DNS Over HTTPS (DoH) : Implications pour le filtrage du WiFi public
Ce guide de référence technique explique comment le DNS over HTTPS (DoH) contourne le filtrage de contenu traditionnel sur le port 53 des réseaux WiFi publics. Il fournit des stratégies d'atténuation concrètes et neutres vis-à-vis des fournisseurs pour les architectes réseau et les responsables informatiques afin de retrouver de la visibilité, d'assurer la conformité et de sécuriser l'accès invité dans les environnements d'entreprise.
Écouter ce guide
Voir la transcription du podcast
- Résumé Exécutif
- Approfondissement technique : Le mécanisme de contournement DoH
- Modèles d'implémentation : DoH au niveau de l'application vs. au niveau du système d'exploitation
- Guide d'implémentation : Une architecture de défense en profondeur
- Couche 1 : Bloquer les points de terminaison des résolveurs DoH connus
- Couche 2 : Appliquer l'interception et la redirection du port 53
- Couche 3 : Bloquer le port 853 (DNS over TLS)
- Bonnes pratiques et considérations de conformité
- Dépannage et atténuation des risques
- Règles d'interception incomplètes
- Omissions IPv6
- Dysfonctionnement des applications
- ROI et impact commercial
Résumé Exécutif
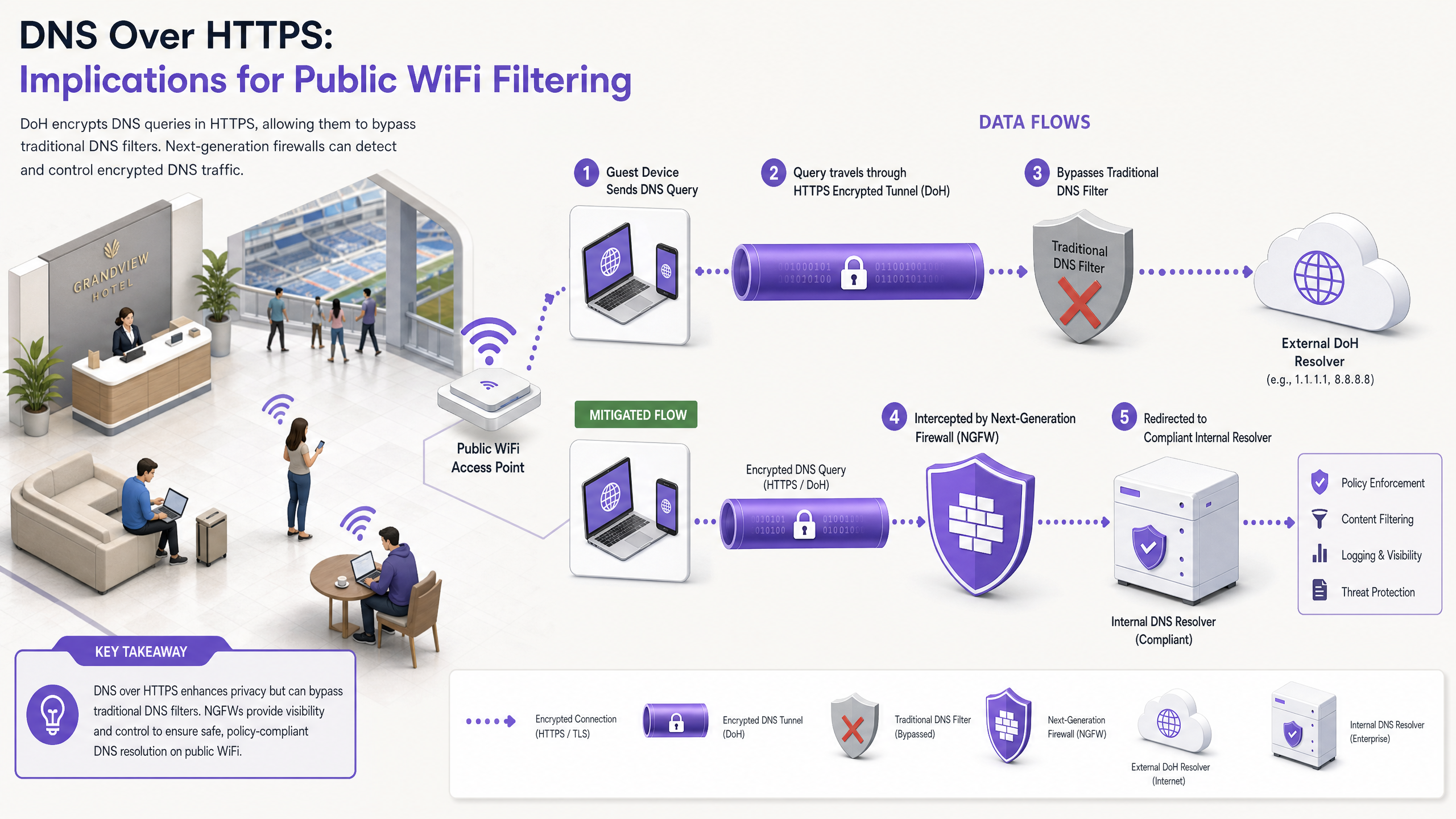
Pendant près d'une décennie, le filtrage DNS traditionnel sur le port 53 a servi de mécanisme principal pour appliquer les politiques de contenu et atténuer les menaces de logiciels malveillants sur les réseaux WiFi publics. Cependant, l'adoption généralisée du DNS over HTTPS (DoH) par les navigateurs et systèmes d'exploitation grand public perturbe fondamentalement ce modèle. En encapsulant les requêtes DNS dans le trafic HTTPS standard sur le port 443, le DoH rend ces requêtes invisibles aux techniques d'interception réseau traditionnelles.
Pour les responsables informatiques d'entreprise et les architectes réseau gérant le WiFi invité dans les secteurs de l' Hôtellerie , du Commerce de détail , les stades et les lieux du secteur public, cela représente une lacune importante en matière de conformité et de sécurité. Lorsque les appareils invités contournent silencieusement les résolveurs DNS désignés du lieu, les politiques d'utilisation acceptable soigneusement élaborées échouent, exposant le réseau au trafic de logiciels malveillants de commande et contrôle (C2) et à du contenu inapproprié. Ce guide détaille les mécanismes du vecteur de contournement DoH et propose une architecture de défense en profondeur à plusieurs couches pour retrouver la visibilité du réseau, assurer la conformité réglementaire et maintenir une sécurité robuste du WiFi invité .
Approfondissement technique : Le mécanisme de contournement DoH
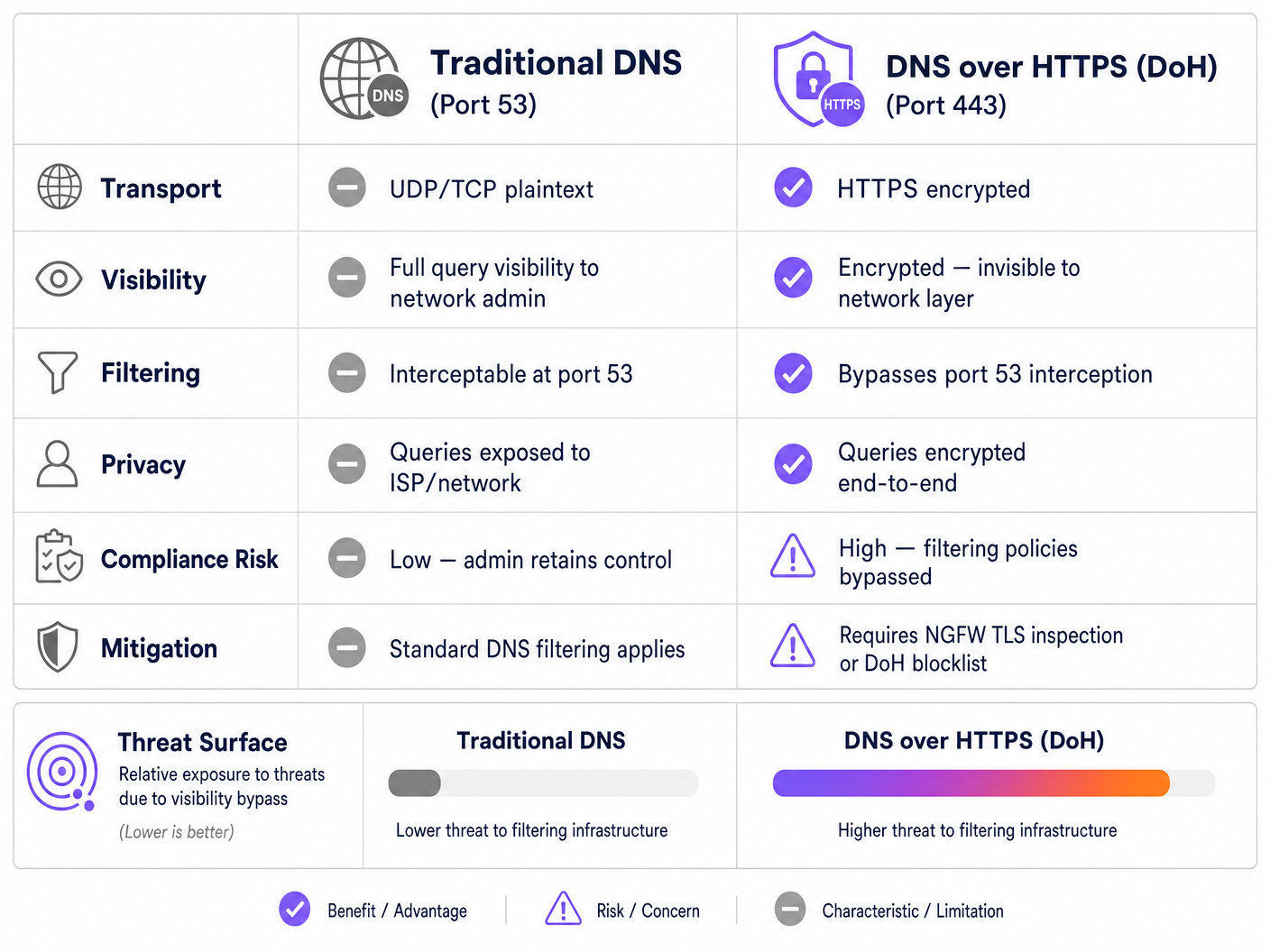
Pour comprendre le vecteur de menace DoH, il faut d'abord examiner l'architecture de base du filtrage DNS traditionnel. Historiquement, lorsqu'un appareil invité se connectait à un réseau public et demandait un domaine, la requête était transmise en texte clair sur le port UDP ou TCP 53. Les administrateurs réseau pouvaient facilement intercepter ce trafic au niveau du pare-feu ou du contrôleur sans fil, le redirigeant vers un résolveur DNS conforme qui vérifiait le domaine demandé par rapport aux flux de renseignement sur les menaces et aux politiques de catégorisation de contenu.
Le DNS over HTTPS contourne l'intégralité de ce plan de contrôle. Par conception, le DoH chiffre la requête DNS et la transmet à un résolveur externe (tel que 1.1.1.1 de Cloudflare ou 8.8.8.8 de Google) en utilisant le chiffrement TLS standard sur le port 443. Du point de vue de l'infrastructure réseau du lieu, une requête DoH est indiscernable d'un utilisateur naviguant sur un site web sécurisé ou diffusant une vidéo.
Modèles d'implémentation : DoH au niveau de l'application vs. au niveau du système d'exploitation
Le défi pour les administrateurs réseau est aggravé par la manière dont le DoH est implémenté sur différentes plateformes. Il existe deux principaux modèles de déploiement :
- DoH au niveau de l'application : Dans ce modèle, l'application gère sa propre configuration DoH indépendamment du système d'exploitation hôte. Mozilla Firefox en est l'exemple canonique ; lorsque le DoH est activé, Firefox ignore les serveurs DNS attribués par DHCP et achemine toutes les requêtes vers son fournisseur DoH préféré. Les règles d'interception du port 53 du lieu sont entièrement contournées.
- DoH au niveau du système d'exploitation (opportuniste) : Les systèmes d'exploitation modernes, y compris Windows 11 et Android, utilisent le DoH opportuniste. Le système d'exploitation vérifie si le résolveur DNS attribué par DHCP possède un point de terminaison DoH connu. Si une correspondance est trouvée, le système d'exploitation met automatiquement à niveau la connexion vers le DoH. Bien que cela préserve le choix du résolveur par l'administrateur, cela déplace toujours le trafic vers le port 443, ce qui peut contourner les outils de surveillance hérités qui s'attendent à du trafic sur le port 53.
De plus, les administrateurs doivent prendre en compte le DNS over TLS (DoT), qui fonctionne sur le port 853. Bien que le DoT soit plus facile à bloquer en raison de son port dédié, il s'agit de la norme par défaut pour la fonction "DNS privé" d'Android et représente un risque de contournement identique si le port 853 est laissé ouvert sur le VLAN invité.
Guide d'implémentation : Une architecture de défense en profondeur
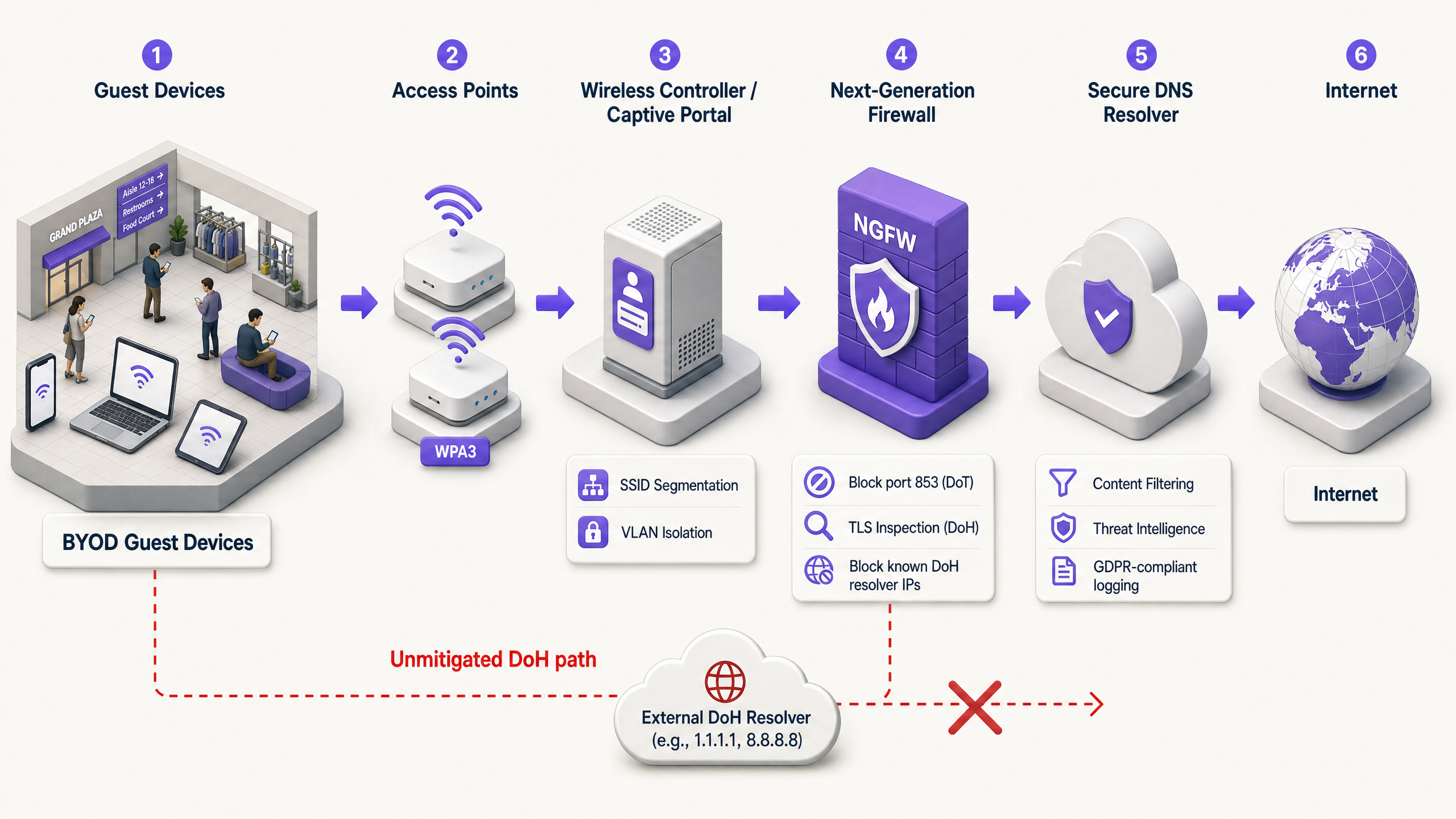
Reprendre le contrôle de la résolution DNS nécessite une stratégie d'atténuation multicouche. S'appuyer sur un seul point de contrôle est insuffisant face aux protocoles modernes et chiffrés. Les architectes réseau devraient implémenter l'architecture suivante pour sécuriser l'accès invité et assurer la conformité avec des cadres tels que PCI DSS et GDPR.
Couche 1 : Bloquer les points de terminaison des résolveurs DoH connus
L'atténuation la plus immédiate et la plus efficace consiste à bloquer le trafic HTTPS sortant vers les résolveurs DoH publics connus à la périphérie du réseau. Bien que le trafic DoH se confonde avec le HTTPS standard, les adresses IP de destination et les domaines des principaux fournisseurs DoH sont bien documentés.
En configurant le pare-feu de nouvelle génération (NGFW) pour abandonner les connexions vers ces points de terminaison spécifiques (par exemple, dns.google, cloudflare-dns.com), les administrateurs forcent l'échec de la résolution DoH de l'appareil client. Dans la plupart des implémentations, lorsque le DoH échoue, le client revient gracieusement au DNS traditionnel non chiffré sur le port 53, qui peut alors être intercepté et filtré.
Note d'implémentation : Cette approche nécessite de maintenir une liste de blocage à jour. Les fournisseurs de pare-feu d'entreprise proposent souvent des flux de menaces dynamiques qui mettent automatiquement à jour les points de terminaison DoH connus, réduisant considérablement les frais généraux d'exploitation.
Couche 2 : Appliquer l'interception et la redirection du port 53
Le blocage du DoH n'est efficace que si le trafic de repli est correctement géré. Le réseau doit être configuré pour intercepter tout le trafic UDP et TCP sortant sur le port 53 provenant du VLAN invité. Ce trafic doit être redirigé de force (via des règles NAT/de redirection de port) vers le résolveur DNS approuvé et conforme du lieu.
Cette étape est cruciale car de nombreux appareils ou applications malveillantes codent en dur des serveurs DNS publics (par exemple, 8.8.8.8) dans leur pile réseau, ignorant les paramètres fournis par DHCP. Sans interception forcée, ces appareils contourneront avec succès les politiques de filtrage du lieu même si le DoH est bloqué.
Couche 3 : Bloquer le port 853 (DNS over TLS)
Pour contrer le vecteur de contournement DoT, les administrateurs doivent explicitement bloquer le trafic sortant sur le port TCP 853 depuis le réseau invité. Similaire à l'atténuation du DoH, le blocking DoT force les appareils Android et autres clients compatibles DoT à revenir au DNS standard sur le port 53.
Bonnes pratiques et considérations de conformité
La mise en œuvre de l'atténuation du DoH n'est pas seulement un exercice technique ; c'est une exigence fondamentale pour maintenir la conformité réglementaire et appliquer les politiques d'utilisation acceptable.
- Documentation des politiques : Assurez-vous que les conditions générales du Captive Portal du lieu indiquent explicitement que le filtrage DNS est en place à des fins de sécurité et de conformité. Cela offre une défense juridique en vertu du GDPR et de la loi britannique sur la sécurité en ligne (Online Safety Act) lors du blocage des protocoles DNS chiffrés.
- Segmentation du réseau : Le WiFi invité doit être strictement isolé des réseaux d'entreprise et de paiement à l'aide de VLAN et de règles de pare-feu. Il s'agit d'une exigence fondamentale de la norme PCI DSS v4.0, qui impose également une surveillance robuste du trafic réseau – une surveillance impossible si le DoH est autorisé à contourner les contrôles de sécurité.
- Surveillance continue : Tirez parti des capacités de reporting de votre service de filtrage DNS d'entreprise pour surveiller les volumes de requêtes et identifier les schémas anormaux. Une chute soudaine du trafic sur le port 53 provenant d'un sous-réseau spécifique indique souvent qu'un nouveau résolveur DoH non bloqué est utilisé par les appareils clients.
- Intégration avec l'analyse : Lors de la mise en œuvre d'un accès invité sécurisé, examinez comment le flux d'authentification s'intègre aux objectifs commerciaux plus larges. L'utilisation d'un assistant Wi-Fi pour une authentification sécurisée basée sur le profil garantit que les utilisateurs se connectent en toute sécurité tout en permettant au lieu de tirer parti de WiFi Analytics pour comprendre l'affluence et les temps de présence, de manière similaire à la façon dont le Mode Cartes Hors Ligne améliore l'expérience visiteur.
Dépannage et atténuation des risques
Lors du déploiement de l'atténuation du DoH, les équipes réseau rencontrent souvent des modes de défaillance spécifiques. Anticiper ces problèmes réduit les temps d'arrêt et les frictions pour les invités.
Règles d'interception incomplètes
La défaillance de déploiement la plus courante est l'interception incomplète du port 53. Les administrateurs peuvent configurer le serveur DHCP pour distribuer les bonnes adresses IP DNS, mais ne parviennent pas à implémenter les règles NAT du pare-feu nécessaires pour intercepter les requêtes DNS codées en dur. Atténuation : Testez toujours le déploiement en configurant un appareil client avec un serveur DNS statique externe (par exemple, 9.9.9.9) et en vérifiant que les requêtes sont toujours acheminées avec succès vers le service de filtrage du lieu.
Omissions IPv6
À mesure que les réseaux passent à des configurations dual-stack, les règles de pare-feu sont souvent écrites exclusivement pour IPv4. Si les listes de blocage DoH et les règles d'interception du port 53 ne couvrent pas IPv6, les appareils modernes contourneront sans problème les contrôles IPv4 en utilisant leur pile IPv6. Atténuation : Assurez-vous que toutes les listes de blocage DoH, les règles de redirection du port 53 et les règles de suppression du port 853 sont appliquées symétriquement sur les tables de routage IPv4 et IPv6.
Dysfonctionnement des applications
Un blocage DoH agressif peut occasionnellement entraîner le dysfonctionnement de certaines applications mobiles qui s'appuient exclusivement sur leur propre implémentation DoH et refusent de revenir au DNS standard. Atténuation : Maintenez un processus d'exception documenté. Si une application critique pour l'entreprise tombe en panne, utilisez l'inspection TLS (si disponible sur le NGFW) pour autoriser sélectivement le trafic DoH vers le résolveur de cette application spécifique, plutôt que d'ouvrir le DoH globalement.
ROI et impact commercial
L'analyse de rentabilisation d'une atténuation robuste du DoH repose sur l'évitement des risques et l'assurance de la conformité. Un seul incident – tel qu'un invité accédant à du contenu illégal entraînant une enquête réglementaire, ou un appareil IoT compromis établissant une connexion C2 via DoH – peut entraîner des coûts qui dépassent de loin le temps d'ingénierie nécessaire pour mettre en œuvre des contrôles appropriés.
Pour une entreprise opérant sur plusieurs sites, la standardisation de l'architecture d'atténuation du DoH garantit une application cohérente des politiques. Cette standardisation réduit la charge opérationnelle du service d'assistance informatique, car les avis d'abus des FAI tombent à zéro et les performances du réseau sont préservées en bloquant le contenu inapproprié à large bande passante. En fin de compte, la sécurisation de la couche DNS garantit que l'investissement du lieu dans le WiFi invité reste un actif sûr et conforme plutôt qu'une responsabilité.
Définitions clés
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System (DNS) resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
When IT teams deploy content filtering, DoH acts as a bypass mechanism, hiding DNS queries within standard encrypted web traffic.
DNS over TLS (DoT)
A security protocol for encrypting and wrapping DNS queries and answers via the Transport Layer Security (TLS) protocol, operating on a dedicated port (853).
Often enabled by default on modern Android devices (Private DNS), DoT must be blocked at the firewall to ensure queries fall back to the venue's filtered DNS.
Opportunistic DoH
A behavior where an operating system or browser automatically upgrades standard DNS queries to DoH if it detects that the configured DNS resolver supports the encrypted protocol.
This feature, common in Windows 11 and Chrome, means that even if a venue assigns a standard DNS IP, the traffic may still shift to encrypted port 443, bypassing legacy monitoring.
Port 53 Interception
A network firewall configuration that captures all outbound traffic on UDP/TCP port 53 and forcibly redirects it to a designated DNS resolver, regardless of the destination IP requested by the client.
Essential for capturing DNS queries from devices with hardcoded DNS settings or those that have fallen back from a failed DoH connection.
Next-Generation Firewall (NGFW)
A network security device that provides capabilities beyond a traditional, stateful firewall, including deep packet inspection, application awareness, and TLS/SSL decryption.
NGFWs are critical for DoH mitigation as they can identify and block DoH traffic based on application signatures rather than just IP addresses.
Fallback Behavior
The programmed response of a client device when its preferred encrypted DNS protocol (DoH or DoT) fails to connect, typically resulting in the device reverting to standard, unencrypted DNS.
Network architects rely on this behavior; by intentionally breaking DoH/DoT connections, they force the device to use the interceptable port 53.
Command-and-Control (C2)
The infrastructure used by attackers to communicate with compromised devices (malware/botnets) within a target network.
Modern malware increasingly uses DoH to hide C2 communications from enterprise network monitors, making DoH mitigation a critical security requirement.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The captive portal is the legally appropriate location to inform users that their DNS traffic is being filtered and that encrypted DNS protocols are blocked.
Exemples concrets
A 400-room hotel recently deployed a cloud-based DNS filtering service to comply with brand standards regarding family-friendly content. However, the IT manager notices that a significant portion of guest traffic is still reaching adult content sites, and the DNS filtering dashboard shows lower-than-expected query volumes. How should the network architect remediate this bypass?
- Audit Firewall Rules: The architect must first verify that outbound TCP/UDP port 53 is being intercepted and NAT-redirected to the cloud DNS service.
- Block DoH Resolvers: Implement an NGFW blocklist to drop outbound HTTPS (port 443) traffic destined for known DoH providers (e.g., Cloudflare, Google, Quad9).
- Block DoT: Add a firewall rule to drop all outbound TCP port 853 traffic to prevent Android Private DNS bypass.
- Verify IPv6: Ensure all the above rules are applied to both IPv4 and IPv6 traffic.
A retail chain with 150 locations needs to implement DNS filtering to block malware and phishing on their guest WiFi. They use basic branch firewalls without advanced TLS inspection capabilities. How can they effectively mitigate DoH without upgrading their hardware?
Without TLS inspection, the chain must rely on robust routing and blocklists.
- Deploy a dynamic DoH IP/Domain blocklist on the branch firewalls, configured to update automatically via an external threat feed.
- Implement strict port 53 NAT redirection to the enterprise DNS filter.
- Block port 853 entirely.
- Update the captive portal Terms of Service to explicitly state that encrypted DNS protocols are blocked to enforce network security policies.
Questions d'entraînement
Q1. A stadium network engineer configures the DHCP server to provide the IP address of their secure, filtered DNS service to all guest devices. However, testing reveals that devices with manually configured DNS settings (e.g., 8.8.8.8) are successfully bypassing the filter. What is the most appropriate architectural fix?
Conseil : Consider the difference between suggesting a route and enforcing a route at the network edge.
Voir la réponse type
The engineer must implement a NAT port forwarding rule on the stadium's firewall. This rule should intercept all outbound UDP and TCP traffic on port 53 originating from the guest VLAN and forcibly translate the destination IP to the secure DNS service's IP address. This ensures that regardless of the client's local configuration, the traffic is routed through the filtering policy.
Q2. Following the implementation of a strict DoH blocklist, the IT helpdesk at a conference centre receives reports that a specific, bespoke event management app is failing to load for attendees. Packet capture shows the app is attempting to use its own hardcoded DoH resolver, which is being blocked, and the app refuses to fall back to standard DNS. How should this be resolved?
Conseil : Balance security policy with business continuity. Can the firewall distinguish between general DoH traffic and traffic to a specific, approved endpoint?
Voir la réponse type
The administrator should create an exception in the NGFW policy. Rather than disabling the DoH blocklist globally, they should identify the specific IP address or domain of the DoH resolver used by the event management app and whitelist it. If the firewall supports application-layer (Layer 7) inspection, a more robust solution is to create a policy that permits DoH traffic only if the destination matches the approved application's infrastructure, ensuring general DoH bypass attempts remain blocked.
Q3. A public sector organisation is auditing its guest WiFi compliance. They have successfully blocked port 853 (DoT) and implemented port 53 interception. However, they lack the budget for an NGFW with advanced TLS inspection or dynamic DoH blocklists. What is the most effective remaining strategy to mitigate DoH?
Conseil : If dynamic lists aren't available, how can you address the vast majority of opportunistic DoH traffic?
Voir la réponse type
The organisation should implement a static blocklist on their existing firewall, targeting the IP addresses and domains of the most common public DoH providers (e.g., Cloudflare, Google, Quad9). While this requires manual maintenance and won't catch obscure DoH resolvers, research shows that the vast majority of DoH traffic defaults to a handful of major providers. This provides a highly effective '80/20' solution within their budget constraints.