Bonnes pratiques de micro-segmentation pour les réseaux WiFi partagés
Ce guide de référence technique fournit des stratégies concrètes pour la mise en œuvre de la micro-segmentation sur une infrastructure WiFi partagée. Il détaille comment les responsables informatiques et les architectes réseau peuvent isoler en toute sécurité le trafic des invités, de l'IoT et du personnel afin d'atténuer les risques, d'assurer la conformité et d'optimiser les performances du réseau.
Écouter ce guide
Voir la transcription du podcast
- Résumé Exécutif
- Approfondissement Technique
- La Couche d'Authentification : IEEE 802.1X et WPA3
- Les Trois Segments Clés
- Guide d'Implémentation
- Phase 1 : Découverte et Audit du Réseau
- Phase 2 : Définition des Politiques
- Phase 3 : Configuration de l'Infrastructure
- Phase 4 : Déploiement Progressif
- Bonnes Pratiques
- Dépannage et atténuation des risques
- ROI et impact commercial

Résumé Exécutif
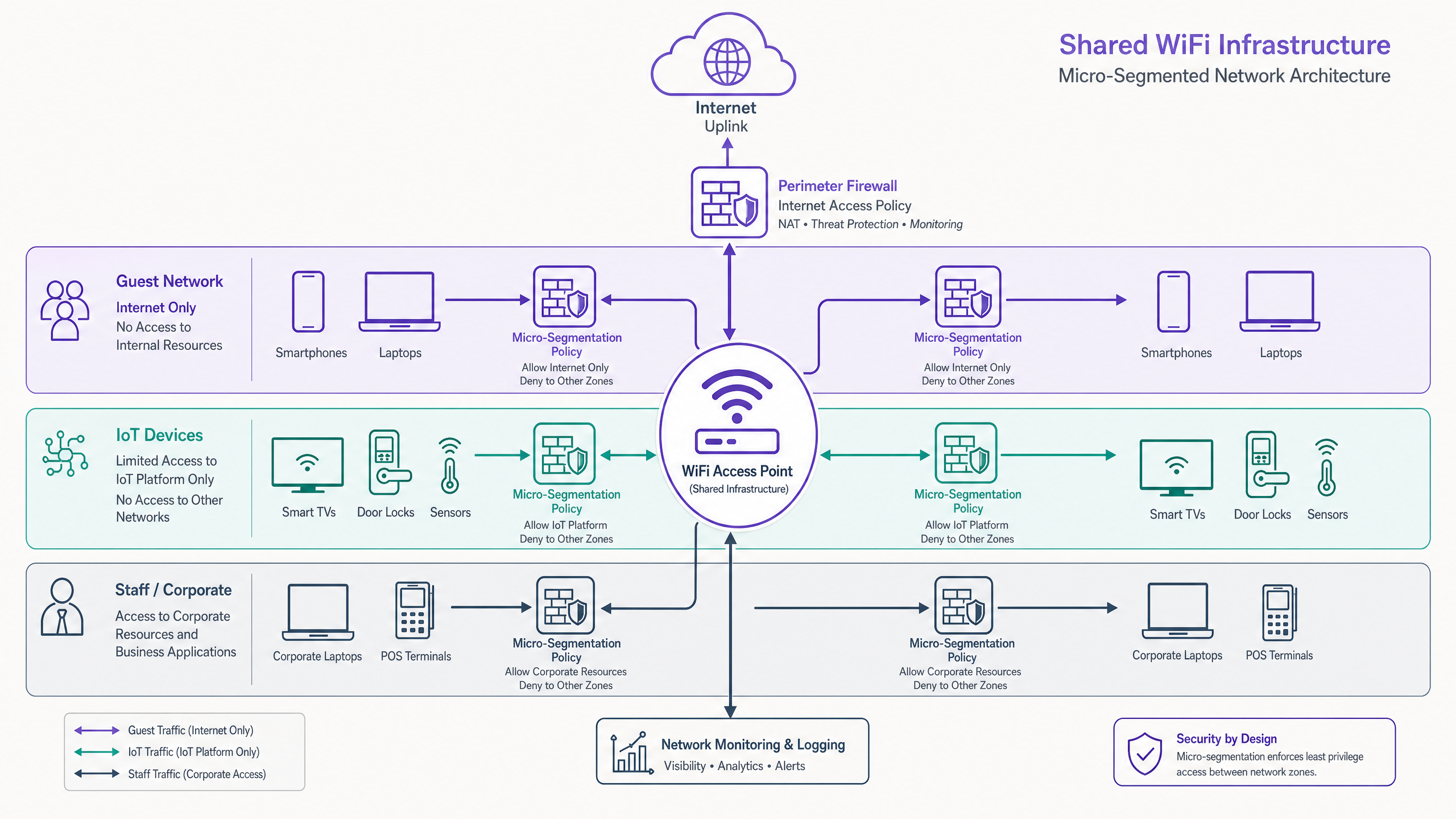
L'exploitation d'une infrastructure WLAN partagée sans micro-segmentation granulaire constitue une vulnérabilité de sécurité importante pour les sites modernes. À mesure que le périmètre se dissout, le réseau interne devient la principale surface d'attaque. Ce guide détaille les principes architecturaux et les méthodologies de déploiement nécessaires pour appliquer une isolation de confiance zéro entre le trafic des invités, les flottes IoT et les terminaux d'entreprise sur une couche d'accès physique unifiée.
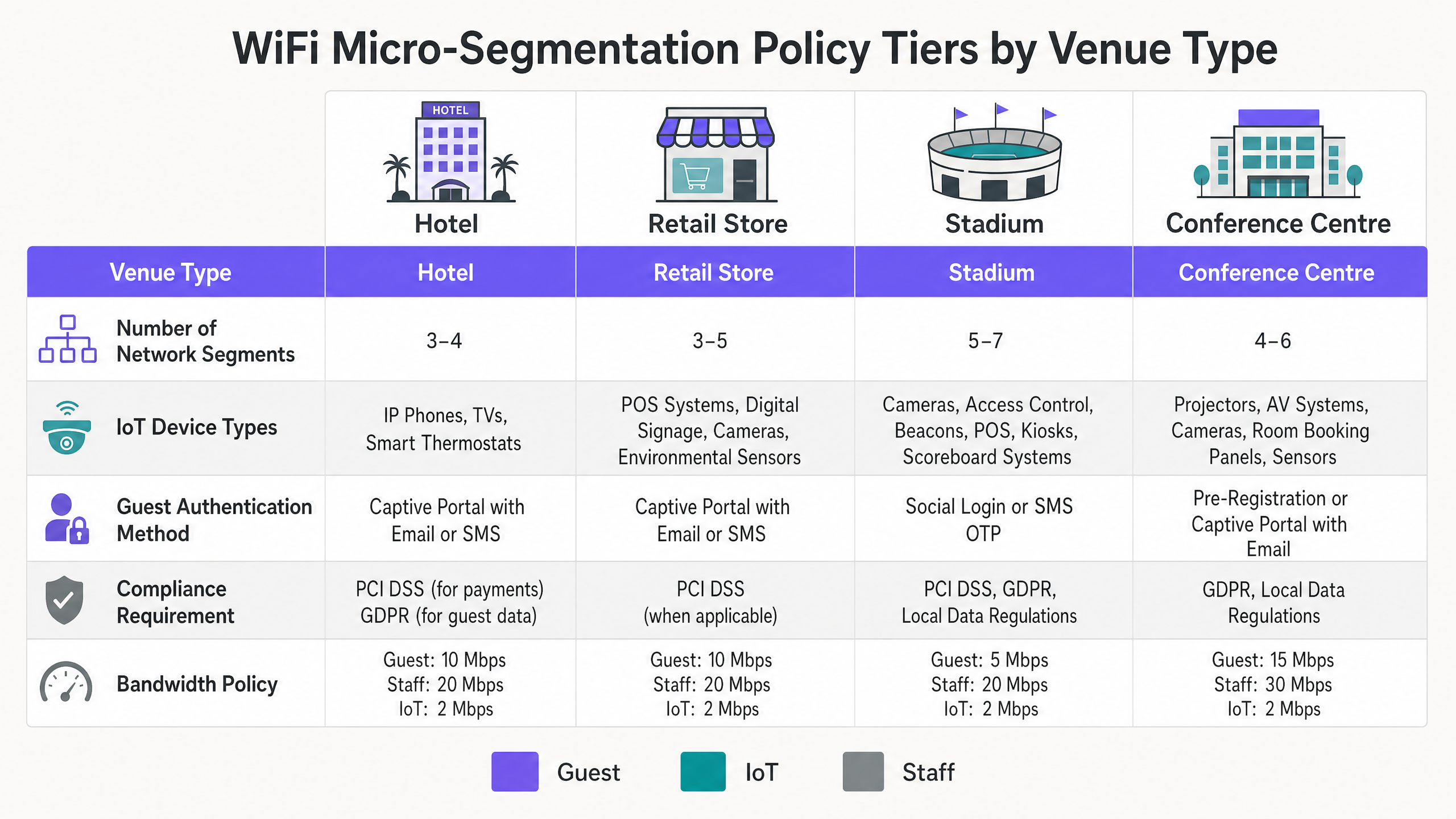
Pour les CTO et les architectes réseau dans l' Hôtellerie , le Commerce de détail , la Santé et le Transport , le mandat est clair : les VLAN traditionnels sont insuffisants. En mettant en œuvre une micro-segmentation dynamique basée sur des politiques, utilisant IEEE 802.1X et RADIUS, les organisations peuvent réduire considérablement leur portée de conformité PCI DSS et GDPR tout en atténuant le risque de mouvement latéral à partir de dispositifs embarqués compromis.
Écoutez le podcast de briefing technique pour un résumé audio :
Approfondissement Technique
La micro-segmentation sur un WLAN partagé exige de dépasser le mappage statique SSID-vers-VLAN. Elle requiert une application dynamique des politiques, basée sur l'identité, à la périphérie.
La Couche d'Authentification : IEEE 802.1X et WPA3
La base d'une segmentation efficace est une authentification robuste. S'appuyer uniquement sur des clés pré-partagées (PSK) sur plusieurs SSIDs donne une illusion de séparation. La véritable micro-segmentation utilise IEEE 802.1X pour authentifier le dispositif ou l'utilisateur auprès d'un backend RADIUS, attribuant dynamiquement le client au VLAN approprié et appliquant des listes de contrôle d'accès (ACL) spécifiques basées sur l'identité.
Pour les déploiements modernes, WPA3 est non négociable. Les réseaux invités devraient utiliser WPA3-Personal avec Simultaneous Authentication of Equals (SAE) pour se protéger contre les attaques par dictionnaire hors ligne, tandis que les segments d'entreprise doivent exiger WPA3-Enterprise (mode 192 bits lorsque le matériel le permet).
Les Trois Segments Clés
Trafic Invité (Non Fiable) : Les invités représentent le segment au volume le plus élevé et à la confiance la plus faible. L'authentification est généralement gérée via un Captive Portal ( WiFi Invité ) utilisant l'e-mail, les SMS ou la connexion sociale. Le contrôle critique ici est l'Isolation Client (isolation de couche 2) pour empêcher la communication de pair à pair entre les appareils invités. Le trafic doit être strictement limité à Internet, avec un filtrage DNS appliqué pour bloquer les domaines malveillants. Consultez notre guide sur Qu'est-ce que le filtrage DNS ? Comment bloquer le contenu nuisible sur le WiFi Invité pour les détails de mise en œuvre.
Appareils IoT (Semi-Fiables, Risque Élevé) : Les appareils IoT — des téléviseurs intelligents aux capteurs CVC — sont connus pour leur mauvaise hygiène de sécurité. Ils doivent résider dans un segment isolé avec des politiques de sortie uniquement. Un appareil IoT ne devrait pouvoir communiquer qu'avec sa plateforme de gestion spécifique. La mise en œuvre de réseaux de suivi ou de capteurs BLE Low Energy Explained for Enterprise nécessite cette isolation stricte pour prévenir les mouvements latéraux.
Personnel et Entreprise (Fiable) : Ce segment gère les données sensibles, y compris les transactions POS et les systèmes RH. L'accès doit nécessiter une authentification mutuelle basée sur des certificats (EAP-TLS). Les appareils d'entreprise doivent être inscrits via MDM, garantissant une connectivité transparente et sécurisée.
Guide d'Implémentation
Le déploiement de la micro-segmentation sur un ensemble de sites distribués nécessite une approche progressive et méthodique.
Phase 1 : Découverte et Audit du Réseau
Vous ne pouvez pas segmenter ce que vous ne voyez pas. Commencez par un audit complet de tous les appareils connectés, en les mappant à leurs niveaux d'accès réseau requis. Utilisez la surveillance des flux (NetFlow/sFlow) pour établir une base de référence des modèles de communication normaux.
Phase 2 : Définition des Politiques
Définissez votre matrice de segmentation. Mappez chaque classe d'appareil à un VLAN spécifique et définissez les règles de routage inter-VLAN. La posture par défaut doit être refuser tout, avec des exceptions d'autorisation explicites uniquement là où c'est strictement nécessaire.
Phase 3 : Configuration de l'Infrastructure
Configurez votre serveur RADIUS pour qu'il renvoie les attributs spécifiques au fournisseur (VSA) corrects pour l'attribution dynamique de VLAN. Assurez-vous que vos points d'accès et commutateurs en amont sont configurés pour étiqueter et tronquer correctement ces VLAN.
Phase 4 : Déploiement Progressif
N'essayez pas une migration « big bang ». Commencez par isoler la flotte IoT — cela offre le retour de sécurité immédiat le plus élevé avec une perturbation minimale pour l'utilisateur. Poursuivez avec le segment invité, et enfin, migrez les appareils d'entreprise vers le segment sécurisé 802.1X.
Bonnes Pratiques
- Appliquer l'Isolation Client : Activez toujours l'isolation client sur les SSIDs invités pour prévenir les attaques latérales entre les appareils non fiables.
- Utiliser l'Attribution Dynamique de VLAN : Éloignez-vous du mappage statique des SSID. Utilisez RADIUS pour attribuer des VLAN en fonction du rôle de l'utilisateur ou du profilage de l'appareil.
- Mettre en Œuvre le Filtrage DNS : Appliquez des politiques de filtrage DNS spécifiques au segment pour prévenir la communication de logiciels malveillants et faire respecter les politiques d'utilisation acceptable.
- Optimiser pour Votre Environnement : Adaptez votre conception RF et votre stratégie de segmentation à votre type de site spécifique. En savoir plus sur Office Wi Fi : Optimisez votre réseau Wi-Fi de bureau moderne et comprenez l'impact des Fréquences Wi Fi : Un guide des fréquences Wi-Fi en 2026 .
- LExploitez l'analyse : Utilisez WiFi Analytics pour surveiller l'utilisation des segments et identifier les comportements anormaux.

Dépannage et atténuation des risques
Le mode de défaillance le plus courant dans les déploiements de micro-segmentation est le routage inter-VLAN mal configuré. Si une règle de pare-feu autorise par inadvertance le trafic entre les segments IoT et d'entreprise, la segmentation est compromise.
Pièges courants :
- Exposition de l'interface de gestion : Laisser les interfaces de gestion des AP ou des commutateurs accessibles depuis les segments invités ou IoT. Le trafic de gestion doit résider sur un VLAN hors bande dédié et hautement restreint.
- Défaillances RADIUS : Un serveur RADIUS mal configuré qui rejette les authentifications 802.1X entraînera une défaillance généralisée de la connectivité pour les appareils d'entreprise. Mettez en œuvre une infrastructure RADIUS redondante.
- Routage asymétrique : Assurez-vous que les chemins de trafic de retour sont correctement définis dans vos politiques de pare-feu pour éviter les pertes de connexion.
ROI et impact commercial
La mise en œuvre d'une micro-segmentation robuste offre une valeur commerciale mesurable :
- Portée de conformité réduite : En isolant cryptographiquement les terminaux POS et les systèmes de paiement, vous réduisez considérablement la portée et le coût des audits PCI DSS.
- Atténuation des risques : Contenir une violation potentielle à un seul segment (par exemple, un lecteur d'affichage numérique compromis) empêche un mouvement latéral catastrophique vers les systèmes d'entreprise centraux.
- Efficacité opérationnelle : L'attribution dynamique de VLAN réduit la charge administrative liée à la configuration manuelle des ports de commutateur et à la gestion de plusieurs SSIDs statiques.
Définitions clés
Micro-Segmentation
The practice of dividing a network into granular, isolated zones to enforce strict security policies and contain potential breaches.
Essential for venue operators running diverse device types (Guest, IoT, Staff) on a single physical network infrastructure.
IEEE 802.1X
A standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The engine for dynamic VLAN assignment and robust corporate device onboarding.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the access point or switch which VLAN a client should be placed in upon successful authentication.
Allows a single SSID to securely serve multiple user roles without static configuration.
Client Isolation
A wireless network feature that prevents connected clients from communicating directly with each other.
A mandatory configuration for any guest WiFi network to prevent peer-to-peer attacks and ensure privacy.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X by using their MAC address as the credential.
Commonly used to onboard headless IoT devices like smart TVs or sensors onto a segmented network.
EAP-TLS
Extensible Authentication Protocol-Transport Layer Security; a highly secure authentication method requiring client and server certificates.
The gold standard for authenticating corporate devices and POS systems to prevent credential theft.
WPA3-Enterprise
The latest WiFi security standard for enterprise networks, offering stronger encryption and robust authentication.
Should be mandated for all new deployments to protect sensitive corporate and staff traffic.
Quality of Service (QoS)
Technologies that manage data traffic to reduce packet loss, latency, and jitter on the network.
Used in conjunction with segmentation to ensure critical applications (like POS) are prioritized over guest or IoT traffic.
Exemples concrets
A 200-room hotel needs to deploy new smart TVs in every guest room, upgrade their POS systems in the restaurant, and provide high-speed guest WiFi, all on the existing physical network infrastructure. How should they architect the segmentation?
- Implement three distinct VLANs: Guest (VLAN 10), IoT (VLAN 20), and Corporate/POS (VLAN 30).
- Configure the APs to broadcast two SSIDs: 'Hotel_Guest' (Open with Captive Portal, mapped to VLAN 10) and 'Hotel_Secure' (802.1X).
- Enable Client Isolation on the 'Hotel_Guest' SSID.
- Use MAC-based RADIUS authentication (MAB) for the Smart TVs to dynamically assign them to VLAN 20.
- Use EAP-TLS certificate authentication for the POS terminals to assign them to VLAN 30.
- Configure the perimeter firewall to deny all inter-VLAN traffic, permitting VLAN 10 and 20 internet-only access, and restricting VLAN 30 to the corporate VPN tunnel.
A large retail chain is experiencing network congestion and suspects their digital signage media players (IoT) are saturating the uplink, impacting the performance of their mobile POS tablets.
- Audit the current network configuration to confirm if digital signage and POS tablets share the same segment.
- Implement micro-segmentation by moving the digital signage players to a dedicated IoT VLAN.
- Apply Quality of Service (QoS) policies at the access switch or AP level: rate-limit the IoT VLAN to 5 Mbps per device, and prioritize traffic from the POS VLAN.
- Ensure the IoT VLAN has a strict egress-only firewall policy to the specific content delivery network (CDN) used by the signage vendor.
Questions d'entraînement
Q1. You are deploying a new WiFi network for a large conference centre. The venue requires a public guest network, a dedicated network for AV equipment (projectors, digital signage), and a secure network for venue staff. You have been instructed to minimize the number of broadcasted SSIDs. How do you architect the wireless access layer?
Conseil : Consider how different device types authenticate and how RADIUS can dynamically assign VLANs.
Voir la réponse type
Broadcast two SSIDs. SSID 1 ('Conference_Guest'): Open network with a captive portal for guest access, mapped to a Guest VLAN with client isolation and internet-only firewall rules. SSID 2 ('Conference_Secure'): 802.1X enabled. Venue staff authenticate via EAP-TLS (certificates) and are dynamically assigned to the Staff VLAN. AV equipment authenticates via MAC Authentication Bypass (MAB) against the RADIUS server and is dynamically assigned to the isolated AV/IoT VLAN.
Q2. During a security audit, a penetration tester successfully compromises a smart thermostat in the hotel lobby. From the thermostat, they are able to access the hotel's reservation database server. What architectural failure allowed this, and how should it be remediated?
Conseil : Consider inter-VLAN routing policies and the principle of least privilege.
Voir la réponse type
The architectural failure is a lack of micro-segmentation and permissive inter-VLAN routing. The IoT device (thermostat) was either placed on the same VLAN as the corporate servers, or the firewall separating the VLANs allowed inbound traffic from the IoT segment to the corporate segment. Remediation: Move all thermostats to a dedicated IoT VLAN. Configure the perimeter firewall with a default-deny policy between VLANs. The IoT VLAN should only be permitted egress traffic to the specific cloud controller required for the thermostats, with no access to internal corporate resources.
Q3. A retail client complains that their guest WiFi is extremely slow during peak hours, and they notice that the POS systems are also experiencing latency. Both are running on the same physical access points. What is the most likely cause, and what are the recommended steps to resolve it?
Conseil : Think about bandwidth contention and traffic prioritization.
Voir la réponse type
The likely cause is bandwidth contention on the shared uplink, with guest traffic saturating the connection and impacting critical POS traffic. Resolution: Implement Quality of Service (QoS) and rate-limiting. 1. Ensure POS and Guest traffic are on separate VLANs. 2. Apply a rate-limit policy to the Guest VLAN (e.g., 5 Mbps per client) to prevent any single guest from hogging bandwidth. 3. Configure QoS rules on the switch and firewall to prioritize traffic originating from the POS VLAN over the Guest VLAN.