eduroam et 802.1X : Authentification WiFi sécurisée pour l'enseignement supérieur
Ce guide de référence technique faisant autorité explique l'architecture, le déploiement et la sécurité de l'authentification eduroam et 802.1X. Conçu pour les responsables informatiques et les architectes réseau, il couvre les étapes de mise en œuvre pratiques, la sélection des méthodes EAP et la manière dont les opérateurs de sites peuvent prendre en charge en toute sécurité l'itinérance académique.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Résumé Exécutif
- Plongée Technique : 802.1X et l'Architecture eduroam
- Le Triangle 802.1X
- La Hiérarchie de Proxy RADIUS eduroam
- Méthodes EAP : Sécurité vs. Déployabilité
- Guide d'Implémentation
- 1. Préparation de l'Infrastructure
- 2. Gestion des Certificats
- 3. Configuration du client (L'outil CAT)
- 4. Attribution et segmentation des VLAN
- Bonnes pratiques et recommandations neutres vis-à-vis des fournisseurs
- Dépannage et atténuation des risques
- ROI et impact commercial

Résumé Exécutif
Pour les établissements d'enseignement supérieur et les sites qui accueillent leurs étudiants et leur personnel, fournir une connectivité sans fil sécurisée et transparente n'est plus un luxe, c'est un impératif opérationnel. La norme pour cette connectivité est eduroam, un service d'itinérance mondial basé sur le cadre IEEE 802.1X.
Ce guide fournit aux responsables informatiques, aux architectes réseau et aux directeurs des opérations de sites une référence complète et neutre vis-à-vis des fournisseurs pour comprendre, déployer et dépanner 802.1X et eduroam. Nous allons au-delà des modèles théoriques de base pour aborder les réalités pratiques du WiFi de campus d'entreprise, y compris la gestion des certificats, l'architecture de proxy RADIUS et l'intégration avec des stratégies de réseau invité plus larges.
Que vous mettiez à niveau un réseau universitaire vieillissant ou que vous configuriez un centre de conférence pour accueillir des visiteurs universitaires, la mise en œuvre correcte de 802.1X atténue les risques de sécurité importants — en particulier le vol d'identifiants — tout en réduisant considérablement les frais de support. Pour les sites en dehors de l'enseignement supérieur traditionnel, la compréhension de ces normes est essentielle pour évaluer les fédérations d'itinérance commerciales comme OpenRoaming, qui partagent la même architecture sous-jacente.
Plongée Technique : 802.1X et l'Architecture eduroam
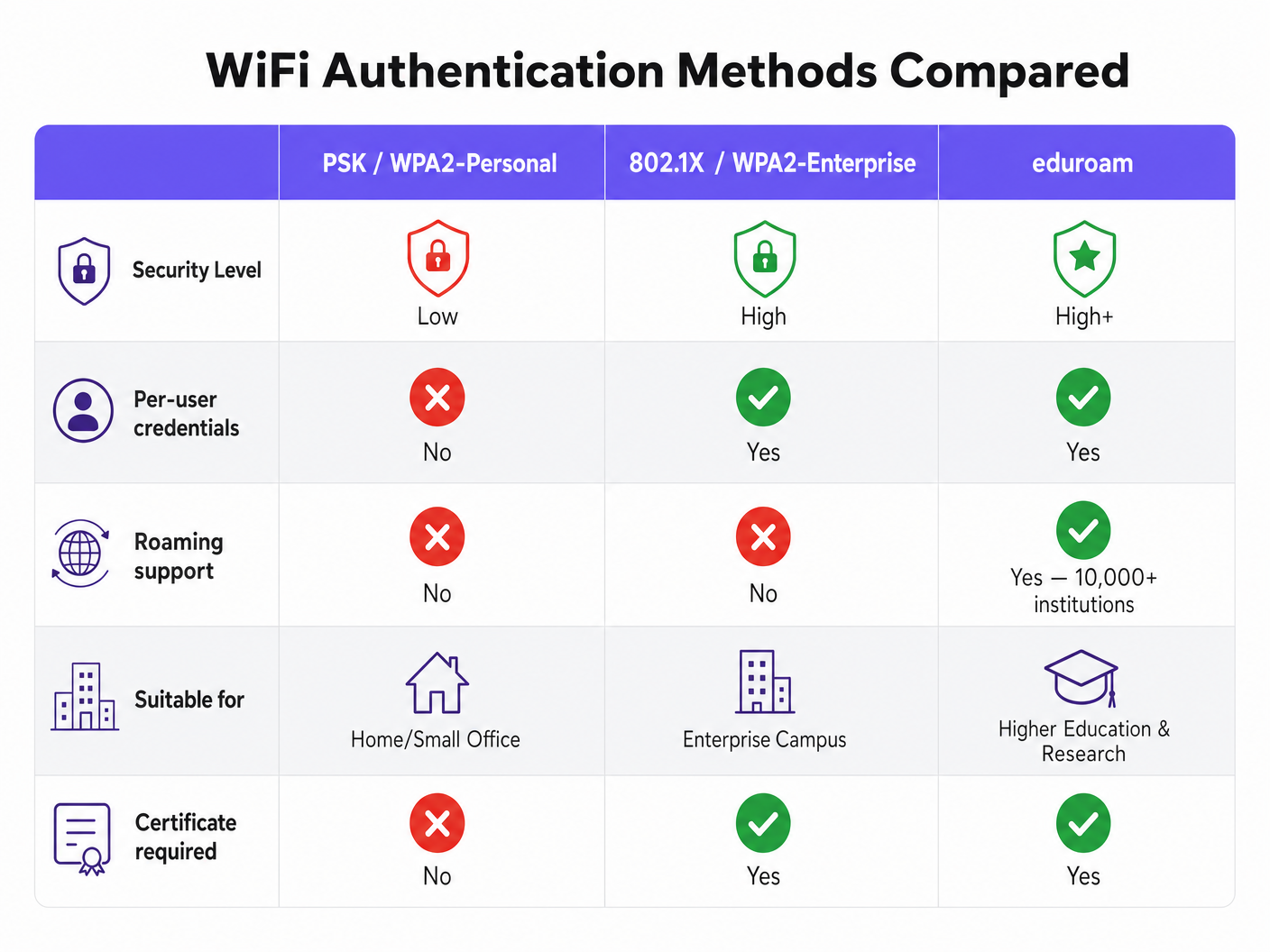
À la base, eduroam est une implémentation de l'IEEE 802.1X, la norme pour le contrôle d'accès réseau basé sur les ports. Bien que conçu à l'origine pour les réseaux câblés, 802.1X constitue le fondement de la sécurité WPA2-Enterprise et WPA3-Enterprise.
Le Triangle 802.1X
Le cadre 802.1X repose sur trois composants distincts interagissant pour autoriser l'accès :
- Demandeur : L'appareil client (par exemple, l'ordinateur portable ou le smartphone d'un étudiant) demandant l'accès au réseau.
- Authentificateur : L'appareil d'accès réseau (par exemple, un point d'accès sans fil ou un commutateur géré). Il agit comme un gardien, bloquant tout le trafic sauf les messages d'authentification jusqu'à ce que l'appareil soit autorisé.
- Serveur d'Authentification : Le système backend qui valide les identifiants, presque universellement un serveur RADIUS (Remote Authentication Dial-In User Service).
Lorsqu'un appareil se connecte, l'Authentificateur établit un port contrôlé. Il transmet les messages du protocole d'authentification extensible (EAP) entre le Demandeur et le Serveur d'Authentification. Si les identifiants sont valides, le serveur renvoie un message RADIUS Access-Accept, et l'Authentificateur ouvre le port pour le trafic IP standard.
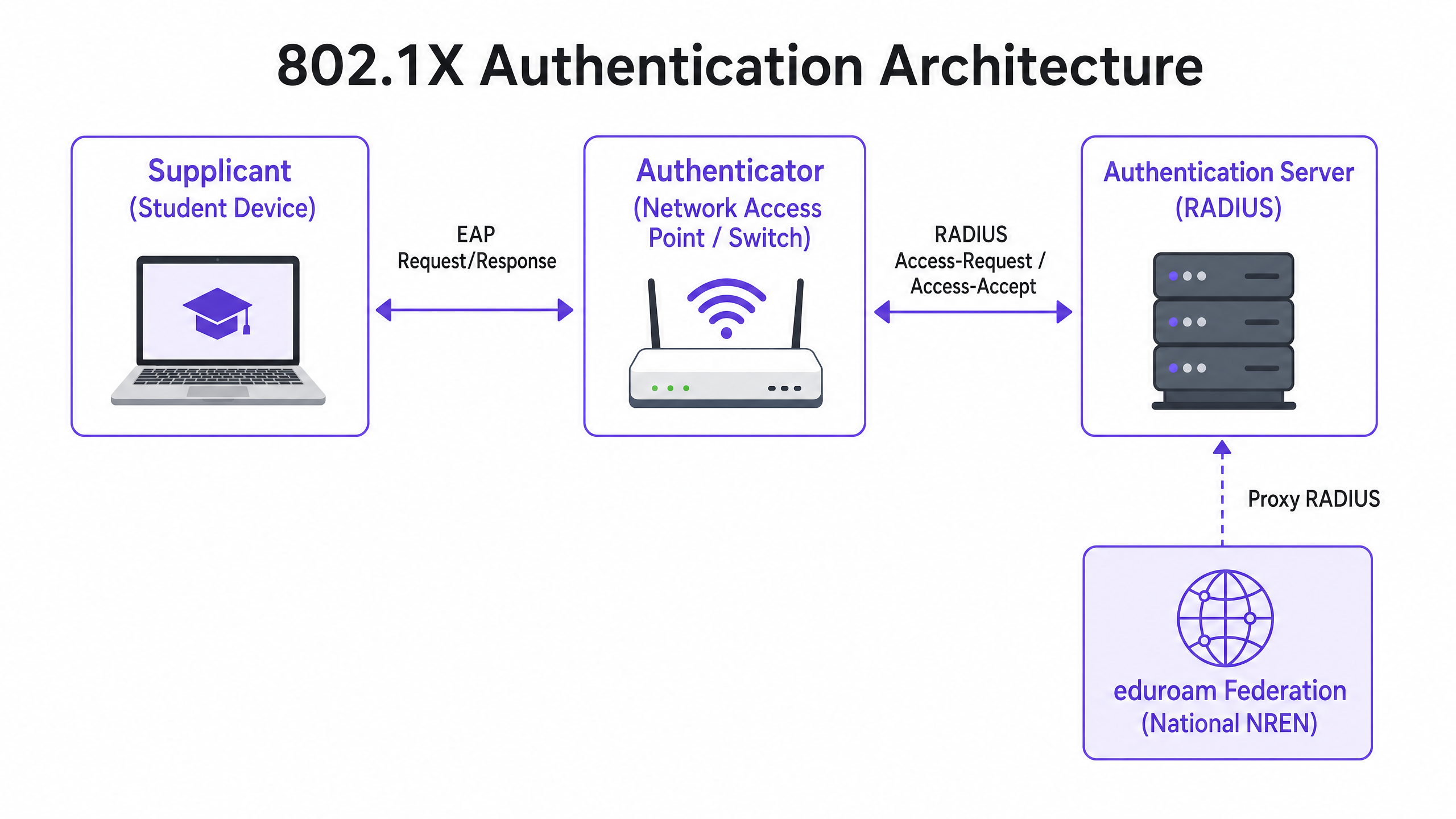
La Hiérarchie de Proxy RADIUS eduroam
Ce qui rend eduroam unique est son architecture fédérée. Il permet aux utilisateurs de s'authentifier auprès de toute institution participante en utilisant leurs identifiants d'origine, sans que l'institution hôte n'ait besoin d'une copie de ces identifiants.
Ceci est réalisé grâce à une chaîne de proxy RADIUS hiérarchique. Lorsqu'un utilisateur de username@university.ac.uk se connecte au SSID eduroam sur un site hôte :
- L'appareil de l'utilisateur envoie une demande d'authentification au format
username@university.ac.uk. - Le serveur RADIUS du site hôte examine le domaine (la partie après l'« @ »). Le reconnaissant comme un domaine externe, il transmet la requête au serveur RADIUS national de niveau supérieur (exploité par le Réseau National de Recherche et d'Éducation, ou NREN).
- Le serveur national achemine la requête vers le serveur RADIUS de l'institution d'origine (
university.ac.uk). - L'institution d'origine valide les identifiants et renvoie un message
Access-AcceptouAccess-Rejectle long de la chaîne.
L'ensemble de ce processus se déroule généralement en moins de deux secondes. Il est crucial de noter que le mot de passe de l'utilisateur n'est jamais exposé à l'institution hôte ou aux proxys intermédiaires ; il est protégé au sein d'un tunnel EAP chiffré établi directement entre le demandeur et le serveur RADIUS d'origine.
Méthodes EAP : Sécurité vs. Déployabilité
Le choix de la méthode EAP dicte la manière dont le tunnel chiffré est formé et dont les identifiants sont échangés. La définition du service de politique eduroam restreint fortement les méthodes autorisées pour garantir la sécurité.
- PEAP (Protected EAP) : Le déploiement le plus courant. Il établit un tunnel TLS à l'aide d'un certificat côté serveur sur le serveur RADIUS. Le client s'authentifie ensuite à l'intérieur de ce tunnel, généralement en utilisant MSCHAPv2 (nom d'utilisateur et mot de passe). Il est relativement facile à déployer mais vulnérable aux attaques de points d'accès non autorisés si les clients ne sont pas configurés pour valider strictement le certificat du serveur.
- EAP-TLS : La référence en matière de sécurité. Il nécessite une authentification mutuelle, ce qui signifie que le serveur RADIUS et l'appareil client doivent présenter des certificats valides. Bien qu'il soit immunisé contre le phishing d'identifiants, il nécessite une infrastructure à clé publique (PKI) robuste pour émettre et gérer les certificats clients, ce qui le rend plus complexe à déployer à grande échelle.
Guide d'Implémentation
Le déploiement de 802.1X et eduroam nécessite une coordination minutieuse entre l'infrastructure réseau, la gestion des identités et la configuration des clients.
1. Préparation de l'Infrastructure
Assurez-vous que vos points d'accès sans fil et contrôleurs prennent en charge WPA2-Enterprise/WPA3-Enterprise et 802.1X. Tout matériel moderne de qualité entreprise (Cisco, Aruba, Juniper, etc.) répondra à cette exigence. Vous devez également déployer une infrastructure RADIUS robuste (par exemple, FreeRADIUS, Cisco ISE, Aruba ClearPass) capable de gérer la charge d'authentification attendue et de transmettre les requêtes.
2. Gestion des Certificats
Pour les déploiements PEAP, votre serveur RADIUS nécessite un certificat TLS émis par une autorité de certification (CA) approuvée par vos clients. N'utilisez pas certificats auto-signés pour les déploiements eduroam en production. Le certificat doit être régulièrement renouvelé pour éviter les interruptions d'authentification.
3. Configuration du client (L'outil CAT)
Le point de défaillance le plus courant dans les déploiements eduroam est une mauvaise configuration du client. Les utilisateurs se connectant manuellement ne parviennent souvent pas à configurer la validation du certificat, ce qui les rend vulnérables à la collecte d'identifiants.
Pour atténuer ce problème, les institutions doivent utiliser l'eduroam Configuration Assistant Tool (CAT) ou une solution MDM pour distribuer des profils préconfigurés. Ces profils configurent automatiquement la méthode EAP correcte, épinglent le certificat du serveur RADIUS attendu et définissent les protocoles d'authentification internes appropriés.
4. Attribution et segmentation des VLAN
Un déploiement mature utilise les attributs RADIUS pour attribuer dynamiquement des VLAN en fonction de l'identité de l'utilisateur.
- Utilisateurs internes : Attribués à des VLAN internes avec un accès approprié aux ressources du campus.
- Utilisateurs visiteurs : Attribués à un VLAN invité restreint avec un accès uniquement à Internet.
Cette segmentation est essentielle pour la sécurité et la conformité, garantissant que les appareils des visiteurs ne peuvent pas accéder aux réseaux internes sensibles.
Bonnes pratiques et recommandations neutres vis-à-vis des fournisseurs
- Prioriser le WPA3 : Pour les nouveaux déploiements, activez le WPA3-Enterprise pour bénéficier d'un chiffrement obligatoire de 192 bits et d'une protection améliorée contre les attaques par dictionnaire hors ligne.
- Appliquer la validation des certificats : Exigez l'utilisation de profils de configuration (via CAT ou MDM) pour garantir que les clients valident strictement le certificat du serveur RADIUS avant de transmettre les identifiants.
- Utiliser RadSec : Lors de la configuration des connexions proxy RADIUS vers la fédération nationale, utilisez RadSec (RADIUS over TLS) plutôt que l'UDP simple. Cela chiffre le trafic proxy et améliore la fiabilité sur les liaisons WAN.
- Intégrer avec les solutions invités : eduroam ne sert que les utilisateurs ayant des identifiants académiques. Vous devez maintenir une solution Guest WiFi distincte et sécurisée pour les entrepreneurs, les visiteurs publics et les participants à des événements.
- Examiner l'infrastructure connexe : Assurez-vous que votre réseau sous-jacent est sécurisé. Lisez notre guide Protégez votre réseau avec un DNS et une sécurité robustes pour plus de détails. Si vous déployez une infrastructure temporaire pour des événements universitaires, consultez Event WiFi: Planification et déploiement de réseaux sans fil temporaires ou la version portugaise Event WiFi: Planeamento e Implementação de Redes Sem Fios Temporárias .
Dépannage et atténuation des risques
Lorsque l'authentification échoue, un dépannage systématique est essentiel.
- Isoler le domaine de défaillance : Déterminez si la défaillance est locale (affectant vos propres utilisateurs sur votre propre réseau), distante (affectant vos utilisateurs ailleurs) ou entrante (affectant les visiteurs sur votre réseau).
- Vérifier les journaux RADIUS : Les journaux du serveur RADIUS sont la source de vérité définitive. Recherchez les messages
Access-Reject(indiquant de mauvais identifiants ou des violations de politique) ou les délais d'attente (indiquant des problèmes de connectivité proxy). - Vérifier la validité du certificat : Assurez-vous que le certificat du serveur RADIUS n'a pas expiré et que la chaîne de certificats complète est présentée au client.
- Surveiller la latence en amont : Une latence élevée sur la connexion au proxy RADIUS national peut entraîner des délais d'attente côté client, ce qui se traduit par des connexions échouées même avec des identifiants corrects.
ROI et impact commercial
Pour les établissements d'enseignement supérieur, le ROI d'un déploiement eduroam approprié se mesure par une réduction drastique des tickets de support. En éliminant les Captive Portal et la saisie manuelle des mots de passe, les services d'assistance informatique constatent une baisse significative des appels liés à la connectivité. (L'engagement de Purple envers ce secteur est évident ; voir Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers ).
Pour les sites commerciaux — tels que ceux de l' Hôtellerie , du Commerce de détail , de la Santé ou des Transports — le support d'eduroam Visitor Access (eVA) ou de fédérations similaires comme OpenRoaming offre une expérience fluide pour les données démographiques de grande valeur. Il garantit que les visiteurs universitaires peuvent se connecter automatiquement et en toute sécurité, améliorant la satisfaction tout en permettant au site de maintenir une segmentation réseau stricte. Si votre site nécessite une bande passante dédiée pour prendre en charge cela, envisagez de lire Qu'est-ce qu'une ligne louée ? Internet d'entreprise dédié .
Lors de la planification des mises à niveau du réseau, l'intégration des capacités 802.1X garantit que l'infrastructure est prête pour la mise en réseau moderne axée sur l'identité, jetant les bases d' WiFi Analytics avancés et de services basés sur la localisation.
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enterprise-grade WiFi security, replacing shared passwords (PSKs) with individualised authentication.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server in an 802.1X deployment that actually checks the user's credentials against a directory (like Active Directory).
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections. It provides for the transport and usage of various authentication mechanisms.
The language spoken between the client device and the RADIUS server during the 802.1X handshake.
Supplicant
The client device (e.g., laptop, smartphone) or the software on that device attempting to authenticate to a network using 802.1X.
The entity requesting access. Its configuration (especially regarding certificate validation) is critical for security.
Authenticator
The network device (e.g., wireless access point, Ethernet switch) that facilitates the 802.1X authentication process by passing messages between the Supplicant and the Authentication Server.
The gatekeeper that blocks network traffic until the RADIUS server gives the green light.
PEAP (Protected Extensible Authentication Protocol)
An EAP method that encapsulates the EAP transaction within a TLS tunnel established using a server-side certificate, protecting the inner authentication (usually a password).
The most common authentication method for eduroam, balancing security with ease of deployment.
RadSec
A protocol for transmitting RADIUS data over TCP and TLS, rather than the traditional UDP.
Recommended for securing the proxy connections between institutions and the national eduroam federation, preventing interception of authentication traffic.
Realm
The portion of a user's identity following the '@' symbol (e.g., 'university.ac.uk' in 'user@university.ac.uk').
Used by RADIUS proxy servers to determine where to route the authentication request in a federated environment like eduroam.
GuidesSlugPage.workedExamplesTitle
A 400-room conference hotel adjacent to a major university frequently hosts academic symposiums. The IT Director wants to allow visiting academics to connect automatically without using the hotel's standard captive portal, but must ensure these visitors cannot access the hotel's corporate network or the standard guest network VLAN.
The hotel should implement eduroam Visitor Access (eVA) or join a commercial federation like OpenRoaming.
- The hotel configures a new SSID ('eduroam' or 'OpenRoaming') on their enterprise access points.
- The APs are configured to use WPA2-Enterprise/802.1X.
- The hotel deploys a local RADIUS server configured to proxy authentication requests for external realms to the national federation (for eduroam) or the OpenRoaming hub.
- Crucially, the local RADIUS server is configured to return a specific VLAN ID attribute in the
Access-Acceptmessage for all proxied authentications. - The access points place these authenticated users onto an isolated, internet-only VLAN, completely segmented from the hotel's corporate and standard guest traffic.
A university IT team notices a spike in compromised student accounts. Investigation reveals that students are connecting to a rogue access point broadcasting the 'eduroam' SSID at a local coffee shop. The rogue AP is using a self-signed certificate to harvest credentials via PEAP.
The IT team must immediately enforce strict certificate validation on all client devices.
- They must stop advising students to manually connect to the SSID and 'accept the certificate warning'.
- They deploy the eduroam Configuration Assistant Tool (CAT) for BYOD devices and update MDM profiles for managed devices.
- These profiles configure the supplicant to only trust the specific Certificate Authority (CA) that issued the university's RADIUS server certificate, and to verify the server's Common Name (CN).
- Once configured, if a student's device encounters the rogue AP, the EAP tunnel establishment will fail because the rogue certificate does not match the pinned CA/CN, preventing the transmission of credentials.
A retail chain wants to offer OpenRoaming across 50 locations using their existing guest WiFi infrastructure, which currently relies on an open SSID with a captive portal.
The retail chain must upgrade their network to support 802.1X and RADIUS proxying.
- The network team enables a new SSID broadcasting the OpenRoaming Consortium OI (Organization Identifier).
- They configure the access points to authenticate via 802.1X.
- They configure their central RADIUS server to proxy requests to the OpenRoaming federation hub.
- They ensure their internet backhaul can support the expected increase in automated connections, potentially upgrading to dedicated leased lines if necessary.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your university is deploying a new wireless network. The CISO mandates that credential phishing via rogue access points must be mathematically impossible. Which EAP method must you select?
GuidesSlugPage.hintPrefixConsider which method relies on passwords versus which relies entirely on cryptographic keys.
GuidesSlugPage.viewModelAnswer
You must select EAP-TLS. Unlike PEAP, which relies on a password inside a TLS tunnel, EAP-TLS requires mutual certificate authentication. Because the client device authenticates using a cryptographic certificate rather than a password, there are no credentials for a rogue access point to phish.
Q2. A visiting researcher from another university complains they cannot connect to your eduroam network. Your local users are connecting fine. You check your local RADIUS server logs and see the request arriving, but it times out before an Access-Accept is received. What is the most likely cause?
GuidesSlugPage.hintPrefixThink about the path the authentication request takes for a visiting user versus a local user.
GuidesSlugPage.viewModelAnswer
The most likely cause is a connectivity or latency issue between your local RADIUS server and the national NREN RADIUS proxy. Because local users authenticate directly against your server, they are unaffected. The visiting user's request must be proxied upstream, and a timeout indicates the response from the home institution is not returning in time.
Q3. You are a network architect for a retail chain located near a large university. You want to offer seamless WiFi to students using eduroam Visitor Access (eVA), but you must comply with PCI DSS for your point-of-sale terminals. How do you securely integrate eVA?
GuidesSlugPage.hintPrefixHow does 802.1X allow the network access point to differentiate traffic after authentication?
GuidesSlugPage.viewModelAnswer
You integrate eVA by configuring your RADIUS server to assign all successful eVA authentications to a dedicated, internet-only guest VLAN. The Access-Accept message from the RADIUS server must include the specific VLAN ID. This ensures student devices are completely segmented from the PCI-compliant VLAN used by the point-of-sale terminals, satisfying compliance requirements.



