BYOD WiFi Security: How to Safely Allow Personal Devices onto Your Network
A pragmatic, vendor-neutral guide for IT leaders on securing BYOD WiFi access. It covers implementing 802.1X authentication, MDM integration, and strict network segmentation to protect corporate assets while enabling personal devices.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- The 802.1X Standard and EAP Protocols
- Network Segmentation and VLANs
- Mobile Device Management (MDM) Integration
- Implementation Guide: Step-by-Step Deployment
- Phase 1: Infrastructure Preparation
- Phase 2: Certificate Authority and MDM Setup
- Phase 3: The Onboarding Experience
- Best Practices and Industry Standards
- Troubleshooting & Risk Mitigation
- Certificate Expiration
- Android MAC Randomisation
- Rogue Access Points
- ROI & Business Impact

Executive Summary
As the perimeter of the corporate network continues to dissolve, managing BYOD (Bring Your Own Device) WiFi access has shifted from a convenience feature to a critical security imperative. For IT managers and network architects operating across enterprise environments—from Hospitality and Retail to Healthcare and Transport —the challenge is clear: how to safely allow personal devices onto the network without exposing corporate assets to unacceptable risk.
This guide provides a pragmatic, vendor-neutral framework for deploying secure BYOD WiFi. We will bypass theoretical models to focus on actionable architecture: implementing 802.1X authentication, leveraging Mobile Device Management (MDM) for compliance, and enforcing strict network segmentation. By mapping these technical controls to business outcomes, IT leaders can deploy solutions that protect data integrity while maintaining operational efficiency. Whether you are upgrading legacy WPA2-PSK networks or designing a zero-trust architecture from the ground up, this reference details the precise configurations required to secure the modern enterprise edge.
Technical Deep-Dive: Architecture and Standards
The foundation of secure BYOD WiFi security rests on abandoning shared passwords in favour of identity-based access control.
The 802.1X Standard and EAP Protocols
The IEEE 802.1X standard is the non-negotiable baseline for enterprise WiFi security. It provides port-based Network Access Control (PNAC), ensuring that a device cannot communicate on the network until it has been explicitly authenticated.
For BYOD deployments, the Extensible Authentication Protocol (EAP) method chosen is critical. While EAP-PEAP (Protected EAP) using username and password provides a baseline, EAP-TLS (Transport Layer Security) is the gold standard. EAP-TLS relies on client-side certificates, eliminating the risk of credential theft and man-in-the-middle attacks. When a user's personal smartphone attempts to connect, the RADIUS server validates the unique certificate installed on that device, ensuring both the user's identity and the device's authorization status.
Network Segmentation and VLANs
A flat network is a compromised network. BYOD devices must never share a subnet with corporate servers, point-of-sale systems, or critical infrastructure.
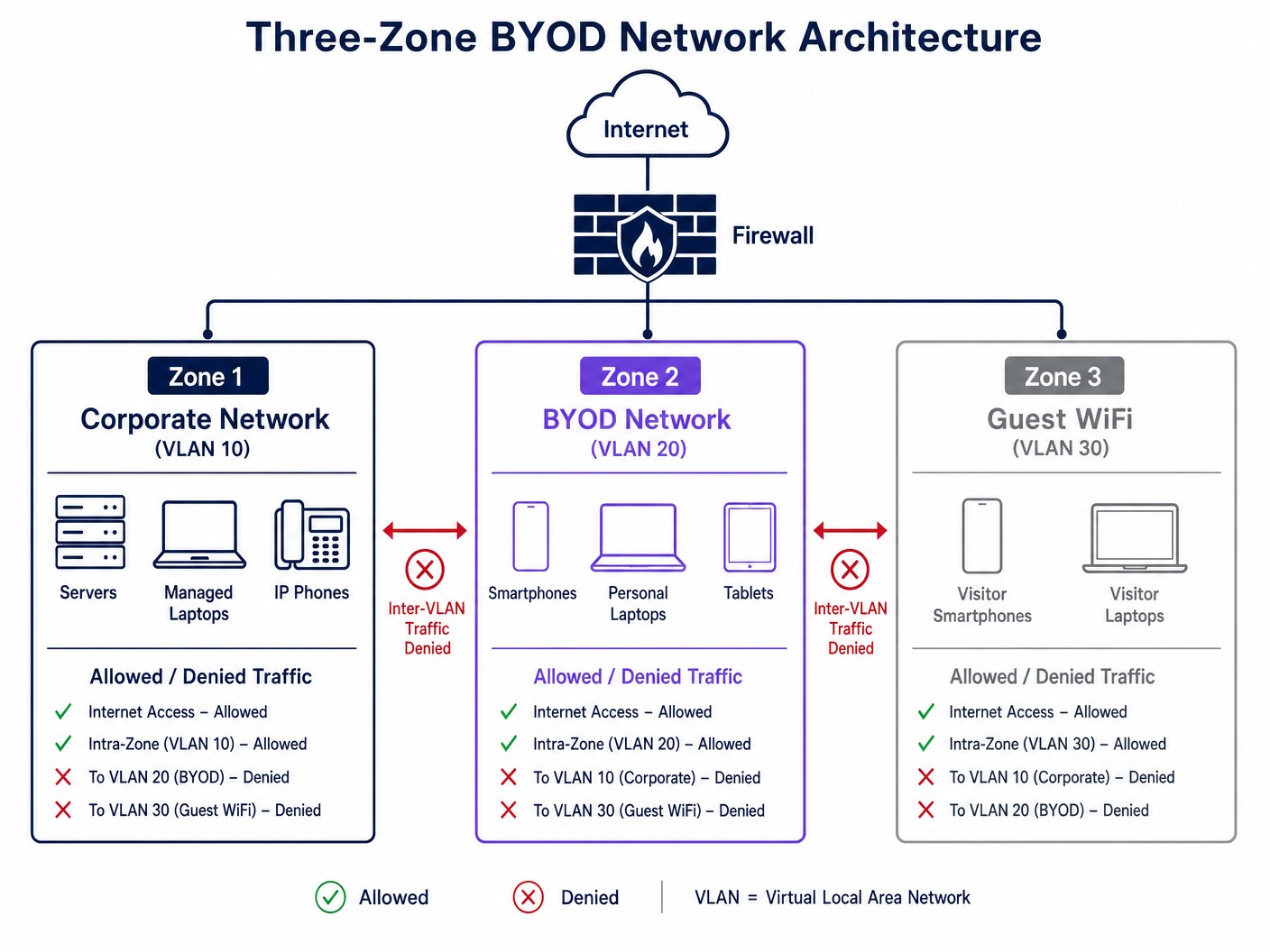
Implementing a strict Three-Zone Architecture is required:
- Corporate Zone (VLAN 10): Managed, company-owned devices with full access to internal resources.
- BYOD Zone (VLAN 20): Employee-owned devices. This zone should have internet access and restricted, heavily monitored access to specific internal applications (e.g., via a reverse proxy or internal VPN).
- Guest Zone (VLAN 30): Visitor devices. Internet access only. Client isolation must be enabled to prevent peer-to-peer communication.
Mobile Device Management (MDM) Integration
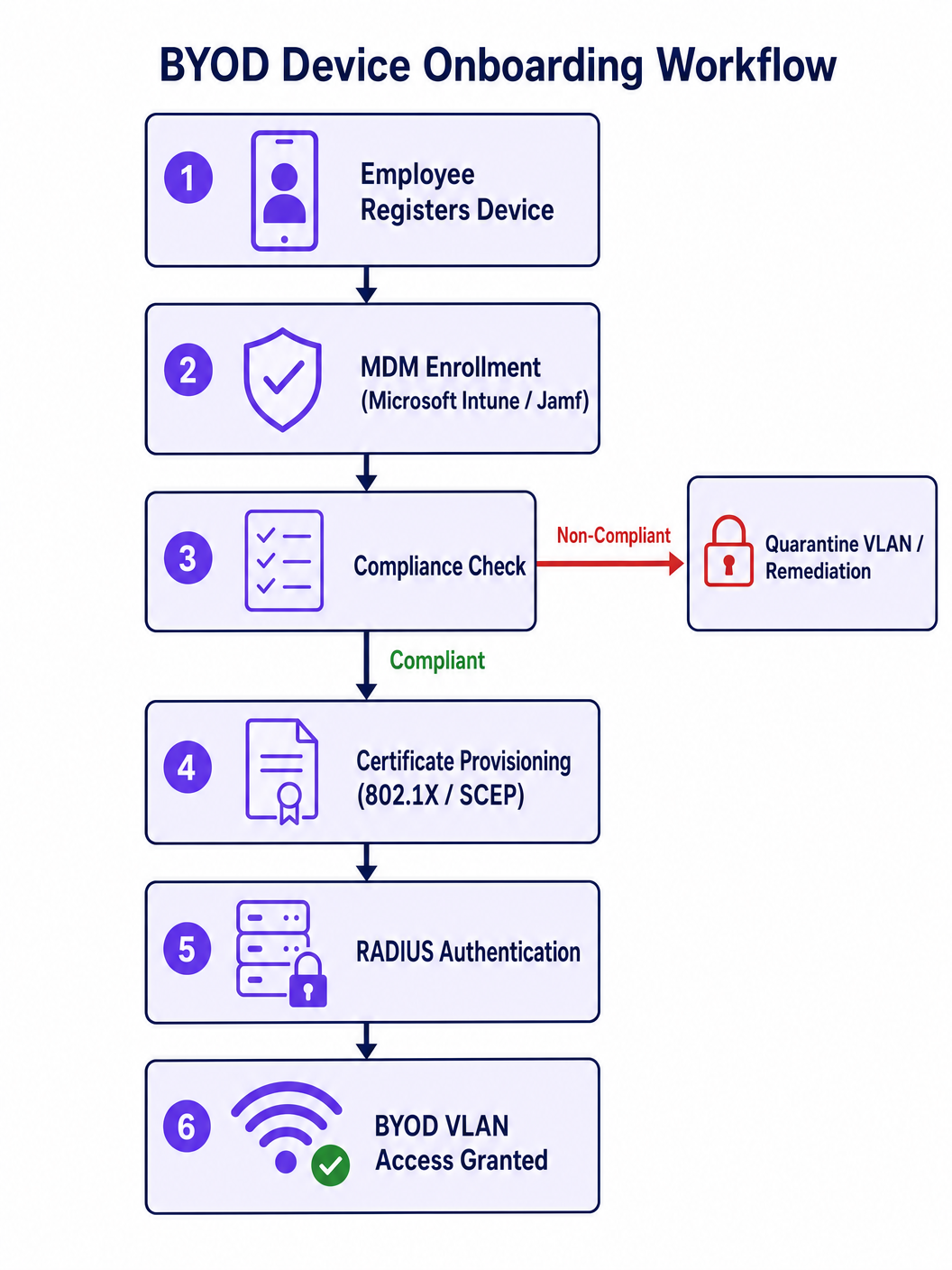
To enforce compliance on personal devices, MDM integration is essential. Solutions like Microsoft Intune or Jamf allow IT to enforce baseline security postures—such as minimum OS versions, active screen locks, and un-rooted status—before issuing the EAP-TLS certificate required for network access. If a device falls out of compliance, the MDM revokes the certificate, immediately terminating WiFi access.
Implementation Guide: Step-by-Step Deployment
Deploying a secure BYOD architecture requires careful orchestration between the wireless LAN controller (WLC), the identity provider (IdP), and the MDM platform.
Phase 1: Infrastructure Preparation
- Configure VLANs: Establish the distinct VLANs on your core switches and propagate them to the access points. Ensure inter-VLAN routing is denied by default at the firewall.
- Deploy RADIUS: Implement a RADIUS server (e.g., Cisco ISE, Aruba ClearPass, or cloud RADIUS) integrated with your corporate directory (Active Directory, Entra ID).
Phase 2: Certificate Authority and MDM Setup
- Establish a PKI: Set up a Certificate Authority (CA) to issue client certificates.
- Configure SCEP/EST: Enable Simple Certificate Enrollment Protocol (SCEP) or Enrollment over Secure Transport (EST) to automate certificate delivery to devices.
- Define MDM Policies: In your MDM, create a compliance policy that checks for device health. Create a WiFi profile payload that pushes the EAP-TLS configuration and the SCEP URL to compliant devices.
Phase 3: The Onboarding Experience
The onboarding process must be seamless to prevent helpdesk overload.
- Provisioning SSID: Broadcast an open or WPA3-SAE provisioning SSID.
- Captive Portal Redirection: When users connect, redirect them to a captive portal. Here, Purple's Guest WiFi platform can serve as the initial touchpoint, guiding users to download the MDM profile.
- Automated Transition: Once the MDM profile is installed and the certificate is provisioned, the device automatically disconnects from the provisioning SSID and connects to the secure 802.1X BYOD SSID.
Best Practices and Industry Standards
To maintain a robust security posture, adhere to the following best practices:
- Enforce Client Isolation: On both Guest and BYOD VLANs, enable client isolation at the access point level. This prevents lateral movement if a personal device is compromised.
- Implement WPA3-Enterprise: Transition from WPA2 to WPA3-Enterprise to benefit from mandatory Protected Management Frames (PMF) and enhanced cryptographic suites.
- Utilise OpenRoaming: For seamless, secure connectivity across venues, consider implementing OpenRoaming. Purple acts as a free identity provider for OpenRoaming under the Connect license, simplifying secure access without manual onboarding.
- Continuous Monitoring: Utilise WiFi Analytics to monitor traffic patterns. Unusual bandwidth consumption or connection attempts from the BYOD subnet should trigger automated alerts.
- Compliance Alignment: Ensure your BYOD policies align with relevant regulations. For example, in healthcare, segregating BYOD traffic is crucial for HIPAA compliance, as detailed in WiFi in Hospitals: A Guide to Secure Clinical Networks .
Troubleshooting & Risk Mitigation
Even with a robust architecture, issues will arise. Here are common failure modes and mitigation strategies:
Certificate Expiration
Risk: Devices suddenly lose connectivity when their client certificates expire. Mitigation: Configure the MDM to automatically renew certificates 30 days before expiration via SCEP. Implement monitoring on the CA to alert IT of impending expirations.
Android MAC Randomisation
Risk: Modern iOS and Android devices randomise their MAC addresses by default, which can break MAC-based access controls or captive portal bypass rules. Mitigation: Rely entirely on 802.1X identity (the certificate) rather than the MAC address for authentication and policy enforcement.
Rogue Access Points
Risk: Employees may plug in personal routers to bypass restrictions, creating rogue access points. Mitigation: Enable Rogue AP detection on your enterprise WLC (e.g., when managing a Wireless Access Point Ruckus deployment) and configure switch ports to disable upon detecting multiple MAC addresses (Port Security).
ROI & Business Impact
Securing BYOD WiFi is not merely a cost centre; it delivers measurable business value:
- Reduced Helpdesk Overhead: Automating certificate provisioning via MDM reduces password reset tickets and manual onboarding requests by up to 80%.
- Risk Mitigation: Strict segmentation and compliance checks drastically reduce the probability of a costly data breach originating from a compromised personal device.
- Enhanced Productivity: Employees gain seamless, secure access to necessary resources on their preferred devices, improving overall efficiency.
- Data-Driven Insights: By routing BYOD and guest traffic through an analytics platform, venues can gather actionable intelligence on space utilisation and dwell times.
For a broader perspective on how personal devices integrate into wider network ecosystems, refer to our guide on Personal Area Networks (PANs): Technologies, Applications, Security, and Future Trends .
Key Terms & Definitions
802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol that prevents unauthorized devices from passing traffic on the enterprise network.
EAP-TLS
Extensible Authentication Protocol-Transport Layer Security. An authentication method that uses public key infrastructure (PKI) and client-side certificates.
The gold standard for BYOD authentication, eliminating the need for passwords and protecting against credential theft.
MDM (Mobile Device Management)
Software that allows IT administrators to control, secure, and enforce policies on smartphones, tablets, and laptops.
Used to verify device health (compliance) before issuing the certificate required to join the BYOD WiFi.
Network Segmentation
The practice of dividing a computer network into multiple subnets or VLANs to improve performance and security.
Crucial for ensuring that compromised personal devices cannot access corporate servers or point-of-sale systems.
Client Isolation
A wireless network security feature that prevents devices connected to the same AP from communicating directly with each other.
Must be enabled on Guest and BYOD networks to prevent peer-to-peer malware spread or lateral movement.
SCEP (Simple Certificate Enrollment Protocol)
A protocol designed to make the issuing and revocation of digital certificates as scalable as possible.
Used by the MDM to silently and automatically push EAP-TLS certificates to compliant BYOD devices.
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The server that checks the device's certificate against the directory and tells the WLC whether to allow the connection.
WPA3-Enterprise
The latest generation of WiFi security, offering enhanced cryptographic strength and mandatory Protected Management Frames (PMF).
The recommended security standard for modern BYOD deployments to prevent deauthentication attacks.
Case Studies
A 200-room hotel needs to allow staff to use personal smartphones to access a cloud-based housekeeping app, but must ensure these devices cannot access the property management system (PMS) or the guest WiFi network.
- Configure a dedicated BYOD VLAN (e.g., VLAN 20) on the core switch and WLC.
- Create an 802.1X SSID (e.g., 'Staff-BYOD') mapped to VLAN 20.
- Integrate an MDM (e.g., Intune) to push EAP-TLS certificates only to devices that meet minimum security baselines.
- Configure firewall rules at the edge: Allow outbound internet access for VLAN 20 to reach the cloud housekeeping app. Explicitly deny routing from VLAN 20 to the Corporate VLAN (where the PMS resides) and the Guest VLAN.
A large retail chain is experiencing high helpdesk call volumes because employee BYOD certificates are expiring, locking staff out of the inventory network.
- Audit the MDM and Certificate Authority (CA) integration.
- Configure the MDM policy to utilize SCEP (Simple Certificate Enrollment Protocol) for automated certificate renewal.
- Set the renewal threshold to trigger 30 days prior to the certificate expiration date.
- Implement an alert system on the CA to notify the IT operations team if a batch of renewals fails.
Scenario Analysis
Q1. A hospital IT director wants to allow visiting doctors to use their personal iPads to view non-sensitive schedules. The director proposes putting these iPads on the existing Corporate VLAN to simplify routing. What is the primary risk, and what is the correct architectural approach?
💡 Hint:Consider the principle of least privilege and the impact of a compromised personal device on clinical systems.
Show Recommended Approach
The primary risk is lateral movement; if a visiting doctor's iPad is infected with malware, placing it on the Corporate VLAN exposes critical clinical systems and electronic health records (EHR) to potential compromise. The correct approach is to implement a dedicated BYOD or Partner VLAN with strict firewall rules that only permit outbound access to the specific scheduling application, explicitly denying routing to the Corporate VLAN.
Q2. Your network currently uses MAC Address Authentication Bypass (MAB) to allow executive personal devices onto a privileged WiFi network. Executives are complaining that they have to re-register their new iPhones frequently. Why is this happening, and how should you redesign the authentication mechanism?
💡 Hint:Think about modern mobile OS privacy features regarding hardware identifiers.
Show Recommended Approach
This is happening because modern iOS (and Android) devices use MAC randomization by default to protect user privacy, meaning the MAC address changes, breaking the MAB rules. To fix this, you must abandon MAC-based authentication and implement 802.1X with EAP-TLS. By deploying an MDM to push unique client certificates to the executives' devices, authentication becomes tied to cryptographic identity rather than a volatile hardware identifier.
Q3. During a BYOD rollout, you decide to use EAP-PEAP (username and password) instead of EAP-TLS to save time on setting up a Certificate Authority. What specific security vulnerability does this introduce?
💡 Hint:Consider how devices verify the network they are connecting to and how credentials are transmitted.
Show Recommended Approach
Using EAP-PEAP introduces the risk of credential theft via Man-in-the-Middle (MitM) attacks or rogue access points. If a device is not configured to strictly validate the server certificate (which is common on unmanaged BYOD devices), an attacker can broadcast a spoofed SSID, intercept the PEAP handshake, and capture the user's corporate credentials. EAP-TLS mitigates this entirely by requiring mutual certificate authentication.



