Is Public WiFi Safe? The Definitive Guide
This definitive guide provides enterprise IT leaders with actionable strategies for architecting secure public WiFi networks. It details the technical mitigation of primary threats like MITM attacks and rogue access points, while outlining how to leverage platforms like Purple to ensure compliance, protect corporate infrastructure, and safely monetise guest connectivity.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: The Threat Landscape and Architecture
- Core Vulnerabilities
- Secure Architecture Principles
- Implementation Guide: Deploying Secure Guest WiFi
- Step 1: Network Segmentation and Firewall Configuration
- Step 2: Access Point Configuration
- Step 3: Captive Portal and Authentication
- Best Practices for Industry Verticals
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For enterprise IT leaders, network architects, and venue operations directors, the question "is public WiFi safe?" is no longer a consumer concern—it is a critical infrastructure mandate. As public connectivity transitions from a hospitality perk to a baseline operational requirement across retail, healthcare, and large-scale venues, the threat landscape has evolved. Unsecured networks expose both guests to data interception and corporate infrastructure to lateral movement.
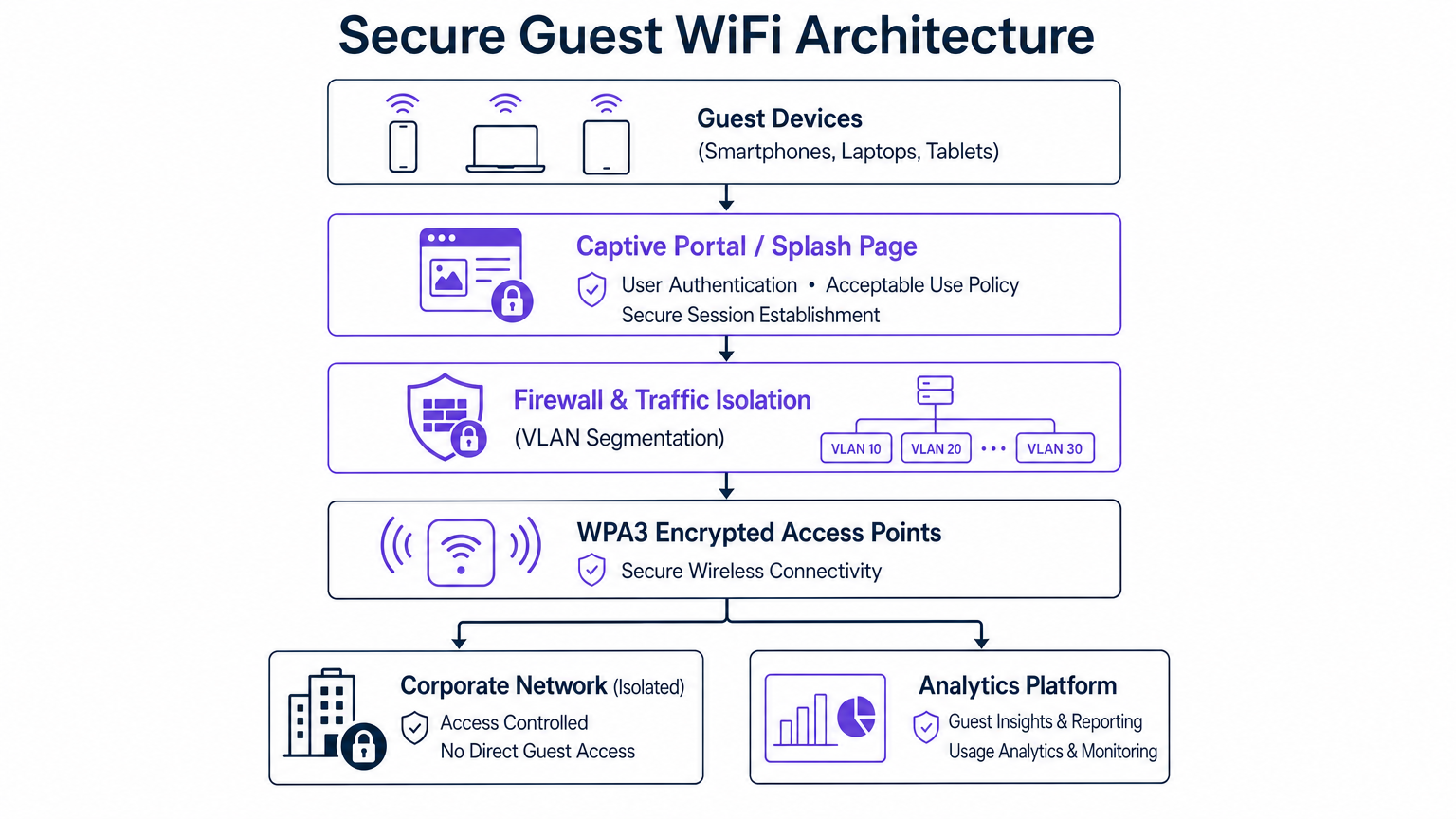
This definitive guide provides actionable, vendor-neutral strategies for architecting secure public WiFi deployments. We examine the mechanics of primary threats—including Man-in-the-Middle (MITM) attacks and Evil Twin access points—and outline the technical countermeasures required to mitigate them. By implementing strict VLAN segmentation, leveraging WPA3 Enhanced Open encryption, and deploying robust captive portals via platforms like Purple, organisations can transform vulnerable open networks into secure, compliant, and monetisable assets. This guide serves as a practical blueprint for deploying enterprise-grade guest WiFi that protects users, ensures regulatory compliance (such as GDPR and PCI DSS), and safeguards corporate data.
Technical Deep-Dive: The Threat Landscape and Architecture
The inherent vulnerability of traditional public WiFi stems from the lack of link-layer encryption on open SSIDs. When data is transmitted in the clear, any device within radio range equipped with packet-sniffing software can intercept the traffic.
Core Vulnerabilities
- Man-in-the-Middle (MITM) Attacks: The attacker positions themselves between the guest device and the access point (AP) or router. By intercepting the communication flow, the attacker can eavesdrop on sensitive data or alter the traffic in transit.
- Evil Twin Access Points: Attackers deploy a rogue AP broadcasting the same Service Set Identifier (SSID) as the legitimate venue network (e.g., "Free_Stadium_WiFi"). Devices automatically connect to the stronger signal, routing all traffic through the attacker's hardware.
- Packet Sniffing: Passive interception of unencrypted data packets travelling over the airwaves. While HTTPS mitigates payload inspection, metadata and DNS queries often remain exposed.
- Session Hijacking: Exploiting intercepted session cookies to impersonate the user on authenticated platforms, bypassing login requirements.

Secure Architecture Principles
To counter these threats, enterprise deployments must move beyond basic flat networks. A secure architecture relies on defence-in-depth principles:
- VLAN Segmentation: Guest traffic must be logically isolated from corporate, Point-of-Sale (POS), and operational technology (OT) networks. A dedicated VLAN ensures that even if a guest device is compromised, lateral movement into the corporate environment is blocked.
- Client Isolation (Layer 2 Isolation): Access points must be configured to prevent peer-to-peer communication between devices connected to the same guest SSID. This prevents infected guest devices from scanning or attacking other guests.
- WPA3 and Opportunistic Wireless Encryption (OWE): WPA3 introduces Enhanced Open, which utilises OWE to provide individualised encryption for each client connection on an open network, eliminating passive eavesdropping without requiring a shared password.
- Passpoint / OpenRoaming: Leveraging IEEE 802.1X, Passpoint allows devices to authenticate automatically and securely using credentials provided by an identity provider. Purple acts as a free identity provider for OpenRoaming under the Connect license, facilitating seamless, encrypted access.
Implementation Guide: Deploying Secure Guest WiFi
Deploying a secure network requires meticulous configuration across the wireless controller, switches, and firewalls.
Step 1: Network Segmentation and Firewall Configuration
Begin by defining a dedicated subnet and VLAN for guest traffic. Configure the edge firewall with strict Access Control Lists (ACLs).
- Rule 1: Deny all traffic from the Guest VLAN to any RFC 1918 private IP space (corporate networks).
- Rule 2: Allow traffic from the Guest VLAN strictly to the WAN (Internet) on required ports (e.g., 80, 443, 53).
- Rule 3: Implement DNS filtering to block known malicious domains, preventing guests from accessing phishing sites or downloading malware.
Step 2: Access Point Configuration
When provisioning your APs (refer to resources like Your Guide to a Wireless Access Point Ruckus for vendor-specific details):
- Enable Client Isolation.
- Configure Rogue AP detection to scan the RF environment and suppress unauthorised SSIDs attempting to spoof your network.
- Limit bandwidth per client to prevent denial-of-service (DoS) conditions caused by a single user monopolising the connection.
Step 3: Captive Portal and Authentication
The captive portal is the critical gateway for security and compliance. Instead of a simple pre-shared key (PSK), route users through a robust portal.
- Integrate a platform like Purple's Guest WiFi solution.
- Enforce acceptance of an Acceptable Use Policy (AUP) before granting access.
- Utilise secure authentication methods (e.g., OAuth via social logins or SMS verification) to establish a verified session.
Best Practices for Industry Verticals
Security requirements vary significantly depending on the deployment environment.
- Hospitality & Retail: In environments like Retail and Hospitality , the focus is on balancing frictionless access with security. Captive portals must be mobile-optimised. Data collection must strictly adhere to GDPR or local privacy laws.
- Healthcare: Healthcare environments face stringent regulatory requirements (e.g., HIPAA). Guest networks must be absolutely isolated from clinical systems. For deeper insights, consult WiFi in Hospitals: A Guide to Secure Clinical Networks .
- Transport & Public Venues: In Transport hubs or stadiums, high-density environments require aggressive client management and robust rogue AP mitigation due to the sheer volume of transient users. Consider advanced deployments like Your Guide to Enterprise In Car Wi Fi Solutions .
For a comprehensive overview of enterprise hardware and software considerations, refer to the Enterprise WiFi Solutions: A Buyer's Guide .
Troubleshooting & Risk Mitigation
Even well-architected networks experience anomalies. Continuous monitoring is essential.
- Failure Mode: Incomplete Segmentation.
- Symptom: Guest devices can ping internal servers.
- Mitigation: Regularly audit firewall rules and perform penetration testing from the guest network perspective.
- Failure Mode: Rogue AP Proliferation.
- Symptom: Users report connecting to the network but failing to reach the captive portal, or IT detects duplicate SSIDs.
- Mitigation: Ensure Wireless Intrusion Prevention Systems (WIPS) are active and configured to automatically contain rogue APs via deauthentication frames.
- Failure Mode: Malicious Outbound Traffic.
- Symptom: A guest device attempts to contact command-and-control (C2) servers or launch outbound spam campaigns.
- Mitigation: Utilise WiFi Analytics to monitor traffic patterns. Implement automated throttling or blacklisting for MAC addresses exhibiting anomalous behaviour.
ROI & Business Impact
Investing in secure public WiFi is not merely a risk mitigation exercise; it drives measurable business value.
- Risk Avoidance: A single data breach originating from an unsecured guest network can result in severe regulatory fines (e.g., GDPR penalties) and catastrophic brand damage. Secure architecture mitigates this unquantifiable risk.
- Enhanced Data Collection: A secure, compliant captive portal builds user trust. When users feel secure, they are more likely to authenticate using real credentials, improving the quality of first-party data collected for marketing initiatives.
- Operational Efficiency: Automated onboarding via OpenRoaming reduces helpdesk tickets related to connectivity issues. Cloud-managed analytics platforms provide IT teams with centralised visibility, reducing the time required to troubleshoot network anomalies.
By treating public WiFi as an extension of the enterprise security perimeter, organisations can deliver a seamless guest experience while maintaining absolute control over their infrastructure.
Key Terms & Definitions
VLAN Segmentation
The practice of logically dividing a physical network into multiple isolated broadcast domains.
Essential for keeping guest traffic entirely separate from corporate data and payment systems.
Client Isolation (Layer 2 Isolation)
A wireless network setting that prevents devices connected to the same access point from communicating with each other.
Critical on public networks to stop infected guest devices from spreading malware to other guests.
Man-in-the-Middle (MITM) Attack
A cyberattack where an adversary secretly intercepts and relays communications between two parties who believe they are communicating directly.
The primary threat on unencrypted public WiFi, allowing attackers to steal credentials or inject malicious code.
Evil Twin Access Point
A fraudulent Wi-Fi access point that appears to be legitimate, set up to eavesdrop on wireless communications.
Attackers use this in venues to trick users into connecting, routing all traffic through the attacker's hardware.
WPA3 Enhanced Open (OWE)
A security certification that provides unauthenticated data encryption for users connecting to open Wi-Fi networks.
Replaces the legacy open network model, ensuring that even without a password, over-the-air traffic cannot be passively sniffed.
Passpoint / OpenRoaming
A protocol based on IEEE 802.1X that allows devices to automatically and securely authenticate to Wi-Fi networks using credentials from an identity provider.
Provides cellular-like roaming capabilities on Wi-Fi, improving user experience while mandating strong encryption.
Captive Portal
A web page that users of a public-access network are obliged to view and interact with before access is granted.
The enforcement point for Acceptable Use Policies and the primary mechanism for collecting compliant first-party data.
Wireless Intrusion Prevention System (WIPS)
A network device that monitors the radio spectrum for unauthorized access points (intrusion detection) and can automatically take countermeasures.
Required in enterprise deployments to automatically detect and suppress Evil Twin attacks.
Case Studies
A 400-room luxury hotel is upgrading its network infrastructure. The IT Director needs to deploy a guest WiFi solution that provides seamless roaming across the property, captures guest data for marketing, but absolutely prevents guests from accessing the hotel's property management system (PMS) and point-of-sale (POS) terminals.
- Define VLAN 10 for Corporate/PMS, VLAN 20 for POS, and VLAN 30 for Guest Access. 2. Configure the edge firewall to drop all packets originating from VLAN 30 destined for VLAN 10 or 20. 3. Enable Layer 2 Client Isolation on all access points broadcasting the Guest SSID. 4. Deploy Purple's Guest WiFi captive portal to handle authentication and enforce the AUP, routing authenticated traffic directly to the WAN.
A large retail shopping centre is experiencing complaints that users are connecting to 'Free_Mall_WiFi' but receiving certificate errors when browsing, indicating a potential MITM attack via a rogue AP.
- Activate the Wireless Intrusion Prevention System (WIPS) on the enterprise wireless controller. 2. Configure the WIPS to classify any unmanaged AP broadcasting the official SSID or matching the venue's BSSID profile as 'Rogue'. 3. Enable automated containment, allowing legitimate APs to send deauthentication frames to clients attempting to connect to the rogue device. 4. Dispatch security personnel to physically locate the rogue hardware using signal strength mapping.
Scenario Analysis
Q1. You are deploying a guest network in a hospital waiting area. You must provide free access while ensuring absolute compliance with patient data protection regulations. What is the most critical architectural requirement?
💡 Hint:Consider how traffic is routed once it leaves the access point.
Show Recommended Approach
Strict VLAN segmentation and firewall ACLs to physically or logically isolate the guest network from the clinical and administrative networks. A captive portal must also be used to enforce an Acceptable Use Policy.
Q2. A stadium deployment is seeing high CPU utilisation on the core router during events, and analytics show several devices performing rapid IP scans across the subnet. What configuration was likely missed?
💡 Hint:Think about how devices communicate with each other on the same SSID.
Show Recommended Approach
Client Isolation (Layer 2 Isolation) is likely disabled on the access points. Enabling this prevents peer-to-peer communication on the guest network, stopping the IP scanning behaviour.
Q3. The marketing team wants to offer 'frictionless' access without a password, but the security team mandates that over-the-air traffic cannot be passively sniffed. How do you resolve this conflict?
💡 Hint:Look at modern wireless encryption standards designed for open networks.
Show Recommended Approach
Implement WPA3 with Enhanced Open (Opportunistic Wireless Encryption). This provides individualised encryption for each connection without requiring the user to enter a pre-shared key, satisfying both marketing and security requirements.



