HIPAA-Compliant WiFi: A Guide for Healthcare Organisations
This technical reference guide provides actionable compliance strategies for healthcare IT teams deploying enterprise and guest WiFi. It covers network segmentation, 802.1X authentication, audit logging, and how to implement secure, isolated wireless access using Purple's platform.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- 1. Encryption and Authentication (802.1X and WPA3-Enterprise)
- 2. Network Segmentation (The Three-Zone Model)
- 3. Audit Logging and SIEM Integration
- Implementation Guide
- Step 1: Conduct a Wireless Risk Assessment
- Step 2: Configure the Clinical and Administrative VLANs
- Step 3: Deploy the Guest WiFi Portal
- Step 4: Implement Continuous Monitoring
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact
- References
Executive Summary
For IT managers, network architects, and CTOs in healthcare environments, deploying wireless networks involves balancing two critical, often competing priorities: securing electronic Protected Health Information (ePHI) to meet strict HIPAA regulations, and providing seamless, high-quality connectivity for patients, visitors, and clinical staff. A single misconfigured access point or shared password can lead to a devastating data breach, regulatory fines, and reputational damage. This guide provides a practical, vendor-neutral framework for deploying HIPAA-compliant WiFi. It covers the essential three-zone segmentation model, data encryption standards (WPA3-Enterprise), robust identity management via 802.1X, and comprehensive audit logging. Furthermore, it details how integrating an enterprise platform like Purple for Guest WiFi and WiFi Analytics ensures that public access remains strictly isolated from clinical systems while still capturing valuable engagement data.
Technical Deep-Dive
Achieving a HIPAA-compliant wireless network requires moving beyond basic connectivity and implementing defence-in-depth architecture. The HIPAA Security Rule mandates technical safeguards for access control, audit controls, integrity, and transmission security [1].
1. Encryption and Authentication (802.1X and WPA3-Enterprise)
The foundation of wireless security is strong encryption. Legacy protocols like WEP, WPA, and even WPA2-Personal (using Pre-Shared Keys) are entirely insufficient for environments handling ePHI. A compromised PSK grants an attacker access to the entire subnet.
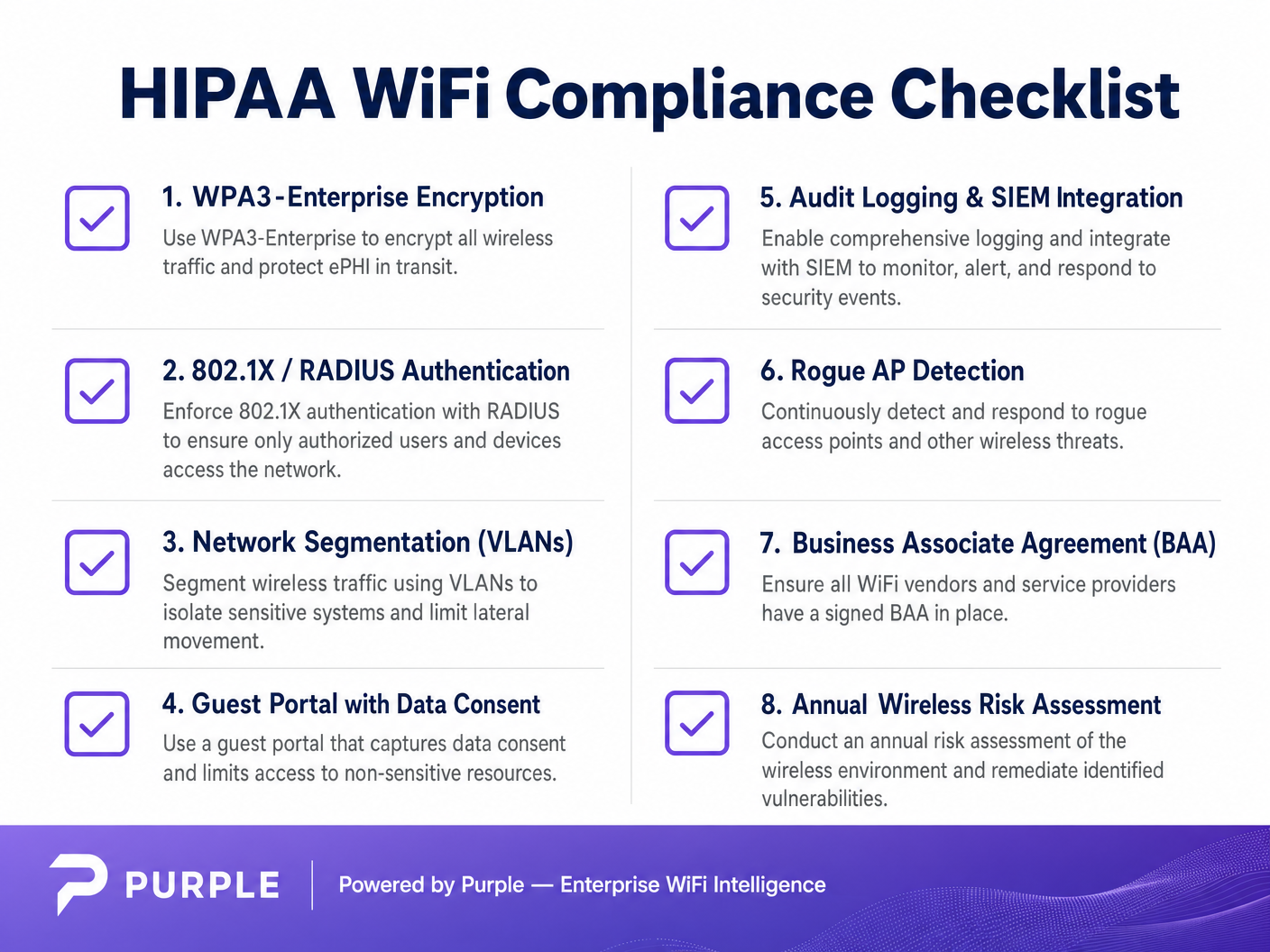
Healthcare organisations must implement WPA3-Enterprise (or WPA2-Enterprise at minimum) paired with 802.1X authentication. This architecture requires every user and device to authenticate individually against a RADIUS (Remote Authentication Dial-In User Service) server before gaining network access [2].
- Clinical Devices (IoT, WOWs): Utilise certificate-based authentication, specifically EAP-TLS (Extensible Authentication Protocol-Transport Layer Security). This eliminates passwords entirely, relying on centrally managed digital certificates installed on authorised devices. If a device is lost, its certificate can be instantly revoked.
- Staff Devices (Laptops, Mobile): Enforce authentication using domain credentials tied to role-based access control (RBAC), often integrating with Active Directory or an Identity Provider (IdP).
2. Network Segmentation (The Three-Zone Model)
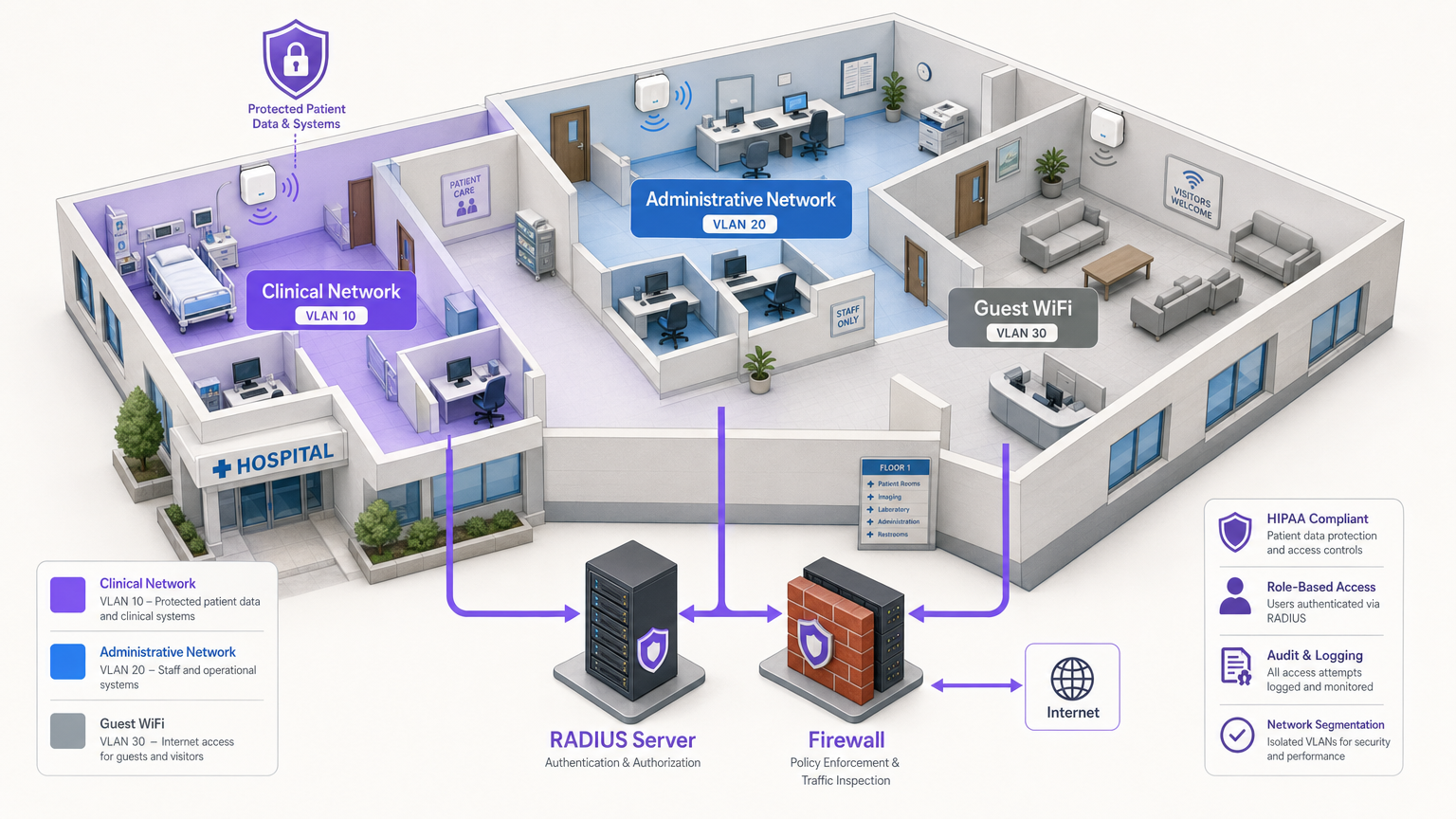
Segmentation is the most critical architectural defence against lateral movement. You cannot have guest smartphones sitting on the same VLAN as your Electronic Health Record (EHR) terminals. The industry standard is a strict three-zone architecture, physically or logically separated via VLANs and firewalls.
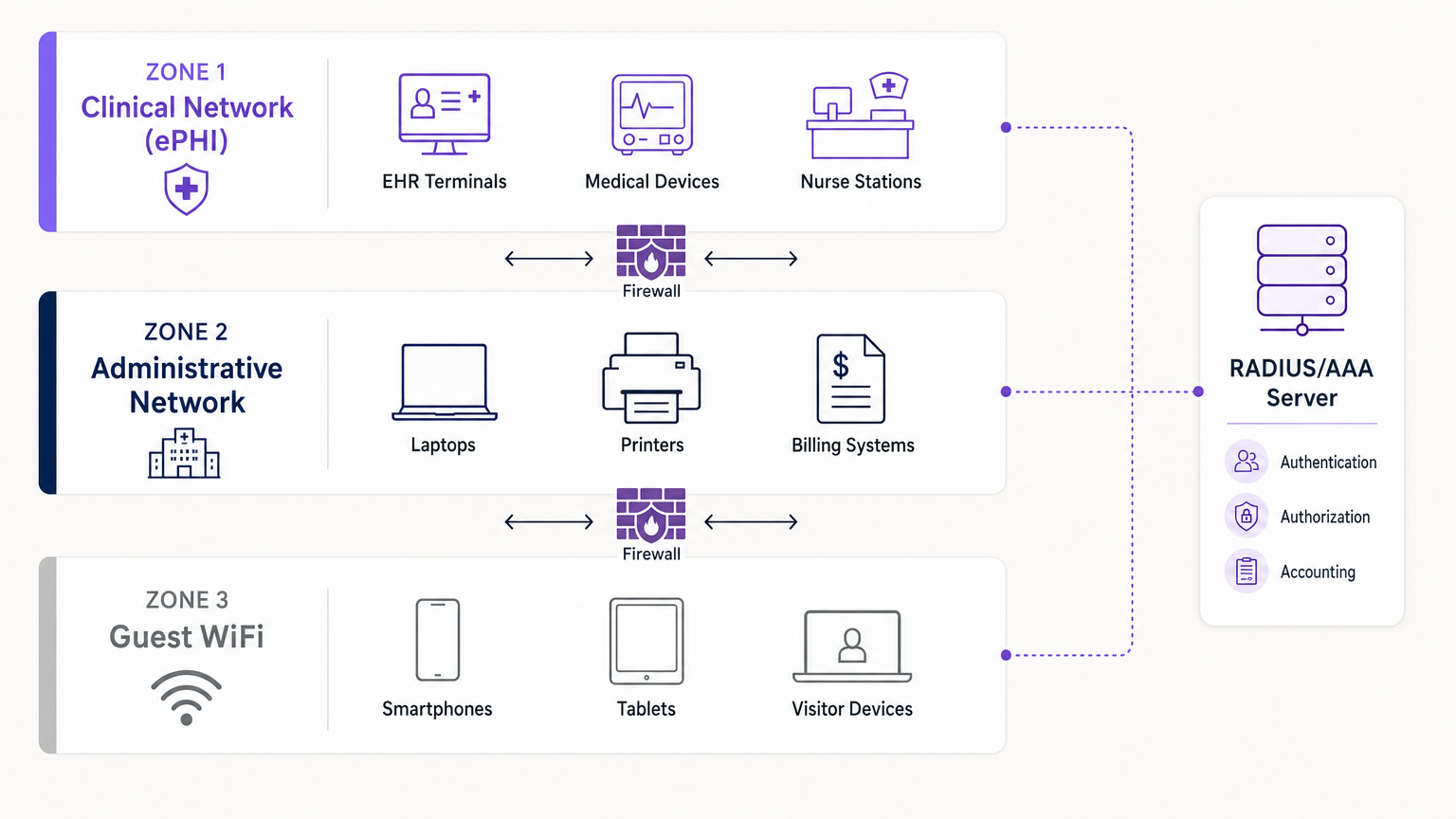
- Zone 1: Clinical Network (ePHI): This highly restricted VLAN handles all sensitive data. It connects EHR systems, medical devices, and nurse stations. Access is limited strictly to authenticated clinical staff and managed devices via 802.1X.
- Zone 2: Administrative Network: This VLAN supports hospital operations—billing systems, staff laptops, and printers—that do not require direct access to patient records.
- Zone 3: Guest WiFi: An isolated, internet-only connection for patients and visitors. It must be completely walled off from Zones 1 and 2, utilising client isolation to prevent guest devices from communicating with each other.
3. Audit Logging and SIEM Integration
HIPAA requires organisations to implement hardware, software, and procedural mechanisms that record and examine activity in information systems containing ePHI [1]. Your wireless controllers and RADIUS servers must log all authentication attempts (successful and failed), session durations, and administrative changes. These logs should be forwarded to a centralised Security Information and Event Management (SIEM) system for continuous monitoring and anomaly detection.
Implementation Guide
Deploying a compliant network requires careful planning and execution. Here is a step-by-step approach for integrating secure clinical access with isolated guest services.
Step 1: Conduct a Wireless Risk Assessment
Before deploying new hardware, conduct a comprehensive RF site survey and risk assessment. Identify all existing access points, including potential rogue devices. Map the required coverage areas for clinical versus guest access. For insights on hardware selection, consult Enterprise WiFi Solutions: A Buyer's Guide .
Step 2: Configure the Clinical and Administrative VLANs
Deploy your core infrastructure (e.g., Cisco Meraki, Aruba, or Your Guide to a Wireless Access Point Ruckus ). Configure the clinical SSID to broadcast only in necessary areas. Implement WPA3-Enterprise and connect your controllers to the RADIUS server. Deploy EAP-TLS certificates to all hospital-owned medical devices.
Step 3: Deploy the Guest WiFi Portal
This is where platforms like Purple excel. Instead of a simple open network, deploy an isolated Guest SSID that routes traffic through Purple's captive portal.
- Isolation: Ensure the Guest VLAN has strict firewall rules denying any internal IP routing. Enable client isolation on the access points.
- Consent and Terms: The captive portal must require users to accept Terms and Conditions, establishing legal boundaries and data usage consent.
- Authentication: Purple acts as the identity provider for guests, handling SMS, email, or social logins, keeping this traffic entirely separate from your internal Active Directory.
Step 4: Implement Continuous Monitoring
Enable Rogue AP detection on your wireless intrusion prevention system (WIPS). This will automatically identify and suppress unauthorized access points plugged into the network by staff or visitors. Ensure all logs are flowing to your SIEM.
Best Practices
- Principle of Least Privilege: Users and devices should only have access to the specific network resources required for their function. A billing clerk does not need access to the imaging VLAN.
- Business Associate Agreements (BAA): Ensure that any vendor providing cloud-managed networking or analytics services has signed a BAA, clearly defining their responsibilities regarding data security.
- Disable Legacy Protocols: Turn off WEP, WPA, TKIP, and outdated management protocols like Telnet on all network hardware. Enforce SSH and HTTPS for administrative access.
- Regular Audits: Wireless security is not a "set and forget" deployment. Conduct annual penetration testing and configuration reviews. For broader context on secure deployments, read WiFi in Hospitals: A Guide to Secure Clinical Networks .
Troubleshooting & Risk Mitigation
Common Failure Modes
- The "Shadow IT" Access Point: A department needs better coverage, so an employee plugs a consumer router into a wall jack. Mitigation: Strict physical port security (802.1X on wired ports) and active Rogue AP suppression via WIPS.
- Certificate Expiration: Clinical devices suddenly drop off the network because their EAP-TLS certificates expired. Mitigation: Implement automated certificate lifecycle management (CLM) and alert thresholds 30 days prior to expiration.
- Guest Traffic Bleed: Misconfigured VLAN tagging allows guest traffic to route into the administrative subnet. Mitigation: Regular penetration testing and automated configuration auditing to verify VLAN isolation.
ROI & Business Impact
Investing in a HIPAA-compliant wireless architecture delivers significant returns beyond simply avoiding regulatory fines (which can reach millions of pounds).
- Risk Mitigation: Robust 802.1X and segmentation drastically reduce the attack surface, protecting the organisation from ransomware and data breaches.
- Operational Efficiency: Certificate-based authentication for clinical devices reduces IT helpdesk tickets related to password resets and connectivity issues, keeping clinicians focused on patient care.
- Enhanced Patient Experience: By securely deploying Purple's guest WiFi platform, hospitals can provide reliable internet access—a key driver of patient satisfaction scores (HCAHPS)—while leveraging the captive portal for wayfinding, patient communications, and gathering feedback without compromising clinical network security.
References
[1] Health Insurance Portability and Accountability Act of 1996 (HIPAA), Pub. L. No. 104-191, 110 Stat. 1936 (1996). [2] Censinet. "HIPAA-Compliant Wireless Network Setup Guide." Censinet Perspectives, 2024.
Key Terms & Definitions
ePHI (Electronic Protected Health Information)
Any protected health information that is created, stored, transmitted, or received electronically.
The primary asset that HIPAA regulations are designed to protect. If a network transmits ePHI, it falls under the strict requirements of the HIPAA Security Rule.
802.1X
An IEEE standard for port-based network access control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The mandatory authentication framework for enterprise healthcare networks, ensuring that only verified users and devices can access the clinical VLAN.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The core server infrastructure that processes 802.1X requests, verifying credentials against a directory (like Active Directory) before granting WiFi access.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An EAP method that relies on client and server certificates to establish a secure connection, providing strong mutual authentication.
The gold standard for authenticating headless medical devices and mobile workstations, eliminating the need for vulnerable passwords.
Network Segmentation
The practice of splitting a computer network into subnetworks, each being a network segment or VLAN.
Crucial for HIPAA compliance, it ensures that a compromised device on the guest or administrative network cannot access the clinical network housing ePHI.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
The primary mechanism used by network engineers to implement segmentation, isolating clinical, administrative, and guest traffic on the same physical access points.
Captive Portal
A web page accessed with a web browser that is displayed to newly connected users of a Wi-Fi network before they are granted broader access to network resources.
Used for Guest WiFi (often provided by platforms like Purple) to capture user consent, enforce Terms and Conditions, and authenticate visitors without touching internal systems.
Rogue AP (Access Point)
A wireless access point that has been installed on a secure network without explicit authorization from a local network administrator.
A major security risk in hospitals (Shadow IT). Enterprise wireless controllers must actively scan for and suppress these devices to prevent unauthorized network bridging.
Case Studies
A 300-bed regional hospital needs to deploy new mobile workstations (WOWs) for nursing staff. The current network uses a single SSID with a WPA2 Pre-Shared Key (PSK) for all hospital-owned devices. How should the IT architect redesign this for HIPAA compliance?
The architect must eliminate the PSK. They should create a dedicated 'Clinical_ePHI' VLAN and SSID. The new SSID must be configured for WPA3-Enterprise (or WPA2-Enterprise). The architect will deploy a RADIUS server and implement EAP-TLS certificate-based authentication. Each WOW will be provisioned with a unique digital certificate via Mobile Device Management (MDM). The RADIUS server will authenticate the certificate before granting the WOW access to the clinical VLAN.
A large outpatient clinic wants to offer free WiFi to patients in the waiting room, but the CTO is concerned about visitors attempting to access the clinic's billing servers. How should this be implemented?
The network team must implement strict network segmentation. They will create a 'Guest_WiFi' SSID mapped to a dedicated, isolated VLAN (e.g., VLAN 30). Firewall rules must be configured to explicitly deny any routing from VLAN 30 to the internal clinical or administrative subnets (VLANs 10 and 20). Client isolation must be enabled on the access points to prevent guest devices from communicating with each other. Finally, the guest SSID should route through a captive portal, such as Purple, to capture Terms and Conditions consent and handle guest authentication (SMS/Email) separately from the clinic's Active Directory.
Scenario Analysis
Q1. A clinic administrator requests that the new Guest WiFi network use a simple WPA2 password ('ClinicGuest2024') posted on the wall to make it easy for elderly patients to connect, rather than using a captive portal. As the network architect, how do you respond?
💡 Hint:Consider the requirements for audit logging, user consent, and the risks of shared credentials on public networks.
Show Recommended Approach
You must advise against using a shared PSK for the guest network. A shared password provides no individual accountability or audit trail, making it impossible to identify malicious actors on the network. Furthermore, it bypasses the opportunity to present a captive portal where users must accept Terms and Conditions, which is critical for limiting the clinic's liability. The recommended approach is an open Guest SSID that routes immediately to a captive portal (like Purple) for individual authentication (e.g., via SMS or email) and T&C acceptance, ensuring secure, logged, and legally compliant access.
Q2. During a wireless risk assessment, you discover a consumer-grade WiFi router plugged into an Ethernet jack in the radiology department. The staff explains they installed it because the enterprise WiFi signal was weak in that corner. What immediate actions must be taken?
💡 Hint:Address both the immediate technical threat and the underlying infrastructure issue.
Show Recommended Approach
- Immediately disconnect the rogue router from the network, as it creates an unmonitored, unencrypted bridge into the clinical environment, violating HIPAA transmission security rules. 2) Ensure that the enterprise Wireless Intrusion Prevention System (WIPS) is configured to automatically detect and suppress rogue APs. 3) Configure 802.1X on all wired switch ports so unauthorized devices cannot connect to the LAN. 4) Conduct an RF site survey in the radiology department to identify the coverage gap and deploy an authorized, properly configured enterprise access point to resolve the staff's legitimate connectivity issue.
Q3. You are configuring 802.1X authentication for a fleet of new medical infusion pumps. The devices do not have keyboards or screens for users to input credentials. How do you securely authenticate them to the clinical VLAN?
💡 Hint:Look for an authentication method that relies on machine identity rather than user identity.
Show Recommended Approach
The devices should be authenticated using EAP-TLS (certificate-based authentication). You will generate unique digital certificates from the hospital's internal Certificate Authority (CA) and install them on each infusion pump. The RADIUS server will be configured to verify these certificates. When a pump connects to the clinical SSID, it presents its certificate; if valid, the RADIUS server assigns it to the clinical VLAN. This provides strong, passwordless mutual authentication.



