How to Set Up Enterprise WiFi on Android Devices with EAP-TLS
This technical reference guide provides senior IT leaders with a comprehensive blueprint for deploying 802.1X EAP-TLS authentication on Android devices. It covers the architectural mechanics, manual and MDM-driven implementation strategies, and troubleshooting methodologies necessary to secure enterprise wireless networks.
Listen to this guide
View podcast transcript
- Executive Summary
- Listen to the Briefing
- Technical Deep-Dive
- The 802.1X Architecture and EAP-TLS Mechanics
- Android-Specific Certificate Requirements
- Integration with Purple's Ecosystem
- Implementation Guide
- Method 1: Manual Configuration (BYOD / Small Scale)
- Method 2: MDM-Pushed Profile (Enterprise Scale)
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
Securing enterprise wireless networks against credential theft and unauthorised access requires moving beyond shared passwords. For Android device fleets across corporate environments, 802.1X EAP-TLS (Extensible Authentication Protocol with Transport Layer Security) represents the definitive security standard. By leveraging mutual certificate-based authentication, EAP-TLS eliminates the risks associated with password fatigue, phishing, and weak credentials.
This technical reference guide provides network architects, IT managers, and CTOs with actionable strategies for deploying EAP-TLS on Android devices. Whether managing point-of-sale terminals in Retail , clinical devices in Healthcare , or back-of-house operations in Hospitality , mastering this deployment ensures robust security compliance (PCI DSS, GDPR, ISO 27001) while delivering a seamless connection experience for end-users. We cover both manual configuration for BYOD environments and zero-touch MDM provisioning for corporate-owned fleets.
Listen to the Briefing
Technical Deep-Dive
The 802.1X Architecture and EAP-TLS Mechanics
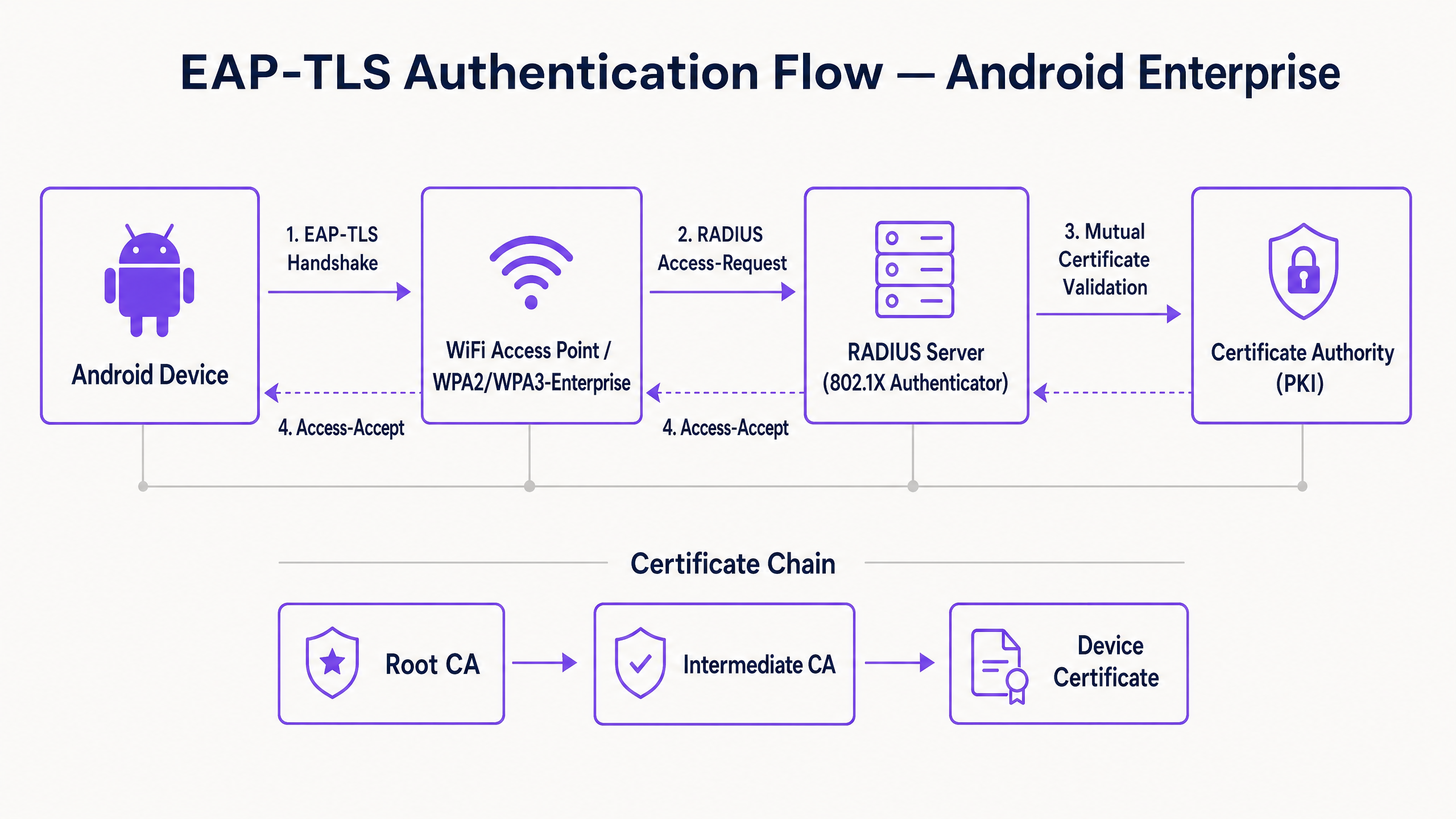
At its core, 802.1X is an IEEE standard for port-based network access control. In a wireless context, the access point acts as the Authenticator, facilitating communication between the Android device (the Supplicant) and the RADIUS server (the Authentication Server).
Unlike PEAP or TTLS which tunnel legacy password authentication within TLS, EAP-TLS relies entirely on X.509 certificates. This creates a mutual authentication paradigm:
- The RADIUS server presents its certificate to the Android device to prove the network is legitimate.
- The Android device presents its unique client certificate to the RADIUS server to prove it is an authorised endpoint.
Android-Specific Certificate Requirements
Deploying on Android introduces specific constraints, particularly from Android 11 onwards. Google deprecated the "Do not validate" option for server certificates to mitigate man-in-the-middle (MitM) attacks. Consequently, the Android device must possess the Root CA certificate that signed the RADIUS server's certificate.
Furthermore, the RADIUS server certificate must contain the correct Extended Key Usage (EKU) attributes—specifically Server Authentication (OID 1.3.6.1.5.5.7.3.1). Without this, the Android supplicant will silently drop the TLS handshake.
For the client side, Android requires the private key and certificate to be bundled, typically in a PKCS#12 format (.p12 or .pfx).
Integration with Purple's Ecosystem
While EAP-TLS secures your corporate devices and operational infrastructure, venue operators must also manage visitor access. This is where a dual-SSID strategy becomes critical. Your corporate SSID utilises 802.1X EAP-TLS, while your public SSID leverages Purple's Guest WiFi platform. This separation ensures operational security while allowing the marketing team to leverage WiFi Analytics on the guest network. For a broader view on securing the physical infrastructure, refer to Access Point Security: Your 2026 Enterprise Guide .
Implementation Guide
Deploying EAP-TLS on Android can be approached manually for small BYOD deployments or via Mobile Device Management (MDM) for enterprise scale.
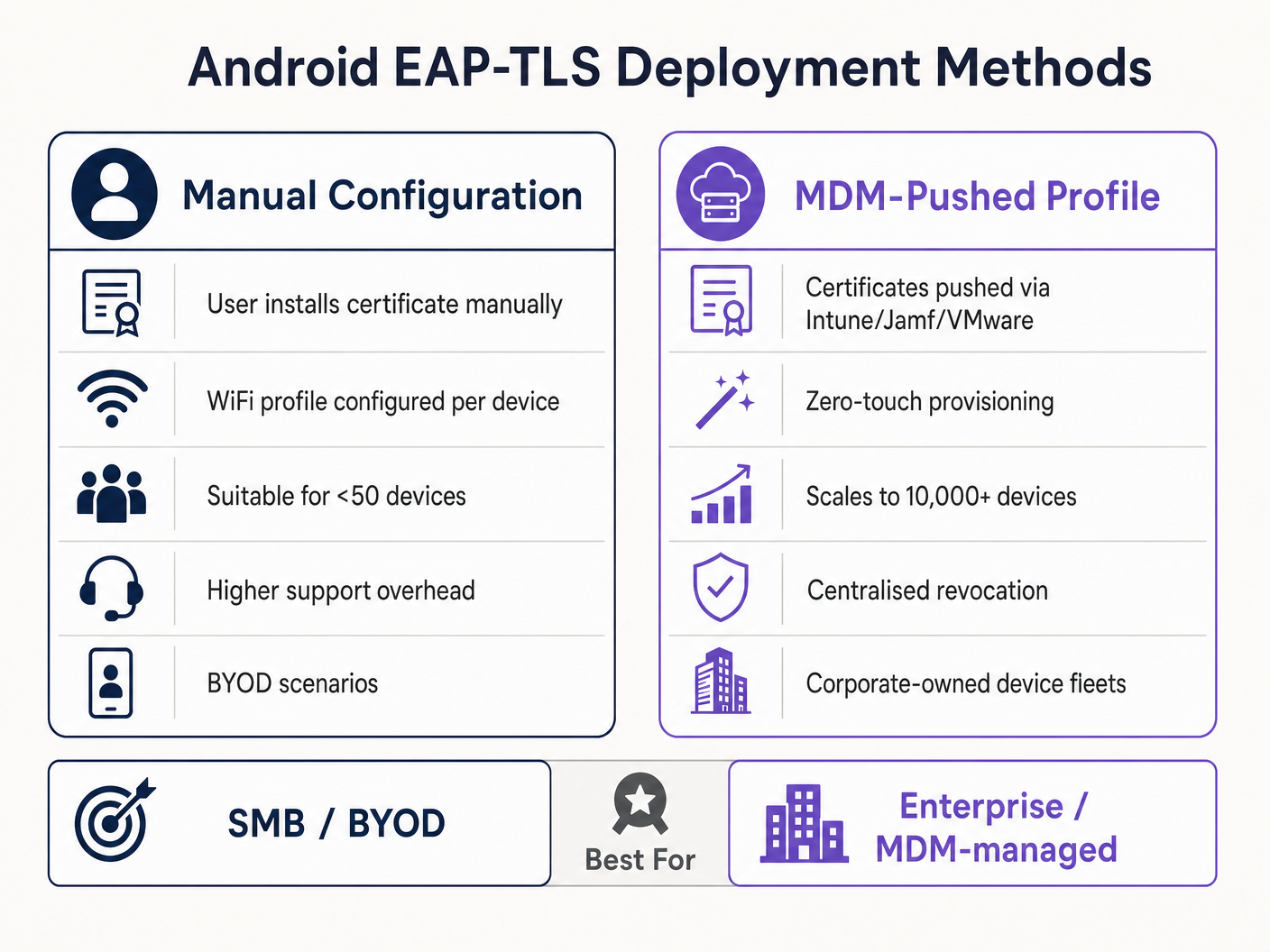
Method 1: Manual Configuration (BYOD / Small Scale)
This method is support-intensive and only recommended for limited rollouts or testing.
- Certificate Delivery: Securely deliver the
.p12client certificate and the Root CA.cerfile to the Android device (e.g., via secure portal or encrypted email). - Installation:
- Navigate to Settings > Security > Encryption & credentials > Install a certificate.
- Install the Root CA as a "Wi-Fi certificate".
- Install the
.p12file, providing the extraction password when prompted.
- Network Configuration:
- Go to Settings > Network & internet > Wi-Fi and select "Add network".
- Enter the SSID.
- Set Security to WPA/WPA2/WPA3-Enterprise.
- Set EAP method to TLS.
- Set CA certificate to the installed Root CA.
- Set Online Certificate Status to Request certificate status.
- Set Domain to match the RADIUS server's certificate Subject Alternative Name (SAN).
- Select the installed Client certificate.
- Enter the Identity (usually the user's UPN or device MAC).
Method 2: MDM-Pushed Profile (Enterprise Scale)
For large estates, such as a university campus or a logistics hub in Transport , MDM is mandatory. This provides zero-touch provisioning and lifecycle management.
- PKI Integration: Connect your MDM (Intune, Workspace ONE, Jamf) to your Certificate Authority using SCEP or NDES.
- Certificate Profile: Create a configuration profile to push the Root CA to the device trust store. Create a second profile (SCEP) to automatically request and install the unique client certificate.
- WiFi Profile: Create a Wi-Fi configuration profile linking the deployed certificates.
- Security Type: WPA2/WPA3 Enterprise
- EAP Type: EAP-TLS
- Authentication Method: Certificate
- Server Trust: Specify the Root CA and the exact server domain name.
For detailed Microsoft-specific instructions, consult our guide: How to Use Microsoft Intune to Push WiFi Certificates to Devices .
Best Practices
- Enforce WPA3-Enterprise: Where hardware supports it, mandate WPA3-Enterprise. The 192-bit security suite explicitly requires EAP-TLS, ensuring the highest cryptographic standards.
- Automate Certificate Lifecycle: Client certificates expire. If you rely on manual renewals, you will face massive outages. Implement SCEP/NDES to automatically renew certificates 30 days prior to expiry.
- Implement Robust DNS: Certificate Revocation List (CRL) checks and OCSP require reliable DNS resolution from the edge. Read more in Protect Your Network with Strong DNS and Security .
- VLAN Segmentation: Map the EAP-TLS authenticated sessions to specific VLANs based on the certificate attributes (e.g., separating POS terminals from manager tablets) using RADIUS attributes like
Tunnel-Private-Group-Id.
Troubleshooting & Risk Mitigation
When Android devices fail to connect via EAP-TLS, the issue almost always resides in the certificate chain or RADIUS configuration.
- Symptom: Android 11+ devices immediately disconnect or show "Authentication error" without prompting the user.
- Root Cause: The device does not trust the RADIUS server certificate. The "Domain" field in the WiFi profile must exactly match the SAN of the server certificate, and the Root CA must be installed.
- Symptom: Connection times out during the TLS handshake.
- Root Cause: The RADIUS server cannot reach the CRL distribution point to verify the client certificate's revocation status. Ensure your RADIUS server has outbound HTTP access to your PKI's CRL endpoints.
- Symptom: Windows devices connect, but Android devices fail.
- Root Cause: Missing
Server AuthenticationEKU on the RADIUS certificate, or the Android supplicant is attempting to use an unsupported cipher suite. Check RADIUS logs for TLS negotiation failures.
- Root Cause: Missing
ROI & Business Impact
Transitioning to EAP-TLS requires upfront investment in PKI and MDM infrastructure, but the return on investment is substantial for senior IT leaders.
- Helpdesk Cost Reduction: Password resets account for 20-30% of IT helpdesk tickets. Certificate-based authentication eliminates password rotation policies for network access, drastically reducing support overhead.
- Risk Mitigation: EAP-TLS provides immunity against credential harvesting and offline dictionary attacks. The cost of a single breach in a regulated industry like Healthcare far exceeds the deployment cost of a PKI.
- Operational Continuity: Automated certificate provisioning ensures that critical operational devices—from warehouse scanners to retail POS systems—never drop off the network due to expired credentials. As Purple continues to expand its reach, highlighted by recent strategic moves like Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers , robust foundational connectivity becomes the enabler for advanced analytics and engagement.
Key Definitions
802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational framework that prevents unauthorised devices from accessing the corporate network at the edge.
EAP-TLS
Extensible Authentication Protocol with Transport Layer Security. An authentication framework that uses X.509 certificates for mutual authentication between the client and the server.
Considered the most secure EAP type, it eliminates password reliance, making it essential for high-security environments.
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management.
The server component (e.g., Cisco ISE, Microsoft NPS) that validates the Android device's certificate against the PKI.
Supplicant
The client device (in this case, the Android smartphone or tablet) that is requesting access to the network.
Understanding the supplicant's specific OS constraints (like Android 11's strict validation) is key to a successful deployment.
Authenticator
The network device (the WiFi Access Point) that facilitates the authentication process between the Supplicant and the RADIUS server.
The AP does not make the decision; it merely enforces the port control based on the RADIUS server's response.
PKI
Public Key Infrastructure. A set of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates.
The backbone of EAP-TLS. Without a robust PKI, certificate-based authentication is impossible.
SCEP
Simple Certificate Enrollment Protocol. A protocol designed to make the issuing and revocation of digital certificates as scalable as possible.
Used by MDM platforms to automatically provision client certificates to Android devices without user intervention.
SAN
Subject Alternative Name. An extension to X.509 that allows various values to be associated with a security certificate.
Android 11+ requires the 'Domain' field in the WiFi profile to match the SAN of the RADIUS server's certificate.
Worked Examples
A national retail chain needs to deploy 5,000 Android-based point-of-sale (POS) tablets. The security team mandates that these devices must not use shared passwords and must be immune to credential phishing. How should the infrastructure team approach this deployment?
The team must deploy a Mobile Device Management (MDM) solution integrated with their internal Public Key Infrastructure (PKI) via SCEP. The MDM will push a configuration profile containing the Root CA certificate, automatically request a unique client certificate for each POS tablet, and configure the WPA3-Enterprise WiFi profile to use EAP-TLS. The RADIUS server will be configured to assign these devices to an isolated POS VLAN based on successful certificate validation.
A hospital IT manager is upgrading the wireless network. Following the upgrade, older Android 9 devices connect successfully to the EAP-TLS network, but newly procured Android 12 devices fail to authenticate, citing a trust error.
The IT manager must update the WiFi configuration profile pushed to the devices. Android 11+ enforces strict server certificate validation. The profile must be updated to explicitly define the Root CA certificate to trust and specify the exact 'Domain' (matching the RADIUS server's SAN) to prevent MitM attacks.
Practice Questions
Q1. Your organisation is migrating from PEAP-MSCHAPv2 to EAP-TLS. During the pilot phase, several Android 13 devices fail to connect. The RADIUS logs show that the TLS handshake is initiated but dropped by the client before the client certificate is sent. What is the most likely configuration error?
Hint: Consider the strict validation requirements introduced in recent Android versions regarding the server's identity.
View model answer
The most likely error is that the WiFi profile pushed to the Android 13 devices does not correctly specify the 'Domain' suffix match, or the Root CA is not properly linked in the profile. Android drops the connection to prevent a Man-in-the-Middle attack because it cannot validate the RADIUS server's certificate.
Q2. You are designing the architecture for a large stadium deployment. The client wants to use EAP-TLS for all staff devices. What specific infrastructure component must be scaled up compared to a standard WPA2-PSK network, and why?
Hint: EAP-TLS involves complex cryptographic operations during the connection phase.
View model answer
The RADIUS server infrastructure must be significantly scaled up. EAP-TLS requires full mutual certificate validation (asymmetric cryptography), which is computationally expensive. In a stadium environment with thousands of devices potentially roaming or authenticating simultaneously, an undersized RADIUS deployment will cause authentication timeouts and connection failures.
Q3. A client certificate is compromised on a lost Android tablet. What is the exact mechanism by which the network prevents this device from connecting via EAP-TLS?
Hint: How does the RADIUS server know the certificate is no longer valid before its expiration date?
View model answer
The IT administrator revokes the client certificate in the PKI. The PKI updates its Certificate Revocation List (CRL) or OCSP responder. When the lost tablet attempts to connect, the RADIUS server checks the client certificate against the CRL/OCSP. Seeing it is revoked, the RADIUS server rejects the authentication request.



