How to Set Up WiFi for Your Business: A Complete Guide
This guide provides a comprehensive, vendor-neutral blueprint for deploying enterprise-grade WiFi, covering network segmentation, hardware selection, and security protocols from WPA3 to 802.1X. It details how IT leaders across retail, hospitality, and public sector can transform wireless infrastructure from a cost centre into a strategic asset by leveraging captive portals and analytics for first-party data capture, compliance, and measurable ROI.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Network Topology and Segmentation
- Hardware Selection and RF Planning
- Implementation Guide
- Step 1: Core Infrastructure Configuration
- Step 2: Access Point Deployment and Provisioning
- Step 3: Corporate Network Authentication
- Step 4: Guest Network and Captive Portal Setup
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
Deploying enterprise-grade WiFi is no longer a peripheral IT task; it is a core business requirement that directly impacts operational efficiency, customer satisfaction, and revenue generation. For IT managers, network architects, and CTOs across retail, hospitality, healthcare, and public sectors, a robust wireless infrastructure forms the foundation of digital transformation. This guide provides a comprehensive, vendor-neutral blueprint for setting up WiFi for business environments. We will explore the critical stages of deployment — from initial site surveys and hardware selection to advanced configuration of corporate and guest networks.
Beyond mere connectivity, modern WiFi deployments must be secure, compliant, and capable of delivering actionable business intelligence. We will examine the implementation of WPA3-Enterprise for corporate networks, the necessity of isolated VLANs, and the strategic deployment of captive portals. Furthermore, this guide will demonstrate how integrating platforms like Purple's Guest WiFi and WiFi Analytics transforms a cost centre into a strategic asset, enabling venues to capture first-party data, ensure GDPR compliance, and drive measurable ROI.
Technical Deep-Dive
The architecture of a business WiFi network fundamentally differs from consumer-grade setups. It requires a layered approach to security, scalability, and performance management. At the core, the infrastructure must support high client density, seamless roaming, and granular access controls.
Network Topology and Segmentation
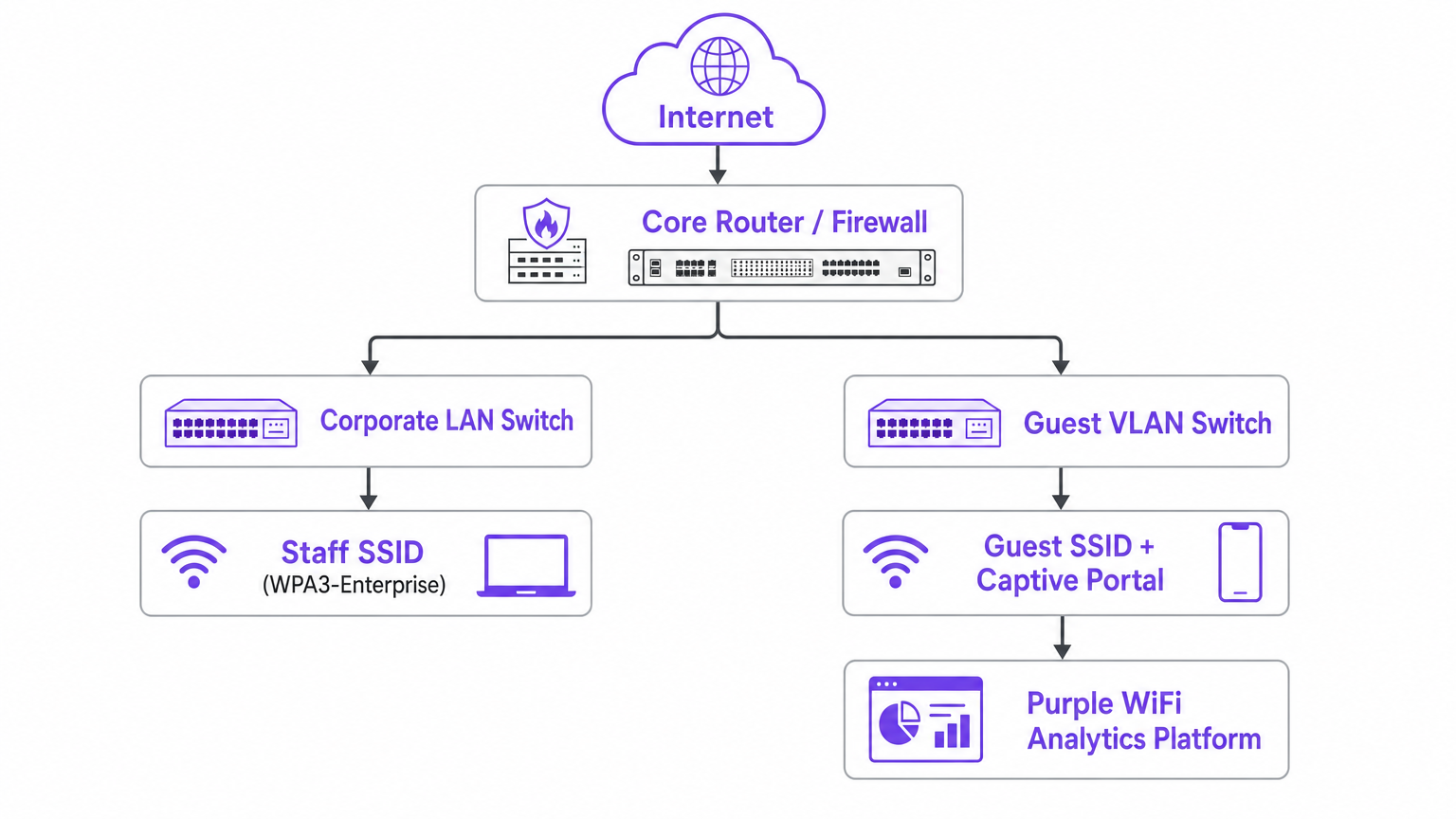
A flat network is a significant security risk in an enterprise environment. Proper network design necessitates the logical separation of traffic using Virtual Local Area Networks (VLANs). The table below outlines the three core segments required in any commercial deployment.
| Network Segment | Primary Users | Security Standard | Key Requirement |
|---|---|---|---|
| Corporate / Staff | Employees, POS systems | WPA3-Enterprise + 802.1X | RADIUS authentication, no guest access |
| Guest | Customers, visitors | Captive portal + Client Isolation | GDPR consent capture, internet-only access |
| IoT / Facilities | Smart devices, cameras | Isolated VLAN | Strict firewall rules, no corporate access |
Corporate/Staff Network: This segment handles sensitive internal data, point-of-sale (POS) systems, and back-office operations. It must be secured using IEEE 802.1X authentication, typically leveraging a RADIUS server to authenticate users against a central directory (e.g., Active Directory or LDAP). This ensures that only authorised personnel and devices can access critical resources.
Guest Network: The guest network provides internet access to visitors, customers, and contractors. It must be strictly isolated from the corporate network. Client isolation (also known as AP isolation) should be enabled to prevent devices on the guest network from communicating with each other, mitigating the risk of lateral movement by malicious actors.
IoT/Facilities Network: A separate VLAN should be dedicated to Internet of Things (IoT) devices, such as smart thermostats, security cameras, and environmental sensors. These devices often have weaker security postures and should be isolated from both corporate and guest traffic.
Hardware Selection and RF Planning
Selecting the appropriate hardware is critical for meeting throughput and coverage requirements. Access Points (APs) should be chosen based on the specific environmental challenges and expected client density.
Wireless standards should be standardised on WiFi 6 (802.11ax) or WiFi 6E to ensure sufficient capacity and performance in dense environments. These standards introduce technologies like OFDMA and MU-MIMO, which significantly improve spectral efficiency when compared to legacy 802.11ac deployments. Antenna design also plays a critical role: omnidirectional antennas are suitable for general coverage in open areas, while directional antennas are necessary for high-density deployments (e.g., stadiums, auditoriums) or to provide coverage in challenging RF environments like warehouses.
A predictive site survey using specialised software is a mandatory first step, followed by an active on-site survey. This process determines the optimal placement of APs, identifies potential sources of interference (e.g., metal structures, radar), and ensures adequate signal strength (RSSI) and Signal-to-Noise Ratio (SNR) across the venue. A minimum RSSI of -67 dBm is typically targeted for reliable enterprise voice and data services.
Implementation Guide
Deploying a business WiFi network requires a systematic approach to ensure security, reliability, and a seamless user experience.
Step 1: Core Infrastructure Configuration
Begin by configuring the core routing and switching infrastructure. Establish the necessary VLANs and configure the firewall rules to enforce traffic separation. Ensure that Power over Ethernet (PoE) switches are adequately provisioned to power the APs, considering the power requirements of modern WiFi 6/6E hardware (often requiring PoE+ or PoE++).
Step 2: Access Point Deployment and Provisioning
Mount the APs according to the site survey design. In environments like Retail or Hospitality , aesthetics may dictate placement, but RF performance must not be compromised. Provision the APs using a centralised cloud or on-premises controller. This allows for unified configuration management, firmware updates, and monitoring across all sites.
Step 3: Corporate Network Authentication
Implement 802.1X authentication for the corporate SSID. Configure the RADIUS server and establish the necessary certificate infrastructure (PKI) for secure EAP methods (e.g., EAP-TLS or PEAP). This ensures that each user or device is individually authenticated and that encryption keys are dynamically generated per session.
Step 4: Guest Network and Captive Portal Setup
The guest network is a critical touchpoint for customer engagement. Implement an open SSID and route all traffic through a captive portal. The captive portal serves multiple functions: authenticating and onboarding users via social media logins, email registration, or SMS; presenting Terms and Conditions and capturing explicit consent for data processing to ensure compliance with GDPR or CCPA; and collecting valuable first-party demographic and behavioural data.
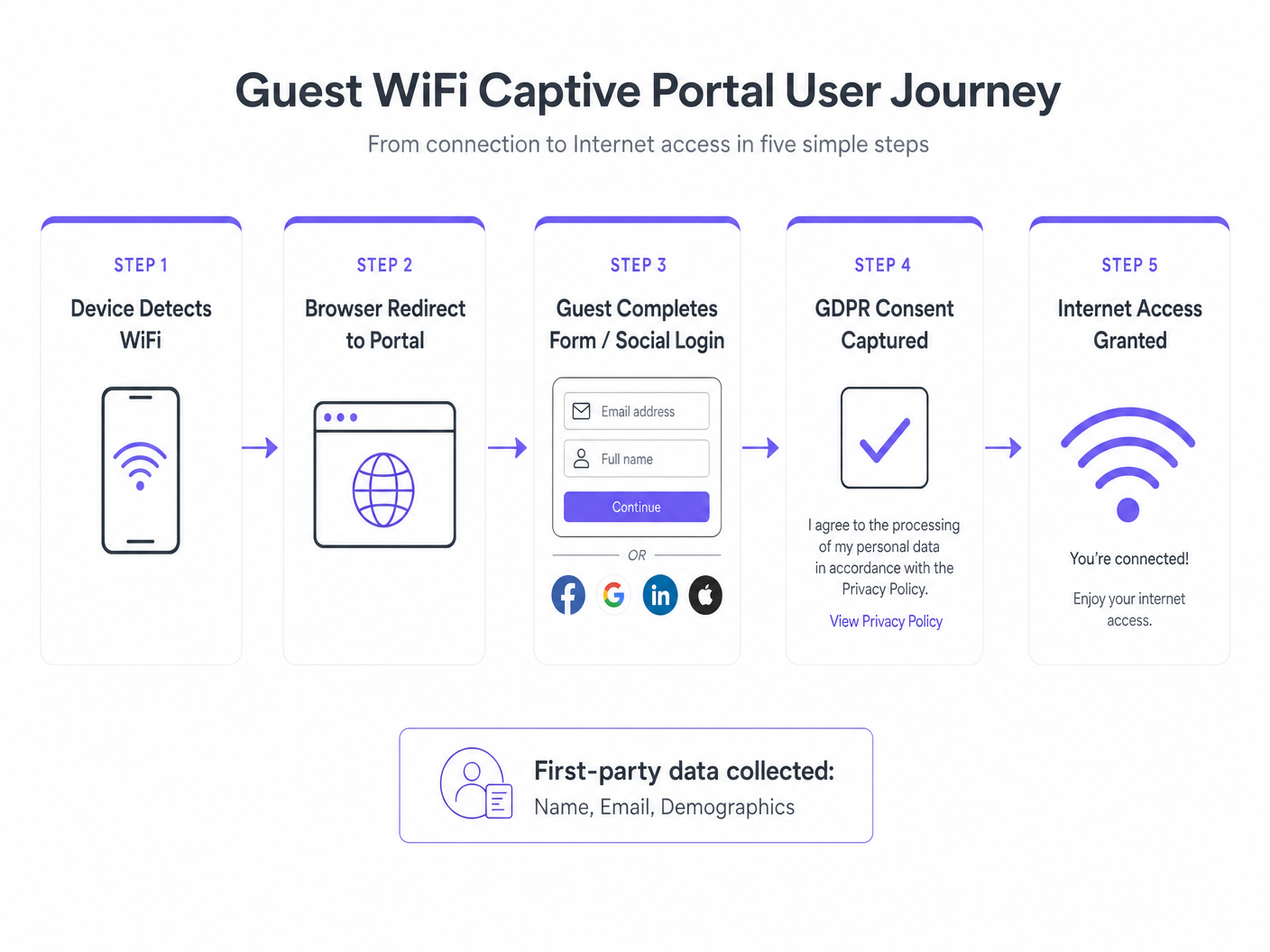
Integrating a platform like Purple streamlines this process, providing customisable splash pages, automated compliance management, and seamless integration with existing CRM systems. Furthermore, Purple acts as a free identity provider for services like OpenRoaming under the Connect licence, offering a seamless onboarding experience for users while maintaining robust security standards.
Best Practices
Adhering to industry standards and best practices is essential for maintaining a secure and performant network.
Implement WPA3: Where hardware supports it, mandate WPA3 for all new deployments. WPA3 provides stronger encryption and mitigates vulnerabilities associated with WPA2, such as dictionary attacks on pre-shared keys.
Enable Client Steering: Configure the network to actively steer clients to the 5 GHz or 6 GHz bands, alleviating congestion on the heavily utilised 2.4 GHz band. This is particularly important in high-density retail and hospitality environments.
Regular Security Audits: Conduct periodic penetration testing and vulnerability assessments to identify and remediate security weaknesses. This is particularly critical in environments subject to compliance frameworks like PCI DSS (e.g., retail or Healthcare environments).
Consider Location Services: In complex venues, consider implementing location-based services to enhance the visitor experience. Refer to our Indoor Positioning System: UWB, BLE, & WiFi Guide for advanced use cases like asset tracking and wayfinding in large venues.
Troubleshooting & Risk Mitigation
Even the most well-designed networks will encounter issues. A proactive approach to monitoring and troubleshooting is essential.
Co-Channel Interference (CCI): In dense deployments, APs operating on the same channel can interfere with each other, degrading performance. Utilise dynamic channel assignment (DCA) features within the wireless controller to optimise channel allocation and minimise CCI. This is a common issue in multi-floor office buildings and shopping centres.
Rogue AP Detection: Implement Wireless Intrusion Prevention Systems (WIPS) to detect and mitigate rogue access points — unauthorised devices connected to the corporate network that can bypass security controls and expose sensitive data.
Captive Portal Availability: Ensure the captive portal infrastructure is highly available. A failure here prevents guest access and disrupts data collection. Monitor the portal's uptime and response times closely, and consider redundant hosting configurations for mission-critical deployments.
Specialised Environments: Deploying WiFi in specific sectors presents unique challenges. Clinical environments require strict adherence to security and interference guidelines; see our guide on WiFi in Hospitals: A Guide to Secure Clinical Networks for detailed information. Similarly, Transport hubs have specific requirements; refer to Your Guide to Enterprise In Car Wi Fi Solutions for relevant insights.
ROI & Business Impact
The investment in enterprise WiFi must be justified by measurable business outcomes. Beyond providing connectivity, the network should function as a strategic asset that generates actionable intelligence.
By leveraging WiFi Analytics , businesses can gain deep insights into visitor behaviour. Key metrics include footfall and dwell time (understanding how many people visit the venue and how long they stay), return rates (measuring customer loyalty by tracking the frequency of return visits), and conversion rates (in retail environments, correlating WiFi engagement data with point-of-sale data to understand the impact on sales).
These insights enable data-driven decision-making, allowing businesses to optimise staffing levels, improve venue layouts, and deliver targeted marketing campaigns based on real-time location and demographic data. The network transitions from an IT overhead to a revenue-generating platform, delivering a compelling and measurable return on infrastructure investment.
Key Terms & Definitions
802.1X
An IEEE standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN. It requires a supplicant (client), authenticator (AP or switch), and authentication server (RADIUS).
Essential for securing corporate networks, ensuring only authenticated users and devices can access internal resources. Eliminates the risk of shared pre-shared key (PSK) compromise.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs, creating isolated broadcast domains at Layer 2 of the OSI model.
Used to segment traffic (e.g., separating guest traffic from corporate point-of-sale systems) to improve security and network performance. Mandatory in any multi-tenant or mixed-use wireless deployment.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before internet access is granted, typically implemented via DNS and HTTP redirection.
Crucial for guest networks to enforce terms of service, capture GDPR consent, and collect marketing data before providing internet access. Also the primary mechanism for first-party data acquisition.
Client Isolation (AP Isolation)
A security feature that prevents devices connected to the same Access Point or SSID from communicating directly with each other at Layer 2.
Mandatory on guest networks to prevent malicious actors from scanning or attacking other users' devices on the same public subnet. Should be enabled on all public-facing SSIDs without exception.
WPA3-Enterprise
The latest WiFi security protocol designed for enterprise networks, requiring a RADIUS server for individual user authentication and providing 192-bit minimum-strength security in its highest mode.
Replaces WPA2-Enterprise to provide robust encryption and protection against brute-force dictionary attacks on corporate SSIDs. Mandatory for any new enterprise deployment.
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal, expressed in dBm (decibels relative to one milliwatt). A higher (less negative) value indicates a stronger signal.
Used during site surveys to ensure adequate coverage. A minimum RSSI of -65 dBm to -67 dBm is typically targeted for reliable enterprise voice and data. Values below -75 dBm indicate poor coverage.
Client Steering (Band Steering)
A feature that encourages dual-band or tri-band capable clients to connect to the less congested 5 GHz or 6 GHz bands rather than the 2.4 GHz band, using techniques like probe response suppression.
Improves overall network capacity and performance in high-density environments by optimising spectrum utilisation. Critical in retail and hospitality deployments where 2.4 GHz congestion is common.
OpenRoaming
A Wireless Broadband Alliance (WBA) federation of WiFi networks that allows users to automatically and securely connect to participating networks without interacting with a captive portal, using identity federation standards.
Provides a seamless onboarding experience for users while maintaining enterprise-grade security. Purple acts as a free identity provider for OpenRoaming under the Connect licence, enabling venues to participate in the federation.
Co-Channel Interference (CCI)
Interference that occurs when two or more Access Points operate on the same radio frequency channel within range of each other, causing contention and degraded throughput.
A common cause of poor WiFi performance in dense deployments. Mitigated through careful channel planning, Dynamic Channel Assignment (DCA), and appropriate AP placement during the site survey phase.
Case Studies
A 200-room hotel needs to upgrade its legacy WiFi to support both corporate operations (PMS, POS) and high-density guest access in conference rooms, while ensuring GDPR compliance for guest data collection.
Deploy WiFi 6 APs following a rigorous predictive and active site survey, paying particular attention to RF propagation through concrete walls and elevator shafts. Implement three distinct VLANs: Corporate (secured via 802.1X/RADIUS with EAP-TLS), IoT (for smart TVs, thermostats, and door locks), and Guest. The Guest VLAN is routed through a Purple captive portal configured to handle social authentication via Facebook, Google, and email, present branded terms and conditions, capture explicit GDPR consent with a double opt-in mechanism, and collect first-party demographic data. Enable client steering to push conference room devices to the 5 GHz band, and configure per-AP transmit power to avoid co-channel interference between densely packed APs on each floor.
A national retail chain with 50 stores is experiencing poor WiFi performance on the shop floor, impacting staff using mobile inventory scanners and frustrating customers attempting to access the loyalty app. The existing infrastructure uses 802.11n APs with no centralised management.
Conduct an RF spectrum analysis across a representative sample of stores to identify interference sources (microwave ovens, competing SSIDs, Bluetooth devices). Replace legacy 802.11n hardware with WiFi 6 APs managed via a cloud controller. Implement aggressive client steering to push modern devices (both staff scanners and customer smartphones) to the 5 GHz and 6 GHz bands, alleviating congestion on the 2.4 GHz band. Configure Dynamic Channel Assignment (DCA) to mitigate Co-Channel Interference (CCI) between densely packed APs. Establish a dedicated IoT VLAN for inventory scanners and a separate guest VLAN with a Purple captive portal to capture loyalty programme sign-ups and drive CRM integration.
Scenario Analysis
Q1. A public sector organisation is deploying free WiFi across several municipal buildings. They want to ensure the network is secure but do not want the administrative overhead of managing individual user accounts for the public. What is the recommended approach, and what compliance obligations must be met?
💡 Hint:Consider the balance between accessibility for the public and the need for basic security controls, data capture, and legal compliance under GDPR.
Show Recommended Approach
Deploy an open SSID for the public network and mandate the use of a captive portal. Enable Client Isolation on the APs to protect users from each other. Use the captive portal to capture GDPR-compliant consent (explicit, informed, and freely given) and offer self-service authentication methods like SMS or social login, avoiding the need for manual account creation by IT staff. Ensure a clear Privacy Policy is linked from the splash page. The network should be on a dedicated Guest VLAN, isolated from all internal municipal systems.
Q2. During a site survey for a large warehouse, you notice significant signal attenuation caused by metal racking filled with dense liquid products. Omnidirectional antennas are failing to provide adequate coverage down the aisles. How should you adjust the deployment design?
💡 Hint:Think about how RF energy can be focused rather than broadcast in a 360-degree pattern, and consider the specific geometry of warehouse aisles.
Show Recommended Approach
Replace the omnidirectional APs with units utilising directional antennas (e.g., patch or sector antennas). Mount these at the ends of the aisles, pointing down the corridors. This focuses the RF energy where it is needed, mitigating the attenuation caused by the dense racking and improving the Signal-to-Noise Ratio (SNR) for devices operating within the aisles. Consider also deploying APs at mid-aisle positions on the racking itself for very long aisles, using lower transmit power to avoid co-channel interference.
Q3. A retail client wants to understand the conversion rate of customers who log into the guest WiFi versus those who simply walk into the store. What integration is necessary to achieve this, and what data privacy considerations apply?
💡 Hint:You need to correlate network identity data with transactional data, and this correlation involves personal data under GDPR.
Show Recommended Approach
Integrate the WiFi Analytics platform (e.g., Purple) with the retailer's Point-of-Sale (POS) or CRM system via API. By matching the identity data captured at the captive portal (such as an email address) with the customer profile in the POS system when a purchase is made, the business can accurately measure the impact of WiFi engagement on sales conversion. From a data privacy perspective, this integration must be disclosed in the Privacy Policy presented at the captive portal, and the user's consent must explicitly cover this use of their data. Data minimisation principles under GDPR should be applied, retaining only the data necessary for the stated purpose.



