NAC for Healthcare: Securing Medical Devices and Patient Data
This guide provides a comprehensive technical reference for deploying Network Access Control (NAC) in healthcare environments, covering architecture design, authentication mechanisms, device profiling, and VLAN segmentation for medical IoT, clinical systems, and guest access. It addresses compliance requirements across HIPAA, NHS DSP Toolkit, ISO 27001, and GDPR, with concrete implementation scenarios and vendor-neutral best practices. For IT directors and CTOs in healthcare, this is the operational blueprint for securing medical devices and patient data without disrupting clinical workflows.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Healthcare Network Challenge
- Core NAC Architecture
- Authentication Mechanisms
- Device Profiling and Posture Assessment
- Implementation Guide
- Phase 1: Discovery and Profiling (Monitor Mode)
- Phase 2: Policy Definition and VLAN Segmentation
- Phase 3: Graduated Enforcement
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- The Fail-Open vs. Fail-Closed Decision
- ROI & Business Impact
Executive Summary
Securing a modern healthcare network is no longer just about protecting the perimeter; it is about managing the explosion of connected devices within the facility. From MRI scanners and smart IV pumps to patient tablets and guest smartphones, the sheer volume and diversity of endpoints create an unprecedented attack surface. Network Access Control (NAC) is the critical infrastructure required to identify, authenticate, and authorise every device connecting to the network, ensuring that medical devices and patient data remain secure.
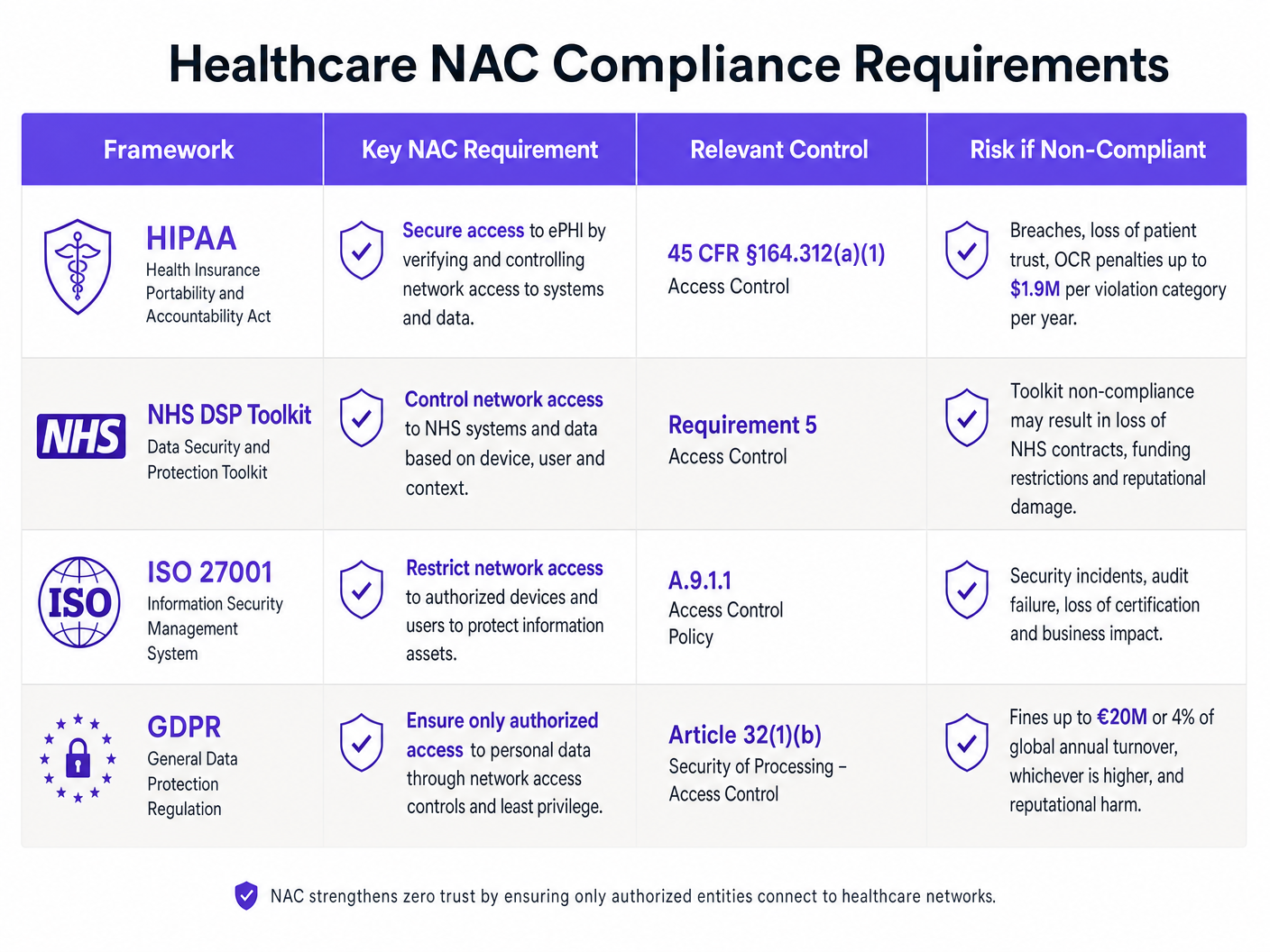
For CTOs and IT Directors in healthcare, deploying a robust NAC solution is a non-negotiable requirement for compliance with HIPAA, the NHS DSP Toolkit, and GDPR, as well as for meaningful risk mitigation. This guide provides a technical deep-dive into NAC architecture, implementation strategies, and best practices tailored for healthcare environments. We explore how to achieve zero-trust network access, segment clinical IoT devices from public traffic, and leverage solutions like Guest WiFi to securely manage visitor access without compromising the core clinical network.
Technical Deep-Dive
The Healthcare Network Challenge
Healthcare networks are uniquely complex. They must simultaneously support clinical systems with strict uptime and data integrity requirements, a vast array of Internet of Medical Things (IoMT) devices running legacy operating systems, staff BYOD, and thousands of unmanaged patient and visitor devices. Traditional perimeter security or static VLAN assignments are wholly insufficient for this environment. A dynamic, identity-driven approach is required to enforce least-privilege access across the entire network fabric.
The scale of the problem is significant. A typical 500-bed hospital may have upwards of 10,000 connected devices at any given time. Fewer than 30% of those devices will be capable of running a traditional endpoint security agent. The remaining 70% — infusion pumps, patient monitors, imaging equipment, smart beds — must be secured through network-level controls rather than host-based ones. This is precisely the problem NAC is designed to solve.
Core NAC Architecture
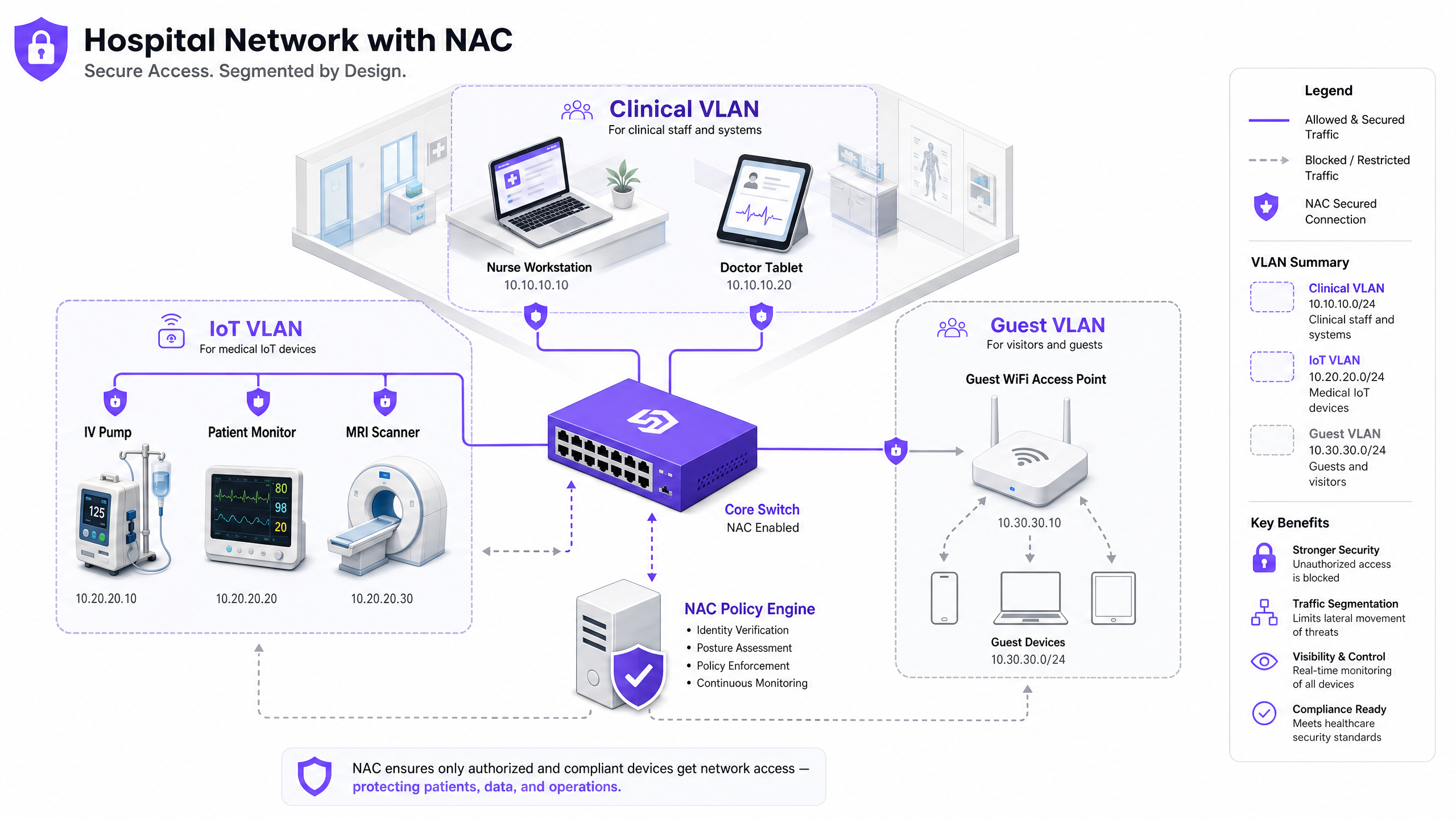
A production-grade NAC deployment in a healthcare setting relies on four key components working in concert. The Supplicant is the client software or native OS component on the connecting device that initiates the authentication exchange. For headless IoT devices that lack supplicant capability, MAC Authentication Bypass (MAB) is used as a fallback. The Authenticator is the network access device — a switch or wireless access point — that intercepts the connection request and acts as a gatekeeper, forwarding credentials to the authentication server. The Authentication Server (typically a RADIUS-based policy engine such as Cisco ISE, Aruba ClearPass, or ForeScout) is the central intelligence of the system; it validates identity, evaluates posture, and returns an authorisation decision with a dynamic VLAN assignment. Finally, the Directory Store — typically Microsoft Active Directory or LDAP — provides the user and device identity records against which the RADIUS server validates requests.
Authentication Mechanisms
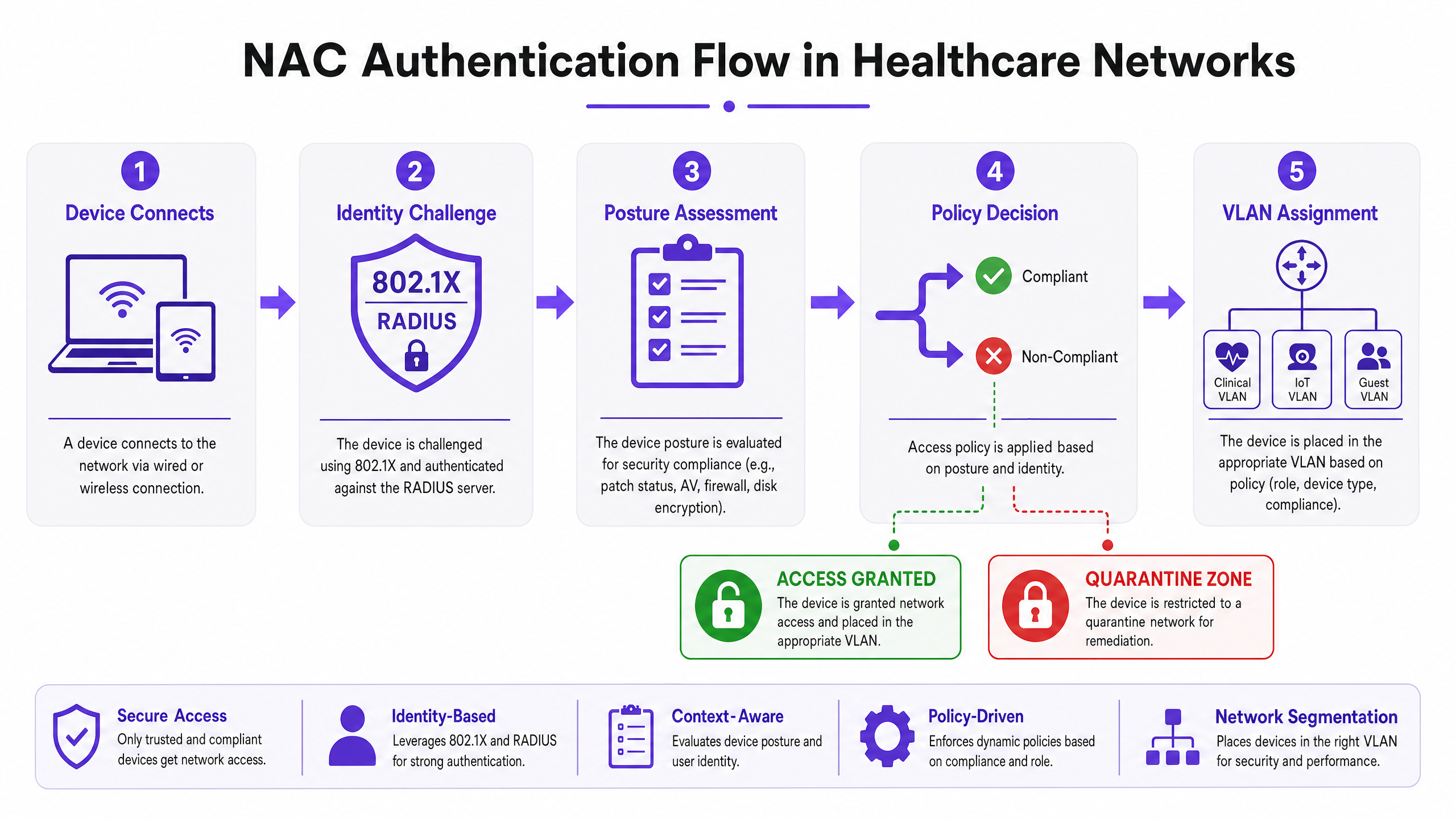
IEEE 802.1X is the gold standard for port-based network access control. It provides a framework for encapsulating EAP (Extensible Authentication Protocol) messages between the supplicant and the authentication server. For corporate-owned devices, EAP-TLS (certificate-based mutual authentication) is strongly preferred over PEAP-MSCHAPv2 (password-based). EAP-TLS eliminates the credential theft vector entirely — a compromised password cannot grant network access if the authentication requires a valid machine certificate signed by your internal PKI.
MAC Authentication Bypass (MAB) is the pragmatic solution for devices that cannot support 802.1X — which describes the majority of medical IoT equipment. The authenticator uses the device's MAC address as its identity credential. MAB alone is weak, since MAC addresses can be spoofed, but when combined with deep device profiling and behavioural analysis, it becomes a robust control for managing known medical devices.
Captive Portal authentication is the appropriate mechanism for guest and patient access. A well-implemented Guest WiFi solution handles user registration, terms of service acceptance, and bandwidth management, ensuring that public traffic is completely isolated from the clinical network from the moment a device associates with the access point.
Device Profiling and Posture Assessment
Knowing who is connecting is only half the battle; knowing what they are connecting with is equally critical. Device Profiling uses a combination of passive and active network probes — DHCP fingerprints, HTTP User-Agent strings, SNMP queries, Nmap-based active scanning, and traffic pattern analysis — to classify every device on the network. A well-tuned profiling engine can distinguish between a Philips IntelliVue patient monitor and a Baxter Sigma Spectrum infusion pump based on their network behaviour alone, even if both connect via MAB.
Posture Assessment applies to managed corporate devices. Before granting access to the clinical VLAN, the NAC system queries the endpoint for compliance: Is the OS patched to the required level? Is the antivirus signature database current? Is full-disk encryption enabled? Devices that fail posture checks are dynamically assigned to a remediation VLAN where they can receive updates but cannot access clinical systems.
Implementation Guide
Deploying NAC in a live hospital environment requires meticulous planning to avoid disrupting critical care services. A phased approach is not just recommended — it is mandatory.
Phase 1: Discovery and Profiling (Monitor Mode)
Begin by deploying the NAC solution in Monitor Mode. Configure switches and access points to forward authentication requests to the NAC server, but instruct the server to permit all access while logging every connection. Run this phase for a minimum of four weeks, covering all operational shifts and device usage patterns. The output is a comprehensive, verified inventory of every device on the network — including shadow IT and legacy equipment that may not appear in your CMDB. Use this data to refine device profiling rules and identify any devices that will require special handling during enforcement.
Phase 2: Policy Definition and VLAN Segmentation
Based on the discovery data, define granular access policies mapped to specific VLANs. The Clinical VLAN should be restricted to authorised staff devices authenticated via 802.1X EAP-TLS and known medical IoT devices authenticated via MAB with verified profiling. The IoT VLAN should be further subdivided by device class — a dedicated VLAN for infusion pumps, a separate one for imaging equipment — with strict ACLs permitting communication only to the specific management servers each device class requires. The Guest VLAN routes all unauthenticated traffic to a captive portal, leveraging a platform that integrates WiFi Analytics to provide operational visibility while maintaining complete isolation from the internal network.
For specific vendor configuration guidance, refer to our detailed walkthrough on How to Configure NAC Policies for VLAN Steering in Cisco Meraki .
Phase 3: Graduated Enforcement
Transition from Monitor Mode to Enforcement Mode in stages. Begin with Low-Impact Enforcement: apply basic ACLs to block known malicious traffic patterns but permit most legitimate traffic. Use this phase to identify and resolve any policy misconfigurations before they affect clinical operations. Then transition to Closed Mode enforcement, rolling out department by department — administrative areas first, clinical support areas second, and critical care units last. At each stage, maintain a rapid rollback procedure and ensure the clinical engineering team is available to validate that medical devices are functioning correctly post-enforcement.
Best Practices
Mandate Certificate-Based Authentication. For all corporate-owned devices, EAP-TLS with machine certificates issued by your internal PKI should be the only accepted authentication method. Passwords are a liability; certificates are not.
Micro-Segment Medical IoT. Do not group all medical devices into a single IoT VLAN. Segment by device class and apply zero-trust ACLs. An infusion pump should only be able to reach its specific management server and the EMR system — nothing else. Lateral movement between device classes should be blocked at the network layer.
Implement Continuous Behavioural Monitoring. NAC is not a set-and-forget control. Integrate your NAC policy engine with a SIEM or network detection and response (NDR) platform. If a profiled IoT device begins exhibiting anomalous behaviour — unexpected port scans, unusual outbound connections — the NAC system should dynamically quarantine it without waiting for a human to intervene.
Optimise Your Wireless Infrastructure. Ensure your access point deployment provides adequate coverage and capacity for the device density in each clinical area. Understanding the implications of different wireless bands is essential — our guide on Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 covers the practical trade-offs between 2.4 GHz, 5 GHz, and 6 GHz for mixed IoT and clinical environments.
Integrate Guest Access as a First-Class Security Control. Guest WiFi is not an afterthought — it is one of the highest-risk traffic types on your network. A dedicated Guest WiFi platform ensures that patient and visitor devices are isolated, authenticated, and managed independently of the clinical network. The WiFi Analytics data generated can also support operational improvements in patient flow and facility management.
Troubleshooting & Risk Mitigation
Common Failure Modes
The Silent IoT Device is the most common operational issue in healthcare NAC deployments. Medical devices that enter a low-power sleep state drop their network connection and fail to re-authenticate correctly when they wake. The result is a device that appears offline to the NAC system but is physically present and attempting to operate. Mitigation involves tuning MAC aging timers on switches to match the expected sleep cycle of each device class, and configuring the NAC profiling engine to recognise returning devices without requiring a full re-authentication cycle.
Certificate Expiration is a systemic risk that can lock out hundreds of staff devices simultaneously if not managed proactively. Implement automated certificate lifecycle management using SCEP or EST protocols, and configure alerting for certificates expiring within 60 days. Stagger certificate renewal cycles across device groups to avoid mass simultaneous expirations.
RADIUS Server Misconfiguration — incorrect IP addresses, mismatched shared secrets, or misconfigured EAP methods on network access devices — will cause silent authentication failures that are difficult to diagnose without proper logging. Use centralised network management to push standardised RADIUS configurations to all switches and access points, and implement RADIUS accounting to provide an audit trail of all authentication events.
The Fail-Open vs. Fail-Closed Decision
This is the most consequential architectural decision in a healthcare NAC deployment. A fail-closed policy (denying network access if the NAC server is unreachable) provides the strongest security posture but risks isolating life-critical medical equipment during a server outage. A fail-open policy (granting restricted access if the server is down) maintains clinical continuity but creates a window of reduced security control. The recommended approach is a tiered failure policy: critical clinical VLANs fail-open with strong network-level ACLs in place, while administrative and guest VLANs fail-closed. Deploy NAC policy engines in a highly available cluster across multiple physical locations or availability zones to minimise the frequency of this decision being triggered.
ROI & Business Impact
The business case for NAC in healthcare is compelling across multiple dimensions. The primary driver is risk reduction: a single reportable data breach involving protected health information (PHI) carries average costs exceeding $10 million when regulatory fines, legal fees, remediation costs, and reputational damage are factored in. NAC directly reduces the probability and potential blast radius of such an incident by ensuring that only authorised, compliant devices can access systems containing PHI.
Operational efficiency is a secondary but significant benefit. Automated device profiling and onboarding eliminate the manual switch-port configuration that consumes significant IT helpdesk time in environments without NAC. Clinical engineering teams gain a real-time, accurate device inventory that supports lifecycle management, maintenance scheduling, and procurement planning.
Compliance posture is directly improved. HIPAA's Access Control standard (45 CFR §164.312(a)(1)), the NHS DSP Toolkit's network security requirements, and GDPR's Article 32 security of processing obligations all require demonstrable controls over who and what can access systems containing patient data. A well-documented NAC deployment provides the audit evidence required to satisfy these obligations.
Finally, patient experience benefits from a well-implemented guest access strategy. Providing reliable, secure Guest WiFi for patients and visitors improves satisfaction scores while the underlying WiFi Analytics data supports operational improvements in bed management, visitor flow, and facility utilisation.
Key Definitions
Network Access Control (NAC)
A security framework that enforces policy-based control over which devices and users are permitted to connect to a network, and what resources they can access once connected. NAC combines authentication, device profiling, posture assessment, and dynamic policy enforcement.
IT teams encounter NAC as both a product category (Cisco ISE, Aruba ClearPass, ForeScout) and an architectural approach. In healthcare, NAC is the primary mechanism for enforcing network segmentation between clinical systems, medical IoT, and guest access.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices wishing to connect to a LAN or WLAN. It defines the roles of the supplicant (client), authenticator (switch/AP), and authentication server (RADIUS), and encapsulates EAP messages between them.
802.1X is the authentication mechanism used for corporate-owned devices in a NAC deployment. IT teams configure it on both the network access devices (switches, APs) and the endpoint devices (via OS-level supplicant settings or Group Policy).
MAC Authentication Bypass (MAB)
A fallback authentication mechanism used for devices that cannot support 802.1X. The network access device uses the connecting device's MAC address as its identity credential, forwarding it to the RADIUS server for authorisation.
MAB is the primary authentication method for medical IoT devices in healthcare NAC deployments. It must be combined with device profiling to provide meaningful security, as MAC addresses can be spoofed.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A certificate-based EAP method that provides mutual authentication between the client and the authentication server using X.509 digital certificates. Both the client and the server present certificates, eliminating the password-based credential theft vector.
EAP-TLS is the recommended authentication method for corporate devices in healthcare NAC deployments. It requires a functioning internal PKI to issue and manage machine certificates.
VLAN Steering
The dynamic assignment of a connecting device to a specific VLAN based on the authentication result and policy decision from the NAC system. The RADIUS server returns a VLAN ID (or VLAN name) as part of the Access-Accept response, and the authenticator places the device's port into that VLAN.
VLAN steering is the mechanism by which NAC enforces network segmentation. IT teams configure RADIUS attributes (Tunnel-Type, Tunnel-Medium-Type, Tunnel-Private-Group-ID) on the authentication server to specify the target VLAN for each device class.
Device Profiling
The process of identifying the type, manufacturer, and operating system of a connecting device using passive network probes (DHCP fingerprints, HTTP User-Agent strings, mDNS/Bonjour advertisements) and active scanning techniques (Nmap, SNMP queries).
Device profiling is essential for accurately classifying medical IoT devices in a healthcare NAC deployment. Without profiling, MAB-authenticated devices are indistinguishable from each other, making it impossible to apply device-class-specific access policies.
Posture Assessment
The evaluation of a connecting device's security compliance state before granting network access. Posture checks typically verify OS patch level, antivirus signature currency, disk encryption status, and the presence of required security software.
Posture assessment applies to managed corporate devices (laptops, workstations) in a healthcare NAC deployment. Devices that fail posture checks are dynamically assigned to a remediation VLAN where they can receive updates but cannot access clinical systems.
Quarantine VLAN
A restricted network segment to which non-compliant or unrecognised devices are assigned when they fail authentication or posture assessment. The quarantine VLAN typically provides access only to remediation resources (patch servers, antivirus update servers) and blocks access to all clinical and corporate systems.
IT teams use quarantine VLANs as the enforcement mechanism for NAC policy violations. A device in the quarantine VLAN is effectively isolated from the rest of the network while still being able to receive the updates needed to achieve compliance.
IoMT (Internet of Medical Things)
The ecosystem of connected medical devices and healthcare applications that communicate over networks to collect and transmit patient data. IoMT includes infusion pumps, patient monitors, imaging equipment, smart beds, and wearable health monitors.
IoMT devices represent the largest and most challenging device category in a healthcare NAC deployment. They typically run legacy operating systems, cannot support endpoint security agents, and require specialised profiling and micro-segmentation strategies.
Zero-Trust Network Access (ZTNA)
A security model that eliminates implicit trust from the network architecture. Under ZTNA, no device or user is trusted by default, regardless of their network location. Every access request must be explicitly authenticated, authorised, and continuously validated.
ZTNA is the architectural philosophy that underpins modern NAC deployments. In healthcare, ZTNA means that even a device on the clinical VLAN must continuously prove its identity and compliance state — network location alone does not grant access to sensitive systems.
Worked Examples
A 350-bed NHS Trust is preparing for its annual DSP Toolkit submission. The IT Director has identified that the network currently has no device authentication — everything connects to a flat network with a single VLAN. There are approximately 2,400 connected devices, of which an estimated 800 are medical IoT devices (infusion pumps, patient monitors, ventilators). The Trust needs to achieve compliance within 6 months without disrupting clinical operations. Where do they start?
The engagement begins with a 4-week Monitor Mode deployment. Configure all core switches and wireless controllers to forward 802.1X and MAB requests to a newly deployed RADIUS policy engine (Cisco ISE or Aruba ClearPass are the leading options for this scale). The server is set to permit-all but log everything. After 4 weeks, analyse the profiling data to categorise all 2,400 devices. Expect to find approximately 800 medical IoT devices (MAB candidates), 600 corporate workstations and laptops (802.1X candidates), 400 staff BYOD devices, and 600 patient/visitor devices. In week 5-8, define the VLAN architecture: Clinical VLAN (10.10.0.0/22) for staff devices and EMR-connected systems, IoT VLAN (10.20.0.0/22) for medical devices with ACLs restricting communication to specific management servers, and Guest VLAN (10.30.0.0/22) routed to a captive portal. Deploy a dedicated Guest WiFi platform for the patient-facing network. In weeks 9-16, begin graduated enforcement starting with the administrative block. In weeks 17-24, extend enforcement to clinical areas, validating each medical device class with clinical engineering before enforcement. By month 6, the Trust has a fully segmented network with documented access controls, satisfying DSP Toolkit Requirement 5 (Access Control) and providing the audit evidence required for the submission.
A private hospital group is expanding its network to support a new oncology wing with 150 new connected medical devices, including 40 infusion pumps from two different manufacturers, 60 patient monitors, and 50 mixed devices (smart beds, nurse call systems). The network team has an existing Cisco Meraki infrastructure with no NAC. The CISO wants micro-segmentation in place before the wing opens in 8 weeks. What is the deployment strategy?
With Cisco Meraki as the existing infrastructure, the deployment leverages Meraki's built-in RADIUS integration and Group Policy features. First, deploy a RADIUS server (FreeRADIUS or Cisco ISE) and configure all Meraki switches and MR access points in the new wing to use it for authentication. Configure MAB for all medical devices, using Meraki's client fingerprinting to assist with device classification. Define three Group Policies in the Meraki dashboard: IoT-InfusionPumps (VLAN 210, ACL permitting only traffic to the infusion pump management server at 10.10.5.20 and the EMR at 10.10.1.10), IoT-PatientMonitors (VLAN 220, ACL permitting traffic to the monitoring server at 10.10.5.30 and the EMR), and IoT-General (VLAN 230, more permissive ACL for mixed devices). Pre-populate the RADIUS server with the MAC addresses of all 150 devices, sourced from the procurement documentation. Run in Monitor Mode for the first two weeks of the wing's soft opening, validating that all devices are correctly profiled and assigned. Transition to full enforcement in week 3. For detailed Meraki-specific VLAN steering configuration, refer to the guide on How to Configure NAC Policies for VLAN Steering in Cisco Meraki .
Practice Questions
Q1. A regional hospital has 1,200 connected devices. During a Monitor Mode NAC deployment, the profiling engine identifies 340 devices with unknown profiles — they are not matching any known medical device fingerprint and are not corporate workstations. The CISO wants to move to enforcement in 2 weeks. What is the correct course of action, and what are the risks of proceeding on the CISO's timeline?
Hint: Consider what those 340 unknown devices might be, and what happens to them when enforcement goes live if they remain unclassified.
View model answer
The correct action is to delay enforcement until the 340 unknown devices are investigated and classified. These devices will be placed in the quarantine VLAN when enforcement goes live, which may include clinical equipment that is critical to patient care. The investigation should involve: (1) cross-referencing MAC address OUI prefixes against manufacturer databases to identify likely device types, (2) reviewing switch port locations to physically identify the devices, (3) engaging clinical engineering to identify any medical devices not in the CMDB, and (4) reviewing DHCP logs for hostname patterns. Only after all 340 devices are classified and appropriate policies are defined should enforcement proceed. The risk of proceeding on the CISO's 2-week timeline is a potential patient safety incident if an unclassified medical device is quarantined during a critical care scenario.
Q2. An IT architect is designing the NAC failure mode policy for a new hospital wing. The clinical director insists that medical devices must never lose network connectivity, even if the NAC server goes offline. The CISO insists on fail-closed for all VLANs. How do you resolve this conflict, and what compensating controls are required?
Hint: Think about tiered failure policies and what network-level controls can substitute for NAC policy enforcement during an outage.
View model answer
The resolution is a tiered failure policy that satisfies both requirements. The IoT VLAN and Clinical VLAN are configured to fail-open (permit access if the RADIUS server is unreachable), while the Guest VLAN and administrative VLAN are configured to fail-closed. The compensating controls that make the fail-open policy acceptable for clinical VLANs are: (1) strict ACLs applied at the VLAN gateway that restrict inter-VLAN traffic regardless of NAC state, (2) NAC server high availability deployment (active-active cluster across two data centres) to minimise the probability of the failure mode being triggered, (3) network-level IDS/IPS monitoring on clinical VLANs to detect anomalous traffic during NAC outages, and (4) documented incident response procedures for NAC outage scenarios. This approach satisfies the clinical director's availability requirement while providing the CISO with documented compensating controls that maintain an acceptable security posture.
Q3. A hospital's NAC deployment has been running in full enforcement mode for 3 months. The security team receives an alert that a device on the IoT VLAN (profiled as an infusion pump) is attempting to establish outbound connections to an external IP address on port 443. The device's MAC address matches the expected profile. What is the immediate response, and what does this incident indicate about the NAC architecture?
Hint: Consider both the immediate containment action and the architectural gap that allowed this traffic to be attempted (even if blocked).
View model answer
The immediate response is to dynamically quarantine the device via the NAC policy engine, isolating it from the IoT VLAN pending investigation. The security team should capture a packet trace from the device's switch port to analyse the traffic content, and clinical engineering should be notified to physically inspect the device and take it offline if necessary. The incident indicates two architectural issues: (1) the ACL on the IoT VLAN is not blocking outbound internet traffic from infusion pumps — the ACL should permit only traffic to the specific management server IP and the EMR, with an explicit deny-all rule for all other destinations; and (2) the behavioural monitoring integration is working correctly (the alert was generated), but the ACL should have blocked the traffic before it was even attempted. The remediation action is to tighten the IoT VLAN ACLs to implement a default-deny posture, permitting only explicitly required communication paths for each device class.