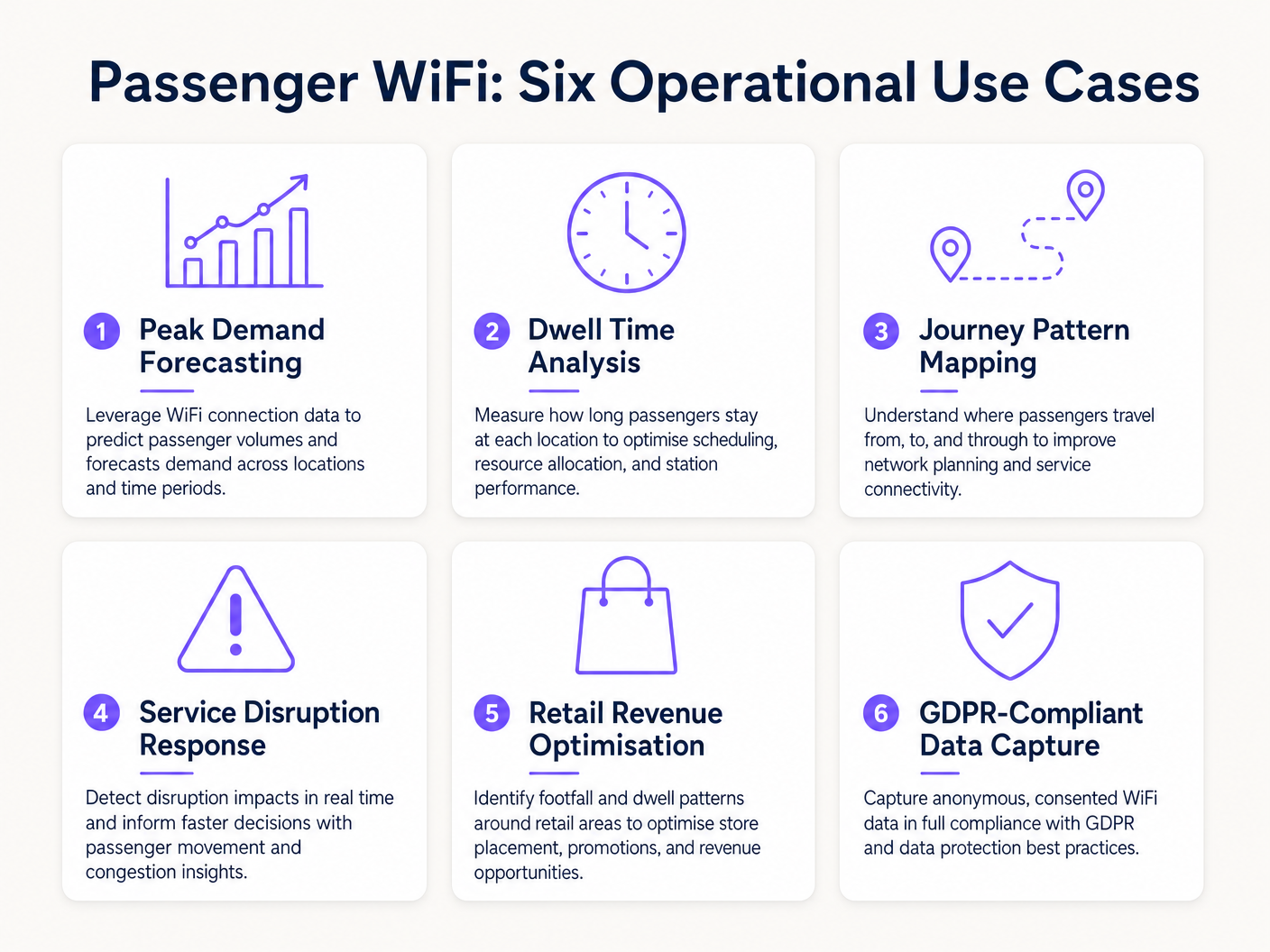
Étude de Cas Réelle : Réseau Ferroviaire Interurbain
Un important opérateur ferroviaire interurbain du Royaume-Uni a déployé l'analyse WiFi dans douze gares terminus pour résoudre les problèmes de congestion des quais. En corrélant les pics de connexion WiFi avec les heures de départ des trains, l'équipe des opérations a identifié que des quais spécifiques connaissaient un surpeuplement dangereux 40 minutes avant le départ.re. Les données ont révélé que les passagers arrivaient plus tôt que prévu en raison d'une signalisation numérique peu claire dans le hall principal. En ajustant le calendrier des annonces de quai sur les panneaux de départ, l'opérateur a fluidifié le flux de passagers, réduisant la densité de pointe sur les quais de 22 % et améliorant la sécurité globale.
Étude de cas réelle : Opérations de terminal de ferry
Un opérateur de ferry régional gérant un trafic estival à fort volume a utilisé l'analyse du temps de présence WiFi pour optimiser sa stratégie de vente au détail dans le terminal. Le tableau de bord analytique a mis en évidence que les passagers attendant des traversées retardées avaient un temps de présence moyen de 45 minutes dans le terminal, mais que seulement 12 % d'entre eux entraient dans la zone de vente secondaire. En repositionnant la signalisation numérique et en déclenchant des notifications push automatisées via le captive portal offrant une réduction sur le café pendant les retards, l'opérateur a augmenté la conversion des ventes de 18 % lors des événements perturbateurs.
Dépannage et atténuation des risques
Lors de la mise en œuvre de l'analyse WiFi des passagers, les équipes IT doivent atténuer plusieurs modes de défaillance courants :
- Dilution des données par les appareils du personnel : L'incapacité à filtrer les appareils du personnel (par exemple, équipes de nettoyage, personnel de vente au détail) fausse considérablement les métriques de temps de présence. Mettez en œuvre un filtrage strict des adresses MAC ou des SSIDs dédiés pour le personnel afin de garantir la propreté des données des passagers.
- Non-conformité : La capture de données d'appareils sans consentement explicite ou base légale documentée viole le GDPR. Assurez-vous que votre captive portal articule clairement la politique de traitement des données et recueille le consentement explicite si nécessaire.
- Goulots d'étranglement du backhaul : Les systèmes embarqués s'appuyant sur le backhaul cellulaire (LTE/5G) souffrent souvent de contraintes de bande passante. Assurez-vous que votre architecture met en mémoire tampon les données analytiques localement pendant les pertes de connectivité et les synchronise de manière asynchrone pour éviter la perte de données sans impacter les vitesses de navigation des passagers.
ROI et impact commercial
Le retour sur investissement de l'analyse WiFi des passagers s'étend bien au-delà du service IT. En traitant le réseau comme un atout d'intelligence, les opérateurs peuvent :
- Optimiser l'allocation des ressources : Alignez le personnel de la gare, les horaires de nettoyage et les patrouilles de sécurité avec des données empiriques de fréquentation plutôt qu'avec des horaires statiques.
- Augmenter les revenus du commerce de détail : Fournissez aux locataires commerciaux des métriques précises de fréquentation et de conversion, justifiant des taux de location premium dans les zones à fort trafic.
- Améliorer l'expérience des passagers : Identifiez les points de friction dans le parcours en gare et gérez de manière proactive les foules, un peu comme le secteur de la Santé utilise une technologie similaire pour comprendre le flux de patients. Pour le contexte des applications intersectorielles, consultez Comment le WiFi peut améliorer l'expérience des patients dans les hôpitaux .
En intégrant l'analyse WiFi dans la stratégie opérationnelle principale, les opérateurs de transport du secteur des Transports peuvent passer d'une gestion réactive à une prestation de services proactive et basée sur les données.
Termes clés et définitions
MAC Address Randomisation
A privacy feature in modern operating systems (iOS, Android) that generates a temporary, random MAC address for each WiFi network the device connects to.
IT teams must account for this as it prevents the tracking of repeat visitors using only hardware identifiers, necessitating captive portal authentication.
Dwell Time
The total duration a device remains connected or visible to the WiFi network within a specific physical zone.
Used by operations directors to measure how long passengers wait on platforms or spend in retail areas, directly impacting commercial and safety planning.
Captive Portal
A web page that users must view and interact with before being granted access to a public WiFi network.
The primary mechanism for capturing user consent, enforcing terms of service, and collecting first-party marketing data.
IEEE 802.11ax (WiFi 6)
The current standard for wireless networks, designed to improve performance in high-density environments.
Essential for transport hubs like stadiums and train stations where thousands of devices attempt to connect simultaneously.
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal.
Analytics engines use RSSI values from multiple access points to triangulate a device's physical location within a venue.
Client Isolation
A security feature that prevents devices connected to the same WiFi network from communicating directly with each other.
Critical for public passenger WiFi to prevent malicious actors from scanning or attacking other users' devices on the network.
Footfall
The total number of unique devices detected by the WiFi network within a specific timeframe.
Provides station managers with an accurate proxy for total passenger volume, independent of ticket sales.
Cellular Backhaul
The use of cellular networks (LTE/5G) to connect a local WiFi network (like on a bus or train) back to the internet.
The primary ongoing operational cost (OPEX) for onboard WiFi deployments, requiring careful bandwidth management.
Études de cas
A major train station operator is experiencing severe congestion on Platform 4 during the evening peak. They need to understand where these passengers are originating from within the station (e.g., main concourse vs. retail zone) to improve flow.
- Deploy high-density IEEE 802.11ax access points across the concourse, retail zones, and Platform 4 to ensure contiguous coverage.
- Configure the analytics platform to define logical 'Zones' for each area.
- Analyse the 'Zone-to-Zone Transition' reports in the analytics dashboard during the 16:00-19:00 window.
- Identify the primary origin zones for devices arriving at Platform 4.
- If the data shows a bottleneck originating from the retail zone corridor, operations can deploy staff to redirect flow or update digital signage to route passengers through a secondary concourse entrance.
A regional bus operator wants to offer free onboard WiFi but needs to justify the cellular backhaul costs to the commercial director by capturing marketing data.
- Implement a cloud-managed captive portal for the onboard WiFi network.
- Configure the portal to require authentication via email or social login (e.g., Facebook, Google).
- Ensure the portal includes a clear, GDPR-compliant privacy notice and opt-in checkboxes for marketing communications.
- Integrate the captive portal data capture directly with the operator's CRM or email marketing platform via API.
- Track the volume of new marketing opt-ins generated per route and calculate the equivalent cost-per-acquisition (CPA) to justify the backhaul OPEX.
Analyse de scénario
Q1. Your ferry terminal has deployed WiFi analytics, but the average dwell time in the main waiting lounge is reporting as 8.5 hours, which is impossible given your sailing schedule. What is the most likely cause and how do you fix it?
💡 Astuce :Consider what other devices might be permanently located in or near the waiting lounge.
Afficher l'approche recommandée
The analytics engine is likely capturing static devices (e.g., smart TVs, digital signage, point-of-sale systems) or staff devices that remain in the lounge all day. The solution is to identify the MAC addresses of these known devices and configure the analytics platform to filter them out of the dataset.
Q2. A bus operator wants to track how many passengers travel the full length of a specific route versus hopping off early. They are relying purely on anonymous MAC address tracking from the onboard access point. Why might this data be inaccurate?
💡 Astuce :Think about how modern smartphones handle network connections to protect privacy.
Afficher l'approche recommandée
Modern smartphones use MAC address randomisation. While connected to the bus WiFi, the session is tracked accurately. However, if a device disconnects (e.g., goes to sleep) and reconnects later on the route, it may present a new MAC address, making it appear as a new passenger rather than a continuing journey. Implementing a captive portal for authentication is required to track persistent journeys accurately.
Q3. You are deploying WiFi across a large train station with a high-density concourse. To ensure secure data capture and protect passengers, what two critical network security configurations must be enabled on the public SSID?
💡 Astuce :One prevents devices from talking to each other; the other prevents access to malicious sites.
Afficher l'approche recommandée
- Client Isolation (Layer 2 isolation) must be enabled to prevent passenger devices from communicating with or attacking each other on the local network. 2. DNS Filtering should be deployed to block access to known malicious domains, phishing sites, and inappropriate content.



